Search Results:
”Role of Huawei H19-431_V1.0 Exam Questions in Getting the Highest-Paid Job 💆 Search for { H19-431_V1.0 } and download exam materials for free through [ www.pdfvce.com ] 🏸Premium H19-431_V1.0 Files”
-
 BlogSeeing is Not Enough: Cyber Asset and Attack Surface Management Use Cases
BlogSeeing is Not Enough: Cyber Asset and Attack Surface Management Use Cases…this context with SIEM/SOC results in faster and more informed incident response. Ordr CAASM+ also enriches IT tools and incident response data with the most comprehensive, accurate, and trusted insights…
Blog
Seeing is Not Enough: Cyber Asset and Attack Surface Management Use Cases
4Min Read
By Monica Armand
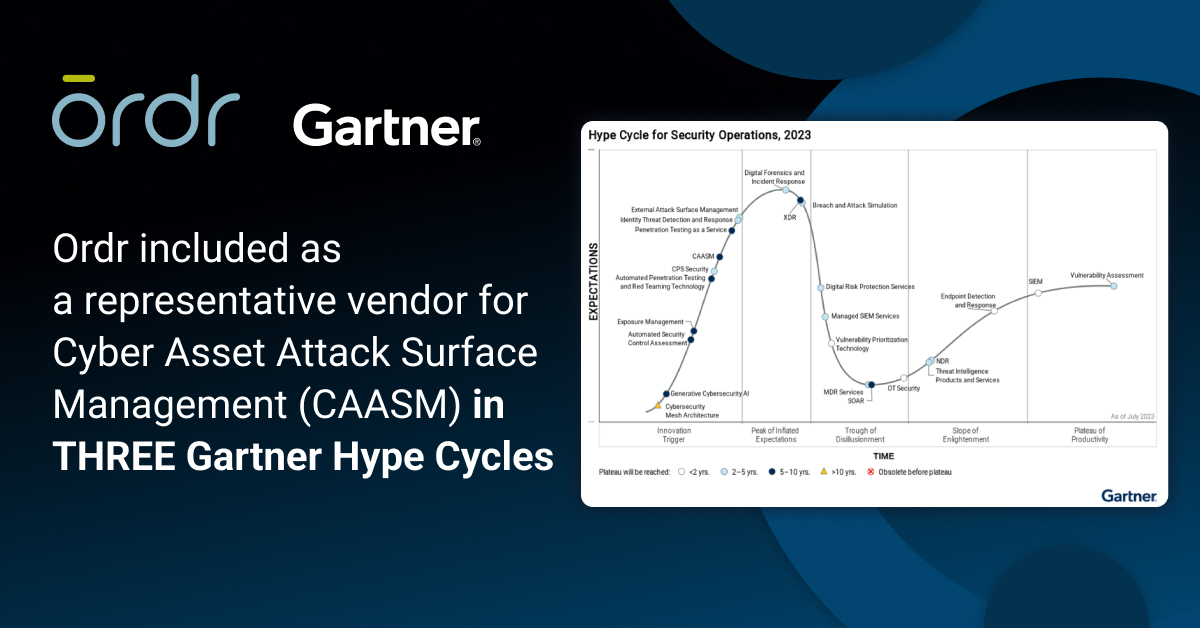
We recently launched our OrdrAI CAASM+ solution, driven by the broad need from our enterprise customers for a platform that unifies asset data for complete visibility and deep context on every asset in their network. CAASM, first defined by Gartner, means “cyber asset and attack surface management,” and is about the increasing need to identify the growing security and management challenges with network connected assets, including devices, users, installed applications, cloud workloads, and SaaS applications.
With the explosive growth of assets (in both volume and diversity) and the corresponding expansion of the attack surface, both security and IT teams find themselves grappling with numerous challenges: from effectively managing asset inventory to pinpointing risks and exposures and ensuring compliance with regulatory requirements.
Recognizing the need for a complete solution to address these pain points, Ordr developed CAASM+ with the belief that merely seeing an organization’s entire asset inventory is not enough. What they truly need is comprehensive, accurate asset visibility coupled with in-depth asset context to tackle critical security and IT use cases head-on. To deliver a CAASM solution that fulfils these use cases, Ordr maintains three fundamental beliefs regarding asset and attack surface management:
- Completeness Asset Discovery: Discovering and classifying every asset on the network, including IoT and OT, and eliminating blind spots is essential functionality for a CAASM solution. These critical assets comprise about 40% of most networks, and most organizations cannot discover or classify them effectively. High level insights about IoT or OT devices and manufacturers are not enough; details about what software is running, where it’s connected, and what it is doing in the network is important.
- High Fidelity Asset Data: The days of “more data is better data” are over. What is important is that a security team has high quality data they can rely on for patching, remediation, and incident response. This means automating the process of correlation, normalization, and deduplication (especially for ephemeral devices) to deliver a single source of trusted asset truth.
- Deep Context and Classification: Finally, a CAASM solution must have granular context and classification to reveal security gaps and vulnerabilities, and prioritize risks based on business impact. Without granular details and classification, organizations can’t align business and technical contexts to build a security strategy that prioritizes their team’s resources on the most critical tasks.
This is what sets CAASM+ apart from other CAASM solutions. Because of our foundation of complete, high-quality, and granular asset data, we provide organizations across all industries with an asset visibility and security solution that solves their most critical asset management use cases. Below we will get into what you can expect from CAASM+ and the top use cases it addresses. In the next several weeks we will publish a series of blogs that dive deeper into each of these so that you can understand why they are important and how Ordr addresses them.
Asset Visibility and Management: Complete and accurate data is foundational for CAASM. By eliminating the need for manual methods and fine-tuning, Ordr CAASM+ provides comprehensive asset oversight with automated inventory capabilities and uncovers hidden gaps in asset management. Ordr addresses critical asset visibility and management challenges that security teams face in their environments such as:
- Automated asset inventory;
- CMDB reconciliation;
- SBOM reporting; and,
- Asset ownership and user insights.
Identify Security Gaps and Coverage Issues: While security teams invest a lot in their security tools each year, determining if their assets are secure and identifying gaps is time-consuming and complex. Ordr CAASM+ simplifies this process by consolidating data from various sources, like vulnerability scanners and endpoint tools, to create a comprehensive cyber asset inventory and then compares tool coverage against this inventory. This improves endpoint security by detecting and addressing endpoint security coverage gaps such as missing EDR and MDM agents. Security teams can use natural language search to easily reveal gaps and continuously monitor for issues like:
- Endpoints missing critical security controls like EDR or MDM;
- Assets banned by the federal government;
- Assets running out-of-date software; and,
- Assets with weak, default, or no passwords.
Vulnerability Prioritization and Management: Identifying and prioritizing critical vulnerabilities puts a heavy burden on security teams. Ordr CAASM+ alleviates this challenge by providing a unified platform for end-to-end vulnerability management, enabling teams to identify, investigate, and prioritize vulnerabilities efficiently. Ordr automatically cross-references data with vulnerability databases, ensuring a comprehensive and up-to-date overview of vulnerabilities across the network. Ordr’s AI/ML mapping and correlation engine and Software Inventory Collector align technical and business priorities, reducing alert fatigue and providing a prioritized list of top risks. Ordr CAASM+ empowers teams to:
- Minimize cyber risk by discovering and understanding the full vulnerability landscape (including IT, OT, IoT, and IoMT).
- Simplify risk prioritization and vulnerability remediation based on asset risk scores tailored to the organization’s risk profile, ensuring that teams can focus on vulnerabilities posing the greatest threat to the business.
- Automate remediation workflows with ITSM workflows that are assigned to the right device owner.
Accelerate Incident Response: Time is critical for incident response teams, and having a centralized asset “database” to analyze incidents is invaluable. Ordr CAASM+ empowers incident response and security teams to act decisively and effectively with complete asset visibility and deep asset context. Sharing this context with SIEM/SOC results in faster and more informed incident response. Ordr CAASM+ also enriches IT tools and incident response data with the most comprehensive, accurate, and trusted insights for all assets to streamline and automate workflows by creating ITSM tickets with ITSM, SIEM, and SOC systems.
Audit and Compliance Reporting: Addressing compliance can be an expensive and time-consuming process, especially because regulations are constantly changing. Ordr’s automated asset inventory and deep asset insights enable teams to easily address and demonstrate compliance for industry and regulatory frameworks with customized dashboard and reports to meet compliance frameworks, including NIST, CIS Controls, Cyber Essentials, DSP Toolkit, CMMC, SOC2, PCI-DSS, and more.
By prioritizing complete asset visibility, high-fidelity data, and deep context, Ordr CAASM+ empowers organizations to address critical asset management challenges, from asset visibility and management, to vulnerability prioritization, incident response, and audit/compliance reporting. Follow along as we explore these benefits and explain how our product effectively addresses each specific use case. If you are ready to learn how CAASM+ can help your organization reduce your attack surface, schedule a personalized demo today.

Monica Armand
Monica is a key member of the Ordr product marketing team, dedicated to linking customers with Ordr products that empower action and diminish asset risk. With prior experience in launching enterprise cybersecurity products across multiple domains—including application security, identity management, and asset management—Monica is deeply committed to introducing innovative technologies that not only solve customer challenges but also facilitate decisive action.
Interested in Learning More?
Subscribe today to stay informed and get regular updates from Ordr Cloud
Ready to Get Started?
-
 BlogExecutive Order and NIST Define OT as Critical Infrastructure
BlogExecutive Order and NIST Define OT as Critical Infrastructure…the peace of mind, in knowing that they can effectively identify, manage and secure their critical infrastructure devices in their critical infrastructure in support of this crucial mission for the…
Security Bulletin
Executive Order and NIST Define OT as Critical Infrastructure
4Min Read
By Greg Murphy

The Executive Order 14028 has sent ripples through the cybersecurity industry. Since my last blog post where I provided my reflections on the EO, NIST has published their definition of ‘critical software’ in their official white paper published on June 25, 2021.
Operational technologies comprise the industrial hardware and software systems that form the backbone of industry. Manufacturing equipment, building automation systems, facilities management controls, transportation and logistics infrastructure are all essential to managing critical operations.
In the guidance, NIST clearly defines Operational Technology as critical software that must be secured. At Ordr, we know fully the gravity of this situation and have built our solution around this paradigm to give our customers the peace of mind, in knowing that they can effectively identify, manage and secure their critical infrastructure devices in their critical infrastructure in support of this crucial mission for the United States.
From the NIST Whitepaper:
NIST recommends that the initial EO implementation phase focus on standalone, on-premises software that has security-critical functions or poses similar significant potential for harm if compromised.
Subsequent phases may address other categories of software such as:
- software that controls access to data;
- cloud-based and hybrid software;
- software development tools such as code repository systems, development tools, testing software, integration software, packaging software, and deployment software;
- software components in boot-level firmware;
- or software components in operational technology (OT).
EO-critical software is defined as any software that has, or has direct software dependencies upon, one or more components with at least one of these attributes:
- Is designed to run with elevated privilege or manage privileges;
- Has direct or privileged access to networking or computing resources;
- Is designed to control access to data or operational technology;
- Performs a function critical to trust; or,
- Operates outside of normal trust boundaries with privileged access.
The definition applies to software of all forms (e.g., standalone software, software integral to specific devices or hardware components, cloud-based software) purchased for, or deployed in, production systems and used for operational purposes. Other use cases, such as software solely used for research or testing that is not deployed in production systems, are outside of the scope of this definition.
The preliminary list of software categories considered to be EO-Critical:
- Identity, credential, and access management (ICAM)
- Operating systems, hypervisors, container environments
- Web browsers
- Endpoint security
- Network control
- Network protection
- Network monitoring and configuration
- Operational Monitoring and Analysis
- Remote scanning
- Remote access and configuration management
- Backup/recovery and remote storage
As an extension of the focus on Operational Technology, on July 20, the Department of Homeland Security (DHS) issued a security directive requiring owners and operators of critical pipelines that transport hazardous liquids and natural gas to implement “urgently needed protections against cyber intrusions.”
In an earlier security directive in late May, immediately following the Colonial Pipeline cyber attack, the DHS began requiring US pipeline operators to conduct a cyber security assessment. The May 2021 Security Directive requires critical pipeline owners and operators to (1) report confirmed and potential cybersecurity incidents to CISA; (2) designate a Cybersecurity Coordinator to be available 24 hours a day, seven days a week; (3) review current practices; and, (4) identify any gaps and related remediation measures to address cyber-related risks and report the results to TSA and CISA within 30 days.
These are all the right steps toward improving the Nation’s Cybersecurity. We are eager to extend the work we already have underway with many federal agencies and organizations that need to protect their Operational Technology. With the Ordr platform, our focus is on visibility and security for cyber resilience:
Continuous visibility into all devices and their vulnerabilities (IT, IoT, and OT):
Ordr can help you identify what assets are in your environment. This allows you to examine your entire business process when calculating risk. It is important to not overlook what seem to be simple IT or IoT systems or processes like shipping or logistics, like billing. Those systems are as critical to production, processing, and delivery as any refinery equipment or manufacturing sensors.
Intelligent insights into how devices are behaving:
We detect known threats via our integrated threat detection engine to identify exploits, active threats and attacker lateral movement tools. We also use machine learning to baseline and map exactly how every device is behaving and what it is communicating to. This is critical to surface unknown threats and anomalous communications, particularly when attackers have already infiltrated your network. Ultimately we have to examine cyber resilience via full spectrum understanding of the flow of device communications (transactions and data) as well as we understand the flow of oil or manufacturing processes.
Automated policies on existing infrastructure:
The most critical function during an attack on OT environments is cybersecurity resilience, how quickly you can respond to an attack and continue business operations. Ordr not only tells you what device is being compromised, where it’s located, what it is doing and who it is communicating with, we also dynamically generate the policies to mitigate threats on your security and networking infrastructure. We can automate the creation of NGFW policies, ACL blocks, quarantine VLAN assignment, port shutdown, or session termination with one click of a button– enforced on existing switches, wireless controllers, and firewalls, or via NAC platforms.
Our work doesn’t just stop in the United States. Being a global leader in IoT, IoMT and OT Security, we are proactively embedding best practices, as well as lessons learned, to nations around the world. The US is not alone in their struggle against threat actors that wish to do them harm. This is highlighted in recent events in Germany, Canada, Australia, United Kingdom as well as other many other nations and industries. We are doing our part to make the giant leap towards a better and safer future.
Setup a time with us to start the process today and you’ll be able to see what connected devices are on your network in minutes.
Greg Murphy
Greg joined Ordr as CEO in December 2018. Previously, he was VP Business Operations for the HPE Aruba Group, the 4,000 person networking and IoT business unit of Hewlett Packard Enterprise. In that role, Greg was responsible for leading the business integration of Aruba and HP Networking following HP’s $3 billion acquisition of Aruba Networks in 2015. Greg held multiple prior senior executive positions within Aruba, including SVP Business Operations, GM of network management software, GM of outdoor and mesh products and VP of Marketing. Greg joined Aruba in 2008 through its acquisition of AirWave Wireless, a network management software provider that Greg founded and led. Greg received his M.A. from Stanford University and his B.A. from Amherst College.
Interested in Learning More?
Subscribe today to stay informed and get regular updates from Ordr Cloud
Ready to Get Started?
-
 NewsOrdr Selected to Deliver Forensic Level Device Insight and Threat Protection
NewsOrdr Selected to Deliver Forensic Level Device Insight and Threat Protection…and compliance and accelerate IT initiatives. Ordr is backed by top investors including Battery Ventures, Wing, and TenEleven Ventures. For more information, visit www.ordr.net and follow Ordr on Twitter and LinkedIn. About University Hospital Southampton…
Ordr Selected to Deliver Forensic Level Device Insight and Threat Protection
For University Hospital Southampton NHS Foundation Trust
3Min ReadLONDON, Jan. 26, 2021 /PRNewswire/ — Ordr, the leader in security for enterprise IoT and connected devices, today announced that it has been named the solution of choice for the University Hospital Southampton NHS Foundation Trust (UHS) in the UK, providing further evidence of its rapid growth within the healthcare market. After analysing the market and reviewing various security solutions, UHS in partnership with reseller SmartGate Group deployed Ordr’s Systems Control Engine (SCE), which discovers and secures every connected device, including Internet of Medical Things (IoMT), Internet of Things (IoT) and Operational Technologies (OT).
Like many hyper-connected NHS organisations with a high number of devices attached to the network, UHS required a solution that protected against potential cyber threats and cyber criminals looking to ransom or steal valuable data, including patient information. Ordr SCE discovers every connected device, profiles device behaviors and risks, and automates response. Ordr not only identifies devices with vulnerabilities, weak ciphers, weak certificates, and active threats, but also those that exhibit malicious or suspicious behaviors.
The Informatics department at UHS faced an issue confronting many organisations – both within and outside of the healthcare community – whereby it is difficult to gain full visibility as to exactly what is connected to their network, the associated risk and how to mitigate the ‘east-to-west’ lateral movement threat from cyber exploitation. This is a common challenge for the NHS as many different departments connect a multitude of devices such as CCTV cameras, door access systems, HVAC systems and a wide range of medical equipment. These devices are business critical but are notoriously susceptible to cyber threats.
“We liked the simplicity of the Ordr solution coupled with its forensic level of insight. It’s very intuitive and quick to install, even on a network of this size, and instantly started to catalogue and risk profile every single device on our network,” said Darran Lebas, Network and IT Security Manager, University Hospital Southampton NHS Foundation Trust. “The way it automatically classifies and then baselines the communications of all our devices is very impressive.”
“By delivering real-time device inventory, monitoring east-to-west communications and providing invaluable utilisation data, Ordr is proving to be a valuable asset to the Trust and is a critical component of our cybersecurity strategy,” added Adrian Byrne, IT Director, University Hospital Southampton NHS Foundation Trust.
“The opportunity to partner with UHS has been fantastic, especially with such a forward-thinking IT team looking to take the Trust forward. It is another example of how our solution addresses the challenges faced by healthcare organisations,” commented Bob Vickers, Head of UK&I, Ordr. “UHS, like so many other hyperconnected organisations, sees our solution as being key in their quest to ensure the ongoing cyber security of their connected devices.”
Ordr continues to experience growth within the healthcare sector. The company was recently named a Leader in the Healthcare IoT Security market, according to a new report “Decision Insights: Healthcare IoT Security” from KLAS Research. Ordr was highlighted for its fast pace of growth, strong technology offering, high customer satisfaction, and the highest market share among selected vendors. Ordr was also named as a Representative Vendor in the Gartner Market Guide for Medical Device Security Solutions.
To view the UHS case study in full, please click this link here.
For more information on how Ordr helps industries such as Healthcare, please visit https://ordr.net/solutions/healthcare/.
For more information about University Hospital Southampton NHS Foundation Trust, please visit www.uhs.nhs.uk.
About Ordr
Ordr makes it easy to secure every connected device, from traditional IT devices to newer and more vulnerable IoT, IoMT, and OT. Ordr Systems Control Engine uses deep packet inspection and advanced machine learning to discover every device, profile its risk and behavior, map all communications and protect it with automated policies. Organizations worldwide trust Ordr to provide real-time asset inventory, address risk and compliance and accelerate IT initiatives. Ordr is backed by top investors including Battery Ventures, Wing, and TenEleven Ventures. For more information, visit www.ordr.net and follow Ordr on Twitter and LinkedIn.About University Hospital Southampton NHS Foundation Trust
University Hospital Southampton NHS Foundation Trust provides services to some 1.9 million people living in Southampton and south Hampshire, plus specialist services such as neurosciences, cardiac services and children’s intensive care to more than 3.7 million people in central southern England and the Channel Islands. They are recognised as one of twelve GDE (Global Digital Exemplar) NHS Trusts – NHS organisations are awarded this status for their IT thought leadership and adoption of effective technology.The Trust is also a major centre for teaching and research in association with the University of Southampton and partners including the Medical Research Council and Wellcome Trust. Follow UHS on Twitter @UHSDigital.
Interested in Learning More?
Subscribe today to stay informed and get regular updates from Ordr Cloud
Ready to Get Started?
-
 BlogAsset Inventory Discovery and Management
BlogAsset Inventory Discovery and Management…not included in inventory Including device details that are critical for device management and security The lack of a complete connected device inventory leaves teams guessing when it comes to…
Asset Inventory Management
Asset Inventory Discovery and Management
Ordr Use Case Series
4Min Read
By Chris Westphal

Connected devices complicate enterprise security and contribute to increased risk for organizations that deploy them. Ordr addresses cyber asset visibility and security in use cases to help security, networking, and device owners manage their asset inventories. Ordr Covers Your Assets with Real-Time Asset Inventory Management
Ordr is a unique and powerful platform because it addresses a plethora of visibility and security use cases for connected devices. In this series of blogs we’ll cover use cases that are top of mind for security, networking, and device owners, starting with asset inventory and management.
In conversations with CISOs and CIOs, we consistently hear the same challenges when it comes to Internet of Things (IoT), Internet of Medical Things (IoMT), operational technology (OT), and other connected devices:
- Maintaining an up to date inventory of connected devices
- Finding connected devices that are not included in inventory
- Including device details that are critical for device management and security
The lack of a complete connected device inventory leaves teams guessing when it comes to managing devices and creates big gaps resulting in unknown risk when it comes to security. Whether you’re in IT ops struggling to keep up with the constant barrage of new devices, a security pro challenged to understand and mitigate risks, or a biomed engineer in healthcare tasked with managing device deployments, updates, and usage, connected device growth presents unique challenges across your organization.
Juniper Research estimates we’ll see more than 83 billion devices deployed by 2024, a 130 percent increase from the 36 billion in use today. With this and similar growth estimates, we’re faced with the reality that IT and security challenges will continue to expand as the volume and variety of connected devices grows.
Unique Challenges of Connected Devices
Compiling and maintaining an inventory of connected devices that is up to date with all the required details is challenging due to several factors, including the number and diversity of devices, improper procurement processes, remote users, and locations behind VPNs. In addition, many connected devices are not only unmanaged but unmanageable since they do not or cannot support agents, and scanning these devices is not always an option for fear of service impact. These factors mean traditional methods aren’t an option for device discovery.
The sheer volume, variability, and mobility of connected devices means inventory and status of devices is constantly changing. Relying on manual efforts or periodic snapshots of the network to maintain a device inventory comes with an almost certain risk of inaccuracy. You need to be able to discover and track your complete asset inventory, including unmanaged devices, and you need to be able to do it in real-time.
You need to be able to discover and track your complete asset inventory, including unmanaged devices, and you need to be able to do it in real-time.
Procurement processes that aren’t aligned with IT and security add to these challenges since they can introduce devices to an environment without being properly onboarded. This results in the potential for more unknown devices on the network, some of which may not meet organizational standards for management and security. In this category are devices that are added by individuals or teams that purchase them outside of organizational protocols. In the case of healthcare it can include vendors that work directly with physicians and drop off devices for evaluation.
Remote users, and locations behind VPNs provide additional challenges. You have less insight and control over devices being connected from users working from home. IP addresses from devices connecting over VPN can change rapidly making it difficult to ensure all connected devices are properly captured in inventory.
How Ordr Helps
Ordr addresses connected device challenges with deep packet inspection (DPI), artificial intelligence (AI), and machine learning (ML) to enable a real-time asset inventory that’s accurate and always up to date. By analyzing network data, we automatically discover every device connected to the network without the need for agents and without impact to device operations. We also accurately classify every device with details such as make, model, operating system, serial number, application/port usage, and location.
Device details are sent to the Ordr Data Lake and enriched with more than 80+ integrations to form a granular and complete profile of every device in the environment. Enrichment includes data from vulnerability and threat feeds, manufacturer and FDA recalls, IT tools to help track IP address changes and user logins, and more.
With Ordr, teams not only know what’s on the network but can also identify risks such as devices with an outdated operating system, unauthorized applications, vulnerabilities, or recalls.
With Ordr, teams not only know what’s on the network but can also identify risks such as devices with an outdated operating system, unauthorized applications, vulnerabilities, or recalls. Ordr also helps identify devices with weak passwords or certificates, and those exhibiting risky behavior that might indicate an active threat. This detail, combined with other insights from Ordr, is used to calculate a risk score for each device and help teams prioritize remediation tasks such as patching and mitigation efforts like quarantining or microsegmentation.
Ordr also integrates with existing CMMS or CMDB tools to enrich details for devices that already exist in inventory, and fill in the blanks with details for devices that were missing. With Ordr, you’ll create a single source of truth for all your connected devices that is always up-to-date and accurate. With that foundation, you can start to wrap your arms around the other unique challenges associated with managing and securing connected devices. In a future post, we’ll cover more on Ordr capabilities beyond asset management.
If you’d like to get a handle on your connected device asset inventory get in touch with us to learn more.
Chris Westphal
Head of Product Marketing
Chris is the Head of Product Marketing at Ordr where he helps drive awareness for connected device security and the value of the Ordr solution. Chris brings more than two decades of experience to his role with a background in enterprise security, cloud, and data center technologies. Most recently, Chris was head of product marketing at Salt Security, the leader in API protection, and has held product marketing leadership roles at companies including VMware, Illumio, and Adallom (acquired by Microsoft).
Interested in Learning More?
Subscribe today to stay informed and get regular updates from Ordr Cloud
Ready to Get Started?
-
 BlogOrdr is Good Medicine for CISOs
BlogOrdr is Good Medicine for CISOs…of the cybersecurity world, we deal with connected devices of the sort that make up the Internet of things (IoT), Internet of medical things (IoMT), and operational technologies (OT) that…
General
Ordr is Good Medicine for CISOs
3Min Read
By Darrell Kesti

The challenges of cyber asset attack surface management (CAASM) and enterprise protection mean that stress and burnout are a major concern for chief information security officers (CISOs), according to a recent study by Heidrick & Struggles. Ordr simplifies CAASM and relieves the stress. Did you catch the recent news that stress and burnout are the primary concerns for most chief information security officers (CISOs) these days? That was the result of a recent study conducted by the executive search firm Heidrick & Struggles as reported by CNBC last month. The survey found stress (59%) and burnout (48%) were identified as the top two personal risks by 327 CISOs from around the globe. Those results were compiled well before former Uber CISO Joe Sullivan’s controversial conviction on charges he hindered a federal investigation into a data breach at the ride-sharing company. Given the range and passion of opinions other CISOs have expressed in response to that case, it’s likely that stress is on the rise.
Scapegoats and Sacrificial Lambs
It’s not that surprising to learn that CISOs are under stress. They are responsible for keeping networks and data safe from a relentless onslaught of attacks from threat actors, and from data breaches that are a result of simple human error. If you spend any amount of time talking with members of the CISO community, as I do, you’ll hear the common complaint that they must manage high expectations and low budgets. You’re also likely to hear a lot of gallows humor involving scapegoats and sacrificial lambs.
I’m sympathetic to a CISO’s plight. In Ordr’s corner of the cybersecurity world, we deal with connected devices of the sort that make up the Internet of things (IoT), Internet of medical things (IoMT), and operational technologies (OT) that are the backbone of industrial and critical infrastructure enterprises. In that world, the pace of change and growth is astounding; it’s impossible to keep up. Consider the following statistics:
- By 2025 there may be as many as 83 billion connected devices active in commercial networks by 2024 (Juniper Research).
- At that time there will be more than 150,000 devices connecting to networks every minute (IDC).
- The average hospital IT infrastructure includes more than 100,000 connected devices, including more than 15,000 IoMT devices dedicated to critical care, and between 10-15 IoMT devices per bed.
Those are big numbers, and they only represent the devices a CISO knows about. There may also be hundreds more unmanaged devices connecting to their networks, enlarging the enterprise’s attack surface, and increasing the chances of a data breach. That’s because you can’t protect what you can’t see. And when vending machines, smart assistants, aquariums, Kegerators, Teslas, Pelotons, and any number of other stranger things decide to make themselves at home on the network, stress rises along with risk.
Just What the Doctor Ordr’ed
Ordr is aware of these trends, and we have just what the doctor ordered to ease the burden that they cause on both the CISO’s enterprise and psyche. Our platform excels at looking across the network to locate and identify each device. Within minutes, Ordr discovers, locates, and automatically classifies all the device assets that are operating on your network, including devices you knew you had, devices you forgot you had, devices you thought you lost, and the ones that you weren’t expecting. In addition to complete devices discovery, Ordr’s feature set is designed to make a CISO’s job easier, including:
- Automated asset inventory synchronized with your CMMS or CMDB.
- Continuous risk assessment uncovering vulnerabilities and risky communications.
- Vulnerability management to help with remediation and mitigation tasks.
- Improved incident response with dynamically created policies to stop attacks.
- Accelerated Zero Trust with dynamically created policies for NAC and segmentation.
- Simplified compliance with detailed reports and documentation to help with auditors and assessments.
And because the Ordr Data Lake is already populated with detailed information on millions of individual device types, every device we find is automatically and accurately profiled, and its communications patterns baselined and monitored. That’s important because connected devices operate in narrow, deterministic ways. Any deviation from normal can be considered as an indicator of compromise, and when Ordr detects a threat, we arm your teams with contextual insights and policies so you can take the right action, quickly. That protects your network by preventing attacks, containing threats, and enabling operational resilience by isolating mission-critical devices that need to remain in service.
You can’t protect what you can’t see. And when vending machines, smart assistants, aquariums, Kegerators, Teslas, Pelotons, and any number of other stranger things decide to make themselves at home on the network, stress rises along with risk.
The CISO’s team also benefits from these features. The ability to automate asset inventory, locate devices easily, and generate security policies on any networking or security infrastructure reduces human errors and frees IT and security personnel to focus on more strategic tasks. This can help CISOs ensure higher job satisfaction, reduce stress, and increase retention for his or her team.
A CISO’s Peace of Mind
Whether you are protecting a hospital, industrial facility, financial services firm, or any other enterprise that relies on a vast constellation of connected devices, Ordr is good medicine. When Ordr is at work a CISO has a little more peace of mind, reducing the stress that comes with being an organization’s Cyber Incident Scapegoat Offering. If you want more information about the Ordr connected device security platform, or if you’d like a demo, reach out and let us know.
Darrell Kesti
Darrell is VP Sales at Ordr. He joined Ordr as one of the original Account Executives in October of 2018 to help launch the field organization. In his prior role as Ordr’s Director of Healthcare Sales, Darrell drove significant growth in healthcare sales and helped position Ordr as the leader in connected device security. Darrell has had over 20+ years of Sales Leadership, Account Management, and Field Engineering experience supporting customers and partners while with leading security and networking organizations – ForeScout Technologies, FireEye, Mandiant, F5 Networks, and Secure Computing Corporation. Darrell earned a Bachelor of Science in Electrical and Computer Engineering from the University of Minnesota, Duluth.
Interested in Learning More?
Subscribe today to stay informed and get regular updates from Ordr Cloud
Ready to Get Started?
-
 NewsOrdr Secures $40 Million in Series C Funding
NewsOrdr Secures $40 Million in Series C Funding…organizations to understand, manage, and secure the growing number of connected devices in their environment, including Internet of Medical Things (IoMT), Internet of Things (IoT), and Operation Technology (OT). The…
Ordr Secures $40 Million in Series C Funding
Answers Increased Demand for Connected Device Security
4Min ReadSanta Clara, CA – June 1, 2022 – Ordr has raised an additional $40 million to meet the growing need for organizations to understand, manage, and secure the growing number of connected devices in their environment, including Internet of Medical Things (IoMT), Internet of Things (IoT), and Operation Technology (OT). The funding round was co-led by Battery Ventures and Ten Eleven Ventures, with participation from new investor Northgate Capital and continuing investors Wing Venture Capital, Unusual Ventures, Kaiser Permanente Ventures, and Mayo Clinic. Other investors in Ordr’s Series C include Silicon Valley entrepreneurs René Bonvanie, former CMO of Palo Alto Networks, Dan Warmenhoven, former Chairman and CEO of NetApp, and Dominic Orr, former Chairman and CEO of Aruba Networks. With this funding, Ordr has raised more than $90 million to date.
Ordr addresses two key enterprise initiatives associated with a growing reliance on and adoption of connected devices: digital transformation and Zero Trust. Each new device connection increases an organization’s attack surface, along with the potential for a breach or ransomware attack. In industries such as healthcare and manufacturing, a cyberattack impacting an IoT device can easily disrupt the entire business or become a life-threatening situation. For organizations to move quickly from “detection” to “response” requires insights into the compromised device, where it’s located, and what policies can be applied.
Ordr offers complete and accurate asset visibility, automates and enforces Zero Trust policies, and accelerates incident response by hours with insights into devices and risks. As a result, Ordr experienced more than 140% year-over-year growth in new customer revenue in its most recent quarter ending on March 31, 2022, is deployed in 3 of the world’s top 6 hospitals, and has been adopted across more than 150 manufacturing sites.
“Ordr has built a platform that not only solves an important market issue – the need to definitively understand and protect what is connecting to your organization’s network – but is truly scalable to keep pace with the speed of today’s businesses. We’ve worked with Ordr’s team and seen firsthand how well they’ve executed against aggressive goals. This additional funding will accelerate Ordr’s market leadership and success in the market,” said Dharmesh Thakker, general partner at Battery Ventures.
“We believe the connected device security market needs a strong, open, and independent player that prioritizes customer success, focuses on time-to-value, and integrates with all the key components of a customer’s security and network infrastructure. This funding validates our best-in-class approach and solidifies our leadership in the market,” said Greg Murphy, Ordr CEO.
Ordr plans to use the Series C funding to accelerate its sales and marketing efforts, especially in vertical markets such as healthcare, where the company has been named a market leader in the Healthcare IoT security industry by analyst firm KLAS Research for three consecutive years. The company will also look to further capitalize on steadily increasing demand from manufacturing and financial services, expand its channel and partnership programs, and accelerate investments in customer success.
“In order to advance their digital transformation goals, every organization needs to enable the visibility and security of connected devices, including IoT, IoMT, and OT. Ordr is a much-needed innovator in the market, with the ability to not only deliver granular visibility into devices, risks, and behaviors, but also automate and enforce Zero Trust policies to secure these devices from attacks,” said Justin Stebbins, partner, Northgate Capital.
“As an early investor in the company, I have witnessed Ordr’s impressive product evolution and growing traction within critical sectors, including healthcare, manufacturing, education, and extended enterprise IoT. They have developed one of the most scalable and technically robust platforms in the market, and some of the world’s leading organizations depend on it to fulfill important security needs and deliver business insights. The time is right to accelerate the company’s mission to be the leader in connected device security. We believe in their success and look forward to the next chapter.” said Alex Doll, Founder and Managing Partner of Ten Eleven Ventures.
Since its last round of funding, Ordr has experienced tremendous growth, coinciding with an increased understanding of the organizational risk represented by unknown connected devices. Some additional highlights since the last funding round include:
- Named a KLAS Research Healthcare IoT Security Market Leader for an unprecedented three years in a row.
- Named a Representative Vendor in the 2022 Gartner Market Guide for Medical Device Security Solutions for the second year in a row.
- Continued product innovation and market leadership in the healthcare industry with the launch of Clinical Defender, streamlining management of connected medical devices.
- Enhanced the company’s integrations with Cisco, making it even easier for Cisco customers to roll out Ordr across their network environments.
- Launched the Ransom-Aware Rapid Assessment to help companies quickly and accurately assess their ransomware risks.
- Successfully achieved SOC2 compliance to keep customer data secure.
“Data privacy and security are imperative IT initiatives within the healthcare industry with connected device security in particular as a critical need given the increase in connected devices in health care facilities. Kaiser Permanente Ventures is pleased to continue its investment in Ordr as a key technology leader in this space, to help protect connected devices automatically, preemptively and at scale across the enterprise,” said Chris Stenzel, executive managing director, Kaiser Permanente Ventures.
Continuing the momentum of the past year, Ordr today also strengthened its executive team with the addition of Paul Davis as the company’s new vice president of customer success. Paul has decades of experience in customer-facing roles at Axis Security, Splunk, Cisco, and other leading organizations. At Ordr, he will be responsible for managing customer relationships and ensuring the successful implementation and use of Ordr technology.
Interested in Learning More?
Subscribe today to stay informed and get regular updates from Ordr Cloud
Ready to Get Started?
-
 BlogWindows 7 End-of-Life is Near…Are You Ready to Take Control?
BlogWindows 7 End-of-Life is Near…Are You Ready to Take Control?…the network. In the case of a VLAN configuration with Access Control Lists for communication, the Security, HTM, and Network team could build the rule set for this ACL and…
Security Bulletin
Windows 7 End-of-Life is Near…Are You Ready to Take Control?
4Min Read
By Darrell Kesti

Medical devices with obsolete software and operating systems often remain in service for years, so Microsoft’s announcement that Windows 7 OS is being obsoleted means healthcare orgs with an inventory of Win7 devices need to protect those systems. Did you know that Windows 7 end of life is on January 14, 2020? This is only 300 days away, and today over 40% of the desktops deployed are still running this 10 year old OS. I can’t even imagine the number of imbedded IoT, OT, and Medical Devices where this OS is still used. This is going to be a big issue for the security community in 2019 to get their arms around this Windows 7 End of Life, the impact it will have on their security posture, and in medical and industrial fields – the safety risks it will expose to their patients and workers.
Here is a great article highlighting the EOL in more detail.
3 Ways Ordr Can Help You Take Control of Windows 7
- Ordr Discovery | Inventory | Categorization: Ordr captures the OS detail on devices as we do our automated Discovery, Inventory, Categorization and analysis of the traffic flows (Flow Genome).
Here is an example of a GE Ultrasound Machine, but the same would apply to other systems:
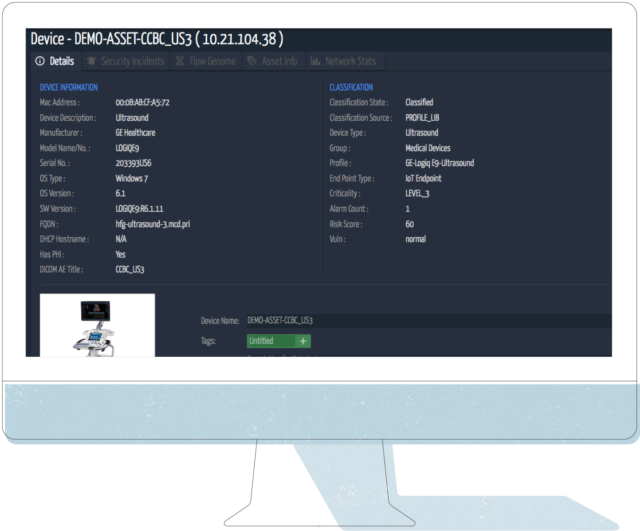
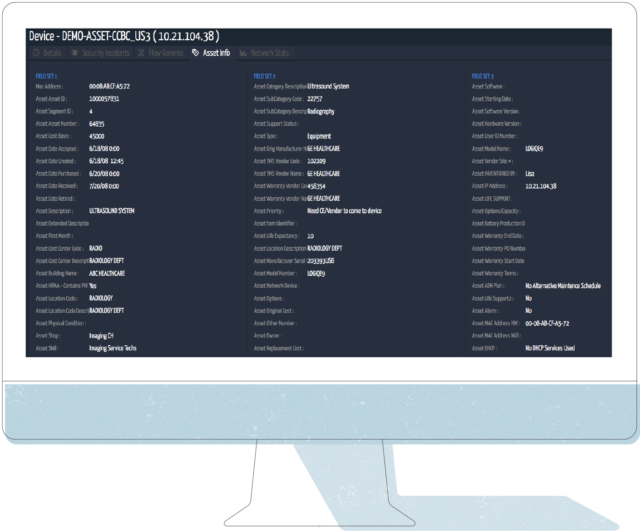
- Ordr integrates with CMDB / ITAM / CMMS Systems: If you integrate Ordr with your CMDB / IT Asset Management / CMMS system – say ServiceNow, Nuvolo, etc – you can further improve your visibility by leveraging the real-time always on view of the Ordr solution, to then update your records as you work to identify systems that need to be updated, who the device owners are, location of the equipment, where it is in its lifecycle, and perform post upgrade validation to close out the update work and document the remediation.
Here is a view of the same Ultrasound Machine as above, with the integrated asset detail from a CMMS system:
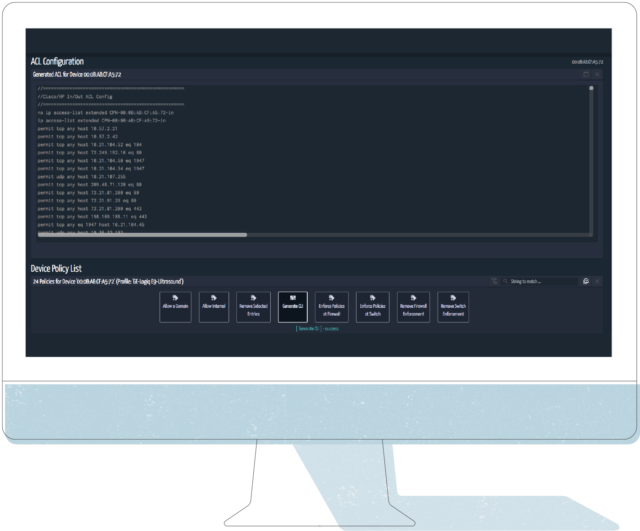
- Asset Info to Action: Armed with all this detail, Security and Network teams can start working with the appropriate lines of business (HTM in my example case), to figure out a plan to either upgrade the system, replace the system, or if can’t replace it and you are stuck with it on your network – build security controls around the device. This is where Ordr helps close the loop. One key area we can help is our capabilities around the behavior of the device in the network, the Flow Genome. Below you can see the 24 baselined normal flows Ordr has detected during this devices time on the network under monitoring.
See below, we will use this information in step 4:

Time to Take Control! OK, so you are stuck with the Windows 7 device on your network beyond 1/14/2020. You are armed with the information in steps 1 – 3. What do you do about it? How do you build in the right controls? This does depend on the environment, where there are firewall systems, NAC, network infrastructure that supports ACLs, etc. I will give you the most common actions I have seen, that should fit most of the customer environments you are working in.
Common controls Ordr can help you achieve
- Leave the device as is, but monitor it: This is probably the most common control. Monitor the device and respond to any alerts, change in behavior. There is concern especially with OT and Medical Devices around putting limiting controls in place. The good news is Ordr can alert on Behavior Violations, meaning if the device starts communicating outside of its Normal Baseline Flow. Ordr can be integrated into a workflow management system, send out email alerts on its own, fire off events to a SIEM or other Orchestration tool, or have a screen like the one below up in your SOC for human monitoring.
Below is a screen shot of our Incident Summary & Device Risk Dashboard: The Behavior Viol. count under Internal Communications is where we highlight behavior anomalies detected by the Flow Genome. All of this is linked to the events to quickly see and understand the reason for the alarm.

- Build a specific VLAN with ACLs for this Device Type: One approach to segmentation is with a custom VLAN for a device type, in this case GE Ultrasound Devices. The good part about Medical IoT, and IoT in general, is there is usually a consistent communication pattern for how it behaves on the network. In the case of a VLAN configuration with Access Control Lists for communication, the Security, HTM, and Network team could build the rule set for this ACL and limit the communication behavior. Or, you could let Ordr generate the ACL for you, that you apply in the environment. Here is an ACL based on the example system above:
- Integrate with your Network Access Control (NAC) solution: In this case Ordr can talk with your NAC system to put this device in a specific group (TAG), where there are ACL and/or TrustSec TAGs to identify and control access of this device. All of the attributes shown above can be shared, and the NAC solution can handle the controls around this device.
- Integrate with your Firewall system: Many customers are leveraging firewalls as part of their segmentation approach. Beyond the normal Internal to External (North / South) traffic control / protections from a firewall, they are putting more Firewall systems in the internal network (East / West) to segment the network. This helps with controlling the traffic flow, gives inspection points, and also gives the chance to apply other security tools of an Advanced Firewall feature set and the audit logging of the communication internally. Ordr integrates with firewall systems to either apply Firewall ACL’s to the traffic discovered by the Flow Genome, or to apply a Security TAG to the firewall. Many of these firewalls support Tagging as well for device groups, so you don’t have to build individual policies for each device. Ordr can give information to North/South and East/West firewall systems, to help with segmentation control.
What other strategies and ideas do you have to Take Control of the Windows 7 End of Life? Let us know.
Darrell Kesti
Darrell is VP Sales at Ordr. He joined Ordr as one of the original Account Executives in October of 2018 to help launch the field organization. In his prior role as Ordr’s Director of Healthcare Sales, Darrell drove significant growth in healthcare sales and helped position Ordr as the leader in connected device security. Darrell has had over 20+ years of Sales Leadership, Account Management, and Field Engineering experience supporting customers and partners while with leading security and networking organizations – ForeScout Technologies, FireEye, Mandiant, F5 Networks, and Secure Computing Corporation. Darrell earned a Bachelor of Science in Electrical and Computer Engineering from the University of Minnesota, Duluth.
Interested in Learning More?
Subscribe today to stay informed and get regular updates from Ordr Cloud
Ready to Get Started?
-
 BlogWelcome to the hyper-connected enterprise
BlogWelcome to the hyper-connected enterprise…in advance to prepare for the inevitability of change and its effects of cybersecurity and risk? The history of enterprise computing is one of increasing scale, complexity and heterogeneity. First…

Every evolution in IT leaves business leaders and CISOs scrambling to protect their vital data, applications, and resources. What can your enterprise do in advance to prepare for the inevitability of change and its effects of cybersecurity and risk? The history of enterprise computing is one of increasing scale, complexity and heterogeneity. First there was client-server computing, ushering in the PC era where there was a computer for every employee and several switch ports in every cubicle. And then the mobile enterprise, with a new generation of employees using their laptops, tablets and smartphones all the time, everywhere.
With each leap forward, IT and business leaders have scrambled to catch up and to protect their most critical data, applications and resources. We’re still gasping from the effort it took to control BYOD. But as hard as that was, the challenge was fundamentally one of human scale. Most users had a small handful of devices. Some ran Windows, some IOS, some Linux. IT could assign most of those users to a relatively small number of roles (often as simple as “guests” vs. “employees”). Yes, certain classes of employees had different levels of access, but in truth IT rarely had to define more roles than there were departments on an org chart. Great vendors stepped forward with intelligent solutions to make role-based access work (mobility controllers, next-generation firewalls, NAC and identity management). A small number of insanely hard-working employees in IT and Security could keep up. Barely.
We are now experiencing the emergence of the hyper-connected enterprise, in which everything is connected. The HVAC system. Security cameras. Point of Sale devices. Digital signage. Sensors. Heart rate monitors and infusion pumps. Complex, multi-million dollar manufacturing systems. IoT devices of every kind. If these things aren’t working, productivity plummets, revenue drops and lives are impacted. And if business leaders don’t know where they are or how they are being used, they risk spending millions on unnecessary cap ex.
In every dimension, the challenge for IT and business leaders is several ordrs (sorry!) of magnitude greater than it was a few short years ago. Instead of 3-4 devices per employee, a Fortune 500 organization or healthcare system will have millions of connected devices, from hundreds of different manufacturers, many running a proprietary OS. Each class of devices is purpose-built — with specifically defined functions, unique behavior patterns and potential vulnerabilities. Where IT used to administer a small handful of user roles, these devices have no users and ‘roles’ do not apply. Instead of managing users, they need to regulate each individual device. And that means they need to define and enforce thousands of specific policies.
The resulting complexity is literally inhuman in scale. A seemingly simple task like completing an inventory of connected devices is neither simple nor feasible for human beings at such scale. It’s about as simple and feasible as counting the stars in the sky. Even if your staff could do it, the data they gathered would be out of date before their report was compiled. If humans can’t even count the devices, there’s no possible way they can monitor them, understand their myriad functions or apply appropriate security policies to them. And if the CFO asks them for a report on usage of these systems and devices as she’s preparing next year’s capital budget? Good luck.
The only way to address this inhuman complexity is by mapping the ‘device flow genome’ through the application of advanced machine learning at a truly massive scale, continuously processing enormous amounts of data to identify everything that is connected and baseline their behavior patterns. Once you can do that, you can identify unusual or dangerous patterns and using actionable AI to automatically create policies that prevent incidents from occurring. That’s what we mean by true ‘closed-loop security.’ And then, because of all the data you’d be processing, you could deliver incredibly valuable insights to business stakeholders about how those devices and systems are being used and how they are performing. That can save organizations millions and extend the life of their assets.
That may sound far-fetched, costly and difficult to implement, but it’s not. In fact, most organizations already have the necessary infrastructure and tools in place: routers and switches, wireless controllers, next-generation firewalls, NAC, and the intelligent vendor-provided systems that operate them . The problem is that even the largest organizations don’t have enough people to interact with each of those intelligent solutions to harness their power at the scale necessary. What’s been missing is a systems control engine capable of processing the massive amounts of data being generated by all of the systems and devices in the hyper-connected enterprise – and translating that information into actionable policies that your smart infrastructure can enforce.
That’s why Ordr exists and that’s what the Ordr Systems Control Engine does. At a massive scale, for the largest enterprises in the world. It’s complex. But we’re a team of networking and security veterans, and we’ve been working for years to build a solution capable of handling that complexity while making your life simple.
The hyper-connected enterprise is here. Take control.
Greg Murphy
Greg joined Ordr as CEO in December 2018. Previously, he was VP Business Operations for the HPE Aruba Group, the 4,000 person networking and IoT business unit of Hewlett Packard Enterprise. In that role, Greg was responsible for leading the business integration of Aruba and HP Networking following HP’s $3 billion acquisition of Aruba Networks in 2015. Greg held multiple prior senior executive positions within Aruba, including SVP Business Operations, GM of network management software, GM of outdoor and mesh products and VP of Marketing. Greg joined Aruba in 2008 through its acquisition of AirWave Wireless, a network management software provider that Greg founded and led. Greg received his M.A. from Stanford University and his B.A. from Amherst College.
Interested in Learning More?
Subscribe today to stay informed and get regular updates from Ordr Cloud
Ready to Get Started?
-
 BlogBOD 23-01: Shedding Light on Federal Enterprise Asset Visibility
BlogBOD 23-01: Shedding Light on Federal Enterprise Asset Visibility…to ensure asset inventories are up-to-date. The philosophy behind the directive is sound. Today’s IT estates are complex and include thousands of components operating on-premises and in the cloud. Servers,…
Security Strategy
BOD 23-01: Shedding Light on Federal Enterprise Asset Visibility
4Min Read
By Chris Westphal

CISA’s Binding Operational Directive 23-01 (BOD 23-01) affirms the importance of full enterprise asset visibility. Ordr offers insights on BOD 23-01 to explain why real-time asset discovery and visibility is vital to compliance with the directive. Binding Operational Directive 23-01 can help close a government security gap
The Cybersecurity & Infrastructure Security Agency (CISA) recently issued an advisory on a dozen new exploits and vulnerabilities affecting industrial control systems (ICS) from nine different manufacturers. The warning is the latest in a growing body of evidence that critical public infrastructure–things like the power grid, transportation systems and facilities, government buildings, and public safety organizations–will soon become the primary target of threat actors in an escalation of attacks against national economic interests. In fact, some observers believe a shift in strategies in the war between Russia and Ukraine is proof that such an escalation is well underway.
It’s hard to argue that threat actors are not becoming increasingly aggressive and willing to attack targets, even when there might be a human cost. Hospitals and healthcare services providers have seen a sharp increase in attacks over the last three years, and research suggests those attacks are associated with an increase in patient mortality. Even the U.S. Federal Reserve warns that attacks on industrial enterprises and infrastructure could impede economic activity and seriously undermine confidence and stability in national financial systems.
Setting a Good Example
And so, as attention turns toward the hardening of private and public infrastructure against cyberattacks, leaders in Washington, D.C. are trying to set a positive example by updating their own security policies. When the White House issued the Executive Order on Improving the Nation’s Cybersecurity on May 12, 2021, it established the foundation for the government’s strategy to address the protection of a sprawling and complex federal IT infrastructure comprising hundreds of different agencies. Then in early March this year the White House published its National Cybersecurity Strategy to bring the issue into sharper focus.
The Cybersecurity & Infrastructure Security Agency (CISA) took a big step forward when it issued Binding Operational Directive (BOD) 23-01,Improving Asset Visibility and Vulnerability Detection on Federal Networks.
But the work toward improving the federal government’s readiness and resilience against cyberthreats was underway before the release of the National Cybersecurity Strategy. In October of 2022 the Cybersecurity & Infrastructure Security Agency (CISA) took a big step forward when it issued Binding Operational Directive (BOD) 23-01, Improving Asset Visibility and Vulnerability Detection on Federal Networks.
Connected Device Visibility is Critical

BOD 23-01, which had a deadline of April 3, 2023, requires all federal civilian executive branch (FECB) agencies to establish the means for effecting “continuous and comprehensive asset visibility” as a first step in assessing and monitoring cyber risk. CISA did not identify penalties for missing the April 3 deadline, but there are ongoing reporting and improvement timelines to ensure asset inventories are up-to-date. The philosophy behind the directive is sound. Today’s IT estates are complex and include thousands of components operating on-premises and in the cloud. Servers, routers, switches, software, application, services, and all kinds of devices, many of which are practically invisible to traditional IT management systems.
This is especially true for connected devices, including the Internet of Things (IoT), Internet of Medical Things (IoMT), operational technology (OT), and more. And what BOD 23-01 does is acknowledge that, without a complete accounting of every single device that connects to the enterprise—expected or unexpected, and for however long it remains connected—each is a potential vector for attack. Also, when connected assets are unaccounted for, an organization’s configuration management database (CMDB) will be inaccurate, leading to other IT operations and security issues that can put the enterprise at risk. Ordr’s experience with connected device discovery illustrates the wide variety of unexpected devices that can be found operating in some enterprises alongside mission-critical equipment. Vending machines and building controls, Tesla cars and Kegerators, Alexas and Pelotons, all connected to the network and communicating out to the Internet, unmanaged and unknown to IT operations and security.
See IT, Protect IT
You can’t protect what you can’t see, and so device discovery, visibility, and monitoring is vital to maintaining security at a high level. Ordr is not only able to discover and monitor these devices in real-time, but the extensive Ordr Data Lake contains detailed profiles of millions of IoT, IoMT, and OT devices, identifying their purpose and operational profile. That enables security teams to identify devices with vulnerabilities, establish a risk score for every device operating in the network, detect when devices exhibit indicators of compromise, and automate policy creation to accelerate response and prevent attacks targeting connected devices or prevent lateral movement. These capabilities support BOD 23-01’s objective to “make measurable progress toward enhancing visibility into agency assets and associated vulnerabilities… an important step to address current visibility challenges at the component, agency, and [federal civilian executive branch] enterprise level.”
These capabilities support BOD 23-01’s objective to “make measurable progress toward enhancing visibility into agency assets and associated vulnerabilities… an important step to address current visibility challenges at the component, agency, and [federal civilian executive branch] enterprise level.”
It’s good that the U.S. federal government recognizes that maximizing the effectiveness of a cybersecurity program demands a full accounting of every device operating in the network. That is the foundational tenet to Ordr’s mission, and it has been embraced by our customers, including many of the world’s largest healthcare, financial, and manufacturing organizations. And for our customers in the federal government, they had a head start on meeting (and likely exceeding) requirements ahead of CISA’s April 3 deadline.
If your agency or organization recognizes that it has blind spots it needs to address to take a full inventory of every device it has connected to its network, give us a call. We can run a demonstration that can show you every connected device on the network. And with a complete accounting of your connected assets, you can build a plan to see, know, and secure your enterprise.
Chris Westphal
Head of Product Marketing
Chris is the Head of Product Marketing at Ordr where he helps drive awareness for connected device security and the value of the Ordr solution. Chris brings more than two decades of experience to his role with a background in enterprise security, cloud, and data center technologies. Most recently, Chris was head of product marketing at Salt Security, the leader in API protection, and has held product marketing leadership roles at companies including VMware, Illumio, and Adallom (acquired by Microsoft).
Interested in Learning More?
Subscribe today to stay informed and get regular updates from Ordr Cloud
Ready to Get Started?
-
 NewsOrdr Announces Expanded Partnership With Fortinet
NewsOrdr Announces Expanded Partnership With Fortinet…IoT and unmanaged devices. The integration of Ordr Systems Control Engine (SCE) with the Fortinet Security Fabric, including FortiManager, FortiGate, and FortiNAC, through the Fortinet Open Fabric Ecosystem, dramatically reduces…
Ordr Announces Expanded Partnership With Fortinet
To Deliver Industry-Leading Security Across Network-Connected Devices
3Min ReadSANTA CLARA, Calif., February 10, 2021 — Ordr, the leader in security for all connected devices, today announced that the company has expanded its partnership with Fortinet, a global leader in broad, integrated and automated cybersecurity solutions, to deliver an industry-leading integrated solution to address the security challenges posed by widespread IoT and unmanaged devices. The integration of Ordr Systems Control Engine (SCE) with the Fortinet Security Fabric, including FortiManager, FortiGate, and FortiNAC, through the Fortinet Open Fabric Ecosystem, dramatically reduces the time and effort needed for customers to create and maintain a complete and detailed asset inventory, determine safe communication patterns, and create effective, business-relevant firewall policies. This integration also enables NAC segmentation policies that automatically update as devices are added, removed, and move around the network.
As the number of connected devices on corporate networks—from critical business infrastructure such as IP-enable physical security devices to consumer devices such as smart speakers—has grown exponentially, they have become lucrative targets for attack. A majority of IoT devices, including critical and expensive systems like MRIs, commonly run legacy software that lack anti-malware and patch management support and are thus an inherent risk to an organization. The only way to reduce threat exposure is to first identify every connected device and its risk, then proactively apply protection policies through firewall rules or NAC policies that permit only necessary and safe communications.
Ordr SCE automatically creates a complete asset inventory, identifies and prioritizes asset risk, and tracks and risk-rates asset communications patterns. Ordr transmits this critical security context to Fortinet FortiGate, FortiManager, and FortiNAC, allowing administrators to create and apply firewall and NAC policies using business-relevant groups, classifications, and device names, while understanding the full risk profile and impact of each change. Ordr further reduces administrative costs by automatically updating asset groupings as devices join and leave the network, as well as by creating and transmitting security policies directly to FortiGate and FortiManager for enforcement.
Benefits:
- Discover and inventory every connected network asset, including the massive volume of IoT and unmanaged devices, and make available across the Fortinet Security Fabric, from endpoint to edge, through FortiNAC, FortiManager, and FortiGate
- Establish comprehensive security controls that restrict IoT devices to known-good network behaviors
- Manage firewall and NAC policies using business-relevant context such as device type, manufacturer, location, risk, and function rather than IP addresses
- Automate updates of firewall groups and address info to ensure consistent policy enforcement regardless of device location, VLAN, or IP assignment, thus drastically reducing operational costs and downtime
- Protect critical devices with automated, zone-based segmentation and microsegmentation within zones
Ordr also incorporates additional network intelligence from FortiGate deployments. Ordr SCE can consume network traffic information, wireless device context, and other data, in some cases eliminating the need for an Ordr sensor in remote offices. Ordr SCE also correlates threat information with FortiGate, clearing alerts when suspect traffic has been blocked by the firewall.
“Fortinet is a leader in enterprise security and today’s announcement bolsters our customers’ ability to discover and inventory every connected device, including the massive volume of IoT and unmanaged devices on a typical network,” said Bryan Gillson, VP of Business Development at Ordr. “It is now easier than ever for customers to establish and automate comprehensive security controls that restrict the behaviors of connected devices. It’s also easier to manage firewall and NAC policies using business-relevant context such as device type, manufacturer, location, and function, rather than manually checking IP addresses.”
“FortiGate Next-Generation Firewalls enhance Ordr’s visibility across the infrastructure by sending flow data to a centralized Ordr sensor,” said John Maddison, EVP of products and CMO at Fortinet. “This extends the visibility in remote and lateral communications to improve overall infrastructure visibility, enhance anomaly detection, and increase the efficacy of FortiGate zone-based segmentation and FortiNAC access control policies. FortiGate NGFWs can also reduce incident response efforts by informing Ordr when malicious traffic is dropped at the firewall.”
“With just a few clicks, administrators can create business-relevant segmentation policies in FortiGate NGFWs that ensure devices of a specific type and role only connect over approved communication channels with necessary destinations—all specific to the organization,” said Josh King, Director of Security Solutions at Carousel Industries, an Ordr partner whose team of more than 1,300 IT professionals provide IT, security, cloud and managed services to thousands of businesses. “This drastically reduces operational costs and downtime, which is essential for companies across all verticals – including healthcare, manufacturing, life sciences, financial services and retail.”
To learn more about how to discover all network-connected devices and automate network segmentation workflows, visit https://ordr.net/partners/fortinet/
About Ordr
Ordr makes it easy to secure every connected device, from traditional IT devices to newer and more vulnerable IoT, IoMT, and OT. Ordr Systems Control Engine uses deep packet inspection and advanced machine learning to discover every device, profile its risk and behavior, map all communications and protect it with automated policies. Organizations worldwide trust Ordr to provide real-time asset inventory, address risk and compliance and accelerate IT initiatives. Ordr is backed by top investors including Battery Ventures, Wing, and TenEleven Ventures. For more information, visit www.ordr.net and follow Ordr on Twitter and LinkedIn.
Interested in Learning More?
Subscribe today to stay informed and get regular updates from Ordr Cloud
Ready to Get Started?