- PARTNERS
- TECHNOLOGY
Enable Faster ROI With Ordr Integrations
Ordr integrates with over 130 security, networking, infrastructure, IT, and clinical solutions to unify device details, enrich device context, and extend the value of your existing investments.
Aruba
With Ordr and HPE Aruba ClearPass Policy Manager (CPPM), organizations can quickly gain complete visibility into every connected device and deploy segmentation to proactively protect and reactively respond and mitigate threats. This includes Zero Trust policy enforcement and microsegmentation to isolate groups or individual devices from non-essential access while protecting them from attack and compromise on existing networking and security infrastructure
How it works
The integrated Ordr SCE and HPE Aruba CPPM solution makes it easy to get rich visibility for IoT and unmanaged devices and to simplify segmentation projects. The solution provides detailed classification and context for every connected device, automatically groups devices into CPPM policy groups for role-based access and facilitates software-defined segmentation to provide more precise controls for every IoT device in the network. By providing continuous, multi-level security monitoring of all device communications, Ordr SCE detects anomalous behavior and shares this information with ClearPass to implement network access control based on vulnerability, threat, and risk ratings. Ordr SCE also integrates with HPE Aruba CPPM to streamline the process of containing threats based on the organization’s access policy such as blocking unauthorized devices, quarantining them, or limiting their network access.
Benefits
- Automating IoT inventory discovery, classification, and categorization, and sharing detailed device context with ClearPass
- Providing rich analytics about the behavior of all devices that guides segmentation design, streamlines the segmentation implementation, and audits the result to assure accuracy and effectiveness
- Quickly contain threats and protect at-risk devices
- Accelerating ClearPass deployments with powerful yet easy-to-use tools that provide accurate device information and automate steps that are traditionally error-prone and labor intensive
CrowdStrike
Integration between Ordr and CrowdStrike ensures the security of all managed and unmanaged devices with comprehensive device visibility, detailed vulnerability insights, an understanding of risk, and the ability to enforce policy to mitigate active threats and improve security across all connected devices
How it works
Ordr analyzes network flow data to automatically discover and classify every connected device, profile behavior, and identify active threats. Security telemetry from the CrowdStrike Falcon platform, is shared with Ordr to enhance device insights, and provide a centralized, deep understanding of each device and its associated risk. Ordr uses multiple factors to calculate risk for each device based on business context, asset criticality, vulnerabilities, and overall threat details. With additional device data from the Falcon platform, Ordr provides a highly accurate risk score for each device. By continuously synchronizing device risk scores with CrowdStrike’s enriched security data, Ordr enables teams with an up-to-date view of risk to help them focus on the most critical devices.
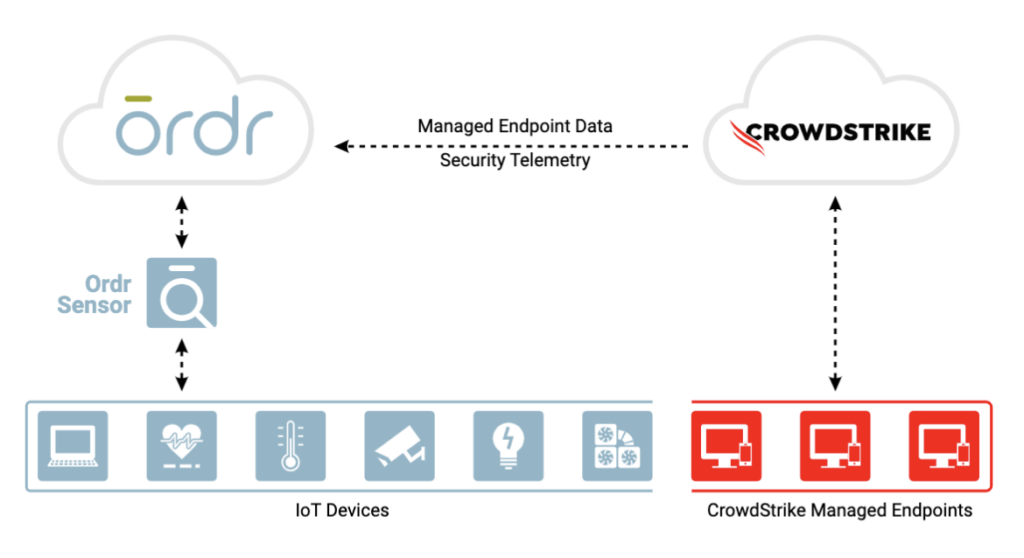
Benefits
Gain complete device visibility
- See into all devices – agentless and agent-based
- Track both online and offline devices continuously
- Identify unmanaged devices without CrowdStrike agent for compliance
Minimize risk with better insights
- Improve Ordr risk score accuracy with supplemental event data from CrowdStrike
Remediate faster
- Improve threat detection and incident response time with a combination of Ordr endpoint flow & CrowdStrike process data
- Block/quarantine/segment managed endpoints in Ordr for rapid remediation via the network
Fortinet
Fortinet and Ordr have partnered to deliver an industry-leading IoT and unmanaged device security solution by integrating FortiManager, FortiGate and FortiNAC with Ordr Systems Control Engine (SCE)
How it works
Automated Visibility and Security of All Connected Devices
Ordr SCE automatically creates a complete asset inventory, identifies and prioritizes asset risk, and tracks and risk-rates asset communications patterns. Ordr transmits this critical security context to Fortinet FortiGate, FortiManager, and FortiNAC, allowing administrators to create and apply firewall and NAC policies using business-relevant groups, classifications, and device names, while understanding the full risk profile and impact of each change. Ordr further reduces administrative costs by automatically updating asset groupings as devices join and leave the network, as well as by creating and transmitting security policies directly to FortiGate and FortiManager for enforcement.
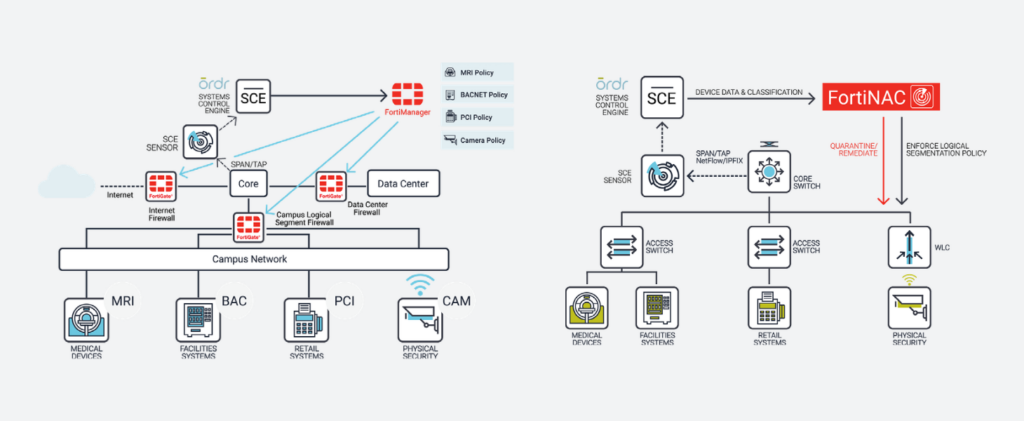
Benefits
With the integration, joint customers can now:
- Discover and inventory every connected network asset, including the massive volume of IoT and unmanaged devices, and make available across the Fortinet Security Fabric, from endpoint to edge, through FortiNAC, FortiManager, and FortiGate
- Establish comprehensive security controls that restrict IoT devices to known-good network behaviors
- Manage firewall and NAC policies using business-relevant context such as device type, manufacturer, location, risk, and function rather than IP addresses
- Automate updates of firewall groups and address info to ensure consistent policy enforcement regardless of device location, VLAN, or IP assignment, thus drastically reducing operational costs and downtime
- Protect critical devices with automated, zone-based segmentation and microsegmentation within zones
SentinelOne
Ordr integration with SentinelOne enables collection of managed device data, vulnerabilities and threat insights for comprehensive device visibility and a better understanding of risk.
How It Works
Ordr discovers and secures every connected device—from traditional IT to new or vulnerable IoT, IoMT, and OT devices. With the SentinelOne integration, Ordr collects managed device data, vulnerabilities, and threat insights from the Singularity Platform delivering comprehensive device visibility, a better understanding of risk, and the ability to enforce policy to mitigate active threats and improve security across all connected devices.
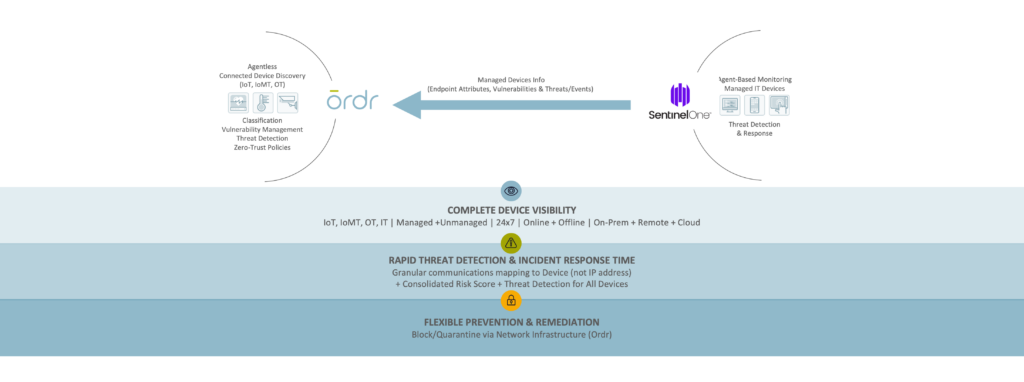
Benefits
Gain Complete Device Visibility
- See granular details for all agentless and agent-based devices.
- Track both online and offline devices continuously.
- Identify unmanaged devices without the SentinelOne agent to meet compliance requirements.
Minimize Risk with Extended Insights
- Improve risk score accuracy with supplemental event data from SentinelOne.
Remediate Faster
- Improve threat detection and incident response with combined Ordr endpoint flow and SentinelOne process data.
- Block/quarantine/segment managed endpoints in Ordr for rapid remediation via the network.
Gigamon
A basic tenet of network security and regulatory compliance is that “You cannot secure what you cannot see.” Gigamon and Ordr have teamed to deliver unsurpassed visibility and control into every thing connected to your network.
How It Works
The Gigamon Visibility and Analytics Fabric (VAF) optimizes data collection of all north-south and east-west traffic across branch, campus, data center and cloud. Collected data is delivered to Ordr for analysis to ensure comprehensive device classification and visibility into all device communications. Integration with Gigamon VAF also eliminates concerns of SPAN security and potential impact to network infrastructure with “yet another SPAN port or session.”
By integrating with Gigamon VAF, customers can significantly reduce the number of Ordr sensors required to comprehensively discover and monitor every network-connected device, simplifying your network and security monitoring architecture.
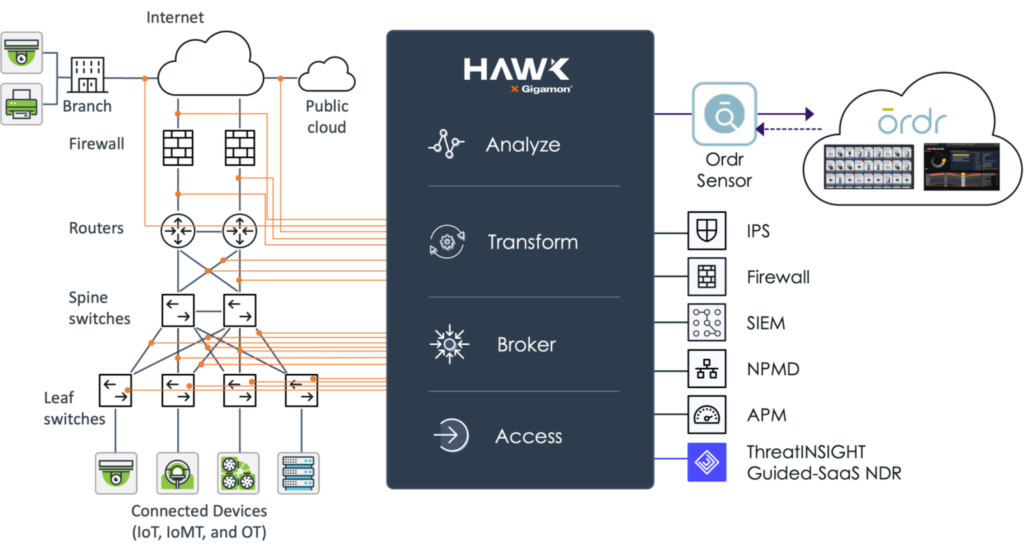
Benefits
- Real-time asset inventory – Ordr continuously analyzes device traffic sent from Gigamon to passively discover an automatically classify every device connected to the network to help you maintain an up-to-date and accurate inventory.
- Connected device risk – using the traffic captured and optimized by Gigamon Hawk, Ordr calculates device risk scores and uncovers connected devices with risk such as outdated operating systems, unpatched software, weak passwords, and manufacturer recalls. Ordr also maps and baselines device communications to identify risk and stop attacks.
- Accelerate Zero Trust – working together, Gigamon and Ordr can map and baseline all IT, IoT and other device communications. Ordr can then dynamically create Zero Trust policies to simplify and accelerate NAC and segmentation projects. These policies can be enforced with popular security and network devices to integrate with existing infrastructure tools.
Palo Alto Networks
Rapid7
Ordr works with Rapid7 to seamlessly discover all connected assets including IoT, IoMT, and OT devices. The joint solution enables Rapid7 to perform the right scan at the right time regardless of the device type, location, criticality or role within the organization. Many vulnerable IoT/OT devices discovered by Rapid7 cannot be patched or updated. Ordr automates the application of compensating controls to safeguard these devices by sending protection policies directly to firewalls, switches, wireless, or NAC systems. Similarly, infected devices can be quickly isolated through existing network and security devices.
How It Works
The integration with Ordr and Rapid7 InsightVM provide ongoing bi-directional synchronization for managing vulnerabilities with rich device context. Ordr discovers every connected device, profiles device behaviors and risks, and automates remediation responses. Rapid7 InsightVM provides visibility into the vulnerabilities and clarity on how those vulnerabilities translate into business risk. Combining Ordr’s unique device intelligence with Rapid7’s advanced vulnerability intelligence provides organizations with the ultimate solution to efficiently manage risks while reducing service disruption and time to remediate.
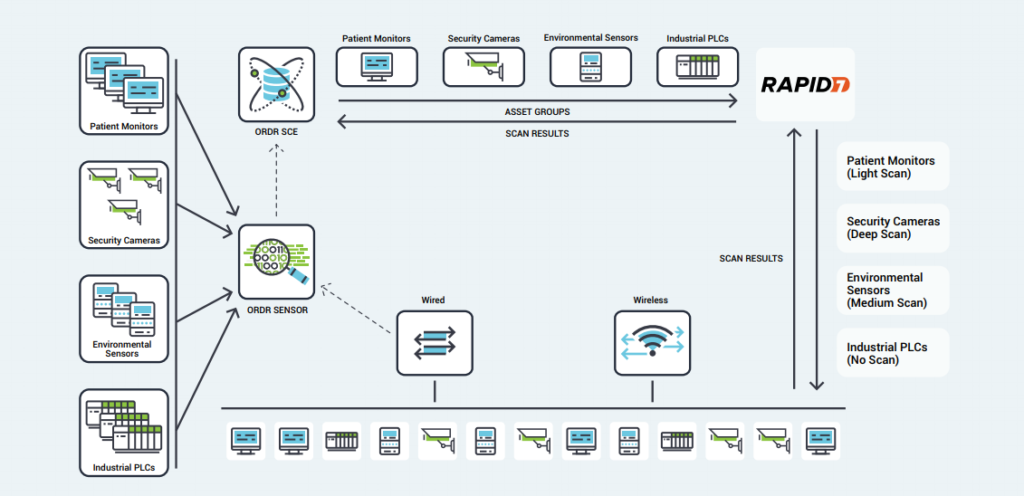
Benefits
- Comprehensive Coverage – Ordr’s identification and classification of lightweight, agentless devices allows administrators to quickly exclude specific IoT devices or categories from active Rapid7 scans, opening network segments to vulnerability scanning that had previously been excluded.
- Optimized Scanning – Using Ordr’s detailed insight into device types, scan sensitivity, and their critical role within the organization, Rapid7 scans can be tailored to each device.
- Proactive Protection – Rather than blocking or quarantining critical IoT devices after infection, Ordr’s segmentation policies create barriers that protect vulnerable devices while still enabling essential services.
- Smart Scheduling – Ordr tracks utilization patterns for critical devices, allowing administrators to schedule vulnerability scans for times when devices are not in use, minimizing disruption and operational risk.
Splunk
Ordr integration with Splunk allows you to leverage Ordr’s rich device data to create alerts, reports, and custom analyses. Ordr transmits security alerts, device information, and other critical information. Splunk ingests the feed for better event management.
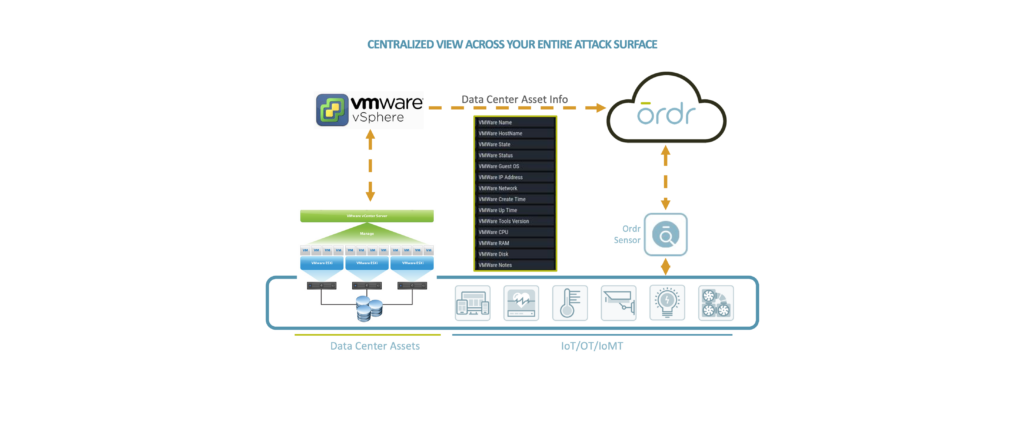
VMware
Ordr leverages the vSphere API, which provides access to server management, virtual machine provisioning, monitoring, and more. Ordr collects datacenter asset details including the servers (hosts), individual virtual machines (guests), operating systems, shared compute resources (CPU, memory, disk), status, and compatibility.
The extended visibility to VMware workloads running in public, private, and hybrid cloud environments delivers a ‘whole hospital’ or ‘whole enterprise’ approach to security ensuring that no device or connection remains unknown.
Microsoft
Ordr integrates with multiple Microsoft solutions to enhance device context and improve risk insights to keep your organization secure.