SANTA CLARA, Calif., February 17, 2021 — ORDR, the leader in security for all connected devices, has been named a Representative Vendor in the 2021 Gartner Market Guide for Operational Technology Security.
The Gartner Market Guide identifies the convergence of IT and OT, calling for the need to address identifying all network connected devices, understanding how they are communicating and properly assessing the risks associated with them.
According to Katell Thielemann, Wam Voster, Barika Pace, and Ruggero Contu (the authors of the report), “Gartner end-user inquiries suggest that, across all industry verticals except for the most highly regulated, about 60% of organizations are still in the awareness phase, about 30% are in the discovery to firefighting phases, and only about 10% are truly in the integration and optimization phases. The proliferation of OT in a wide number of different verticals, ranging from medical to fast-moving consumer goods, and critical infrastructure further complicates the situation.”
As described in the report, the OT/CPS security journey aligns with six key phases. “Once they enter the “Oh Wow!” Phase [3], organizations realize that security — whether IT, OT, physical or supply chain — needs a whole-of-enterprise focus. Historical IT and OT functional differences are becoming a liability when security is involved. Due to design, age or function, the unique requirements of OT systems now add to IT security concerns in ways that can no longer be ignored. Modernization efforts bring risk, reliability and safety discussions to the forefront. As a result, leading organizations are starting to elevate OT security requirements into their enterprise risk management (ERM) efforts by adopting an integrated security strategy across IT, OT, CPS, physical security and supply chain security.”
Phase 3. “The “Oh Wow!” Moment: Invariably, proof of concepts (POCs) become eye openers. For example:
- Unmanaged assets are connected everywhere.
- OT networks that were initially designed to be highly segregated have become flatter than realized.
- Ports on all kinds of systems in all kinds of remote locations are wide open.
- OEMs are accessing the machines they sold remotely and no one is managing it.
- Disclosed vulnerabilities on old OSs have never been evaluated for possible patching.
- The functional silos between separate security disciplines (e.g., cybersecurity, physical security, supply chain security, product security, health and safety) are creating seams that bad actors can exploit.
- The realization sets in that operational environments where security is lacking are centers of value creation for most organizations; however, no centralized governance exists to start making sense of it all. Recognition develops that roles and responsibilities for a wide variety of (security related) processes and decisions have never been clear, let alone agreed on.”
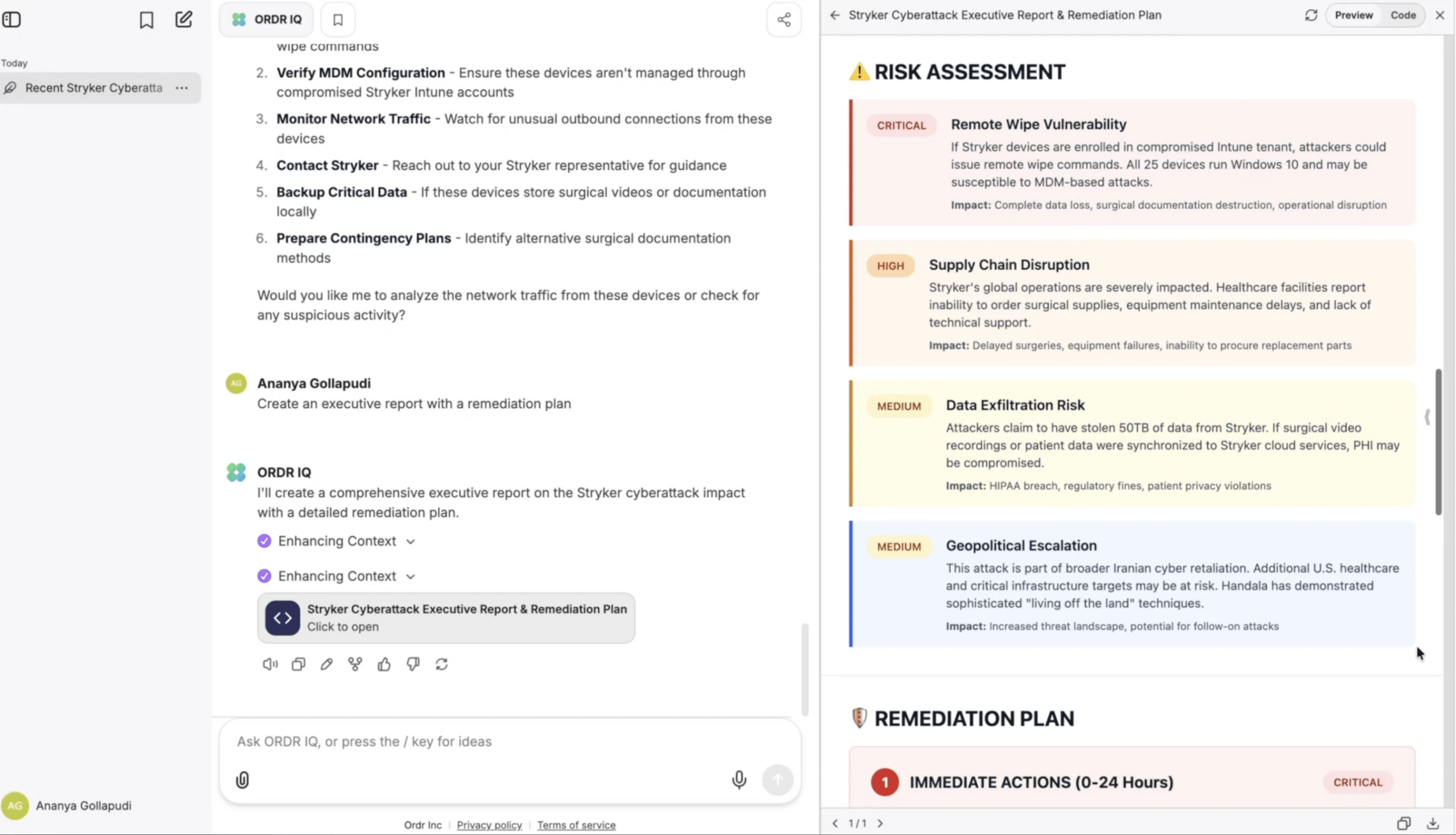
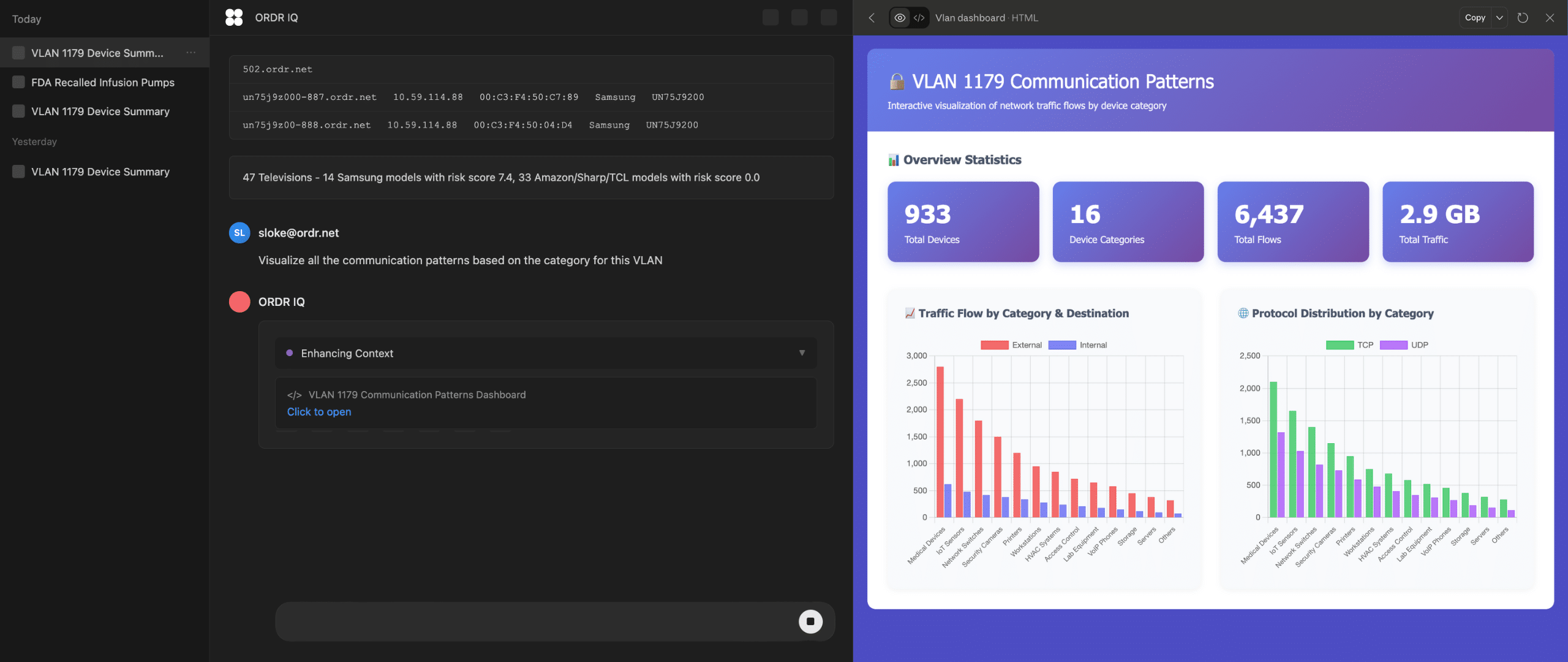
“We take a whole-enterprise approach with our customers, starting with continuous and real-time asset discovery,” said Greg Murphy, CEO of ORDR. “ORDR’s platform is differentiated by our use of deep packet inspection to classify and provide visibility to all the connected devices – from traditional servers, workstations and PCs to IoT and OT devices — that can serve as attack vectors. We not only classify every device, we also profile device behavior using advanced machine learning, to risk score every communication flow and surface anomalies. Further, our customers have access to automated policy creation and proactive segmentation of devices or device groups for business-critical devices that cannot be taken out of service.”
Gartner Disclaimer
Gartner does not endorse any vendor, product or service depicted in its research publications, and does not advise technology users to select only those vendors with the highest ratings or other designation. Gartner research publications consist of the opinions of Gartner’s Research & Advisory organization and should not be construed as statements of fact. Gartner disclaims all warranties, expressed or implied, with respect to this research, including any warranties of merchantability or fitness for a particular purpose.
About ORDR
ORDR makes it easy to secure every connected device, from traditional IT devices to newer and more vulnerable IoT, IoMT, and OT. ORDR Systems Control Engine uses deep packet inspection and advanced machine learning to discover every device, profile its risk and behavior, map all communications and protect it with automated policies. Organizations worldwide trust ORDR to provide real-time asset inventory, address risk and compliance and accelerate IT initiatives. ORDR is backed by top investors including Battery Ventures, Wing, and TenEleven Ventures. For more information, visit www.ordr.net and follow ORDR on Twitter and LinkedIn.

Interested in
Learning More?
Subscribe today to stay informed and get
regular updates from ORDR Cloud