Check Point
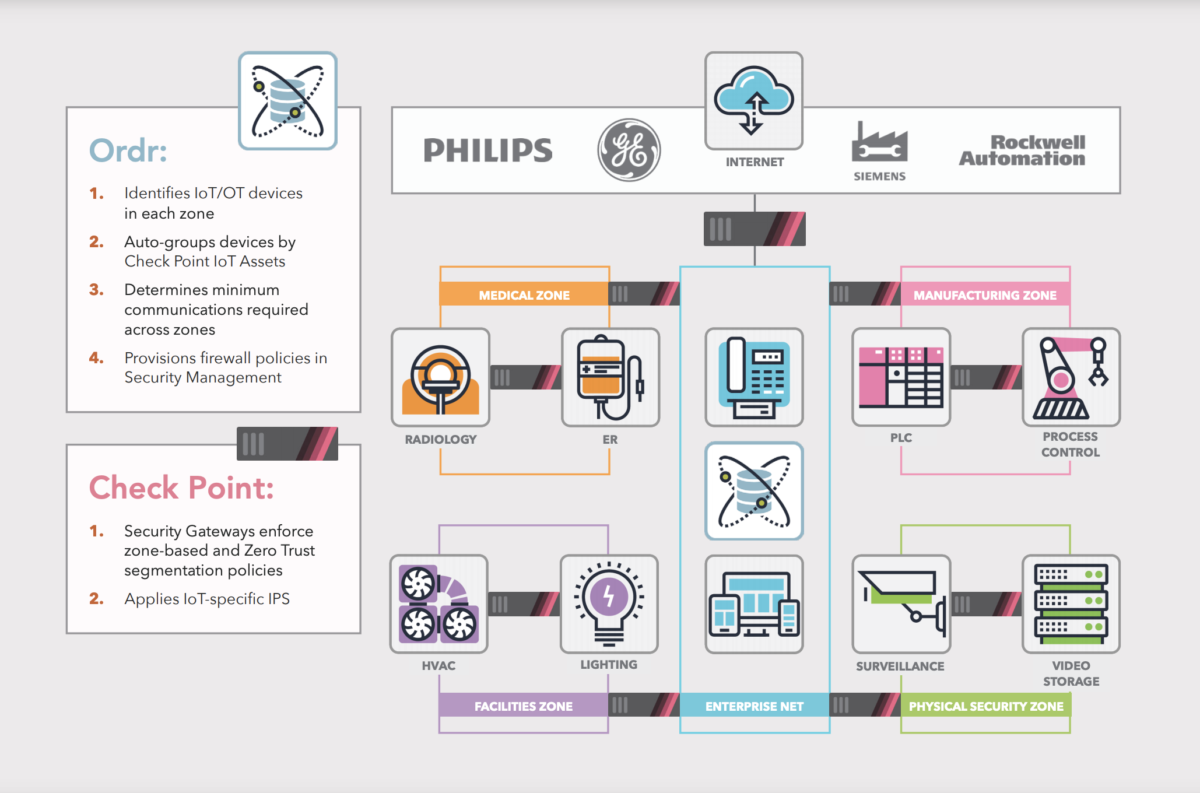
Together, Ordr and Check Point allow you to Take Control of your IOT and OT security by implementing segmentation across your hyper-connected enterprise. Ordr integrates natively with Check Point Security Management for multi-gateway policy enforcement. When new devices are connected to the network, they are automatically classified and updated in Check Point Security Management and Security Gateways with the proper IoT Asset membership. Through its network and device awareness, Ordr maintains current IP addressing for IoT Assets in all Security Gateways.