Policies take too long to create
AI PROTECT FOR SEGMENTATION
Zero Trust Enforcement That Actually Works
Turn Intelligence Into Safe, Continuous Protection, Without Disrupting Operations
Most organizations can identify their security gaps. ORDR AI Protect for Segmentation helps you close them by translating authoritative asset intelligence into enforced micro-segmentation policies that contain exposure, prevent lateral movement, and protect critical systems, all without causing downtime.
ORDR AI Protect for Segmentation: Intelligence Becomes Enforcement
ORDR turns segmentation into a living, adaptive system built on real device behavior rather than static assumptions.
Instead of relying on manual policy design and guesswork, ORDR:
-
Generates policies automatically based on real traffic and device behavior
-
Simulates impact before enforcement using a live communication matrix
-
Adapts continuously as devices, roles, and risks change
-
Enforces policies through your existing infrastructure, no rip-and-replace required
The result is segmentation that can actually be enforced, safely, quickly, and at scale.
From Behavior to Enforcement, Safely
ORDR transforms segmentation from a manual project into a continuous, validated system. No guesswork.
No downtime. No multi-year rollout.
| Segmentation Phase | Benefits |
|---|---|
| Understand Real Device Behavior |
Policies are built from how your environment actually operates, not assumptions.
|
| Automatically Generate Policies |
Create least-privilege policies without manual effort.
|
| Validation Before Enforcement |
Test policies safely before applying them.
|
| Enforce without Disruption |
Apply policies through the infrastructure you already trust.
|
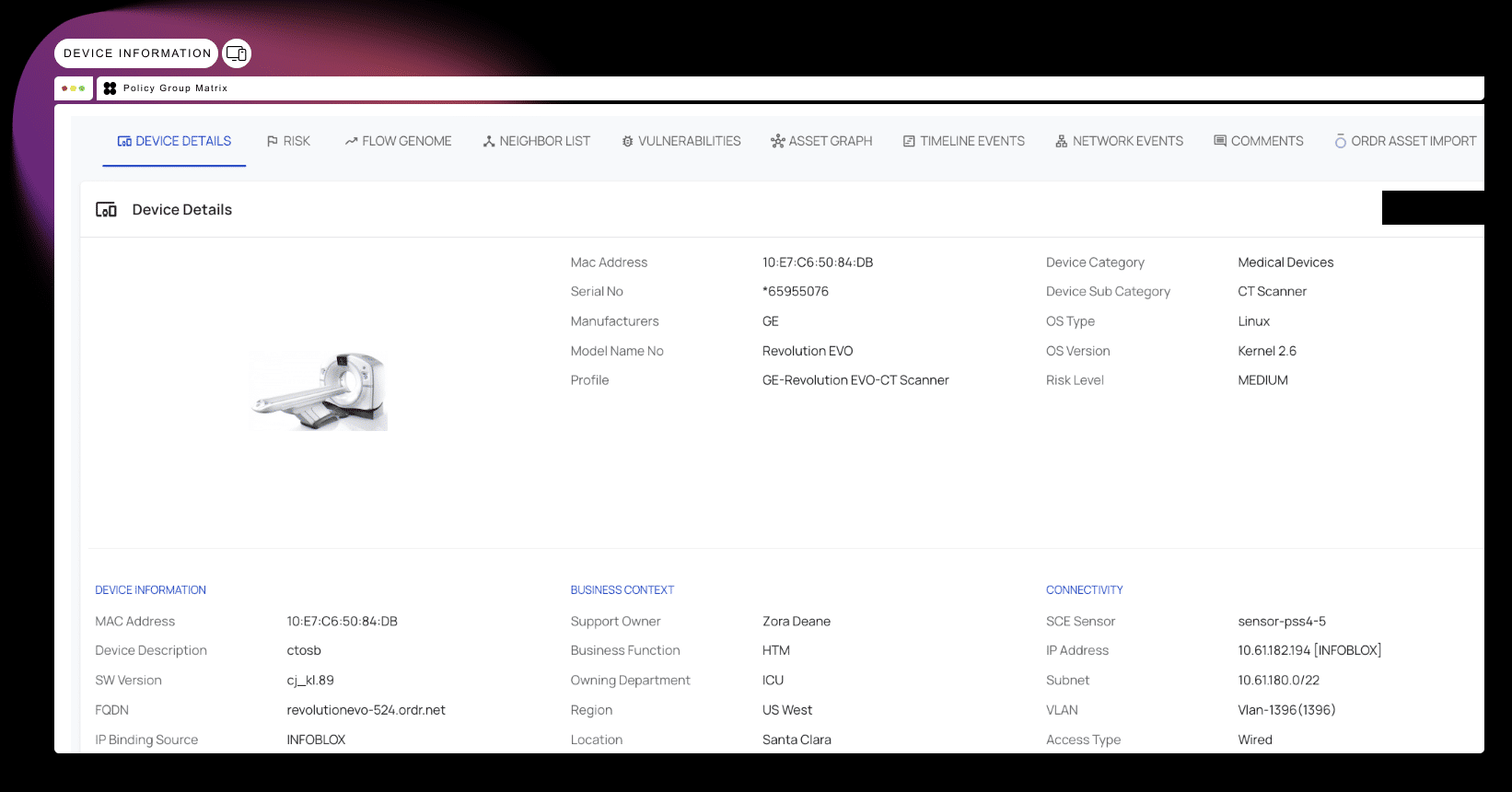
Built on Authoritative Intelligence You Can Trust
What makes ORDR different is the foundation: AI Protect for Security establishes a single, authoritative source of truth about every connected device across your environment.
This intelligence is:
Because everyone operates from the same reality, enforcement decisions can be made with confidence before risk becomes an incident.
Zero Trust Segmentation at Enterprise Scale
Segmentation That Keeps Up With Your Environment
Traditional approaches rely on static policies and manual updates. ORDR continuously adapts, so protection stays aligned with how your network actually behaves.
| Capability | How ORDR Delivers | Benefits |
|---|---|---|
| Behavior-Based Policies | Built from real traffic, not templates | Accurate policies that don’t require constant rework |
| Dynamic Segmentation | Updates automatically as environments change | Protection that doesn’t drift over time updates |
| Least-Privilege Enforcement | Granular control across all connected devices | Reduced blast radius without operational impact |
| Simulation Before Enforcement | Simulates real-world impact before applying policies | Safe enforcement, even in high-risk environments |
Enforcement Through the Infrastructure You Already Trust
ORDR doesn’t replace your infrastructure; it activates it.
Policies are translated into controls and pushed directly to the systems already enforcing traffic in your environment.
No new enforcement layer to deploy
No gaps between policy and execution
No vendor lock-in
Just consistent, real-world enforcement, across what you already have.
It integrates seamlessly with:
Firewalls
- Cisco
- Palo Alto Networks
- Fortinet
- Check Point
Network Access Control
- Cisco ISE
- Aruba ClearPass
- Forescout
Switches
- Cisco
- Aruba
- Juniper
Wireless Access Points
- Enterprise WAP infrastructure
SIEM/SOAR
- Splunk
- IBM QRadar
- Microsoft Sentinel
Why ORDR AI Protect for Segmentation is Different
Built to Enforce, Not Just Recommend
Most solutions stop at visibility and policy recommendations. ORDR is built to take the next step, turning intelligence into safe, continuous enforcement.
What sets ORDR apart:
Enforcement, Not Just Insights
- Other platforms show you what to fix. ORDR ensures it gets done.
- Policies don’t sit in dashboards
- No manual translation from recommendation to action
- Enforcement happens through your existing infrastructure
Safe by Design for Production Environments
- Segmentation only works if it can be enforced safely.
- Policies are simulated and validated before enforcement
- Impact is understood before changes are applied
- Built for environments where downtime isn’t acceptable
Built on Real Behavior, Not Templates
- Static policies don’t reflect how networks actually operate.
- Policies are generated from real traffic and device behavior
- Automatically adapt as environments change
- No reliance on generic templates or manual mapping
No New Enforcement Layer Required
- ORDR doesn’t add complexity; it uses what you already have.
- Enforces through firewalls, NAC, and network controls
- No rip-and-replace
- No gaps between policy and execution
This isn’t segmentation as a project.
It’s segmentation as a continuous system of action.
Real Results From Real Organizations
“The power of the ORDR platform has always been its ability to automate device classification and behavioral modeling using AI. This is foundational to our Zero Trust and segmentation strategy.” — Larry Smith, Manager Cybersecurity Architecture and Engineering, El Camino Health
“It’s eye-opening when you put something like ORDR on your network. It has improved our incident response capabilities.” — Jay Bhatt, CISO, Franciscan Alliance
Segmentation in Days, Not Years
Traditional segmentation projects take months to design, validate, and safely enforce.
ORDR accelerates the process, so you can move from visibility to enforcement much faster.
How we accelerate deployment:
-
AI-generated policies: Automatically created from real traffic and device behavior, eliminating weeks of manual design
-
Built-in Simulation and Validation: Test policy impact before enforcement to ensure operational safety
-
Streamlined Enforcement: Push validated through your existing infrastructure, without rebuilding your network
-
Continuous adaptation: Policies evolve as devices and behaviors change, reducing ongoing maintenance
Frequently Asked Questions
How is ORDR different from visibility-only platforms like Armis or Claroty?
Visibility platforms are very effective at identifying assets, risks, and exposures.
But acting on that information still requires additional tools and manual coordination.
ORDR combines visibility with enforcement, so the same intelligence used to identify risk can be used to safely reduce it
How is ORDR different from segmentation-only tools like Elisity?
Segmentation requires accurate, continuously updated device intelligence to be effective.
Segmentation-only tools rely on external data sources, which can introduce gaps or inconsistencies.
ORDR brings intelligence and enforcement together, so policies are based on a single, trusted source of truth.
Can ORDR work in environments where downtime isn’t an option?
Yes. ORDR is designed for environments where disruption isn’t acceptable, including healthcare, manufacturing, and critical infrastructure.
Policies are simulated and validated before enforcement, so teams can understand the impact and move forward safely.
How long does deployment take?
Most organizations gain visibility within 24-48 hours.
From there, segmentation policies can be generated quickly and rolled out in a controlled manner.
Deployment timelines vary by environment, but teams can move significantly faster than traditional approaches.
Will enforcement break production systems?
ORDR is designed to minimize that risk.
Policies are simulated using real traffic before enforcement, allowing teams to see exactly what would be impacted.
This enables validation and adjustment before anything is applied in production.


