Visibility Gaps
Traditional IT security tools can’t discover or classify OT devices. SCADA systems, PLCs, and BACnet controllers remain invisible to endpoint agents and vulnerability scanners.
Secure Cyber-Physical Systems Without Disrupting Operations
ORDR protects converged IT/OT environments with protocol-aware discovery, behavioral intelligence, and validated segmentation policies that prevent lateral movement across critical infrastructure without causing downtime.
Critical infrastructure organizations eliminated the air gap. Production systems that were once isolated now connect to IT networks, cloud platforms, and supply chains. Every SCADA controller becomes a potential entry point. Every BACNet-enabled building system creates an attack surface. Every industrial sensor adds risk.
In 2025, ransomware attempts against industrial operators increased 46% in a single quarter. The threat landscape targeting converged environments includes:
Impact on Operations
75% of OT threats originate in IT and spread to production assets
Why It Matters
A single compromised workstation can access industrial systems
Impact on Operations
Manipulation of control systems disrupts physical processes
Why It Matters
Leads to production halts, safety failures, and physical damage
Impact on Operations
Exploits insecure protocols like BACnet and Modbus
Why It Matters
Legacy protocols lack authentication and built-in security
Impact on Operations
Persistent access established by nation-state actors
Why It Matters
Enables future large-scale disruption across infrastructure
Legacy approaches to operational technology security relied on network isolation. The Purdue Model assumed air gaps would protect production systems. IT/OT convergence rendered that model obsolete. Organizations now face three critical gaps:
Traditional IT security tools can’t discover or classify OT devices. SCADA systems, PLCs, and BACnet controllers remain invisible to endpoint agents and vulnerability scanners.
Security teams fear segmentation policies will break production. Without validated enforcement, organizations see threats but can’t act on them.
Standard discovery methods don’t understand industrial protocols. Organizations can’t identify which devices communicate via Modbus, BACnet, or proprietary SCADA languages.
ORDR delivers three integrated capabilities designed to protect cyber-physical systems.
ORDR identifies every device across converged IT/OT networks, including devices communicating via industrial protocols:
| Capability | What ORDR Discovers | Business Value |
|---|---|---|
| SCADA Systems | Supervisory control systems, RTUs, MTUs | Complete visibility into distributed control systems |
| Industrial Control Systems (ICS) | PLCs, DCS, HMIs, industrial sensors | Real-time inventory of production equipment |
| BACnet Devices | Building automation, HVAC, access control systems | Unified view of facility management systems |
| Legacy OT Assets | Devices with outdated firmware or unsupported OS | Identify vulnerable systems that can’t be patched |
| Converged Infrastructure | IT/OT bridging devices | Map attack paths between corporate and production networks |
ORDR doesn’t just catalog devices. It understands what they do, how they communicate, and where exposure exists.
Behavioral profiling delivers:
When a BACnet controller starts communicating outside its normal pattern, ORDR detects it. When a PLC exhibits behavior inconsistent with its production role, you’re alerted before damage occurs.
Segmentation projects fail when enforcement risks break production. ORDR validates policies before implementation, ensuring Zero Trust protection without operational disruption.
| Capability | How It Works | Business Value |
|---|---|---|
| Policy Validation | Simulates segmentation policies against live traffic to identify the impact | Deploy Zero Trust without risking plant downtime |
| Production-Safe Enforcement | AI analyzes device dependencies to ensure no workflow disruption | Enforce protection with confidence in high-risk environments |
| Protocol-Aware Segmentation | Builds policies aligned with industrial protocol requirements | Segment SCADA and BACnet devices without breaking operations |
| Lateral Movement Prevention | Isolates IT from OT and contains compromised devices | Prevent attackers from reaching production systems |
| Existing Infrastructure Integration | Pushes policies to firewalls, switches, and NAC systems | Leverage existing investments without rip-and-replace |
Here’s how network segmentation applies across major critical infrastructure sectors:
| Sector | Key Use Case |
|---|---|
| Power and Utilities | Protect SCADA systems, segment substations, and prevent nation-state pre-positioning in energy infrastructure |
| Manufacturing | Secure production lines, isolate legacy PLCs, and stop ransomware from reaching control systems |
| Building Management Systems | Segment BACnet-based HVAC, lighting, and security systems to prevent network entry points |
| Water and Wastewater Treatment | Protect supervisory systems and isolate treatment operations from administrative networks |
| Transportation and Logistics | Secure traffic systems, rail networks, and warehouse automation from operational disruption |
ORDR provides unified visibility across corporate IT, IoT, and operational technology. Security teams, OT engineers, and IT operations work from the same source of truth.
ORDR’s AI has been trained on industrial protocols, including SCADA, Modbus, BACnet, and proprietary control system languages. This enables accurate classification where generic tools fail.
ORDR was built for environments where disruption is unacceptable. Policies are simulated, validated, and deployed safely. Production continues without interruption.
Healthcare systems use ORDR to protect medical devices. Manufacturing plants secure production lines. Critical infrastructure organizations protect SCADA networks. All without causing downtime.
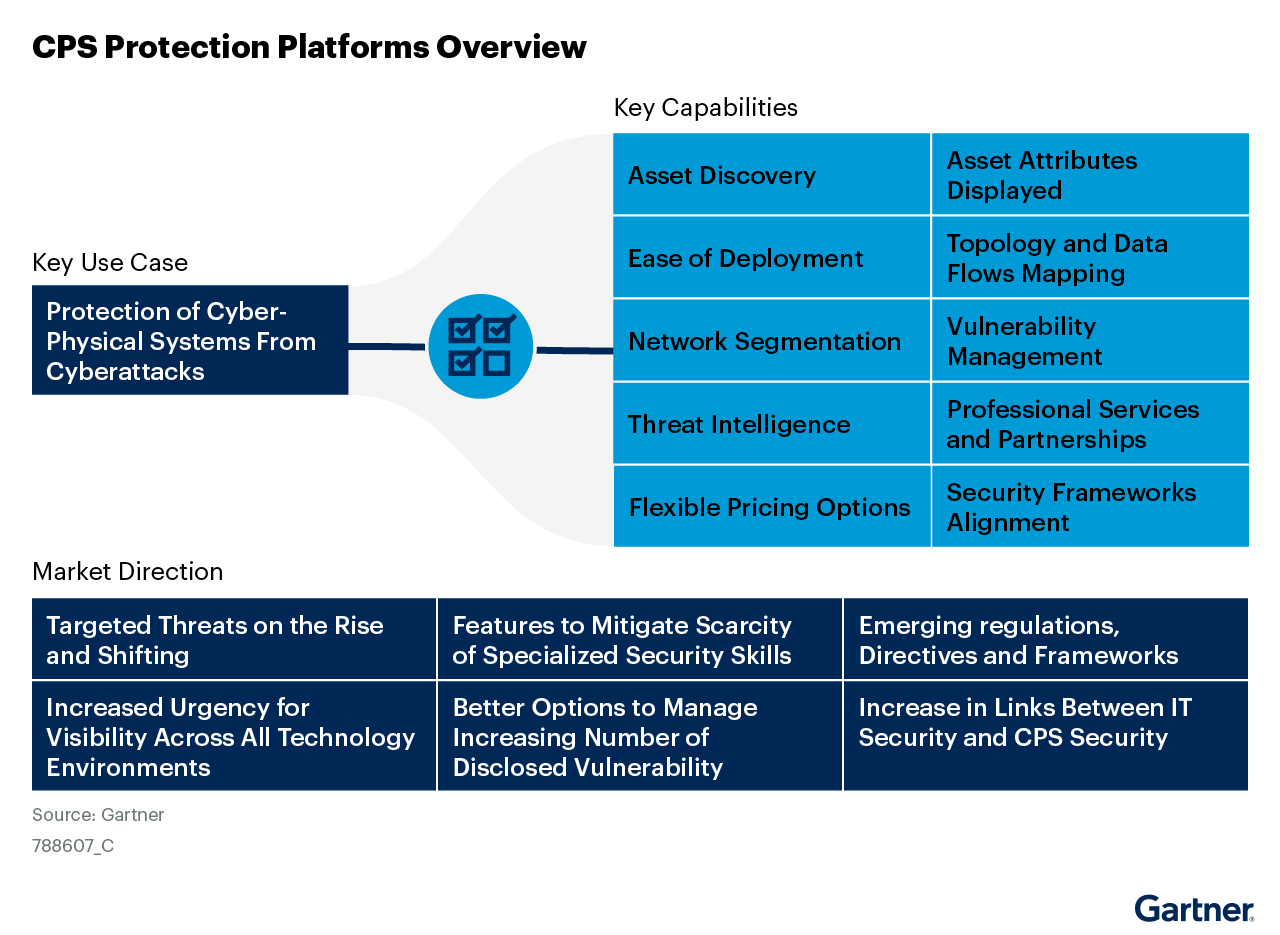
IT/OT convergence creates regulatory obligations. ORDR helps organizations meet requirements:
| Framework | Requirement | How ORDR Delivers |
|---|---|---|
| NIST SP 800-82 | OT security guidelines, including asset management and segmentation | Continuous OT device discovery with validated segmentation policies |
| IEC 62443 | Security levels for industrial automation and control systems | Risk-based device classification with zone and conduit enforcement |
| NERC CIP | Critical infrastructure protection for bulk electric systems | Asset inventory, segmentation, and monitoring for compliance |
| TSA Security Directives | Pipeline and rail cybersecurity requirements | OT visibility and incident response capabilities |
| ISA/IEC 62443-3-3 | Zone and conduit security architecture | Automated policy generation aligned with security requirements |
The following outlines how quickly ORDR moves from visibility to active segmentation:
| Stage | Duration | What Happens |
|---|---|---|
| Discovery | 24–48 hours | ORDR passively identifies IT, IoT, and OT devices across converged networks |
| Intelligence Foundation | ~1 week | Behavioral baselines establish normal device communication patterns |
| Policy Development | Days to weeks | AI generates segmentation policies from real traffic data |
| Validation | Varies by environment | Policies are simulated against live traffic to ensure operational safety |
| Enforcement | Phased rollout | Validated policies deploy to firewalls, switches, and NAC systems |
ORDR works with the security and network tools you already have:
ORDR uses passive network traffic analysis to identify devices based on communication patterns. No agents, no active scanning, no credentials required. Discovery happens without touching production equipment.
Yes. ORDR’s AI recognizes SCADA, Modbus, BACnet, DNP3, and proprietary industrial protocols. This enables accurate device classification in OT environments where generic tools fail.
No. ORDR simulates every policy against live traffic before enforcement. You see exactly what will be affected, validate operational safety, and then push policies with confidence.
Discovery typically completes within 48 hours. Segmentation enforcement timelines vary by environmental complexity, but organizations report deploying policies in weeks rather than the 12–24-month timelines common with legacy approaches.
Absolutely. ORDR was designed specifically for converged environments. The platform provides unified visibility across IT, IoT, OT, and cyber-physical systems while enabling safe enforcement that respects operational requirements.
IT/OT convergence created the problem. ORDR delivers the solution. Discover how protocol-aware intelligence and validated enforcement protect cyber-physical systems without disrupting operations.