As the war in Ukraine broke out in late Feb, security teams around the globe took notice. Russia has long been a focus in the fight against cybercrime, and their aggression raised concerns to new levels with fears that cyberattacks could increase with a focus on the US and other western countries. On March 21, 2022, President Biden confirmed the rising concerns with a statement warning of a potential increase in Russian cyber activity targeting the US, allies, and partners. As organizations across the globe were taking steps to improve cyber defenses, we heard from many of our customers asking what ORDR could do to help improve security, threat prevention, and the ability to monitor their environments. A primary requirement was the ability to identify devices in their environments that had communications with potentially malicious Russian sites.
By continuously analyzing network data, ORDR uncovers all connected device communications within an organization as well as communications to external sites. We also assess the risk for these communications and provide that insight to every customer in our UI. To make these insights a little easier to access, we created a focused report that our customers could run to get a quick view of the exact flow level details of medical devices communicating with Russian sites and assess the risk. You can learn more about the report in this video:
While our customers could collect some of this data from various tools across their environment, only ORDR combines communication insights with device context. This triangulation methodology from multiple sources helps them understand the risk of communication and provides them with the details needed to pinpoint the device at risk and quickly craft the proper response to eliminate the threat.
Helping Everyone Understand the Risk
ORDR's continuous analysis of network data and the report highlighting communications to Russia is available to all ORDR customers, providing necessary details to help them understand and quickly respond to potential threats. We also wanted to share our insights beyond ORDR's customers to help others understand the potential risk to their environment.
The threats uncovered below focus on medical devices; however, these threats are not limited to just medical devices or the healthcare industry. Attackers target connected devices in all industries, including manufacturing, financial services, retail, and utilities. Attacks not only target medical devices but also operational technology (OT) devices such as HVAC systems, elevator controls, and connected cameras that are common across all industries. Many of these devices are critical to business operations even if it seems there is no direct connection, and a successful breach could have a significant impact. For example, an attack that takes an HVAC system offline could create unsafe conditions in the emergency ward and hamper patient care.
Before getting into the details of our findings, here's an extremely brief overview of how ORDR works and some of the details we uncover for each device:
Device Insights Provided by ORDR
ORDR analyzes data collected from multiple points in the network to discover every connected device. We also uncover details to accurately classify every device and identify devices with vulnerabilities and potential threats. With our approach to collecting and analyzing network data we provide granular device insights without the need for agents or scanning and no impact on device operations.
ORDR insights help customers understand the exact devices connected in their environment, how those devices fit into the organization, and their potential risk. ORDR device details include:
- MAC Address – Important detail but identifying a device by its MAC alone can be limiting and misleading.
- IP Address – Since IP addresses can change, ORDR provides a historical view of a device's IP addresses.
- Operating System – Helps to identify devices running an outdated or unpatched OS.
- Device Profile - Includes the manufacturer and model.
- Device Group – How the organization has grouped the device and its role in the environment (e.g., medical, mobile, office equipment, facilities).
- Device Type – Details including exact model number and firmware version to understand specific threats that may impact the device.
- Device Category – The type of device (e.g., CT scanner, infusion pump, patient monitor)
- Device Location – The exact physical and network location including the switch/port or access point/SSID the device connects to.
Communication Insights Provided by ORDR
ORDR also uncovers internal and external communication insights for each device by analyzing network data. This post focuses specifically with devices communicating with Russian sites but could also be used to identify communications with other restricted or high-risk countries. ORDR insights specific to devices communicating with external sites include:
- Destination IP - IP address of the site communicated with.
- Destination Domain Name - Domain name of the site communicated to.
- Destination City - Approximation of the site's city. NOTE: Obfuscation techniques will impact accuracy (e.g., The Onion Router (Tor), VPN, etc.).
- URL - Complete the URL of the communication.
- URL Category - Category of the site (e.g., gaming, shopping, advertising, government, military, etc.).
- Reputation score 1 - URL reputation derived from a leading threat feed.
- Reputation score 2 - URL reputation derived from another leading threat feed.
- Receive Bytes - Number of bytes received by devices from the site.
- Transmit Bytes - Number of bytes transmitted to the site from devices.
- Last Activity - Timestamp of the last activity from devices to or from the site.
- Incident Type – Classification of the destination site (e.g., malicious URL, SPAM URL, etc.).
- Incident Score – Determined by aggregating multiple factors of device communications
- Aggregate Score - Determined by aggregating multiple factors of a device and its communications (e.g., vulnerabilities based on OS version, east-west communication analyzed using IDS signatures, external communication with malicious websites, etc.).
- Risk State - Overall assessment of device risk and potential impact to the organization (i.e., Critical, High, Medium, Low).
ORDR Analysis and Findings
For the insights that follow, the ORDR platform performed deep analysis on data aggregated and anonymized from 50 large health care chains, each consisting of multiple hospitals. The details below focus on medical devices used in healthcare settings such as infusion pumps, patient monitors, EEG/ECG, MRI/CT scanners, X-Rays, ultrasounds, medical gateways, medical workstations running medical apps, medical servers used to process and store patient data, and other connected device in the clinical setting delivering patient care. As mentioned previously, these threats are not limited to healthcare devices or the healthcare industry.
The goal of this analysis is to shed light on the potential threats so that organizations across all industries can be better prepared and take proper steps to secure their environments.
NOTE ON METHODOLOGY
- All data was aggregated and anonymized before analysis. None of the following details pertain to a specific customer, manufacturer, or device.
- Network Time Protocol (NTP) is a required service, and some devices may have legitimate reasons to communicate with Russian hosted NTP servers. Communications to Russian NTP sites have been removed from this analysis.
Top Russian Domains by Traffic
The first analysis highlights Russian domains that were identified for sustaining the highest levels of traffic into and out of the organizations we analyzed. While these domains may look somewhat benign, each may have the potential to be used to distribute malware or perform other malicious activities. Many of these sites are known to generate intrusive online ads and collect personal information. Device communications to any of these domains should be scrutinized to determine if communication is required and expected.
- *.yandex.ru
- *.ssp.rambler.ru
- ssp.adriver.ru
- sm.rtb.mts.ru
- *.rutarget.ru
- counter.yadro.ru
Devices Communicating with the Largest Number of URLs
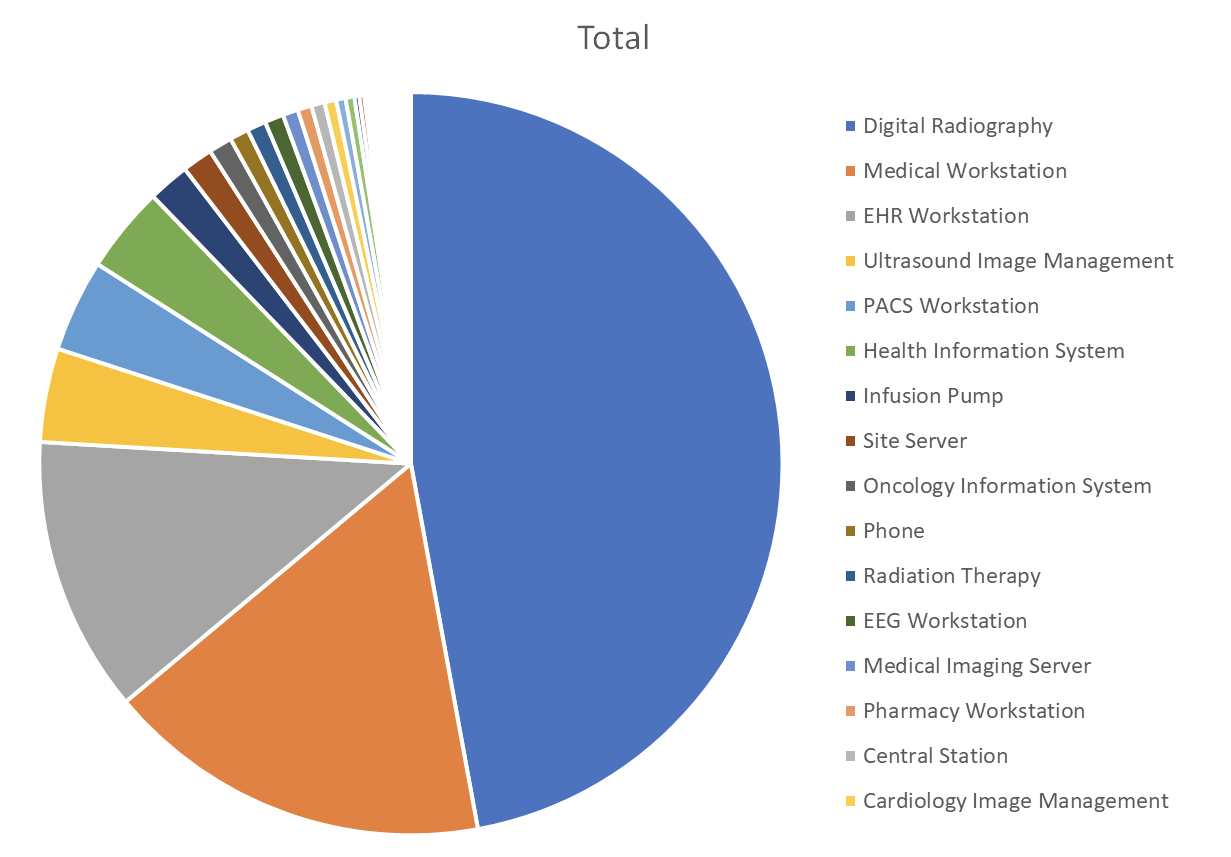
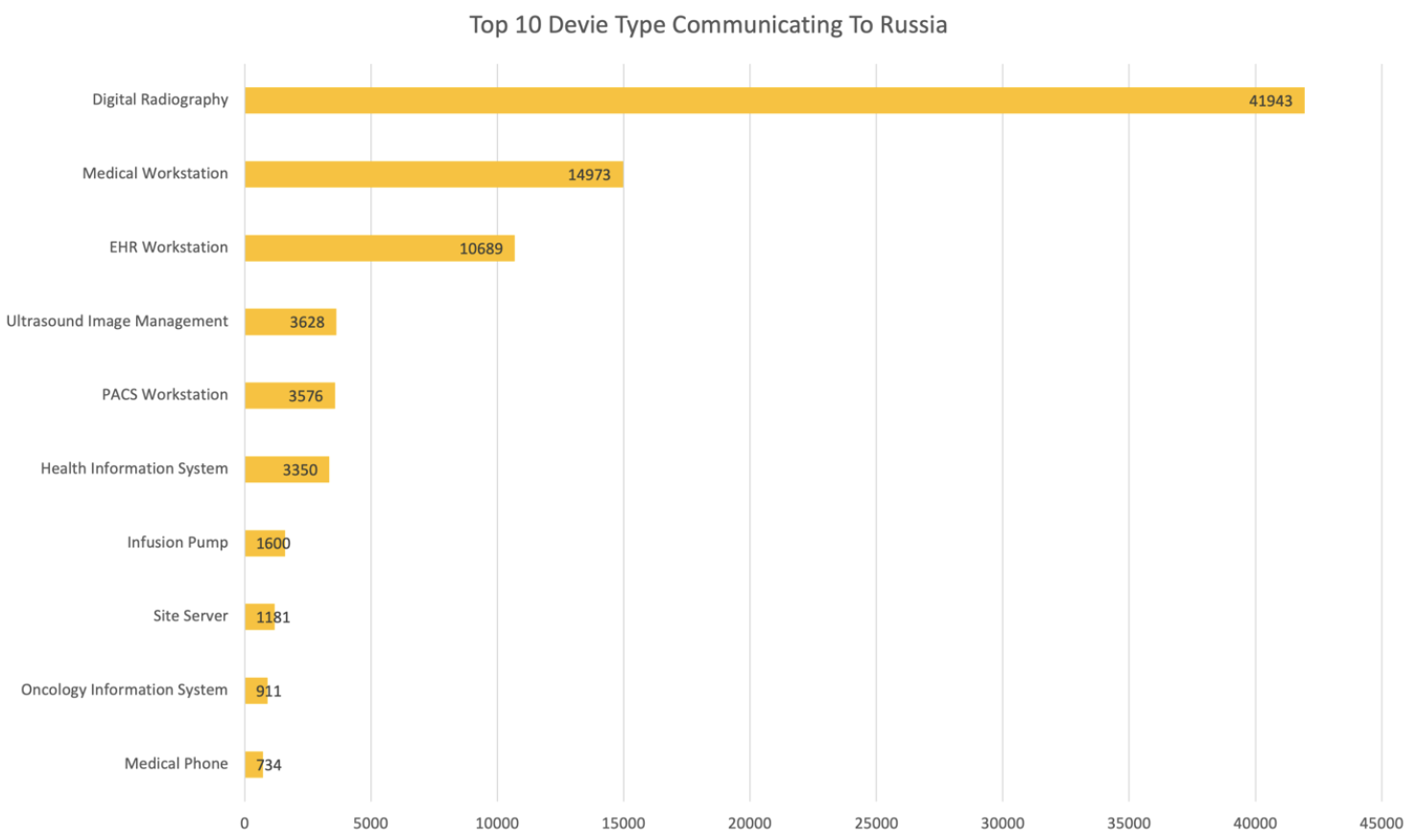
The next analysis identifies device types that have communications with the largest number of Russian URLs. Many of these devices perform critical functions in healthcare environments and we can infer these types of devices are top targets for attackers.
Devices Communicating with the Smallest Number of URLs
The following medical device types have communications with the least number of Russian URLs compared the devices listed above. Like the devices above, many of these devices provide critical functions in healthcare environments and although they communicate with fewer Russian URLs, this activity should still be scrutinized to determine if communications are required and expected.
- Video Digitizer Recorder
- Coagulation Meter
- Perimetry System
- Blood Gas Analyzer
- Radio Fluoroscopy
- Surgical System
- X-ray Volume Imaging
- MR Image Analysis System
- Mobile X-ray System
- Molecular Diagnostics System
- ECG
- Anesthesia Cart
- Hematology Analyzer
- Digital Radiography System
- EEG
- PET/CT System
- Computed Tomography
- PET Scanner
- Patient Monitoring
- Mammography
- MRI Analyzer
- Dental X-ray System
- X-ray System
- SPECT System
Devices with the Most Received Data on a per Device Basis
Focus using our analysis on individual devices, the following details highlight the device types with the most amount of data received from Russian sites per device. Even if outbound communication is blocked by a firewall, the fact that these devices are receiving this volume of data from Russian sites should be of concern, and communication should be scrutinized to determine if communications are required and expected.
Device Category (Received bytes per device)
- CT Scanner (700K)
- Infusion Pump (160k)
- Medical Workstations (95K)
- X-Ray (47K)
- CT Scanner (21K)
- Hematology (19K)
- PACS (22K)
- Radiotherapy (7K)
- Ultrasound (5K)
Device Categories with the Most Received Data
Since a single organization may have multiple units of each device, we aggregated and analyzed device data to highlight the device categories with the most amount of data received from Russian sites. As with the other categories these devices provide critical functions in healthcare environments.
- EEG Workstation
- Ultrasound Image Management
- Infusion Pump
- Glucose Monitor
- Medical Workstation
- EHR Workstation
- PACS Workstation
Device Categories with the Most Transmitted Data
Since a single organization may have multiple units of each device, we aggregated and analyzed device data to highlight the device categories with the most amount of data transmitted to Russian sites. These devices provide critical functions in healthcare environments and are also found in the list above, highlighting device categories receiving the most data from Russian sites.
- Ultrasound Image Management
- EHR Workstation
- Medical Workstation
- PACS Workstation
- EEG Workstation
- Infusion Pump
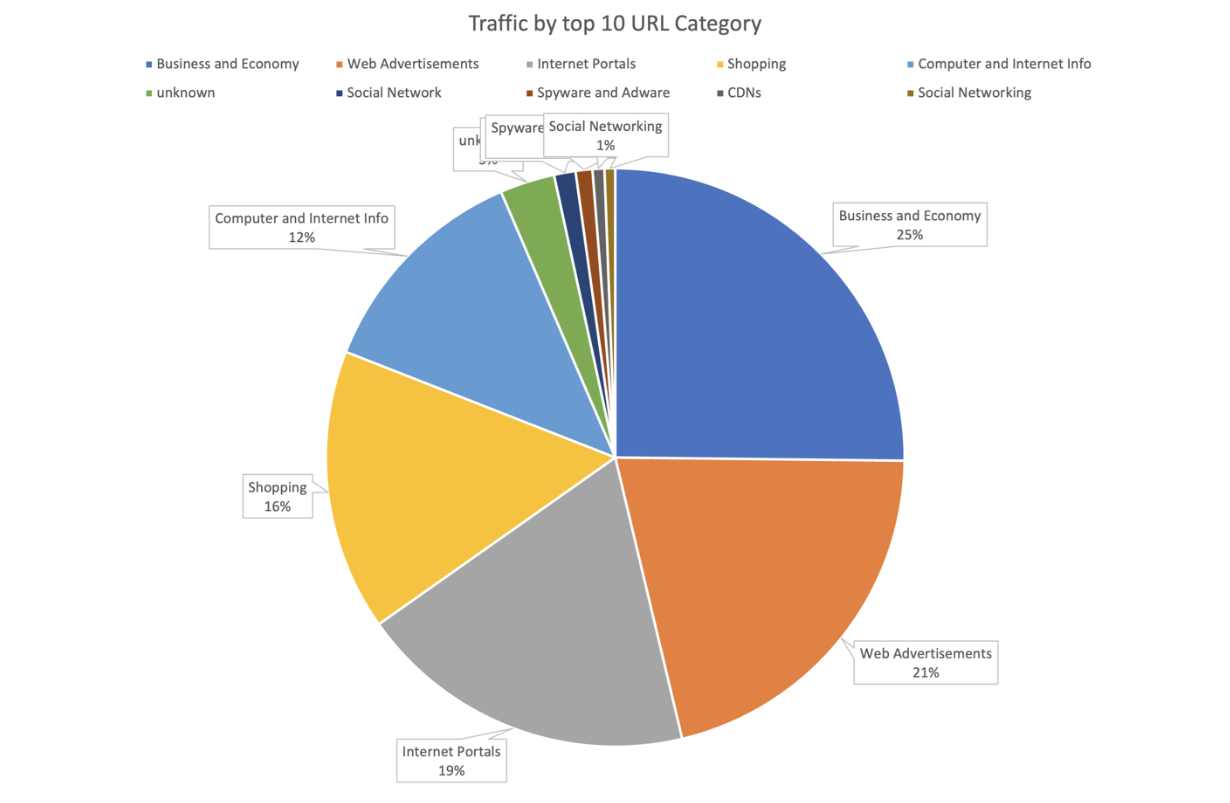
Categories of Sites Communicating the Most with Medical Devices
Looking at the types of Russian sites communicating with the device data we analyzed, the following shows the distribution of site categories communicating with medical devices. As with the Top Russian Domains by Traffic analysis above, many of these categories may look benign; however, each may have the potential to be used to distribute malware or perform other malicious activities.
Device Types and Reputation Score of Sites
Looking at the reputation score of destination URLs, the following chart highlights device types and the reputation of the Russian sites they communicate with. Sites with a low reputation score (e.g., 10) are determined to be very suspicious with a high probability of being malicious. As an example, these sites could host a Command and Control (C&C) server and a connection could be used to download malware such as ransomware to a device and orchestrate the spread across an environment.
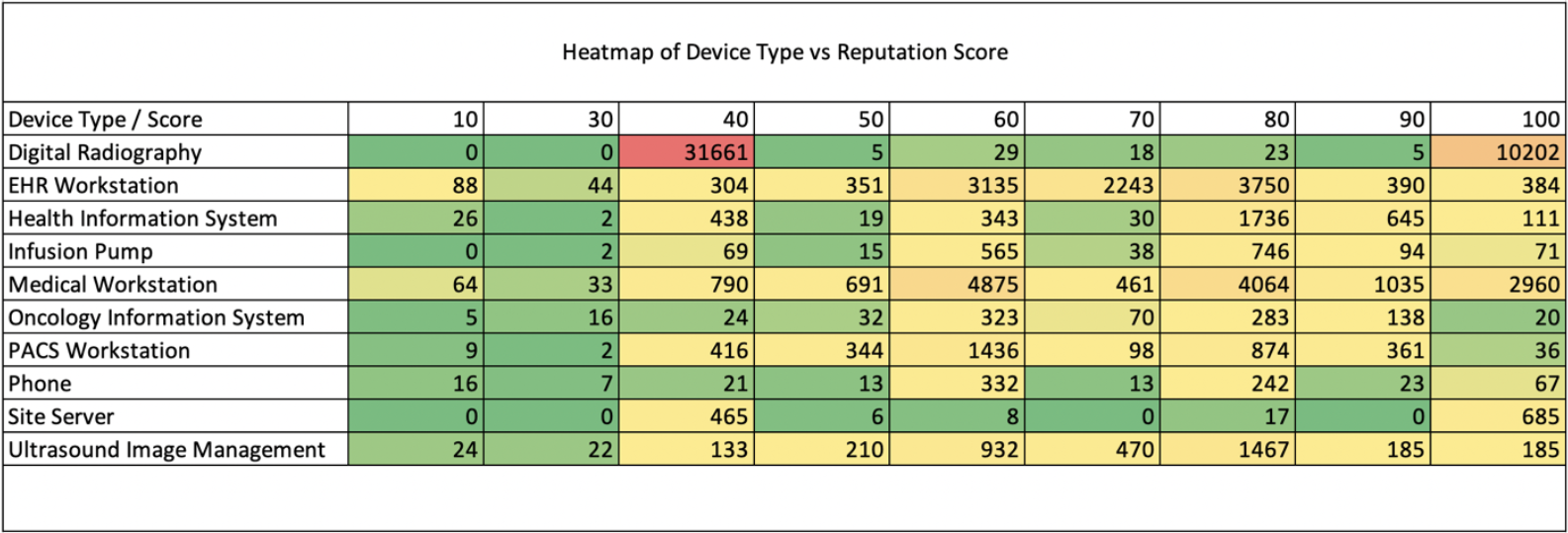
Malicious Russian Site Example
The site counter.yadro.ru is a known malicious site advertisement that has had several reports in the past of downloading malware. The following device types analyzed had frequent transactions with this site.
- Patient Monitor
- PACS Workstation
- EEG Workstation
- Blood Analyzer
Here is a list of the offenders by device type with the number of URLs they are reaching out to.
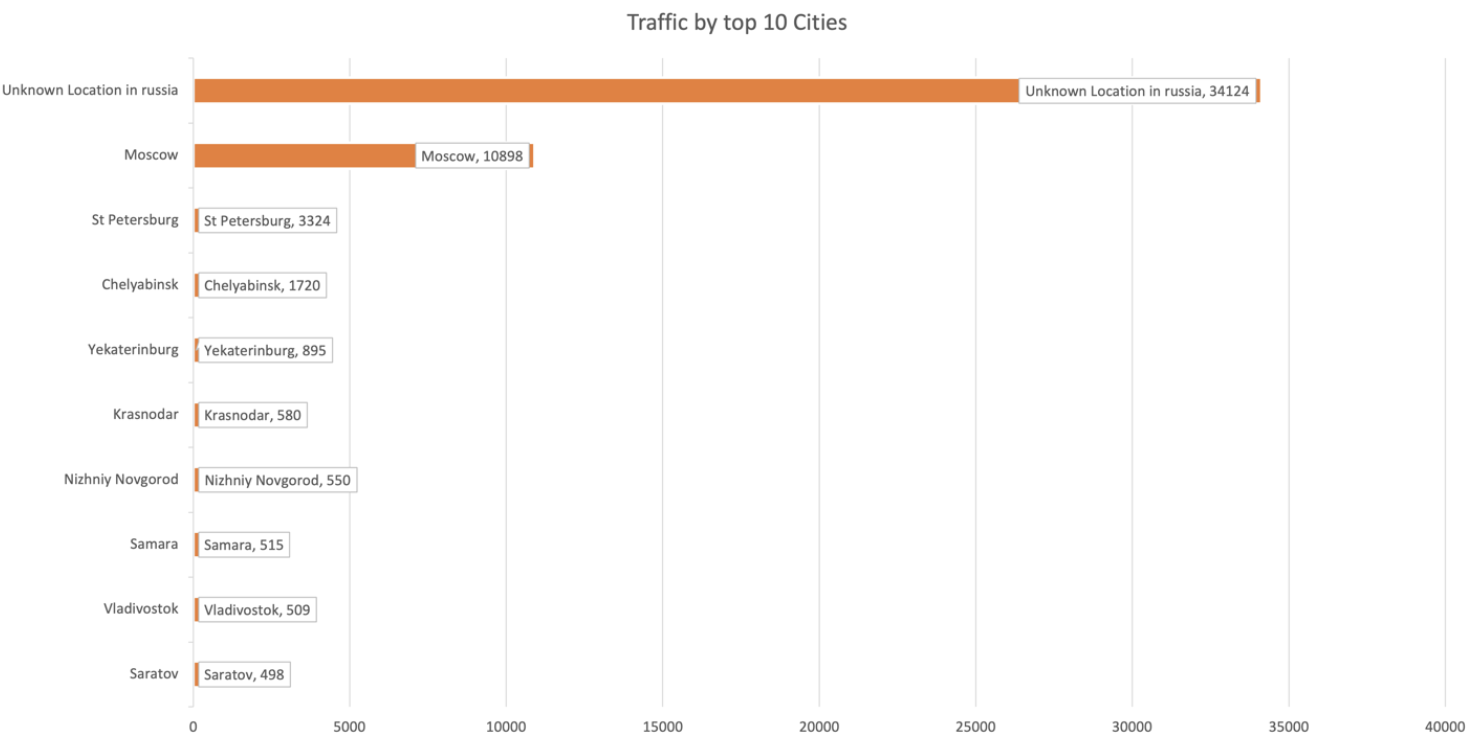
Cities With the Most Communications
The following analysis highlights the top Russian cities with the most traffic to and from the devices we analyzed. Since attackers commonly use techniques to obscure their details, it is not always easy to determine the exact location of malicious activity. However, by analyzing the site IP address, it can be possible to provide insight and an approximation of the potential location.
Protecting Your Environment
Identifying potentially malicious activity and understanding risk is a critical first step to protecting any environment. ORDR customers regularly generate and review their detailed reports showing devices in their environment that have communicated with Russian sites. That report not only identifies these communications but also provides detailed analysis to help customers understand and address the potential risk in their environments.
ORDR also helps customers eliminate risk by dynamically generating policies for enforcement across their existing security and network infrastructure. ORDR has Integrations with leading firewall vendors and can automatically push policies to limit the sites with which devices are allowed to communicate. Examples might be manufacturer maintenance, software update, and services such as image enhancements for medical imaging.
If a device is already infected and spreading malware, ORDR can quickly push policies to switches or wireless controllers to isolate them and stop the spread of the attack. ORDR can also push proactive zero-trust policies to switches or wireless controllers, allowing only a pre-determined set of devices and flows to and from any medical device.
If you want to learn more about the ORDR solution, the insights we provide to uncover the risk of Russian communications, and how you can improve the security for your connected devices, reach out for a personalized demo.
