Search Results:
”Role of Huawei H19-431_V1.0 Exam Questions in Getting the Highest-Paid Job 💆 Search for { H19-431_V1.0 } and download exam materials for free through [ www.pdfvce.com ] 🏸Premium H19-431_V1.0 Files”
-
 BlogConnectWise ScreenConnect CVE Vulnerabilities
BlogConnectWise ScreenConnect CVE Vulnerabilities…devices running a vulnerable version of the software are highlighted in the Ordr Vulnerabilities and Info page in the Latest Vulnerabilities card. Global CVE Search: For easy lookup in just…
Security Bulletin
ConnectWise ScreenConnect CVE Vulnerabilities
3Min Read
By Pandian Gnanaprakasam

The ConnectWise Screen Connect vulnerabilities (CVE-2024-1708 and CVE-2024-1709) put many enterprises at risk of a cyberattack. Ordr can identify and mitigate the vulnerabilities by supporting patching, segmenting affected systems, and facilitating rapid response. Background
ConnectWise ScreenConnect software is a comprehensive remote desktop access software solution that enables secure, flexible, and efficient technical support for its customers. Part of ConnectWise’s suite of IT service delivery and support products, ScreenConnect is commonly used by managed service providers (MSPs) to gain remote access to customer endpoints for services such as IT support.
ConnectWise recently announced it discovered that flaws in ScreenConnect were being actively exploited and issued a security advisory. The ConnectWise advisory reported that all versions of ScreenConnect prior to 23.9.8 contained two vulnerabilities.
Vulnerability Details
CVE-2024-1709 CVE-2024-1708 Severity Critical
CVSS: 10High
CVSS: 8.4Products affected ConnectWise ScreenConnect Software. ConnectWise ScreenConnect Software. Versions affected Up to (excluding)
23.9.8Up to (excluding)
23.9.8Details Authentication bypass using an alternate path or channel to gain unauthorized access to confidential information or critical systems. Improper limitation of a pathname to a restricted directory (“path traversal”) via a Zip Slip attack. Exploitability Score 3.9 1.7 Vector CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:C/C:H/I:H/A:H CVSS:3.1/AV:N/AC:L/PR:H/UI:R/S:C/C:H/I:H/A:H Impact Score 6.0 6.0 NVD Published Date 02/21/2024 02/21/2024 NVD Last Modified 02/22/2024 02/22/2024 Reference CVE-2024-1709 Detail CVE-2024-1708 Detail Have these vulnerabilities been exploited?
Yes. CVE-2024-1708 and CVE-2024-1709 have been exploited and, due to that evidence, have been added to the Known Exploited Vulnerabilities Catalog by CISA. Trend Micro says that multiple cybercrime groups, including the Black Basta and B100dy ransomware groups, have started exploiting the flaws.
CISA has directed that all federal civilian Executive Branch agencies must address vulnerabilities identified in this catalog by a specified due date, which for CVE-2024-1709 is Feb 29, 2024.
For detailed information and updates on CVE-2024-1709 and CVE-2024-1708, refer to the official CVE database and the advisories provided by ConnectWise and CISA.
How to use Ordr to detect and respond to this threat
- Ordr updated its vulnerability database for all customer instances with these latest ConnectWise ScreenConnect CVEs for early identification and patching.
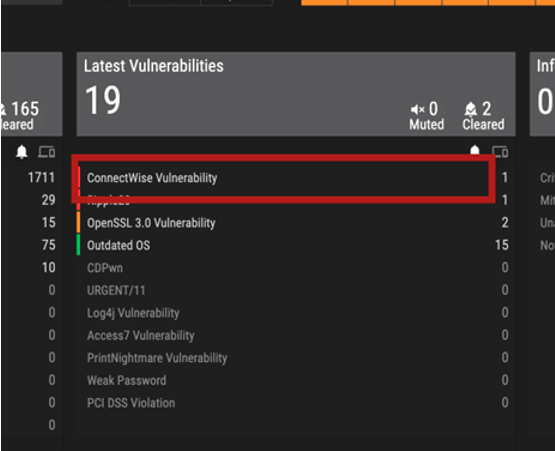
- Ordr added a new alert type in the “Latest Vulnerabilities” threat card as an easy visual indicator. Ordr analyzes the total software installed on all devices, checks for this specific version and matches with this vulnerability after a quick lookup of affected devices.
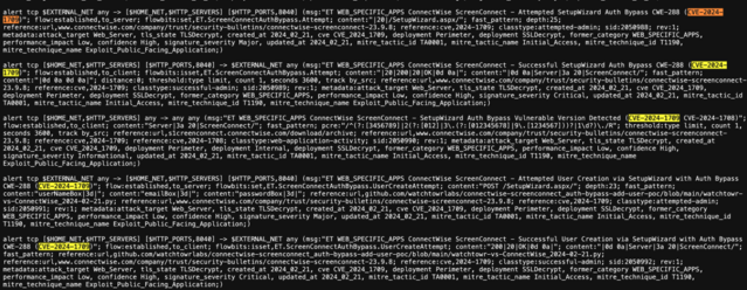
- Ordr updated its IDS rules corresponding to the exploitation of these vulnerabilities for real-time detection. As a result of this update, Ordr’s IDS engine will automatically look for relevant signatures and add a visual indication in the Ordr security page incident card if there is a match with the signature on the packet stream.
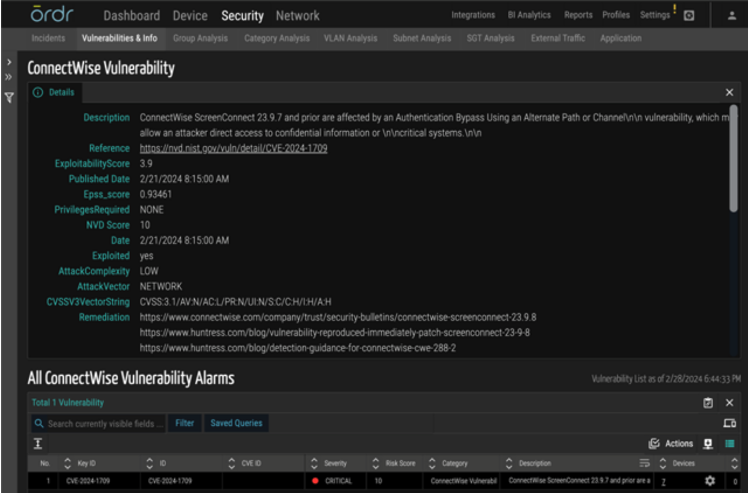
Ordr detection details and CVE lookup
The following are ways to identify if your organization has been exposed to these vulnerabilities and how to mitigate them.
Vulnerability mapping of impacted devices:
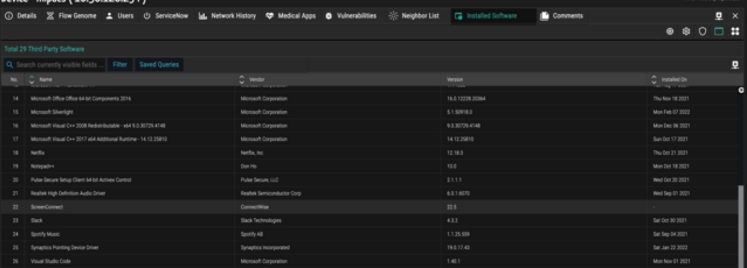
- Ordr provides visibility into all the devices running ConnectWise applications by mapping applications collected via Ordr Software Inventory Collector or 3rd party integrations like EDR, MDM, MSFT-AD, and others.
- Ordr also maintains a list of all the software packages installed on the endpoints with exact version numbers and a time stamp on which it was installed and last updated.
- Ordr matches the software version number against the various vulnerability databases to identify vulnerable versions of ConnectWise ScreenConnect applications.
This information can be looked up easily in the following ways:
- Latest Vulnerabilities Card: All devices running a vulnerable version of the software are highlighted in the Ordr Vulnerabilities and Info page in the Latest Vulnerabilities card.
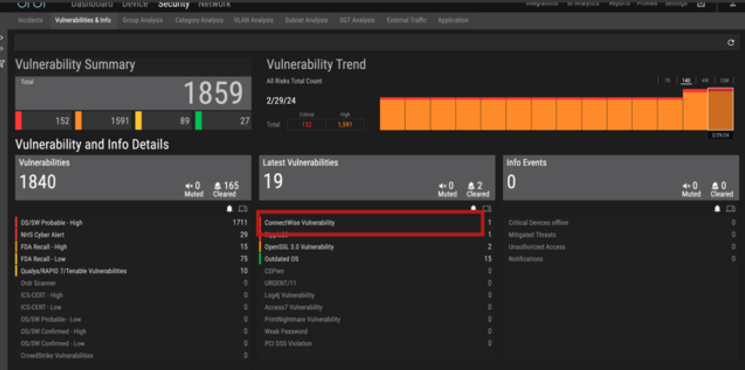
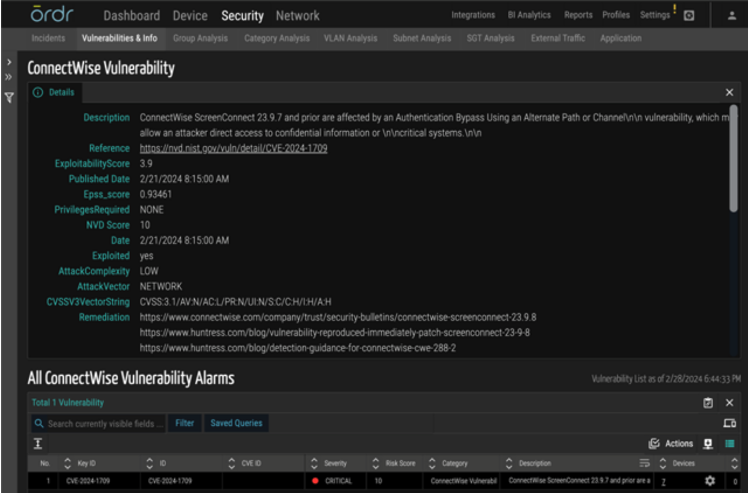
- Global CVE Search: For easy lookup in just a click, customers can search for the CVE ID corresponding to ScreenConnect vulnerabilities directly from the global CVE search in the Ordr main dashboard page.

Real-time detection of exploits using IDS, behavioral violation, and threat correlation:
The Ordr IDS engine detects this specific vulnerability using analysis of packets transacting over the wire. Ordr IDS signatures have been updated to detect ConnectWise ScreenConnect software exploitations.
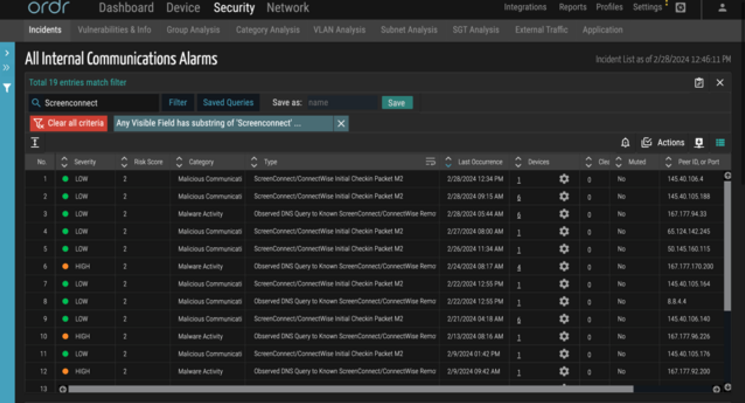
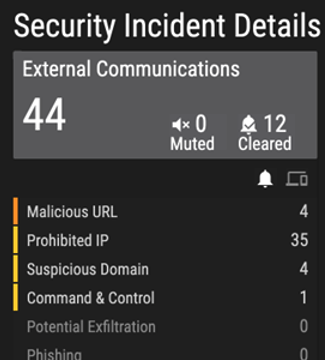
Generate alerts based on communication malicious IPs/URLs: Ordr’s external IP/IOC tracks every communication to prohibited IP/URLs in real-time. Ordr uses a continuously updated, cloud-based threat intelligence platform and all malicious communications alerts are marked accordingly in the Ordr Security Threat Card.
Mitigation actions to perform if detected:
To mitigate the risks associated with CVE-2024-1708 and CVE-2024-1709, several strategies are recommended:
- Update ConnectWise ScreenConnect software: Ensure that you are using the latest version of ConnectWise ScreenConnect above version 23.9.8. Updates often include patches for known vulnerabilities, which can prevent exploitation.
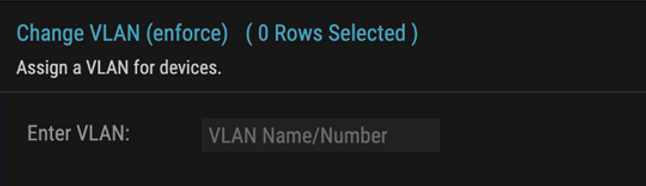
- Reactive rapid threat containment: Ordr has the capability to rapidly isolate the affected devices if it is deemed to have this vulnerability by putting the device in a quarantine VLAN, or denying its connection to the network using automation with a single click. This automation works with almost any networking, switch, or wireless controller vendor.
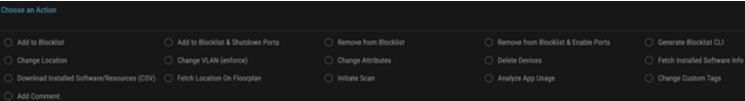
- Pro-active protection: Even if a breach happens, mission-critical assets (medical devices, industrial controls, etc.) can be protected using Ordr-enabled policies such as quarantining, or limiting communications to specific assets over certain protocols.
Ordr supports integration with multiple industry-leading NAC vendors.
- Stay Informed and Respond Quickly: Regularly check for updates from ConnectWise and security advisories from cybersecurity researchers and organizations like CISA. Responding quickly to vulnerabilities by patching can significantly reduce the risk of exploitation.
Ordr’s Call to Action for Customers
Customers are requested to monitor their environment and quickly identify the presence of the ConnectWise ScreenConnect CVEs mentioned using Ordr’s easy lookup methods, then Patch/Remediate them promptly to safeguard their organization against this rapidly known and exploited vulnerability.
Please get in touch with Ordr customer support for any queries or guidance.
Pandian Gnanaprakasam
Pandian has more than 20 years of product and engineering leadership experience and is also a serial entrepreneur. Before founding Ordr, he was the Chief Development Officer at Aruba, responsible for all of engineering and product management functions. Aruba, an enterprise mobile wireless company, was acquired by HPE for $3 Billion in March 2015. Before Aruba, Pandian served as the head of engineering for Cisco’s multi-billion-dollar Wi-Fi business unit and before that as VP of engineering for low-end switching product lines. He graduated with a master’s degree in Electrical Engineering from IIT, Chennai, India and holds several patents to his credit in various networking technologies.
Interested in Learning More?
Subscribe today to stay informed and get regular updates from Ordr Cloud
Ready to Get Started?
-
 BlogIt’s All About Identity
BlogIt’s All About Identity…close the gap and bring identity-based controls to these critical devices? This post looks deeper into the challenges, these questions, and how Ordr helps provide answers in a straightforward and…

Identity management is integral to security, allowing organizations to control access to data or services. The explosion of IoT, OT, IT, and other connected devices is a challenge for organizations that are unprepared for identifying and managing the growing enterprise attack surface. Identity is a foundational component of modern security models, allowing organizations to control the data or services a user or account should be able to access. The explosion of IoT, IoMT, OT and other connected devices introduces significant gaps in identity-based security while creating new challenges and posing questions:
What is an identity for these devices that do not inherently have what we think of as an identity?
How can we close the gap and bring identity-based controls to these critical devices?
This post looks deeper into the challenges, these questions, and how Ordr helps provide answers in a straightforward and automated way.
It’s the End of Identity as We Know It…and I Feel Fine?
There are several methods organizations use to establish and verify identity for their users and assets. Unfortunately, none of these methods work well for the new class of connected devices.
Traditional devices such as laptops and workstations can be associated with a specific user and can be reliably linked to that user’s identity. Security teams can also verify the identity of a device by installing certificates or using USB keys. When a high-value asset is accessed, multi-factor authentication mechanisms can be leveraged by sending the user a passcode via email or text to be provided for additional verification.
The new class of connected devices are rapidly increasing in numbers and can be found everywhere in enterprise environments. Connected devices include everything from consumer products and phones to printers and media displays. In industrial settings IIoT and OT devices span the range of sensors to the multi-million dollar equipment essential to manufacturing lines. In healthcare, IoMT includes a vast array of medical devices from health monitoring equipment to magnetic resonance imaging (MRI) scanners that are critical to delivering care and ensuring patient safety.
Connected devices are increasingly critical infrastructure in organizations across industries, yet these devices can’t be managed the same as traditional devices. The simple task of installing enterprise certificates or endpoint agents is virtually impossible since many of these devices run embedded operating systems or are agentless. Even if agents could be installed, the vast diversity of hardware and software variations of IoT devices makes it almost impossible for vendors to develop and support agents.
Connected devices are commonly found with software stacks from various sources layered on embedded and customized operating systems. For these devices, any tool that uses a map of the processes to perform behavioral analysis is virtually useless.
Integrated firmware running on connected devices typically prevents any new software from being installed to ensure security and device reliability. As an example, new software can’t be installed on a piece of medical equipment once it’s gone through FDA certification.
Multi-factor authentication is another non-starter for IoT. An infusion pump can’t be expected to receive and provide a passcode to verify its identity.
Bringing Ordr to the Chaos of IoT Identity
With all of these limitations, how is identity determined and used for connected devices? The best unique identifier (not identity) is a device MAC address or serial number. MAC addresses are at least trackable (although easily spoofable), but serial numbers are nearly impossible to track and manage.
Ordr takes a new approach that doesn’t require IT and security teams to manually track the endless minutia of device details or do anything to update or change devices. Instead, Ordr automatically and passively analyzes the behavior of each device and recognizes a device’s identity based on what it actually does (i.e., the device communication).
To illustrate, let’s look at a device that claims to be a printer. Does it act like a printer? How do we know how a printer should act?
To answer this a large number of printers must be studied to understand what printers normally do, the protocols they speak, destinations they connect with, packet patterns they exhibit, etc.
With sufficient sampling a baseline can be established and used to verify if a new “printer” behaves like all the other printers previously seen – if it walks and squawks like a printer, then it’s probably a printer.
It’s also important to understand normal behavior for a particular environment. It’s not enough to know if a printer is behaving within the norms of other printers – it’s essential to know if the printer is behaving like my other printers. Is it talking to the appropriate management server, using the appropriate network segments, and so on.
The combination of global and local insights into behavior gives a very reliable approach to understanding a device’s identity. Just as importantly, it is a passive, hands-off approach that doesn’t require more work from staff or to change anything on the device itself.
As a result, Ordr is able to easily establish identity and continuously monitor it throughout its life cycle. Request a demo to learn more about how Ordr can help with identity and security for all your IoT, IoMT, OT and other connected devices.
Pandian Gnanaprakasam
Pandian has more than 20 years of product and engineering leadership experience and is also a serial entrepreneur. Before founding Ordr, he was the Chief Development Officer at Aruba, responsible for all of engineering and product management functions. Aruba, an enterprise mobile wireless company, was acquired by HPE for $3 Billion in March 2015. Before Aruba, Pandian served as the head of engineering for Cisco’s multi-billion-dollar Wi-Fi business unit and before that as VP of engineering for low-end switching product lines. He graduated with a master’s degree in Electrical Engineering from IIT, Chennai, India and holds several patents to his credit in various networking technologies.
Interested in Learning More?
Subscribe today to stay informed and get regular updates from Ordr Cloud
Ready to Get Started?
-
 BlogReducing Attack Surface Risks with Accurate, Automated Inventory
BlogReducing Attack Surface Risks with Accurate, Automated Inventory…These challenges hinder incident response and make it difficult to understand—and limit—an attack’s blast radius. They also complicate the task of identifying security gaps, vulnerabilities, and prioritizing cyber risk management….
Blog
Reducing Attack Surface Risks with Accurate, Automated Inventory
Strengthening the Enterprise Security Posture
3Min Read
By Srinivas Loke
The definition of a cyber asset has evolved significantly, expanding beyond network devices to encompass a wide array of elements such as users, applications, SaaS, and cloud resources. The shift to a distributed, hybrid workforce further complicates matters as administrators need visibility into assets that traditional, on-premises security controls do not protect. As a result, security and IT teams are now tasked with managing hundreds, thousands, and even millions of cyber assets to protect their organizations from cybersecurity threats. Unfortunately for CISOs and their teams, this broadening definition has expanded the cyber asset attack surface, making it larger and more diverse, creating new challenges for enterprise security teams, including:
- Incomplete asset inventory leading to network blind spots, particularly with IoT, OT, and IoMT devices.
- Duplicate asset entries and inaccurate inventories due to reliance on tracking assets using IP addresses.
These challenges hinder incident response and make it difficult to understand—and limit—an attack’s blast radius. They also complicate the task of identifying security gaps, vulnerabilities, and prioritizing cyber risk management. And when incidents do occur, it is challenging for security and IT teams to quickly identify which assets are impacted and understand the connections to other devices on the network, leaving them to rely more on guesswork than data-driven analysis.
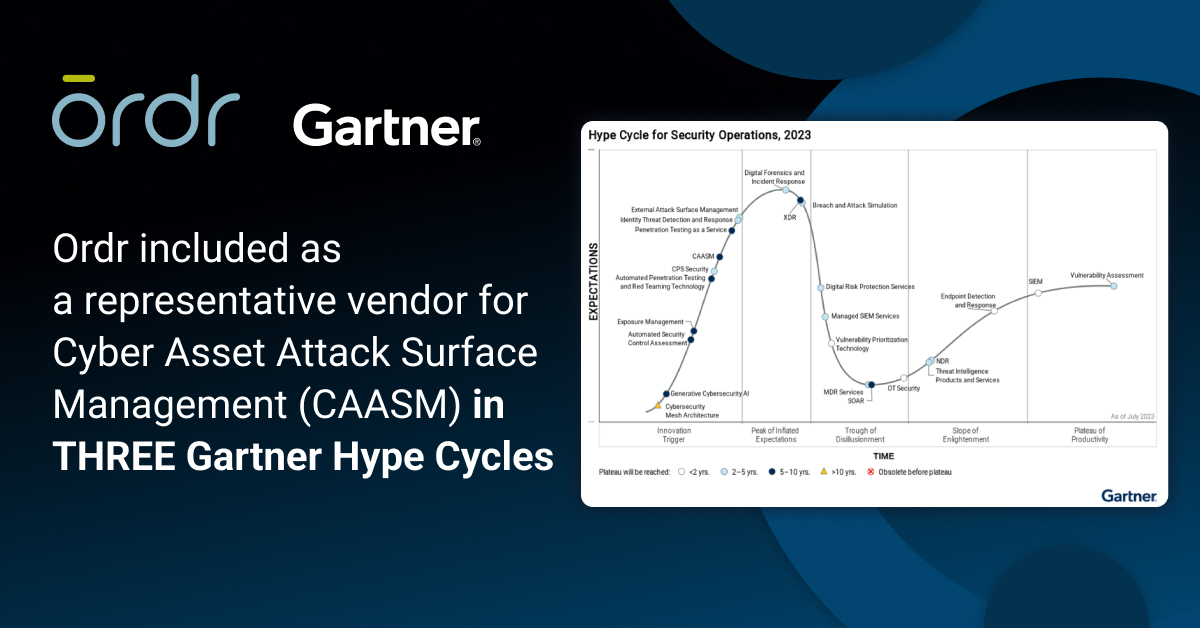
OrdrAI CAASM+ Enables Enterprise Teams to Improve Their Security Posture and Reduce the Attack Surface
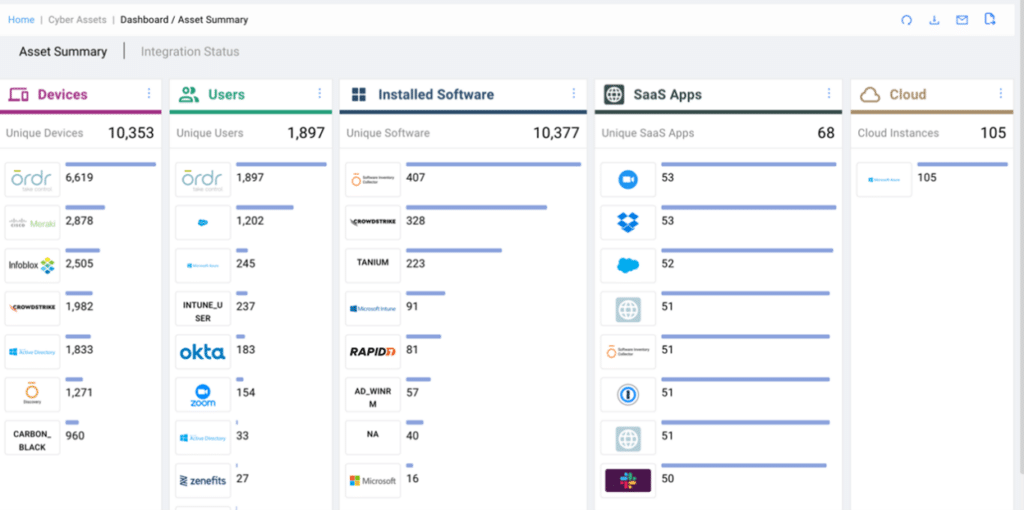
Going beyond API-only solutions, OrdrAI CAASM+ provides security teams with complete visibility and data for all assets, including devices (IT, IoT, OT, IoMT), cloud, installed software, SaaS, and users. Then, utilizing a combination of over 180 security and IT ecosystem integrations a proprietary discovery technology and AI/ML classification, Ordr empowers security teams with a unified platform to address critical asset management questions such as:
- How many cyber assets do I have?
- What software is running on my devices?
- What is the blast radius of a compromised cyber asset?
To help enterprise organizations maintain up-to-date asset information and enhance overall security posture, Ordr recommends integrating with a variety of data sources, including:
- CMDB
- IPAM
- EDR
- MDM
- AWS for cloud assets
- Network infra integration (SNMP)
- Active querying from Ordr
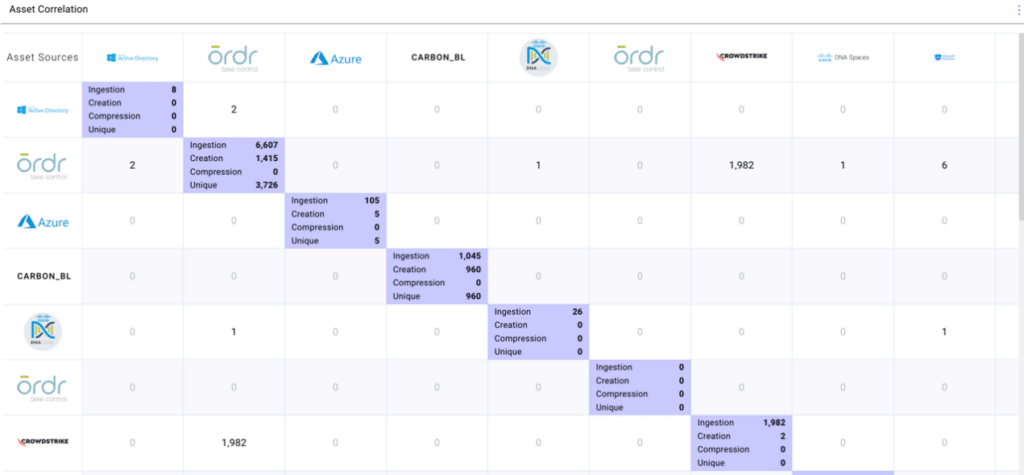
OrdrAI CAASM+ Deduplicates, Normalizes, and Aggregates Asset Data and Correlates it into a Single Source of Asset Intelligence
Merely seeing an organization’s entire asset inventory is not enough. What enterprise organizations need is comprehensive, accurate asset visibility coupled with in-depth asset context to tackle critical security and IT use cases head-on. To provide this data, Ordr uses a multi-level de-duplication technique to consolidate and compress the asset data based on the set of attributes to provide an accurate asset count. This eliminates issues with duplicate assets such as when data is collected from EDR using MAC addresses and VA using IP addresses, resulting in duplicate entries.
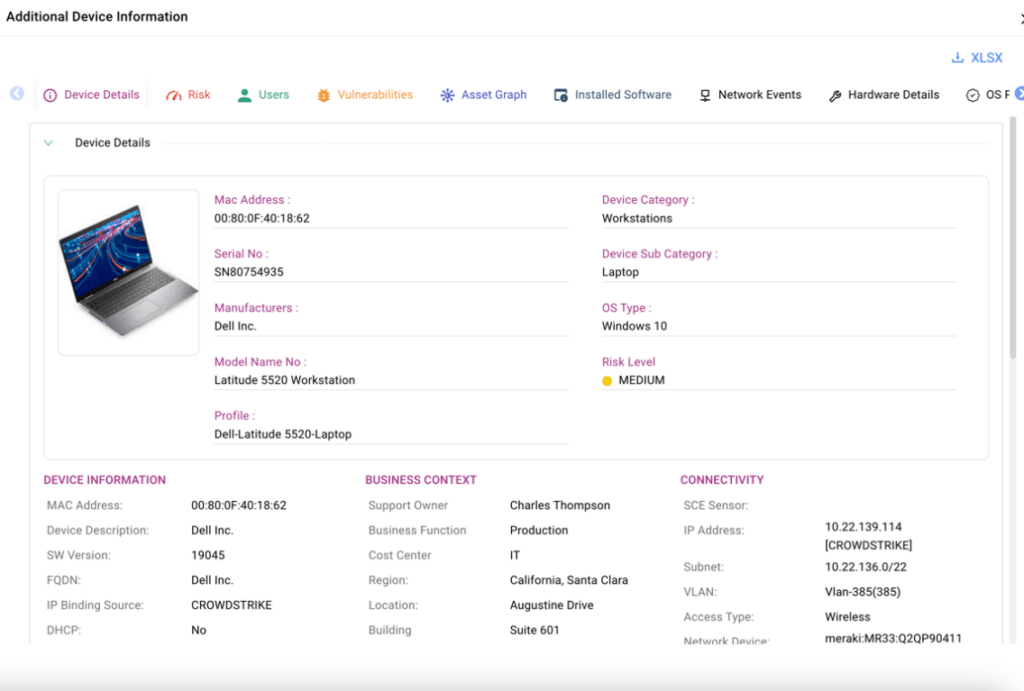
Tracking all assets independently and displaying this data within the platform, CAASM+ provides teams with the necessary asset insights to determine the blast radius of an exposed asset. The information is readily available in the user interface, as shown below, and can be accessed for any type of asset with a simple click of a button.
Using AI/ML Classification, Ordr Provides In-Depth Asset Context to Reveal Security Issues and Coverage Gaps in Asset Management
Over the last six years, Ordr has built a crowd-sourced asset repository—the Ordr Data Lake—comprising data from over 1.5 million different assets across networks from all industries. Leveraging our proprietary AI/ML technology, Ordr classifies and assigns a three-level hierarchy for every asset. This classification enables Ordr to assign a risk score based on business context and asset criticality. Additionally, it allows the enterprise security admins to easily find and identify security infrastructure gaps, eliminating guesswork by clearly defining security control boundaries. This allows teams to distinguish which devices require Endpoint Detection and Response (EDR) and which already have it installed. This differentiation is crucial, as it ensures that teams do not waste time on devices that cannot support EDR installation.
https://www.youtube.com/watch?v=FnNP0_QTxIwWhen starting from a foundation of comprehensive, accurate asset inventory, enriched with in-depth context and business insights, security teams can better address critical challenges in cyber asset visibility and management. OrdrAI CAASM+ empowers organizations by providing:
- Actionable asset data and detailed business insights, such as make, model, OS, serial number, connectivity and more. This data can be easily share with CMDBs and other IT tools to reconcile asset data and easily identify missing assets, update records, and remove outdated information.
- Generative-AI powered natural language search to easily obtain answers about your security posture and identifying security issues.
- Asset risk scores to prioritize and remediate risks and exposures based on asset context, CVSS scores, vulnerability exploitability, type of data (encrypted), location, and more.
- Streamlined remediation through automated workflows integrated with ITSM, SIEM, and SOC, ensuring actions are assigned to the appropriate device owner.
Do these challenges sound familiar? Schedule a meeting with our team of security experts to learn how you can leverage Ordr’s automated, accurate asset inventory management solution to proactively prioritize and reduce risks and exposures, streamline incident response, and enhance your overall security posture.
Thanks for joining us for another blog in our series on CAASM+ use cases. Stay tuned as we explore more of these critical use cases in the coming weeks and discuss how Ordr addresses them.
Srinivas Loke
Srinivas Loke is Vice President of Product Management at Ordr. Srinivas has a passion for cybersecurity with a deep understanding of network, end point, cloud and IoT security. Prior to Ordr, he led product teams at Aruba, Pulse Secure, FireEye and McAfee. He loves taking 1.0 products to the market and furthering cutting edge technologies that are solving customer problems.
Interested in Learning More?
Subscribe today to stay informed and get regular updates from Ordr Cloud
Ready to Get Started?
-
 BlogSegmentation Done Right – Part 1: Great Idea
BlogSegmentation Done Right – Part 1: Great Idea…between to help control and keep zones safe and secure. If for example, there was a cyberattack and a device is compromised, the segmentation will keep the damage from spreading…
Security Strategy
Segmentation Done Right – Part 1: Great Idea
3Min Read
By Pandian Gnanaprakasam

Device segmentation is essential for protecting at-risk devices (and the networks they attach to) from cyberattack. Ordr gives you a comprehensive, step by step guide to implement connected asset segmentation for your enterprise security strategy. Segmentation Done Right Part 1 of 3
When I was in middle school standing in the cafeteria lunch line, there was always that feeling of nervousness before the spaghetti or tuna casserole(or aloo tikka masala if you are familiar with the Indian school lunch trays) hit my lunch tray with its unique thud. After the entrée, I would shuffle my feet to the left to receive my overcooked peas and carrots. Last but not least was a big scoop of extra syrupy canned peaches. Ah, the joys of being in 7th grade. The good thing about public school lunch was that at least the lunch tray was compartmentalized and my noodles only caught a little bit of that extra sugary-extra sweet peach syrup. Segmentation, what a great idea.
Contain the Damage
Reminiscing about my school noodles made me think about the benefits of network segmentation which is the division of a network into smaller more manageable groups. These zones can be separated from each other with controls in between to help control and keep zones safe and secure. If for example, there was a cyberattack and a device is compromised, the segmentation will keep the damage from spreading as the damage is confined to a specific zone or segment. Think blast radius control. Unusual lateral side to side movement is also kept in check when a network is properly segmented.
It’s Recommended
It sounds simple enough, separate the network into its own compartment to limit the spillover effect and zones can readily consist of VLAN/subnets, groups or segments, hence the name. In terms of application, one can deploy network segmentation using existing network infrastructure or even via deploying new next-generation firewalls into specific zones. The National Institute of Standards and Technology (NIST) in its framework for zero trust architecture recommends segmentation for enhanced identity governance.
Factors to Consider
Getting started with segmentation takes a little bit of thought. How big will the zones be? How many devices of similar types would be in each zone? What about the regulatory environment? The regulatory side can have a say in how things are portioned as well. For example, if your business deals with payments the PCI-DSS standard will state a clear demarcation between payment card authorization and point of sale. In hospitals, one would want to keep life-saving equipment separated from the IT devices.
So how does one begin and are segments rigid in a “set it and forget it” way? How can segments evolve as network requirements change? How is it going to adapt to changing business policies? It helps to start off the right way with a segmentation project by considering the various enterprise departments and the level of fine-grained control required. Furthermore, consider the zones of vulnerability, as plenty of exploits and attacks can occur from inside the network. Departmental segmentation can be done with firewalls but if you want to get more granular control, it very quickly amounts to deploying a large number of small hardware firewalls everywhere on the campus, which is not practical nor cost-effective.
Network segmentation by itself is a great methodology, but if your organization does not know how your applications communicate with your endpoints, then you may risk having incoherent policies at your control points, which reduces the solution’s effectiveness and usefulness of segmenting. Also, segmentation applied without precision, can even impact the day to day operations of a company, so something to consider when it comes to implementation. The other factor to consider is the growth and expansion of your network as you want a segmentation method that is scalable with your business requirements.
Slice and Dice Your Way to Segmentation
When you use a platform from Ordr, you can get as granular as you like. Beyond buildings, sites, departments, and floors, one can segment a network via business requirements and even perform grouping by device functions, even for the same class of devices. For example at a casino, we can separate all the cameras into various groups based on their function, physical surveillance cameras for regulatory compliance (watching the slot machines) vs. general use security cameras observing foot traffic. High-risk assets vs. mission-critical assets are another way to consider the segmentation process.
Segmentation similar to the lunch tray can work great when it’s done right. There is no spillover or cross-contamination and things are in a nice tidy order. Next week we will discuss the limitations and shortcomings of existing approaches and dive deeper into modern methods for segmenting the network the right way.
Read Segmentation Done Right – Part 2.
Pandian Gnanaprakasam
Pandian has more than 20 years of product and engineering leadership experience and is also a serial entrepreneur. Before founding Ordr, he was the Chief Development Officer at Aruba, responsible for all of engineering and product management functions. Aruba, an enterprise mobile wireless company, was acquired by HPE for $3 Billion in March 2015. Before Aruba, Pandian served as the head of engineering for Cisco’s multi-billion-dollar Wi-Fi business unit and before that as VP of engineering for low-end switching product lines. He graduated with a master’s degree in Electrical Engineering from IIT, Chennai, India and holds several patents to his credit in various networking technologies.
Interested in Learning More?
Subscribe today to stay informed and get regular updates from Ordr Cloud
Ready to Get Started?
-
 BlogClosing the IoT Security Gap – Cadre and Ordr
BlogClosing the IoT Security Gap – Cadre and Ordr…the estate. In organizations that rely heavily on internet connected devices—the Internet of Things (IoT)—that level of visibility can be elusive. And for the unprepared, it’s going to get worse….

As a trusted advisor for cybersecurity, it’s important to be able to develop security strategies that match the challenges inherent in each customer’s unique IT environment. To do that requires a complete understanding of the IT estate; and a complete understanding of the IT estate requires device discovery that delivers total visibility into the estate.
In organizations that rely heavily on internet connected devices—the Internet of Things (IoT)—that level of visibility can be elusive. And for the unprepared, it’s going to get worse. That’s because there’s been a huge increase in IoT use across industry, and in healthcare and manufacturing especially. IoT deployments worldwide were at 10 billion in 2018 and are predicted to exceed 25 billion by the end of 2021. Some believe that number could more than triple by 2025, driven by the advent of 5G network connectivity.
Overcoming Historical Challenges
At Cadre we work with manufacturing and healthcare organizations with complex environments and a significant need to secure connected devices. Historically, protecting IoT devices in manufacturing and healthcare was a hard thing to do. Most organizations chose to either air gap their networks, or use a well-protected jump host to access the environments. On the manufacturing shop floor, where industrial sensors and controllers are used to maintain production, devices remained segregated from corporate networks.Now you have devices that are communicating not only internally with the owner, but out on the internet to supply chain partners. That dynamic has upended the Purdue Enterprise Reference Architecture (PERA) model, dramatically increasing organizational risk of malware infections and attacks by malicious actors. The stakes are even higher when the equipment you’re protecting is used for medical care. From an IT security perspective, you can’t treat a patient monitor or ventilator the same way you treat an HVAC controller.
When we learned about Ordr and its approach to securing IoT devices in these complex environments, we were intrigued. It was important to us that they are a Check Point integration partner with a strong, stable organization and track record of success. Our experience with the Ordr Systems Control Engine (SCE) has been great, so when we had a chance to evaluate Ordr’s IoT Discovery Program, a complete kit of zero-touch, cloud-managed IoT sensor and Ordr Core software, we were on board.
Ordr Core Lives Up to the Claim
Ordr Core quickly and easily discovers the full extent of an organization’s IoT asset inventory, allowing us to automatically populate the customer’s configuration management database (CMDB) with the profile of every device connected to the network. From there we can automatically generate and enforce appropriate policy based on device risk.Ordr Core has already become an indispensable tool for us to see into the customer’s environment, control the chaos, and implement complex security strategies like device segmentation at a level of granularity that was unattainable before.
Every time we run Ordr Core in a customer environment, or when evaluating prospective engagements, we find devices that were unknown to the CIO and CISO. Often these are older devices that had fallen out of view and were forgotten, but we also find unauthorized devices like consumer electronics that have no business being on the network in the first place.
Discover, Profile, Evaluate, Protect
Once Ordr Core discovers these devices, we are able to profile them and observe things like communications flow, and identify and evaluate the inventory of legacy devices. It’s easy to forget that, while the IoT market is in the midst of a renaissance, networked controls and sensors have been in use for decades. Many organizations rely on equipment that was made by companies that no longer exist, or that operates with obsolete operating systems or firmware that cannot be patched. All of this is easily understood by Ordr, and it gives us a clear view into the health, availability, and risk of the network and allows us to close a security gap that network access controls can’t handle natively.Ordr Core gives Cadre a competitive advantage with the ability to see across the entire IoT estate and derive insights that were not available before. We know there’s no slowdown in sight for the adoption of IoT, and every organization that relies on them has a compelling need to control and protect each device to keep it from becoming a point of entry for malicious actors.
If you’d like to see what your IoT environment looks like and take informed action to address the vulnerabilities you knew were there but couldn’t find, you can request your free zero-touch, self-provisioning Ordr Core sensor here.
Ken Dickey
Ken Dickey heads the Business Development department at Cadre. With over 29 years of experience in information technology, Mr. Dickey has established himself as an expert on IT security architectures and design.
Interested in Learning More?
Subscribe today to stay informed and get regular updates from Ordr Cloud
Ready to Get Started?
-
 BlogWhy Ordr? Why Now?
BlogWhy Ordr? Why Now?General 4Min Read By Wes Wright Wes Wright tells the inside story of why he joined Ordr as the company’s first Chief Healthcare Officer at a crucial time for the…
Wes Wright tells the inside story of why he joined Ordr as the company’s first Chief Healthcare Officer at a crucial time for the industry, his early experiences with connected device security solution, and how Ordr helped him address security needs prior to becoming part of the Ordr team. I just joined Ordr as Chief Healthcare Officer and, as is often the case in life, there’s a story, personal and professional, behind my new adventure here.
A little more than seven years ago, while I was CTO at Sutter Health, a friend from my days as CIO at Seattle Children’s Hospital called and told me about a technology he really wanted to get my opinion on. It was an innovative new product aimed at keeping connected devices secure—a growing problem for healthcare environments. Since I was just a few hours from Silicon Valley, I drove out to find out more.
That’s when I met Gnanaprakasam Pandian, one of Ordr’s co-founders. Pandian proceeded to show me v1 of Ordr and I was floored. In more than 20 years in healthcare IT and security, I had never, ever, been able to get complete visibility on everything that was on any of the networks I managed. And from conversations with my colleagues and peers I knew I was not alone; nobody could.
Sure, I could see all my PCs, printers, routers, switches and other traditional IT and back-office gear; I could even manage them fairly efficiently with the right set of tools, but my vulnerability scanners kept reminding me that there were things connected to my network that were just out of view. Yes, I might have a MAC or IP address, but no clear understanding of what the associated device was, where it was, or how it was behaving. That’s the kind of stuff that keeps a CIO or CISO up at night.
My network managers had told me not to worry about it. They would try to assuage my fears by telling me those unknown configuration items were probably just biomedical devices, not real IT equipment. Yes, they were operating on the network, but they were someone else’s problem. Their advice was meant to reassure me, but I couldn’t shake the feeling of dread.
Ordr Visibility and Security Capabilities
I described my experience with Pandian, and he showed me that, with the Ordr platform, he could tell me exactly what devices all those MAC and IP addresses were assigned to. Not only that, but Ordr could also tell me if any of those devices had associated ECRI notices, vulnerabilities, recalls, and other insights invaluable to understanding a hospital’s security posture. The visibility alone would have been enough to give me the confidence to get a full night’s sleep, but the depth and device intelligence Ordr provided was invaluable to a CISO.
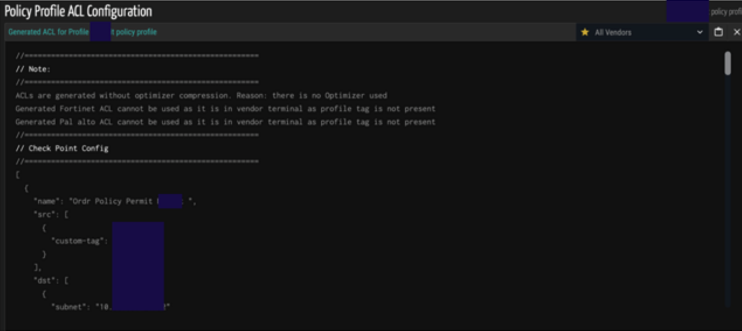
Then Pandian showed me how Ordr could learn and establish a baseline for all these devices– establishing what is “normal behavior”, and then automatically generating VLAN, ACL, and Firewall policies for network and security engineers to review and execute. This functionality delivered “Zero Trust policies” — enabling only the normal communications required for its function–and was thanks to the machine learning (ML) artificial intelligence (AI) that Ordr’s other founder, Sheausong Yang, brought to the platform. And because it is ML driven, Ordr has been learning about device behavior for a long time and has a precise understanding of what constitutes abnormal activity—and what to do about it.
As impressed as I was at the demonstration, it was still a demonstration. And while I am not from Missouri, I am fond of the state’s motto: “Show Me”. So, I asked Pandian if he would be willing to bring Ordr to my organization’s operational environment. I wanted to see how the platform would perform with my stuff, and, oh boy, did it ever perform. I was amazed at the level of device intelligence I was getting out of Ordr, and I wasn’t the only one. I had my security team with me, and their faces lit up.
Seven Years Later
That was seven years ago. Today, with 61 million individual device profiles (with 1000 attributes each) now populating the Ordr Data Lake, it is now the leading asset visibility and security platform used by healthcare organizations everywhere.
Because of that experience, Sutter engaged Ordr for a trial and we began putting the platform through its paces and working with the company’s engineers. Alas, I left Sutter to take on the CTO role at Imprivata, and did not get through the PoV process before I left. Pandian and I had discussed the possibility of joining Ordr then, but the timing wasn’t quite right. I did join the company’s advisory board, however. As it turns out, that was the best scenario for both parties.
While I had extensive experience as a healthcare CIO and CTO, Ordr is much more than just a healthcare security platform and I don’t think I would have been able to do what the company needed at that point in its growth. In fact, I remember one of my first meetings “on the vendor side” listening to people talk about TAM, SAM, and SOM. I made a mental note thinking, “I’d better meet these people. They seem important!”
Today, I think I’m much better prepared to work with my friends and colleagues in the healthcare field and to use those conversations to help Ordr continue to evolve its market leading device security platform. That’s why I decided to join the Ordr team now.
I am eager and excited for this next chapter to unfold, and I hope that it involves you.
Wes Wright
Chief Healthcare Officer
Wes is responsible for driving Ordr’s engagements in healthcare. Previously he was the CTO for Imprivata, and prior to that VP and CTO at Sutter Health, a 26 hospital network in Northern California. Prior to Sutter, Wes was CTO and then CIO at Seattle Childrens’, which, to this day, he says was his most gratifying work experience.
Interested in Learning More?
Subscribe today to stay informed and get regular updates from Ordr Cloud
Ready to Get Started?
-
 NewsOrdr Clinical Defender 8.1
NewsOrdr Clinical Defender 8.1…managing thousands of medical devices, many of them critical to patient care and safety. The volume of devices is increasing every day, with equipment from hundreds of manufacturers, running an…
Ordr Clinical Defender 8.1
Delivers Full-Lifecycle Vulnerability Management Platform Optimized for HTM
4Min ReadSanta Clara, CA – August 31, 2022 – Ordr, the leader in connected device security, today announced Ordr Clinical Defender 8.1, providing Healthcare Technology Management (HTM) teams a full-lifecycle vulnerability management platform to more efficiently prioritize and address risks for their connected medical devices.
Clinical engineering teams are tasked with managing thousands of medical devices, many of them critical to patient care and safety. The volume of devices is increasing every day, with equipment from hundreds of manufacturers, running an enormous volume of operating systems. As hospitals merge (or are acquired), the diversity of devices can multiply overnight. The attack surface also continues to expand – while device visibility decreases – as healthcare providers open remote clinics and support telemedicine environments.
Securing the environment of care directly depends on the operational efficiency of the HTM team. With the 8.1 release, Ordr Clinical Defender optimizes the process of managing medical devices and their vulnerabilities. HTM teams benefit from visibility into devices everywhere, with insights optimized based on their function, location, skills, and experience. Critical vulnerabilities are prioritized based on business risks, and simplified workflows assign the right tasks to the right teams. As a result, no time is wasted, and no vulnerabilities go undetected or unaddressed.
“Simply put, HTM teams require more efficient ways to monitor devices and vulnerabilities in an ever-expanding healthcare environment,” said Pandian Gnanaprakasam, Ordr Chief Product Officer and Co-Founder. “Ordr Clinical Defender allows each user to focus on the specific devices they’re responsible for, from a single screen, and helps them understand, prioritize and manage vulnerability workflows based on full business context. This will ultimately improve efficiencies and enhance patient safety.”
The Clinical Defender 8.1 release also adds the Ordr Software Inventory Collector, and integration with Crowdstrike and Crowdstrike Humio to ensure HTM teams have comprehensive device and operating system visibility at their fingertips. Healthcare organizations no longer have to struggle with discovering offline devices, those in remote clinics and locations, and behind VPN connections, making it easy to properly patch software and protect every device everywhere. Healthcare delivery organizations can now also easily manage diverse devices – from un-agentable devices like MRI systems, to medical workstations with agent-based Crowdstrike protections – within the same environment of care.
“The visibility that we now have into our networked devices and their software inventory gives us greater assurance that we are properly maintaining and securing our systems to ensure that we can continue to provide excellent service and patient care,” said Stacy Estrada, Information Security Manager, Montage Health.
“Efficiencies in HTM and clinical engineering teams translate to improvements in patient safety,” said Boyd Hutchins, Director of Clinical Engineering, Arkansas Children’s Hospital. “With the enhancements in Ordr Clinical Defender 8.1, HTM teams will now be able to manage the complete vulnerability lifecycle for all clinical devices. Ordr takes us beyond vulnerability monitoring and remediation to visibility into system utilization, instant access to system configuration, software levels, and location within our system.”
Clinical Defender was built on Ordr’s foundational asset and risk management features and developed with best practices from the top healthcare delivery organizations in the world. Now with comprehensive visibility into the software “stack” essential to understand vulnerabilities, Ordr makes it easy for HTM teams to work with their security teams to address the shared goal of patient safety.
“Ordr Clinical Defender has been an invaluable tool to help our clinical engineering teams improve the management and security of our IoMT devices,” said Dave Yaeger, Biomed Security DBA for ProHealth Care. “The advancements in the latest release support our whole hospital security approach across the healthcare system and will evolve the way our clinical engineering and security teams work together to manage device vulnerabilities and risks.”
Ordr Clinical Defender 8.1 delivers the following:
- Risk reduction through Full-Lifecycle Vulnerability Management – Ordr simplifies how healthcare delivery organizations manage the complete vulnerability lifecycle for connected healthcare devices.
- View all risks on a single vulnerability dashboard – Ordr now provides a single clinical vulnerability dashboard to help view all clinical vulnerabilities, across all vulnerability databases.
- Prioritize vulnerabilities based on risks – Ordr’s Customizable Clinical Risk Score allows HTM teams to plan and prioritize remediation efforts. Risk scores are automatically calculated based on environmental factors and device lifesaving capabilities and are easily customized to align with organizational goals.
- Optimize mitigation efforts – Leverage simplified workflows to collaborate across teams and manage the entire lifecycle of vulnerabilities. Custom Tags can be used to associate devices with applications, location, priorities, groups, individuals, or other key attributes, to simplify management of vulnerabilities across teams.
- Collaboration with security teams – Ordr now integrates with Humio, Crowdstrike’s scalable log management platform, sharing medical device context to facilitate better collaboration with security teams.
- Operational efficiency by aligning to HTM roles and responsibilities – Ordr enables users to group devices based on real-world business functions, allowing each user to see all devices under their management – and only those devices. Devices may be grouped by device type, across multiple types, by location, cost center, ownership, or any other business logic. This is useful when a mix of devices such as workstations, medical equipment, security cameras and more must be managed and maintained by an individual or group.
- Enhanced security by eliminating device blind spots – Ordr Software Inventory Collector and Ordr’s new integration with Crowdstrike eliminate blind spots by gaining granular details of all connected devices everywhere.
- Simplify how device context is gathered – Ordr Software Inventory Collector simplifies how device context, including vulnerabilities, can be gathered for all managed and unmanaged devices on all leading operating systems, no matter where and how the devices and users connect. This includes devices offline or online, in remote locations, and connected behind VPN or gateways.
- Comprehensive visibility for all devices, managed and unmanaged – Ordr now integrates with Crowdstrike. The integration provides healthcare delivery organizations with comprehensive visibility across all devices, managed and unmanaged. Insights from devices with Crowdstrike agents are integrated within the Ordr DataLake to enhance device context.
“Ordr tracks IoT, OT, and medical devices where the CrowdStrike agent cannot be installed. By integrating Ordr’s dataset with Falcon’s in Humio, Crowdstrike’s scalable log management platform, this solution provides our customers unprecedented observability and visibility on all devices, agent or agentless, 24×7, online or offline,” said Adam Hogan, SE Director, Humio, CrowdStrike.
“Connected devices in healthcare bring unique risks. Ordr Clinical Defender 8.1 demonstrates Ordr’s continued focus on innovation, and will allow us to help healthcare providers to more effectively manage clinical vulnerabilities across the full lifecycle and safely deliver connected care,” said Carter Groome, CEO, First Health Advisory.
Learn more about Ordr Clinical Defender 8.1 and how it can help your HTM team stay on top of connected device security.
Interested in Learning More?
Subscribe today to stay informed and get regular updates from Ordr Cloud
Ready to Get Started?
- Risk reduction through Full-Lifecycle Vulnerability Management – Ordr simplifies how healthcare delivery organizations manage the complete vulnerability lifecycle for connected healthcare devices.
-
 BlogOrdr Response to Log4j Vulnerability
BlogOrdr Response to Log4j VulnerabilitySecurity Bulletin 3Min Read By Pandian Gnanaprakasam Ordr dives into the details of how attackers are taking advantage of the Log4j vulnerability by, for example, exploiting VMware networks that have…

Ordr dives into the details of how attackers are taking advantage of the Log4j vulnerability by, for example, exploiting VMware networks that have not yet been patched. We look closely at how the Ordr System Control Engine’s (SCE) detects and protects against the Log4j vulnerability. Like many other security and incident response teams, Ordr was busy over the weekend responding to the critical Apache Log4j vulnerability (NIST details here CVE 2021-44228). We want to make sure our customers understand what the Log4j vulnerability is, how it affects them, and how Ordr helps keep their enterprises protected.
What is the critical Apache Log4j Vulnerability?
Log4j is an Apache Java logging library used in many forms of enterprise and open-source software. This includes cloud platforms, web applications, and email services that could be at risk from attackers attempting to exploit this vulnerability.
The Log4j vulnerability (CBE-2021-44228), also known as “Log4Shell,” is a vulnerability that was announced on December 9. The attack vector is extremely trivial for threat actors. A single string of text can trigger an application to reach out to an external location if it is logged via a vulnerable instance of Log4j. It can allow unauthenticated remote code execution and access to servers. There are already active examples of attackers attempting to exploit this Log4j vulnerability in the wild, from installing cryptomining malware, installing Cobalt Strike malware, and of botnets attempting to use it for botnet activities.
Is the Ordr Platform or Ordr operations impacted by Log4j?
No. The good news is that all three areas of Ordr operations–Ordr internal IT, Ordr Data Center/AWS that use various tools and hosts cloud instances of Ordr Systems Control Engine (SCE), and the Ordr SCE that runs on customer premises–are NOT impacted by Log4j.
What Systems/Vendors are impacted by Log4j?
There is a long and growing list of systems and vendors impacted by Log4j.
What about healthcare organizations and medical devices impacted by Log4j?
While the full scale of affected devices and systems is still being analyzed, healthcare organizations should consider any web-connected medical device vulnerable as they likely use Java-based applications or other Java components.
Identifying medical devices with Log4J vulnerability may require a slightly different approach. In a typical IT scenario, security teams can scan or run scripts on servers to identify what kind of log4j version is being used but in healthcare situations, hospital staff do not have the privilege to run scripts directly on heavy iron devices like CT/X-ray machines as well as patient monitoring devices.In addition, in some cases, it is not feasible to patch these medical systems.
Ordr will also work with medical device manufacturers as they disclose their vulnerability to make sure customers are kept up to date.
Another best practice for healthcare organizations is to monitor device communications from these devices to watch for connections to suspicious IP/URLs. Ordr’s Traffic Analysis and behavioral-based anomaly can provide visualization and baselining of traffic patterns of medical devices. We will monitor external communication to make sure malware is not getting downloaded, exploited through this vulnerability and communicating to attacker C2 domains.
Can we use the Ordr Systems Control Engine to detect systems impacted by Log4j?
Yes. Ordr has comprehensive threat protection capabilities that will detect systems and assets impacted by this vulnerability:
- You can start by using Ordr to first identify all workstations and servers that may be vulnerable.
- Our integrated IDS/threat detection engine has already been updated with signatures to detect active exploits of Log4j. You can investigate impacted systems that are being exploited.
- Ordr threat intelligence and malicious IP/URL database lookup have already been updated to detect the latest external communications to Log4j IoCs (indicators of compromise)
- You can create an Ordr custom policy profile and use the Ordr behavioral anomaly detection to monitor workstations and servers suspected to have this vulnerability and track their external communication.
Look for more best practices and new enhancements on detecting and protecting against Log4j using Ordr this week.
What can I do to mitigate the Log4j vulnerability’s impact?
While this vulnerability is extremely trivial to exploit, the mitigation is also trivial. For more details, please reference the recommendations provided by the Apache foundation.
- Identify vulnerable systems on your network, and update. The CVE-2021-44228 Log4j RCE vulnerability was patched in Log4Jv2.15.0 by Apache
- The vulnerability can also be mitigated in previous releases (>=2.14.1)
- By setting the system property flag “log4j2.formatMsgNotLooku[s” to “true”
- By removing the NdsiLookup class from the classpath
- Users since Log4j 2.7 may specify %m{nolookups} in the PatternLayout configuration to prevent lookups in log event messages.
- Remove the JndiLookup and JndiManager classes from the log4j-core jar. Note that removal of the JndiManager will cause the JndiContextSelector and JMSAppender to no longer function.
Please note that log4j versions 1.x are not affected by this vulnerability. Also, JDK versions greater than 6u211, 7u201, 8u191, and 11.0.1 are not affected by the LDAP attack vector.
For more questions on Ordr or the Log4j vulnerability, reach out to us at info@ordr.net, or if you’re a customer, please reach out to your customer success team.
Pandian Gnanaprakasam
Pandian has more than 20 years of product and engineering leadership experience and is also a serial entrepreneur. Before founding Ordr, he was the Chief Development Officer at Aruba, responsible for all of engineering and product management functions. Aruba, an enterprise mobile wireless company, was acquired by HPE for $3 Billion in March 2015. Before Aruba, Pandian served as the head of engineering for Cisco’s multi-billion-dollar Wi-Fi business unit and before that as VP of engineering for low-end switching product lines. He graduated with a master’s degree in Electrical Engineering from IIT, Chennai, India and holds several patents to his credit in various networking technologies.
Interested in Learning More?
Subscribe today to stay informed and get regular updates from Ordr Cloud
Ready to Get Started?
-
 BlogEnsure Cyber Readiness in a Time of Chaos
BlogEnsure Cyber Readiness in a Time of Chaos…we are in such times today. The eruption of violence over the border into Ukraine by one of the world’s most aggressive perpetrators of state-sponsored cyberattacks, and threats of retaliatory…
Security Strategy
Ensure Cyber Readiness in a Time of Chaos
3Min Read
By Greg Murphy

Threat actors thrive in times of chaos. When war broke out between Russia and Ukraine the resulting chaos had a predictable effect on cybersecurity. CISA offers tips to help prepare for cyberattacks. But don’t overlook the role protecting connected devices has on cyber-readiness. Threat actors thrive in times of chaos and confusion, and we are in such times today. The eruption of violence over the border into Ukraine by one of the world’s most aggressive perpetrators of state-sponsored cyberattacks, and threats of retaliatory cyberattacks on nations providing aid to Ukraine should put all organizations on high alert and give urgency to taking inventory of standing security plans and readiness.
The U.S. Cybersecurity & Infrastructure Security Agency’s (CISA) Shields-Up program “recommends all organizations—regardless of size—adopt a heightened posture when it comes to cybersecurity and protecting their most critical assets,” providing resources and guidance to ensure organizations prepare for possible attacks. CISA’s recommendations include:
- Reduce the likelihood of a damaging cyber intrusion – Validate remote access and administrative privileges; ensure that software and vulnerability patches are up-to-date; disable all ports and protocols that are not essential for business purposes; affirm strong cloud services controls are in place; and implement training and use of good cyber hygiene.
- Take steps to quickly detect a potential intrusion – Quickly identify, investigate, and act on unusual activity; update threat intelligence for systems that use it; be particularly careful with activities involving Ukrainian organizations.
- Ensure that the organization is prepared to respond if an intrusion occurs – Stand up a crisis-response team with necessary resources and information; make sure key personnel are available in the event of an incident; test your plan in advance.
- Maximize the organization’s resilience to a destructive cyber incident – Back-up critical data and review procedures; isolate backups from connected systems; make certain manual controls are operational in the event of attacks on industrial control systems or operational technologies.
CISA’s advice is solid, best-practice guidance that should be standard operational procedure for all organizations even in the best of times. But for many organizations, especially those whose IT estates are characterized by sophisticated, highly complex, and heterogeneous systems, preparation must go deeper. This is especially true for organizations with functions that provide vital services to their communities, like hospitals and healthcare organizations, operators of critical infrastructure, and communities that have adopted smart-city technologies.
Pay Attention to Connected Devices
Such organizations should pay particular attention to the connected devices they rely on, ensuring those devices are properly categorized by their function, and that mission-critical devices are segmented, with policies in place that ensure such devices are able to be isolated from the network, protected while remaining in service.
Bilateral communications of all devices must be monitored, as well as their behavior, to ensure no suspicious activity is taking place. Because connected devices are designed to carry out narrowly defined operations, any changes in behavior—measured against a known baseline—must be regarded as suspicious, triggering applicable security policies. Devices that communicate externally are especially vulnerable.
Patch management for devices should be brought up-to-date immediately, but for medical devices that may have restrictions prohibiting modifications, segmentation and appropriate policy application must be implemented. And, of course, all employees should be reminded of their individual responsibility to be aware of common threats like phishing schemes, practice good cyber hygiene, and to be alert for any unusual activities they see with any connected systems they use. The “see something, say something” adage applies here.
If you are an Ordr customer, know that—as has been our commitment from the start—we stand ready to answer your questions and to provide support to your organization at this time of heightened concern. We are confident that our Ordr platform will be an invaluable resource for you as you scan your IT estate for threats and vulnerabilities.
Be ready. Be safe. And to the people of Ukraine, know that our thoughts and prayers are with you.
Greg Murphy
Greg joined Ordr as CEO in December 2018. Previously, he was VP Business Operations for the HPE Aruba Group, the 4,000 person networking and IoT business unit of Hewlett Packard Enterprise. In that role, Greg was responsible for leading the business integration of Aruba and HP Networking following HP’s $3 billion acquisition of Aruba Networks in 2015. Greg held multiple prior senior executive positions within Aruba, including SVP Business Operations, GM of network management software, GM of outdoor and mesh products and VP of Marketing. Greg joined Aruba in 2008 through its acquisition of AirWave Wireless, a network management software provider that Greg founded and led. Greg received his M.A. from Stanford University and his B.A. from Amherst College.
Interested in Learning More?
Subscribe today to stay informed and get regular updates from Ordr Cloud
Ready to Get Started?
-
 BlogOrdr’s Continuous Device Discovery
BlogOrdr’s Continuous Device Discovery…Brandon Rivera, Enterprise Infrastructure Architect at CHRISTUS Health, and myself as we take a deep dive into the integration, and provide a demo of the Ordr and NSX Intelligence capabilities. Iain Leiter Iain Leiter is…
Security Strategy
Ordr’s Continuous Device Discovery
Accelerates NSX Data Center Microsegmentation
3Min ReadBy Iain Leiter

I am excited to announce the integration of Ordr Systems Control Engine (SCE) and VMware NSX-T™ Data Center and VMware NSX® Intelligence™.
Ordr Systems Control Engine (SCE): Discovers every connected device, profiles device behaviors and risks, and automates response. Ordr not only identifies devices with vulnerabilities, weak ciphers, weak certificates, and active threats, but also those that exhibit malicious or suspicious behaviors. Ordr enables networking and security teams to easily automate response by dynamically creating policies that isolate mission-critical devices, those that share protected organizationally unique sensitive data (PCI, PHI, PII) or run vulnerable operating systems.
VMware NSX-T Data Center: Includes Distributed Firewall functionality to specify dynamic security policies down to the VM level with the ability to configure east-west and north-south firewalling.
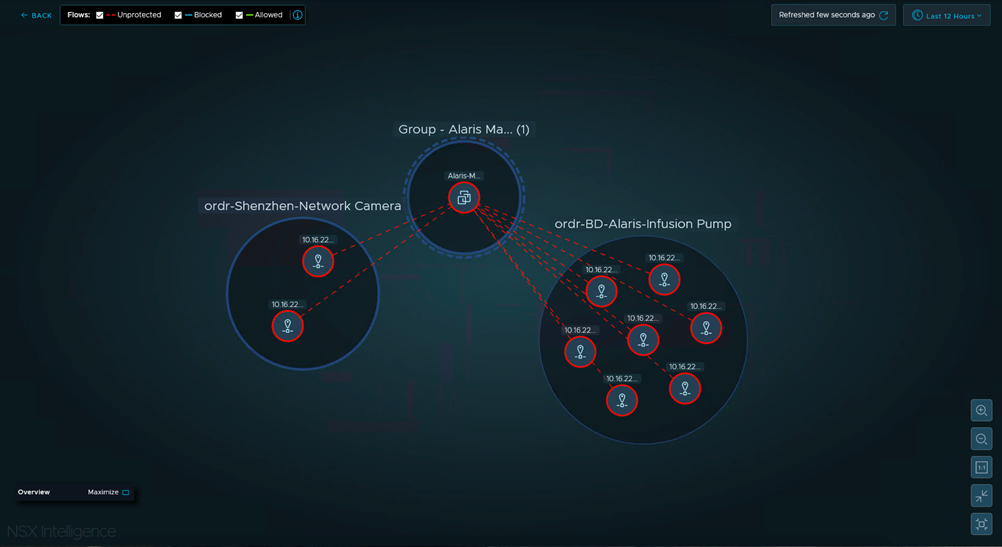
VMware NSX Intelligence: Provides a graphical user interface to visualize the security posture and network traffic flows that have occurred in your on-premises NSX-T Data Center environment.
With the integration, joint customers can now:
- Achieve cutting edge visibility
- Accelerate NSX-T Data Center microsegmentation
- Minimize the potential business impact associated with firewall changes
If your VMware NSX data center firewall microsegmentation team is looking for a method to significantly reduce the overhead of maintaining static NSX-T IPsets and group objects, it is time to consider a solution that is capable of addressing the following scenarios:
- Automated NSX-T group object creation for non-data center device types
Since NSX-T provides excellent visibility for the entire data center, the most time-consuming objects to create and maintain are ones which pertain to devices outside of the data center (enterprise campus, branch sites, etc).
Ordr continuously discovers devices as they join campus and branch networks and can automate the creation of corresponding group objects in NSX.
NOTE: Ordr creates NSX objects with a standard prefix of “ordr-“. This allows NSX admins to easily recognize which objects are autogenerated and maintained by Ordr.
- Automated IP address membership tracking for NSX group objects
Dynamically creating NSX-T groups is a great start, but this capability alone does not solve the labor-intensive aspect of maintaining IP address membership for each type of device.
Ordr tracks the IP addresses of each type of device in the campus and branch. If a credit card reader device IP changes, Ordr will automatically update the NSX group with the new IP address. - Support for advanced visualizations in the latest version of NSX Intelligence
Ordr programmatically creates NSX group objects and their members in a format which is compatible with the latest version of NSX Intelligence (announced at VMworld 2020[CI1] ).
This means that NSX Intelligence is able to render all communications from Ordr-defined and maintained NSX device groups.
This capability is key for teams who are looking to accelerate their data center security initiatives by gaining a comprehensive understanding regarding all types of campus and branch devices which are communicating to virtual machines in the data center.
How it works:
Step 1
Ordr SCE sensors use advanced deep packet inspection (DPI) techniques to process campus and branch traffic from a SPAN/port mirror, TAP, or packet broker feed
Step 2
Ordr SCE sensors forward metadata to the SCE Analytics system which identifies all the device types (including unmanaged IoT devices) which are communicating on the campus network
Step 3
Ordr SCE Analytics programmatically creates NSX groups and their member IP addresses
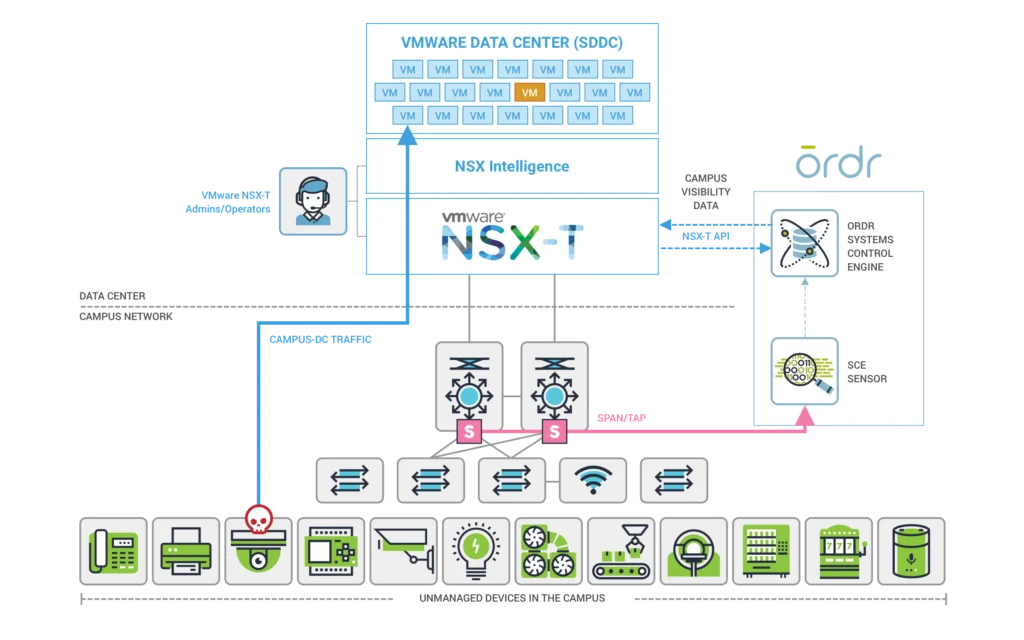
NSX Intelligence with Ordr device data in action:
In this example screenshot from NSX Intelligence, we can quickly see that the Alaris Manager VM is receiving unprotected communication from two different device types in the campus network.
NSX group 1: ordr-BD-Alaris-Infusion-Pump
NSX group 2: ordr-Shenzhen-Network-Camera
This type of information can be leveraged to reduce the amount of manual labor associated with understanding source/destination communication for thousands of different campus and branch device types communicating to virtual machines in the data center.
In summary, the Ordr integration with NSX-T Data Center and NSX Intelligence allows teams to achieve greater operational efficiency by automating labor intensive tasks and unlocking rich device type context visibility for all campus and branch devices communicating with virtual machines.
For more on how one of our customers is leveraging this integration today, visit our on-demand VMworld breakout session NSX Intelligence: Visibility and Security for the Modern Data Center – Pt2 [ISNS2496] with Ray Budavari, Sr. Staff Technical Product Manager at VMware, Brandon Rivera, Enterprise Infrastructure Architect at CHRISTUS Health, and myself as we take a deep dive into the integration, and provide a demo of the Ordr and NSX Intelligence capabilities.
Iain Leiter
Iain Leiter is a Sr. Technical Solutions Architect at Ordr where he is focused on enabling networking and security solutions for IoT devices. Iain has over 20 years of operational experience with a broad range of enterprise networking and security technologies for branch, campus and data center. Prior to Ordr, Iain was an Enterprise Network Virtualization Architect for a large hospital system where he was responsible for defining enterprise network architecture for initiatives such as SD-WAN, VMware NSX, data center switching, mergers & acquisitions, campus LAN design, routing design, and network security.
Interested in Learning More?
Subscribe today to stay informed and get regular updates from Ordr Cloud
Ready to Get Started?