Macro-Segmentation
Controls traffic between network zones and reduces blast radius during security incidents
AI Protect for Segmentation
ORDR delivers microsegmentation and NAC acceleration that moves from visibility to enforcement without disrupting operations.
Built on AI-driven device intelligence, this approach enables security teams to deploy policies in days and prevent lateral movement before threats spread.
Most segmentation tools show you what’s exposed but leave enforcement to manual work across disconnected systems. ORDR provides both intelligence and enforcement on a single platform, enabling security teams to implement macro- and micro-segmentation to stop lateral movement without disrupting production systems.
Traditional segmentation projects drag on for 12–24 months. ORDR reduces deployment timelines to days or weeks by using AI-generated policies that reflect real device behavior rather than generic templates.
Controls traffic between network zones and reduces blast radius during security incidents
Generates least-privilege policies based on real device behavior and restricts asset-to-asset communication precisely
Provides device intelligence, NAC solutions need to enforce policies for unmanaged devices
Simulates policies before enforcement using live traffic data to validate operational impact
Here’s how ORDR enables segmentation without the complexity of multiple disconnected tools.
ORDR establishes a single source of truth about every connected device across your environment. This intelligence is behavior-based, not scan-based, providing continuous observation of real communication patterns that make policy enforcement-ready. The platform has leveraged AI since its inception, with over 8 years of patented technology that has learned from 100+ million connected devices.
Visibility-only platforms like Armis and Claroty excel at identifying threats but stop at recommendations. To enforce segmentation, they partner with third-party tools, creating integration complexity. Segmentation-only tools like Elisity require a separate asset intelligence platform to feed them data. ORDR combines both capabilities, eliminating vendor finger-pointing.
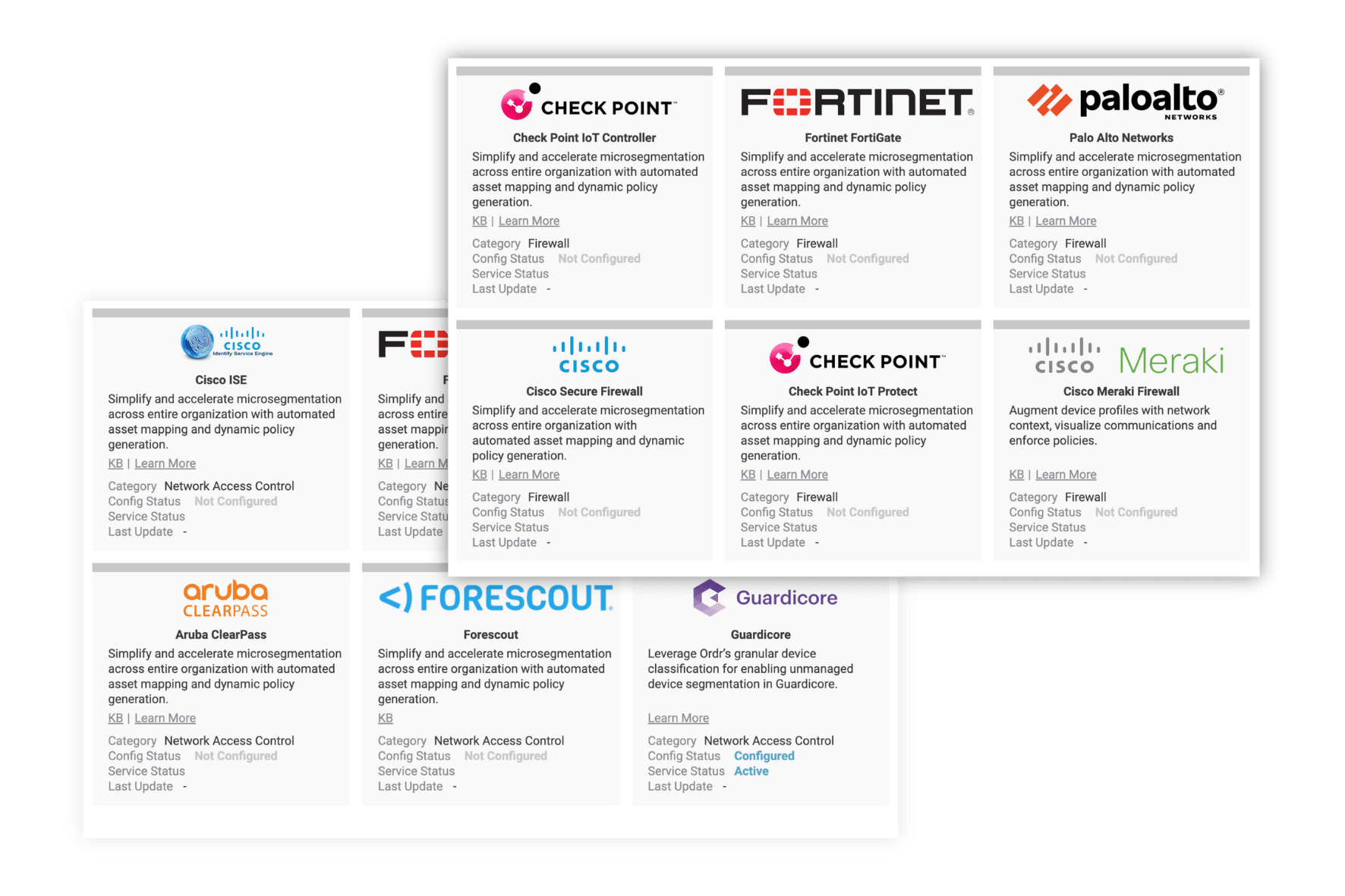
ORDR integrates directly with the systems you already trust:
Here’s how ORDR’s network segmentation process works from discovery through continuous enforcement:
| Stage | What Happens |
|---|---|
| Discovery & Intelligence Foundation (24–48 Hours) | ORDR passively analyzes traffic to identify every device and map real communication behavior and dependencies. |
| Policy Generation & Simulation | AI creates least-privilege policies from live traffic data and allows natural-language policy creation with full “what-if” simulation before enforcement. |
| Safe Deployment & Continuous Adaptation | Validated policies are pushed to infrastructure with one-click deployment and continuously updated as device behavior changes. |
Traditional macro-segmentation creates broad network zones that still allow attackers to move laterally once inside the network. ORDR’s micro-segmentation enforces zero-trust principles across unmanaged devices, reducing risk without disrupting clinical or operational workflows.
Build segmentation groups by function, risk, location, or role. Policies adapt automatically as devices or roles change, maintaining continuous protection without manual updates.
Restrict asset-to-asset communication only to what devices actually need to function. Video cameras connect only to camera management systems. Medical imaging devices communicate only with PACS or DICOM servers.
ORDR analyzes device behavior to establish group and device-centric baselines unique to your network. These sanctioned communication patterns convert into segmentation policies.
Network Access Control solutions excel at user and managed device authentication but struggle with IoT and unmanaged devices that lack certificates or authentication capabilities. ORDR addresses NAC deployment challenges by providing high-fidelity discovery and classification, as well as make, model, serial number, and location for devices that NAC solutions can’t profile effectively.
Traditional NAC profiling provides insufficient visibility into unmanaged devices, forcing organizations to grant access based on MAC addresses or IP addresses. This creates a fleet of “exception devices” that are blindly trusted. ORDR provides the rich context NAC solutions need to confidently apply policy decisions. This data can be shared with CMDB, CMMS, or NAC platforms to appropriately allow or deny access.
Here’s a side-by-side view of how ORDR compares to other segmentation approaches:
| Vendor | Limitation | ORDR Difference |
|---|---|---|
| Illumio | Workload-only; needs separate asset intelligence tools | Unified IT/IoT/OT visibility + built-in segmentation |
| Elisity | Segmentation-only platform | Combines asset intelligence + enforcement in one system |
Security teams face a consistent challenge: visibility platforms generate endless reports while segmentation projects stall due to fear of breaking production systems. ORDR enables security teams to move from seeing problems to solving them. Policies are simulated before enforcement to show exactly what will be affected. This makes segmentation safe for high-consequence environments where downtime is unacceptable.
Here’s a structured approach to implementing segmentation using ORDR’s capabilities:
| Best Practice | How It’s Done | ORDR Advantage |
|---|---|---|
| Start With Critical Assets | Segment high-risk/high-value devices first (e.g., IP cameras, HVAC), expanding gradually over time | Phased rollout reduces risk and allows incremental, controlled segmentation |
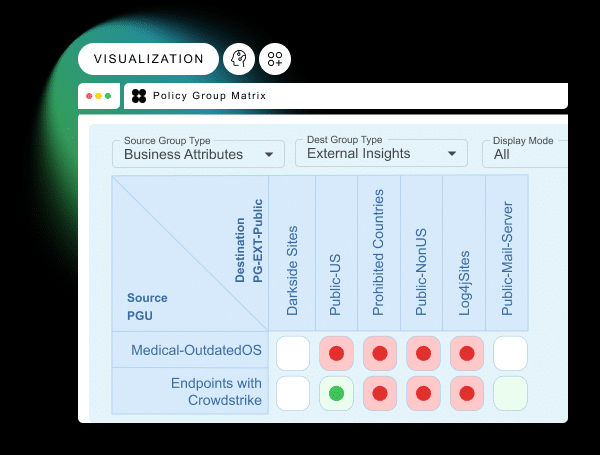
| Validate Before You Enforce | Test policies using live traffic simulation to uncover dependencies before activation | Visual traffic matrix ensures safe enforcement with no operational surprises |
| Leverage Existing Infrastructure | Push policies through existing firewalls, NAC, and network tools | No rip-and-replace—works with current security stack |
| Maintain Continuous Monitoring | Continuously baseline device behavior and detect anomalies in real time | Flow Genome mapping enables ongoing visibility and automated response to threats |
ORDR was built specifically for healthcare, manufacturing, and critical infrastructure, where disruption is unacceptable.
The platform has leveraged AI since day one, with patents on AI-powered device classification and behavioral modeling. This is foundational technology, not a marketing buzzword.
ORDR works with your existing security and network infrastructure, pushing policies to the systems you already trust.
Discovery and initial visibility typically happen within 24–48 hours. Segmentation enforcement timelines vary by environmental complexity, but organizations report deploying policies in days to weeks.
No. ORDR simulates every policy before enforcement, showing exactly what will be impacted. You validate safety using the live traffic matrix interface, then push to production with confidence.
Absolutely. ORDR was built for environments where disruption is unacceptable. Policies are simulated and validated before enforcement.
Visibility platforms excel at identifying threats but stop at recommendations. ORDR provides both visibility and enforcement on a single platform, eliminating integration complexity.
Segmentation-only tools require a separate asset intelligence platform to feed them data. ORDR combines asset intelligence and enforcement in one system.
This solution is ideal for:
Deploy segmentation that protects medical devices and patient data without disrupting clinical workflows.
Secure OT environments and prevent lateral movement while maintaining production continuity.
Meet compliance requirements with continuous enforcement and measurable progress.
Implement zero-trust segmentation across utilities, transportation, and government facilities where operational availability is non-negotiable.