Search Results:
”Role of Huawei H19-431_V1.0 Exam Questions in Getting the Highest-Paid Job 💆 Search for { H19-431_V1.0 } and download exam materials for free through [ www.pdfvce.com ] 🏸Premium H19-431_V1.0 Files”
-
 BlogA Response to Maui Ransomware
BlogA Response to Maui Ransomware…large and complex mix of connected devices like IoT, IoMT, IT, OT, and more. Ordr helps them ID and mitigate the threat quickly. CISA, the FBI and the U.S. Treasury…
Security Strategy
A Response to Maui Ransomware
Ordr Security Bulletin
3Min Read
By Pandian Gnanaprakasam

North Korean cybercriminals using Maui ransomware are targeting the healthcare industry. Those organizations are more vulnerable because they operate a large and complex mix of connected devices like IoT, IoMT, IT, OT, and more. Ordr helps them ID and mitigate the threat quickly. CISA, the FBI and the U.S. Treasury have released a joint Cybersecurity Advisory (CSA) about North Korean-sponsored attackers using Maui ransomware to target the healthcare industry. We urge healthcare organizations to quickly act now to protect their systems.
Every connected device increases the attack surface. Healthcare organizations cannot afford to only do the minimum to secure their networks – especially when patient safety is at stake. Hospitals and healthcare organizations rely on all kinds of connected devices to operate and they don’t always know exactly what’s connecting to their networks. This makes it hard to immediately understand what’s at risk when these ransomware alerts are issued.
In addition, healthcare organizations often rely on older, more vulnerable legacy devices and equipment that have a long lifespan and can’t be taken out of service. These legacy devices (such as those running outdated Windows 7/8/10 operating systems) often represent about 20% of devices or more in a network.
The Maui Ransomware is more challenging to detect than many other types of ransomware because of the way threat actors execute these operations remotely. With help from our customers, we’ve validated that no communications from their devices to North Korea exist, other than DNS traffic from guest devices. However, this is a wake up call for healthcare organizations to shut down all communications to North Korea so we are protected from future breaches.
Here are some immediate steps to take based on this Maui Ransomware advisory.
Monitor device communications flows
Track communication to certain countries like Russia and N. Korea and understand the web reputation of the sites these devices are going to. Medical devices should not have a legitimate business need to be communicating with certain countries.
Healthcare organizations can do this using the Ordr traffic analysis tool.
Additionally, similar to our Russian communications report, and the detailed analysis we performed, Ordr will be delivering a North Korean communications report. Our customers can generate this report when they need the data, or schedule it daily or weekly.
Monitor privileged communications
Healthcare organizations need to monitor devices using privileged protocols, for example, SMBv1 and RDP protocols. Security teams need to scrutinize the usage of these protocols and shut them down if they are not required. These protocols come into play for device manufacturers to perform maintenance, but access should be enabled only for the duration of services needed.
Ordr tracks connected devices using these protocols continuously today. Our customers can get details about these devices with one click on our dashboard.
Monitor all remote execution activities
The Maui ransomware is designed for manual execution by a remote actor via a command-line interface, using it to target specific files on the infected machine for encryption. So, it is imperative to watch all the remote execution commands like telnet/rsh, rcp, rlogin etc., and track such activities carefully. The Ordr platform allows you to identify all devices using these methods to make sure they are all open and available only for a very few select devices and shut this down on all other devices if the need that opened this up has been fulfilled.
Monitor all user login attempts
It is imperative to monitor closely all windows workstations and servers that serve clinical needs and work closely with medical devices. The Ordr platform provides a list of all logins attempts on any windows machine to track and identify unwanted logins. It is advised to clean up the numerous unnecessary accounts on various machines in clinical setting using a report from Ordr, following the principle of least privilege.
Monitor for IoC files
Healthcare organizations can detect files that are used by the Maui ransomware threat actors, for example maui.exe/maui.log/maui.key and its variations as well as malicious file indicators. Customers using Ordr can identify the presence of these files from the software inventory that is extracted from devices.
Baseline all connected devices
The initial infection (i.e., entry point) for ransomware may be challenging to detect. Therefore, it is important to focus on other stages of the kill chain, for example lateral movement. Healthcare organizations can baseline connected devices using Ordr to ensure they are not deviating from their baseline of “normal behavior”. Whenever ransomware takes over one of these devices, there is lateral movement, and this baselining will immediately detect abnormal internal communications.
We hope the above guidance helps all healthcare organizations. Read our ransomware best practices and ensure that you are keeping your connected devices secure. Due to patient care disruption, more and more healthcare organizations are resorting to quickly paying ransom, as they cannot even afford to wait for systems to recover on their own through backups. However, note that paying a ransom does not guarantee data will be recovered. Additionally, lightning does hit twice in the case of ransomware victims, i.e., organizations that have paid ransom have been targeted again.
Finally, if you need assistance, Ordr and our team are here to help. Contact us today to get the conversation started.
Pandian Gnanaprakasam
Pandian has more than 20 years of product and engineering leadership experience and is also a serial entrepreneur. Before founding Ordr, he was the Chief Development Officer at Aruba, responsible for all of engineering and product management functions. Aruba, an enterprise mobile wireless company, was acquired by HPE for $3 Billion in March 2015. Before Aruba, Pandian served as the head of engineering for Cisco’s multi-billion-dollar Wi-Fi business unit and before that as VP of engineering for low-end switching product lines. He graduated with a master’s degree in Electrical Engineering from IIT, Chennai, India and holds several patents to his credit in various networking technologies.
Interested in Learning More?
Subscribe today to stay informed and get regular updates from Ordr Cloud
Ready to Get Started?
-
 NewsOrdr Unveils Cybersecurity Innovations and Ransom-Aware Rapid Assessment
NewsOrdr Unveils Cybersecurity Innovations and Ransom-Aware Rapid Assessment…and vulnerable devices in the environment, reviewing user activity and devices access, and monitoring for communications to ransomware sites. The Ransom-Aware Rapid Assessment comes with a detailed report of findings…
Ordr Unveils Cybersecurity Innovations and Ransom-Aware Rapid Assessment
Expands Leadership In Connected Device Security
4Min ReadSANTA CLARA, Calif. – October 28th, 2021 – Ordr, the leader in connected device security, announced new cybersecurity features along with a Ransom-Aware Rapid AssessmentTM service to help security teams accelerate their response to ransomware and other advanced attacks.
Ransomware attacks have accelerated in the past year, due to the ready availability of ransomware as a service, the expansion of the attack surface from connected devices and remote work, and the ease of ransomware payments using cryptocurrency. Enterprises are recognizing that in order to move quickly from threat detection to response, security teams need context on the device that is under attack – what it is, where it is located, whether they can act upon the device and exactly what mitigation steps are possible.
Ordr provides these answers via comprehensive visibility into devices, their corresponding network flows, risks, and anomalous behaviors, along with automated policies to proactively, reactively and retrospectively respond to attacks.
Highlights of the new cybersecurity features and benefits in the latest Ordr Hydrangea Fall 2021 Release include:
- Ransom-Aware Rapid AssessmentTM –Ordr now adds Ransom-Aware Rapid Assessment as an additional services This assessment, available from Ordr and its reseller partners, evaluates ransomware exposure risks in an organization, including identifying threats and vulnerable devices in the environment, reviewing user activity and devices access, and monitoring for communications to ransomware sites. The Ransom-Aware Rapid Assessment comes with a detailed report of findings and recommendations to help organizations prepare for an attack.
- Behavioral-based tracking and visualization of suspicious communications – Ordr baselines the behavior of every device so that “abnormal” communications can be detected. Security teams can now create policies and alert when “normal” behavioral patterns are violated, such as devices communicating with blocked IPs and URLs, banned countries and malicious sites. Ordr automatically provides a visual representation of communications to newly discovered malicious domains via the Ordr Traffic Analysis view, or security teams can customize their view to include specific malicious domains targeting their industry.
- Risk customization – Every enterprise measures risks differently based on the probability of an attack to the business. Ordr now adds the ability for risk and security customization by security teams including multiple high fidelity threat feeds controlled by weightages, risk score customization, custom alarm notifications, and flexible policy groups to customize policies by business context and/or protocol interactions.
- Multi-stage, correlated kill chain detection – In addition to the ability to detect East West lateral movement via its integrated threat detection engine, Ordr now adds new threat detection capabilities including application anomaly detection for high-risk protocols (SMB, RDP, etc.), IP based TOR detection and special purpose scanning engine enhancements to unearth vulnerabilities like PrintNightmare. Every device risk score computation correlates risks from multiple threat events in the kill chain to surface key security issues.
- Retrospective security – As security teams receive new indicators of compromise, it is important to incorporate a model of retrospective security, where the latest threat intelligence is continuously applied to historical device behavior and communications. Ordr adds retrospective analytics to track prior communications to new indicators of compromise. This can identify compromised devices that have slipped past preventative security measures. Ordr comprehensive device, network and behavioral context can be used to shorten the duration in triaging any malware, and to aid in forensics analysis. In one customer deployment, Ordr identified a compromised device behaving maliciously more than 15 days before the FBI indicators of compromise were published.
“As threat actors continue to target organizations around the world with ransomware, security teams need to understand where their risks lie. Ordr helps organizations understand their ransomware exposure and readiness. This will be invaluable to every organization trying to prepare against this imminent threat, “ said Frank Rondinone, President and Founder, Access2Networks.
“The enhancements in this release further bolster what is the most complete agentless device security platform in the industry. We’re making it easier than ever for enterprises to customize their risks, detect threats specific to their industry, continuously manage risks and secure every connected asset everywhere,” said Pandian Gnanaprakasam, co-founder and Chief Product Officer of Ordr.
The Ordr platform is already helping security teams reduce their time to detect and respond to attacks. In a KLAS Research customer interview, one Chief Information Security Officer said Ordr had reduced their incident response time by hours:
“The biggest outcome is a significant decrease in the amount of incident response time. We have used Ordr Platform as part of our incident response with ransomware. Because we couldn’t run our antivirus on our machines, we were able to go in and identify the specific machine on the Ordr Platform and provide a picture to the field support. The network engineers had already logged into the Ordr Platform, saw the traffic and killed the port so that it couldn’t communicate. That was very handy so that when a field support person walked into the room, they knew exactly where they were going. We were able to get the medical devices back up and running on our network and segmented really quickly. Ordr made that quick turnaround happen. We have factored the utilization of Ordr platform into our incident response plans. We have been able to reduce our response time by hours. We already had a really robust response time and plan, and the system sped things up significantly.”
For ransomware best practices and insights: Download Ordr’s ebook “Ransomware:These Four Best Practices Could Save You $4M”
Interested in Learning More?
Subscribe today to stay informed and get regular updates from Ordr Cloud
Ready to Get Started?
-
 BlogImproving the Nation’s Cybersecurity: A Reflection on the Executive Order
BlogImproving the Nation’s Cybersecurity: A Reflection on the Executive Order…one of the voices speaking in support of greater federal involvement and calling out the need for greater attention to protecting public services and infrastructure. And we were pleased to…
Security Strategy
Improving the Nation’s Cybersecurity: A Reflection on the Executive Order
3Min Read
By Greg Murphy

On the afternoon of May 12, President Joe Biden issued his Executive Order on Improving the Nation’s Cybersecurity. The executive order came on the heels of a ransomware attack that shut down operation of a major U.S. refined products pipeline system, a critical infrastructure operator that supplies approximately 40% of the gasoline supply to states along the U.S. East Coast.
As gasoline stopped flowing from suppliers to service stations, prices shot up, shortages broke out and drivers rushed to fill their tanks, unsure of how long the effects would last. The impact of this attack was consequential, dramatically illustrating the vulnerability of key pieces of our economy, but it was not an isolated event. The Executive Order on Improving the Nation’s Cybersecurity was not a knee-jerk reaction to a singular event. It is the result of years of attacks on government, industry, and individual organizations and of a steady cry from both the public and private sector to enlist the resources of our federal government in the fight against cybercrime.
Ordr has been one of the voices speaking in support of greater federal involvement and calling out the need for greater attention to protecting public services and infrastructure. And we were pleased to see that the new executive order called out the need to focus attention not just on information technology (IT), but on operational technology (OT), and the importance of Zero Trust.
OT Security
Operational technologies are the industrial hardware and software systems that form the backbone of industry. Manufacturing equipment, scientific equipment, facilities management controls, transportation and logistics infrastructure, and, yes, the valves and monitors and other gear essential to managing critical operations.
In many cases these systems were not designed with cybersecurity in mind and have been in place for decades. But, as our world grows more interconnected and dependent on technology, the lines between IT and OT have blurred. Those vulnerable systems are an attractive target for threat actors who can exploit weaknesses in IT infrastructure to move laterally into OT networks and execute attacks intended to extract valuable data, or disrupt operations through sabotage or extortion. Read Jamison Utter’s article on 90% of OT Security attacks being primarily common attacks like ransomware, and our Dir of Product Management Srinivas Loke’s response to DarkSide to understand our perspective more.
Zero Trust for Connected Devices
We are also pleased to see Zero Trust called out as one of the key architectural tenets within the executive order. When it comes to the volume of connected IT, IoT, IoMT and OT in particular, it is impossible for any security team (even the government) to “react” to potential security alerts with these devices. Visibility into devices and their risks, along with proactive Zero Trust policies for mission-critical or vulnerable devices will limit the attack surface and mitigate risks, reducing the Security Operations Center (SOC) or Cyber Security Incident Response Team (CSIRT) burden of investigating alerts.
We’ve been advocating for Zero Trust for connected device security for several years now, and in fact, our platform is designed to make it simple to not only create Zero Trust network policies but also ensure that they can be properly enforced across existing networking and security infrastructure.
The executive order has set a number of priorities, including:
- Improve the Federal Government’s ability to detect vulnerabilities and incidents on federal government networks;
- Standardize the playbook for responding to cybersecurity vulnerabilities and incidents; and,
- Improve the Federal Government’s investigation and remediation capabilities following cyberattacks.
At first glance, the Executive Order on Improving the Nation’s Cybersecurity seems to set overly ambitious goals for meeting these objectives on aggressively accelerated schedules. In fact, the clock is already ticking on deadlines that arrive in as little as 14 days. But the experience and innovation that has been happening within the private sector puts these goals well within reach.
For our part, Ordr already works with many federal agencies to achieve the goals and objectives the White House has articulated. Our technology is adept at identifying the many vulnerabilities that plague OT, and at executing real-time response to detect and isolate attacks that occur, preventing threat actors from moving laterally to gain the information and leverage they need to disrupt operations. We are also proven in our ability to execute Zero Trust policies in industries like healthcare, manufacturing, financial services, education, and more. We are eager, excited and ready to be a part of the mobilization effort that improves the nation’s cybersecurity.
Greg Murphy
Greg joined Ordr as CEO in December 2018. Previously, he was VP Business Operations for the HPE Aruba Group, the 4,000 person networking and IoT business unit of Hewlett Packard Enterprise. In that role, Greg was responsible for leading the business integration of Aruba and HP Networking following HP’s $3 billion acquisition of Aruba Networks in 2015. Greg held multiple prior senior executive positions within Aruba, including SVP Business Operations, GM of network management software, GM of outdoor and mesh products and VP of Marketing. Greg joined Aruba in 2008 through its acquisition of AirWave Wireless, a network management software provider that Greg founded and led. Greg received his M.A. from Stanford University and his B.A. from Amherst College.
Interested in Learning More?
Subscribe today to stay informed and get regular updates from Ordr Cloud
Ready to Get Started?
-
Knowledge BaseRipple20: How to identify and protect vulnerable devices
…the cybersecurity firm JSOF discovered the vulnerabilities in 2020. They named the vulnerabilities Ripple20 because of their potential to cause a “ripple effect” across supply chains of which IoT devices…
Ripple20: How To Identify And Protect Vulnerable Devices
5Min ReadIt’s one thing to hear about theoretical security vulnerabilities that could impact IoT devices. It’s another to know that serious security flaws have existed for decades in a software library that is widely used in the IoT ecosystem.
That’s exactly what happened in the case of Ripple20, a series of security vulnerabilities that impact hundreds of millions of IoT devices. This article explains what Ripple20 is, why it’s dangerous and how companies can help mitigate threats like Ripple20 within their network.
What is Ripple20?
Ripple20 is the name that security researchers at JSOF gave to a collection of vulnerabilities that they discovered within a software library first developed in the 1990s by a company called Treck. The library is a lightweight implementation of a TCP/IP stack, meaning that it provides the core functionality that devices need to connect to networks.
Researchers at the cybersecurity firm JSOF discovered the vulnerabilities in 2020. They named the vulnerabilities Ripple20 because of their potential to cause a “ripple effect” across supply chains of which IoT devices are a part. In other words, the vulnerabilities impact not just end-user devices (like printers or home security systems), but entire operational networks that include IoT hardware at any layer. For example, IoT sensors that help manage environmental conditions on a manufacturing floor and are affected by Ripple20 could have a ripple effect that compromises the security of “downstream” participants in the supply chain of which the facility is a part.
Although the Ripple20 vulnerabilities did not come to light until 2020, researchers believe that they have existed for at least twenty years.
What is Treck?
Treck is a nearly ubiquitous embedded TCP/IP that works well on devices with limited hardware resources. That feature made it a very popular solution for IoT devices, which typically lack the resources to run the more demanding types of software that are common on PCs or servers.
The library is consequently in widespread use, and likely places “hundreds of millions” of devices at risk, according to JSOF. Those devices represent a broad category of IoT use cases, from home and enterprise printers, to Industrial Control Systems (ICS), to healthcare equipment and beyond.
What are the effects of Ripple20?
As noted above, the Treck library impacted by Ripple20 powers the network communications of devices that use it. Because networking is at the core of device operations, Ripple20 vulnerabilities expose devices—and users who depend on them—to a range of potential attacks.
Perhaps one of the most serious is remote-code execution attacks, in which threat actors take control of an affected device in order to harvest private data from it or run malicious software on it. Making matters worse from a security standpoint, remote-code attacks can be executed from external networks, which means attackers need not have breached a company’s network perimeter or firewalls in order to exploit Ripple20 vulnerabilities.
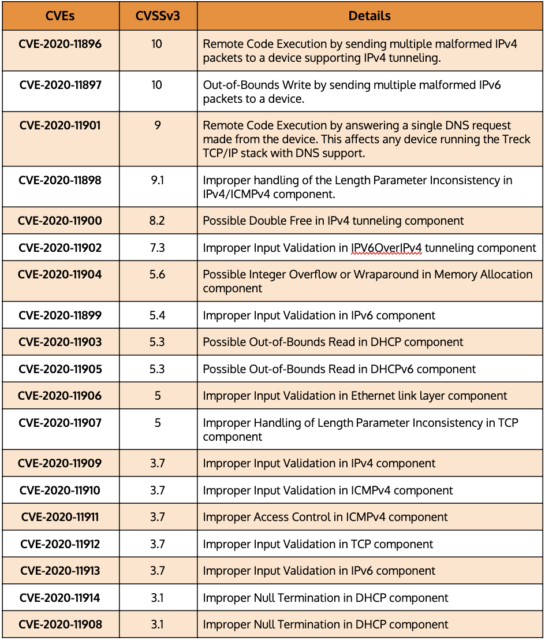
The following table displays a number of common vulnerabilities and exposures (CVE) that correspond to specific types of attacks and risks that have emerged from Ripple20.
CVEs that correspond to active Ripple20 attacks
In practice, Ripple20’s effects could include attacks such as the theft of personal data from Internet of Medical Things (IoMT) devices, or the interference with dosage levels distributed by such devices to patients. Or, if attackers use Ripple20 to take control of a manufacturer’s network, it could disrupt operations, leading to downtime and significant financial loss.
The list of potential attack scenarios could go on. The takeaway is that Ripple20 creates an unusually large and serious set of vulnerabilities that impact virtually every niche within the IoT ecosystem. JSOF has confirmed that Ripple20 affects IoT devices manufactured by fifteen specific vendors, including Baxter, Intel, Caterpillar, Cisco, Aruba, HP, and Xerox, but many others manufacturers’ products are likely to be at risk as well.
Identifying devices vulnerable to Ripple20
Because Ripple20 became publicly known only in 2020, many organizations are still in the process of assessing their exposure and risk. To do so, they must start by building an asset inventory within their infrastructure. Then, they must determine which devices are impacted by Ripple20.
There are two main ways to identify affected devices. One is to consult advisories from device manufacturers who have determined that their devices are impacted. But because not all manufacturers have issued advisories yet, equally important is proactive monitoring of devices in order to discover whether they are using the Treck TCP/IP stack and appear vulnerable to Ripple20. Ordr has developed novel techniques to discover devices that have Ripple20 vulnerabilities regardless of whether advisories from device manufacturers exist.
Once companies identify vulnerable devices, they can typically address the Ripple20 vulnerabilities by installing patches provided by device manufacturers. If a patch does not yet exist, the vulnerable devices can be taken offline until one becomes available or, at a minimum, segmented from other devices in order to mitigate the potential impact.
How to detect Ripple20
Because attackers can execute Ripple20 exploits from external networks, traditional firewalls and Network Access Controls (NACs), which filter traffic only along the boundary between the public Internet and a company’s internal network, provide little protection.
This is why novel Ripple20-detection techniques like those developed by Ordr are so important. In addition to looking for the presence of impacted Treck software on devices themselves, Ordr also baselines device behavior to determine malicious or suspicious patterns and will flag this activity. Ordr provides a level of protection against Ripple20 that a firewall and NAC solutions alone cannot deliver.
How to protect vulnerable devices from Ripple20
Although identifying devices that are impacted by Ripple20 and patching them is an obvious step for responding to the Ripple20 vulnerabilities, organizations must take broader steps to ensure that their networks are hardened against threats like Ripple20. That includes embracing the principles of Zero Trust security. It’s a safe bet that similar vulnerabilities exist in the wild but have not yet been discovered. Zero Trust helps ensure that your network will be resilient against such attacks, regardless of which form they take.
Zero Trust means that networks are configured in such a way that, whenever a new device appears on a network, or an existing device’s configuration changes, the device has no access to the network or the hosted resources until a security administrator has verified that the device should be granted access.
In addition, network administrators should adhere to several other best practices associated with Zero Trust:
- Do not rely on firewalls or private IP addresses to establish which devices are “safe.” Instead, identify each device that exists on a network and ensure that it can be trusted before you grant it access to network resources.
- Implement least-privilege access. Grant devices only the minimal access privileges they need to operate.
- Use Multi-Factor Authentication (MFA). MFA is a security enhancement that requires a user to present two or more pieces of evidence when logging in to an account.
- Implement microsegmentation. Grant access privileges to each device on a highly granular basis, rather than assigning broad access rights. Policies are tailored to the individual needs of each device on the network.
Proactive protection of IoT devices with Ordr
The Ripple20 vulnerabilities highlight just how much risk IoT and unmanaged devices face, even when they run software that has been used and trusted for decades. They demonstrate the need for proactive protection and deep visibility.
Ordr Systems Control Engine (SCE) is a solution for organizations that need to protect their network and devices from Ripple20 and other vulnerabilities. Ordr SCE can:
- Discover all network-connected devices.
- Identify vulnerable assets impacted by Ripple20.
- Detect and flag anomalous behavior using a built-in intrusion detection engine.
- Proactively protect devices from Ripple20 attacks by dynamically generating policies and enforcing them on next-generation firewalls or NAC solutions.
Interested in Learning More?
Subscribe today to stay informed and get regular updates from Ordr Cloud
Ready to Get Started?
-
 BlogEmbrace the Future of Cyber Asset Attack Surface Management
BlogEmbrace the Future of Cyber Asset Attack Surface Management…Successful CAASM Strategy In the ever-evolving landscape of cybersecurity, the need for an innovative and effective Cyber Asset Attack Surface Management (CAASM) strategy is more critical than ever. And as…
Blog
Embrace the Future of Cyber Asset Attack Surface Management
3Min Read
By Pandian Gnanaprakasam

Cyber asset attack surface management (aka CAASM) is a hot category of cybersecurity tool, but not all technologies that say “CAASM” are the same. Learn what true CAASM is, Ordr’s CAASM capabilities, and what sets us apart from the pretenders. CAASM+ DIfferentiators Series: Ordr’s Advanced Deduplication and Data Integrity Features are Vital to a Successful CAASM Strategy
In the ever-evolving landscape of cybersecurity, the need for an innovative and effective Cyber Asset Attack Surface Management (CAASM) strategy is more critical than ever. And as we navigate the complexities of integrating data from disparate sources to embrace the advantages of CAASM, it’s essential to ensure that cyber asset data is rich, timely, and accurate. That requires a data integrity program supported by complete asset visibility and real-time data ingestion, and I am excited to share with you how Ordr is leading the charge in enhancing data integrity through our advanced deduplication and data correlation methodologies.
Data integration within CAASM platforms is like assembling a jigsaw puzzle, where each piece comes from different puzzle sets. We have noticed that, without a coherent strategy, this results in a fragmented understanding of the cyber asset landscape akin to tunnel vision. Each tool in an organization’s arsenal only offers a glimpse into the assets within its scope. True asset visibility can only be accomplished by performing aggregation, normalization, mapping, and correlation to this data using GenAI organizational methods.
The Duplicates and Ephemeral Device Conundrum
One particularly challenging aspect of CAASM is managing duplicated data in situations such as IP rotation, MAC randomization, multiple adapters, etc. Ephemeral tech apparitions could be anything from virtual machines to IoT gadgets—ubiquitous yet elusive. These devices come through VPNs, get spun up as VDIs, etc., as they fit in and out of corporate networks. That makes acquiring and managing an accurate asset inventory a Herculean task using traditional approaches and tools.
That is because traditional asset discovery methods are like using a net with oversized holes: they simply cannot catch these quicksilver-like devices. For however long they are active in the network they have an effect on operations and risk calculus, opening a window to incidents and threats. And so, while invaluable for monitoring more persistent assets, agent-based and other asset management solutions often fail with ephemeral devices that avoid consistent network connections.
Ordr’s Unique Approach to Dynamic Asset Discovery
At Ordr, we’ve developed dynamic asset discovery mechanisms that embrace the transient nature of duplicate and ephemeral devices that is endemic to network operations today. Our approach involves leveraging real-time monitoring technologies and anomaly detection algorithms to spot these elusive assets based on their behavior.
Enhanced network visibility is also crucial. We provide additional insights into device activity by incorporating contextual real-time activity from network sources and endpoint telemetry. This contextual intelligence is pivotal in differentiating between legitimate devices and transient entities. Moreover, we utilize machine learning algorithms to sift through network-based real-time data ingestion, seeking out anomalous patterns that might signal an ephemeral device. These models, honed on historical data, enhance detection accuracy and minimize false positives.
Ordr’s AI/ML Deduplication
Addressing errors related to manual data entry and data duplication is another perpetual challenge in data management. Given the speed and volume of data creation and change, there is no practical reason to rely on manual data entry today, and yet it remains. At Ordr, we recognize that duplicated data is not just a nuisance—it can be a significant obstacle in business operations and security triaging.
What sets Ordr apart is our innovative use of AI and ML in deduplication. Our advanced machine learning techniques, along with predictive large language models, classify devices within an extensive asset knowledge base. We organize devices into an “Asset Catalog” with a sophisticated hierarchical structure, from buckets to categories, sub-categories, profiles, and device instances, along with business/owner context such as who is using the asset.
This organizational prowess and our learning engine’s precise identification capabilities significantly enhance our deduplication algorithm. We developed the vast Ordr Data Lake with rich profiles on millions of crowd-sourced individual assets, informed by data from manufacturers and other authoritative sources, which aids in the comprehensive understanding of device identities.
The Importance of Data Preprocessing
Our strategy hinges on establishing each device’s “true identity” through globally unique identifiers. This foundational understanding is essential for effective deduplication and provides the context to prevent erroneous duplicates.
Every integration at Ordr undergoes a rigorous mapping process to ensure incoming attributes are normalized, mapped and represented within our central database. This preprocessing is vital for maintaining data quality and consistency, forming our subsequent analysis’s bedrock. These innovative strategies that address the nuances of our digital ecosystem pave the path to robust CAASM. And we tirelessly refine our methodologies to ensure that our enterprise customers have a reliable, single source of truth for their asset management needs.
The Road Ahead
I hope this blog clarifies the importance of sophisticated data management within CAASM and how Ordr is at the forefront of tackling these challenges. Our mission is to empower organizations with the tools to manage their assets effectively, ensuring security and operational efficiency in an increasingly complex cyber landscape with an expanding attack surface.
As we look to the future, we remain committed to continuously improving our platform and ensuring that it remains at the forefront of the fight against cyber threats. Thank you for joining us on this journey as we redefine the standards of CAASM and pave the way for a more secure digital world.
Pandian Gnanaprakasam
Pandian has more than 20 years of product and engineering leadership experience and is also a serial entrepreneur. Before founding Ordr, he was the Chief Development Officer at Aruba, responsible for all of engineering and product management functions. Aruba, an enterprise mobile wireless company, was acquired by HPE for $3 Billion in March 2015. Before Aruba, Pandian served as the head of engineering for Cisco’s multi-billion-dollar Wi-Fi business unit and before that as VP of engineering for low-end switching product lines. He graduated with a master’s degree in Electrical Engineering from IIT, Chennai, India and holds several patents to his credit in various networking technologies.
Interested in Learning More?
Subscribe today to stay informed and get regular updates from Ordr Cloud
Ready to Get Started?
-
 BlogARPA-H UPGRADE: A Response
BlogARPA-H UPGRADE: A Response…made available to those hospitals serving mid-market, rural, and disadvantaged communities in the form of grants, loans, and incentive programs specifically for the purpose of funding investments in the people,…
Blog
ARPA-H UPGRADE: A Response
3Min Read
By Wes Wright
Advanced Research Projects Agency for Health (ARPA-H) is a U.S. federal agency operating independently under the aegis of the National Institutes for Health whose mission is to “accelerate better health outcomes for everyone by supporting the development of high-impact solutions to society’s most challenging health problems.” On May 20, ARPA-H announced a new initiative called Universal PatchinG and Remediation for Autonomous DEfense (UPGRADE) aimed at developing technologies for improving cybersecurity for healthcare organizations.
A Worthwhile Goal
UPGRADE comes with $50 million in new funding to support collaborative research and development ARPA-H says is needed to create “an autonomous cyber-threat solution that enables proactive, scalable, and synchronized security updates. Importantly, this software platform will enable simulated evaluations of potential vulnerabilities’ impact and adapt to any hospital environment across a wide array of common devices. The program aims to reduce the uncertainty and manual effort necessary to secure hospitals, guaranteeing that vulnerable equipment is fixed and allowing staff to focus on patient care.”
That is a worthwhile goal.
Clearly there is a critical need to stem the tide of cyberattacks on the healthcare industry, and while I am glad to see that the federal government has taken notice, I can’t help but wonder if leadership at ARPA-H have taken a look at the cybersecurity market to see what innovative solutions exist that already do what it hopes to accomplish. If so, they might have noticed that there are already billions of dollars in private investment capital pouring into the market to address this very issue, and many “high-impact solutions” are already available to help address the cyberthreats that hamper the industry’s ability to focus on patient care.
In fact, a part of the hypothetical software platform ARPA-H describes sounds a lot like the platform Ordr’s customers have been using for years. The Ordr platform reduces their cyber risk, prevents and mitigates the effects of cyberattacks, automates responses in the face of threats, maximizes operational resilience for hospitals, and allows them to maintain effective operations without the need to resort to radical “code dark” exercises.
Ideals vs. the Realities
From my perspective as a former healthcare CTO/CIO, and confirmed by the numerous conversations I’ve had (and continue to have) with my peers in the industry, the challenge isn’t primarily one of a lack of tools capable of addressing the threats the industry faces; it is in having the resources (time, money, and people) necessary to invest in and implement those tools. And this problem is most acute in the mid-market, rural, and disadvantaged communities where finances are focused on keeping the lights on. Cybersecurity may be near the top of priorities, but even placing second on that list means making do with a meager budget and keeping your fingers crossed.
Perhaps when ARPA-H assembles its body of experts it will conclude that there’s no real value in initiating a process that our great community of cybersecurity vendors is already driving toward, and focus their efforts (and $50M) on an area where improvement is possible and solutions are lacking. I choose to be optimistic in this regard because it is encouraging to see the problem acknowledged, and federal dollars allocated to try and do something about it.
New Innovation, Not Recreations
Rather than try to recreate existing technology, ARPA-H might want to look at what Health and Human Services is doing with their Healthcare Sector Cybersecurity strategy and think about how to complement that initiative. There is an opportunity to apply new innovations in pursuit of HHS’ four Healthcare Sector Cybersecurity goals, namely:
- Establish voluntary cybersecurity performance goals for the healthcare sector
- Provide resources to incentivize and implement these cybersecurity practices
- Implement an HHS-wide strategy to support greater enforcement and accountability
- Expand and mature the one-stop shop within HHS for healthcare sector cybersecurity
And by working with industry experts to estimate budget, then enlisting Congress to allocate significant financial resources, funding (far more than $50 million) can be made available to those hospitals serving mid-market, rural, and disadvantaged communities in the form of grants, loans, and incentive programs specifically for the purpose of funding investments in the people, processes, and technologies needed to defend against cyberthreats. Such a program should be easy to access and apply for (heaven knows they don’t need more burdensome paperwork thrust upon them), while structured to ensure that the monies provided are spent in direct support of effective cybersecurity investments and programs.
No More Unfunded Mandates
It is frustrating for those responsible for securing the most at-risk hospitals to read about more mandates and best practices proclaimed from afar when they are fighting for every dollar they can get to simply keep their IT running. No one in healthcare IT and security is ignorant of the threats they face, and they all want to do the best they can for their organization and the patients they serve. There are good security tools available to them; what they need is the means to access them and put them to use.
For more information about Ordr and how we protect healthcare organizations, contact us to see our platform in action.
Wes Wright
Chief Healthcare Officer
Wes is responsible for driving Ordr’s engagements in healthcare. Previously he was the CTO for Imprivata, and prior to that VP and CTO at Sutter Health, a 26 hospital network in Northern California. Prior to Sutter, Wes was CTO and then CIO at Seattle Childrens’, which, to this day, he says was his most gratifying work experience.
Interested in Learning More?
Subscribe today to stay informed and get regular updates from Ordr Cloud
Ready to Get Started?
-
 NewsKLAS Research Names Ordr a Top Performer for Healthcare IoT Security
NewsKLAS Research Names Ordr a Top Performer for Healthcare IoT Security…more secure. The information in the product is outstanding, but the opportunity to translate that information into actionable security policies is the big selling point of the product for us.”…
KLAS Research Names Ordr a Top Performer for Healthcare IoT Security
3Min ReadSanta Clara, CA – February 15, 2023 – Ordr, the leader in connected device security, today announced that it has been named a top performer by KLAS Research in the firm’s 2023 Best in KLAS Software & Services Report for Healthcare IoT Security. Ordr has been recognized as a Top Performer in this report for three years in a row.
The Best in KLAS report recognizes software and services companies that excel in helping healthcare professionals improve patient care. All rankings are based on feedback from thousands of providers, compiled over the past year, who use the products reviewed.
“Healthcare technology management and security teams benefit from Ordr’s ‘whole hospital’ approach to visibility and security. As shared by our customers, we continue to deliver unique product innovations – from granular device context, full-lifecycle vulnerability management, and utilization insights to meaningful integrations – to help healthcare systems enhance patient safety, optimize usage and improve efficiencies. Our market-leading security and segmentation capabilities help security teams anticipate, withstand, and respond to cyberattacks such as ransomware, ensuring operational resilience,” said Jim Hyman, CEO at Ordr. “We’re thrilled to be recognized by our customers. It is a strong endorsement of our team’s continued dedication to delivering the best healthcare IoT security product on the market.”
When asked about Ordr, customers shared the following comments:
- “Ordr is one of our favorite vendors, and they enable a practical approach to zero trust security. They do a wonderful job of helping us secure our medical devices, and they are a pleasure to work with. They are putting a lot of new features into their product, and they are going beyond what we originally purchased them for to the extent that we might actually be able to get rid of one of our other network monitoring products.” CIO (November 2022)
- “Ordr comes out with new technology that blows me away all the time. They just keep adding functionality. Ordr’s product is the only product I can ever remember. When I am talking to peers or companies that [I] do work with, I tell them they need to check out Ordr’s platform.” Director (October 2022)
- “The biggest thing I like is that we can use the information gathered by the system to implement tangible policies for other things, such as my firewall. That is the true value of being able to look at devices and see what they are. The product allows me to write access control list policies around entire groups of devices, and that makes us more secure. The information in the product is outstanding, but the opportunity to translate that information into actionable security policies is the big selling point of the product for us.” Director (October 2022)
- “Ordr is truly exceptional. I have regular calls with their team, and one of the talking points on every agenda is the vendor’s road map. I do lots of check-in calls with vendors on a variety of products, and Ordr is the vendor that is the clearest with their road map.” Director (October 2022)
- “Ordr has an incredible ability to integrate their solution with my firewall and endpoint protection software. The integration between Ordr’s platform and my other security platforms is really high, whether Ordr’s product is integrating with an IoT device or simply a Windows workstation sitting on someone’s desk. The level of integration that the product has is ridiculous.” Director (October 2022)
- “The product has really helped me discriminate between the devices on my network; I can tell whether something is a PC as opposed to an infusion pump or a pulse oximeter. That is very helpful for specific healthcare IoT purposes. The system has changed our workflow.” Director (October 2022)
- “Our implementation with Ordr was incredibly smooth. Ordr killed it. I don’t have enough good things to say about Ordr. I don’t know whether I have ever been as satisfied with another implementation as I was with Ordr’s implementation.” Director (October 2022)
The Ordr “whole hospital approach” secures all connected devices – IoT, IoMT, operational technology (OT), and traditional IT systems – that are critical to operations and patient care. With Ordr, HTM and security teams gain the insight and tools they need to identify risks such as devices with outdated operating systems, devices with vulnerabilities, and take action by applying segmentation to devices that can not be updated or otherwise secured.
Ordr recently published a Connected Device Security Healthcare Maturity Model to guide healthcare organizations on their journey to Zero Trust. For more information, see how Ordr can help your organization gain visibility and control over its connected medical devices and equipment.
Interested in Learning More?
Subscribe today to stay informed and get regular updates from Ordr Cloud
Ready to Get Started?
-
 BlogWhat Are Cyber-Physical Systems?
BlogWhat Are Cyber-Physical Systems?…Brief History That scenario is playing out in the realm of the Internet of Things (IoT) and its permutations like the Internet of Medical Things (IoMT), Industrial Internet of Things…
Security Strategy
What Are Cyber-Physical Systems?
3Min Read
By Chris Westphal
What are cyber-physical systems? Cyber-physical systems (CPS) represent an interplay of digital and analog infrastructure. CPS can’t be protected by traditional means and so CISOs require new tools and a new approach to device-centric security. Paradigmatic shifts are often not fully recognized until after they have occurred. Innovations are made, evolutions take place, and then someone realizes, “Hey, this is much different from when it started.” That’s when people start to re-think context and terminologies reflective of the new reality.
Cyber-Physical Systems: A Brief History
That scenario is playing out in the realm of the Internet of Things (IoT) and its permutations like the Internet of Medical Things (IoMT), Industrial Internet of Things (IIoT), Internet of X Things (IoXT) that covers consumer, military, automotive, and other applications of connected technologies, and operational technology (OT). It’s a trend that began back in the 1980s when system-on-chip technology started getting designed into office printers, then adapted to use for industrial equipment, allowing users to manage and monitor machines and office appliances via the organization’s local area network (LAN). When the LAN gave way to public networks, the term “Internet of Things” was coined by MIT’s Kevin Ashton during a proposal to Procter & Gamble in which he suggested using RFID tags to track products moving through the supply chain.
Fast-forward to 2006 when, according to the National Institutes of Health’s National Library of Medicine, the term cyber-physical systems was introduced to describe the interplay of digital and analog infrastructure in which “embedded computers monitor and control physical processes, usually with feedback loops, where physical processes affect computations and vice versa.”
Gartner has since adopted the term cyber-physical systems (CPS) to describe the full scope of connected technologies that once seemed arcane but are now not only common, but integral to the digital operations and infrastructure of nearly every enterprise. CPS are therefore the next-generation of integrated physical and cyber systems, and can include IoT, OT, and IoMT assets such as critical infrastructure sensors, surveillance cameras, building management systems, and healthcare devices with embedded systems that interact with the real world as well as with complex software elements. And because of the essential role CPS now plays, the devices comprising CPS assets have introduced new, critical risks to the organizations that have adopted them as a part of their digital transformations.
Managing Risks With Cyber-Physical Systems
That means new challenges for the IT security teams responsible for keeping networks, data, and people safe. In a recent report, Innovation Insight for Cyber-Physical Systems Protection Platforms, Gartner wrote:
“As organizations connect operational or mission-critical systems, or deploy automation and digital transformation technology, they create cyber-physical systems that security and risk management leaders must securely manage. Enter CPS protection platforms — new solutions for a new security reality.”
A cyber-physical systems protection platform is a security solution that automates cyber-physical systems asset discovery, and adds a range of security-related features to improve the risk posture of CPS. Gartner believes that by 2025, “70% of companies will deploy cyber-physical systems protection platforms as the first step in their asset-centric security journey.” As described in the Gartner graphic below, when organizations embrace digital transformation and IT/OT convergence, they will need to move towards an asset-centric view of security.
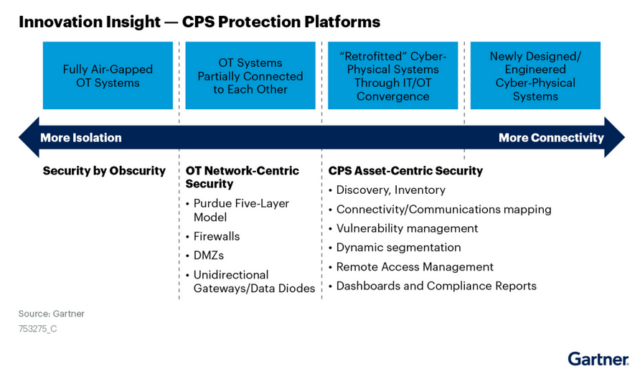
The Gartner report outlines findings, challenges, and recommendations for organizations confronting their CPS security realities for the first time, describes the risks that unprepared and ill-equipped enterprises face, and requirements for CyberPhysical Protection platforms.
Ordr Addresses Visibility and Security of Cyber-Physical Systems
Fortunately, Ordr offers a CPS protection platform that addresses these risks and makes it easy for organizations to see, know, and secure the devices that have been accruing to their enterprise inventories over the years (as well as those ones they didn’t know were connecting and operating on their infrastructure) — including IT, IoT, and OT. In fact, Ordr is named by Gartner as one of the leading CPS protection platform innovators, focused on addressing the unique, asset-centric approach required to protect connected devices and their infrastructures.
Ordr was engineered for the CPS environment, and delivers many security benefits specific to protecting cyber-physical systems, including:
- Automated asset discovery and classification to gain an accurate view of your CPS attack surface.
- Identification of vulnerable devices, malicious communications, and active threats to uncover previously unknown risks.
- Prioritized remediation and mitigation efforts with risk scores calculated for every asset.
- Accelerated incident response with dynamically created policy to stop malicious communications and protect devices.
- Improved security with automated policy for NAC and Zero Trust segmentation.
Learn more about the Ordr platform and how we can help you protect your CPS assets, get in touch with us directly.
Chris Westphal
Head of Product Marketing
Chris is the Head of Product Marketing at Ordr where he helps drive awareness for connected device security and the value of the Ordr solution. Chris brings more than two decades of experience to his role with a background in enterprise security, cloud, and data center technologies. Most recently, Chris was head of product marketing at Salt Security, the leader in API protection, and has held product marketing leadership roles at companies including VMware, Illumio, and Adallom (acquired by Microsoft).
Interested in Learning More?
Subscribe today to stay informed and get regular updates from Ordr Cloud
Ready to Get Started?
-
 BlogAligning Healthcare Cybersecurity for Connected Medical Devices
BlogAligning Healthcare Cybersecurity for Connected Medical Devices…Decker, the CISO of Intermountain Healthcare, former Board Chair of the Association for Executives in Healthcare Information Security (AEHIS), and co-leader of the HHS task group implementing the Cybersecurity Act…
Security Bulletin
Aligning Healthcare Cybersecurity for Connected Medical Devices
New Federal Cybersecurity Law – Public Law 116-321
3Min ReadBy Ty Greenhalgh
A guest blog from Cyber Tygr’s Ty Greenhalgh addresses how to align strategies for operating and securing connected medical devices, IoMT, and other healthcare technologies with a new healthcare cybersecurity law that attempts to address exploitable weaknesses in healthcare IT. The second episode of the seven-part CHIME Medical Device Security webinar series aired last week. The episode addressed the topic of aligning healthcare cybersecurity for connected medical devices with a new cybersecurity law for healthcare. Once again, I moderated the episode under my new role as, Senior Account Executive with Nuvolo. I was joined by two industry experts who weighed in on the subject. Erik Decker, the CISO of Intermountain Healthcare, former Board Chair of the Association for Executives in Healthcare Information Security (AEHIS), and co-leader of the HHS task group implementing the Cybersecurity Act of 2015. Returning from Episode One was Rob Suárez, CISO of Becton Dickinson (BD) and chairman of the Medical Device Innovation Consortium’s (MDIC) Cybersecurity Steering Committee and the Advanced Medical Technology Association’s (AdvaMed) Cybersecurity Work Group.
The Cybersecurity Act of 2015, in particular its 405(d) provision, expressly calls out the healthcare industry. While the name “405(d)” offers little insight as to the legislation’s relevance to medical device security, Mr. Decker is uniquely positioned, perhaps more so than anyone else, to elaborate on its significance. As he explained, healthcare is officially designated as critical infrastructure and simply requires more protection. Cyber-attacks to hospital operations are direct threats to patient safety, and compromises to highly sensitive electronic health information threatens patient privacy rights. Ransomware attempts against healthcare are increasing, rising 123% in 2020, incurring $20.8 billion in downtime costs. 405(d) mandates the formation of an industry-led task group to publish a compendium of cybersecurity best practices, frameworks, methodologies, technologies, and other recommendations to serve as a set of Federally recognized cybersecurity practices that afford legal safe harbor to Health Delivery Organizations (HDOs) when implemented. In the words of Mr. Decker, “It’s a way to draw a line in the sand and say, ‘here is an example of what you can do that demonstrates best practice’; and if you do it, you get a benefit for it; and if you don’t, you might be hindered by it.” The cornerstone publication of the 405(d)-task group is Health Industry Cybersecurity Practices (HICP, pronounced liked ‘hiccup’). Comprised of three primary volumes, HICP has a main document providing a high-level summary of the threats and recommendations, and two technical volumes prescribing specific practices, including connected medical devices, to be implemented by IT specialists of small, medium, and large HDOs. Under the new law, Public Law 116-321, following the best practices for medical device security detailed in HICP will require the Office of Civil Rights within the HHS (OCR) to consider reductions in fines, audits and post breach oversight.
Next, Mr. Suárez discussed the Medical Device and Health IT Joint Security Plan (JSP), authored by a Healthcare and Public Health Sector Coordinating Council (HSCC) task group in 2019, which Mr. Suárez co-chaired. The JSP document proposes a voluntary framework in which responsibility for medical device security is disseminated across healthcare stakeholder organizations. Under the JSP, MDMs proactively aid their customers by developing and communicating processes, personnel training recommendations, device life-cycle strategy, vulnerability patches, decommissioning plans, and incorporating HDO feedback into future product design. HDOs work with their vendors to establish baseline best practices and measures of device maturity and process effectiveness, communicate complaints and discovered vulnerabilities, and institute remediation procedures.
Episode Three of CHIME’s Medical Device Security webinar series airs on Thursday, August 5th. If you missed Episodes One, you can view my recap here, or register for the entire series at https://store.ignitedigital.org/product?catalog=medical_device_security_webinar_series.
Acronym Glossary
- 405d: A provision within the Cybersecurity Act of 2015 (CSA). The CSA 405(d) document aims to raise awareness, provide vetted practices, and foster consistency in mitigating the most pertinent and current cybersecurity threats to the sector. It seeks to aid the Healthcare and Public Health (HPH) sector organizations to develop meaningful cybersecurity objectives and outcomes.
- AdvaMed: Advanced Medical Technology Association
- AEHIS: Association for Executives in Healthcare Information Security
- BD: Becton Dickinson
- CHIME: College of Healthcare Information Management Executives
- HDOs: Health Delivery Organizations
- HHS: Health and Human Services
- HICP: Health Industry Cybersecurity Practices
- HSCC: Healthcare and Public Health Sector Coordinating Council
- JSP:Medical Device and Health IT Joint Security Plan
- MDIC: Medical Device Innovation Consotium
- MDM: Medical Device Manufacturers
- OCR: Office of Civil Rights within the HHS
- Public Law 116-321: An act to amend the Health Information Technology for Economic and Clinical Health Act to require the Secretary of Health and Human Services to consider certain recognize security practices of covered entities and business associates when making certain determinations, and for other purposes
Ty Greenhalgh
For the last 4 years, Ty has been the CEO of Cyber Tygr, a company dedicated to improving and protecting the privacy, cybersecurity and compliance of our nation’s Health Industry by operationalizing advanced technologies. As a result of his intensive efforts in supporting the cybersecurity posture of healthcare medical devices and facility equipment, Nuvolo has brought him on board to spearhead their new Cyber OT module. Mr. Greenhalgh is an active member in several groups and associations, such as Healthcare and Public Health Sector Coordinating Council’s Joint Cybersecurity Workgroup, the Department of Health and Human Services 405(d) Workgroup and the Department of Commerce National Information and Telecommunications Agency.
Interested in Learning More?
Subscribe today to stay informed and get regular updates from Ordr Cloud
Ready to Get Started?
-
 BlogDetect & Defend Against Chrome Vulnerabilities Using OrdrAI
BlogDetect & Defend Against Chrome Vulnerabilities Using OrdrAI…simple search, you can then add this as a widget and dig deeper into these devices for remediation, identifying the blast radius in case these vulnerabilities are exploited. You can…
Blog
Detect & Defend Against Chrome Vulnerabilities Using OrdrAI
Ordr Security Bulletin
< 1Min Read
By Pandian Gnanaprakasam
This security bulletin written with support from Ordr senior product manager Derek Loomis
Google Chrome has experienced eight zero-day exploits so far in 2024 and four in May alone! To mitigate these threats users are strongly advised to update their Chrome browser to version 125.0.6422.112/.113 for Windows and macOS, and version 125.0.6422.112 for Linux.
Similarly, users of Chromium-based browsers such as Microsoft Edge, Brave, Opera, and Vivaldi are urged to apply the available fixes promptly. Additionally, CISA has acknowledged active exploitation of CVE-2024-5274 and requested that users patch the flaw before June 18, 2024. It’s crucial for administrators to enable application vulnerability policies and consider setting the severity to high, blocking user access to work data until the app is updated.
Attackers may exploit these vulnerabilities by delivering a maliciously crafted webpage through SMS, email, or messaging platforms, convincing victims to tap the link and initiate the exploit. A successful attack could grant attackers access to sensitive data or deliver phishing sites or malware to the vulnerable device, posing a critical risk to enterprise security postures that rely heavily on mobile devices accessing sensitive cloud data.
OrdrAI CAASM+ (Cyber Asset Attack Surface Management) accelerates the remediation of these threats by providing software version information so you don’t have to wait for vulnerability scans to complete. The most recent zero-day exploits are so serious, the U.S. government has warned federal employees to apply emergency updates or stop using Chrome altogether. Deadlines for updates exist for both June 3rd and June 6th. As with all zero-day vulnerabilities, time-to-remediation is crucial, and OrdrAI enables you to act quickly to secure your assets.
Vulnerability Details:
CVE-ID Severity Details Exploitability Score Vector NVD Published Date CVE-2024-5274 8.8 Type Confusion in V8 in Google Chrome prior to 125.0.6422.112 allowed a remote attacker to execute arbitrary code inside a sandbox via a crafted HTML page. 2.8 CVSS:3.1/AV:N/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:H 05/28/2024 CVE-2024-4671 9.6 Use after free in Visuals in Google Chrome prior to 124.0.6367.201 allowed a remote attacker who had compromised the renderer process to potentially perform a sandbox escape via a crafted HTML page. 2.8 CVSS:3.1/AV:N/AC:L/PR:N/UI:R/S:C/C:H/I:H/A:H 05/14/2024 CVE-2024-4761 8.8 Out of bounds write in V8 in Google Chrome prior to 124.0.6367.207 allowed a remote attacker to perform an out of bounds memory write via a crafted HTML page 2.8 CVSS:3.1/AV:N/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:H 05/14/2024 CVE-2024-4947 8.8 Type Confusion in V8 in Google Chrome prior to 125.0.6422.60 allowed a remote attacker to execute arbitrary code inside a sandbox via a crafted HTML page. 2.8 CVSS:3.1/AV:N/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:H 05/15/2024 CVE-2024-2886 Awaiting Analysis Use after free in WebCodecs in Google Chrome prior to 123.0.6312.86 allowed a remote attacker to perform arbitrary read/write via a crafted HTML page. Awaiting Analysis Awaiting Analysis 03/26/2024 CVE-2024-2887 Awaiting Analysis Type Confusion in WebAssembly in Google Chrome prior to 123.0.6312.86 allowed a remote attacker to execute arbitrary code via a crafted HTML page. Awaiting Analysis Awaiting Analysis 03/26/2024 CVE-2024-3159 8.8 Out of bounds memory access in V8 in Google Chrome prior to 123.0.6312.105 allowed a remote attacker to perform arbitrary read/write via a crafted HTML page 2.8 CVSS:3.1/AV:N/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:H 04/06/2024 CVE-2024-0519 8.8 Out of bounds memory access in V8 in Google Chrome prior to 120.0.6099.224 allowed a remote attacker to potentially exploit heap corruption via a crafted HTML page. 2.8 CVSS:3.1/AV:N/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:H 01/16/2024 Source: CVE Details
Google Chrome May Vulnerabilities- CVE-2024-5274 (type confusion in V8 JavaScript and WebAssembly engine)
- CVE-2024-4671 (use-after-free in Visuals)
- CVE-2024-4761 (out-of-bounds write in V8)
- CVE-2024-4947 (type confusion in V8)
Other Google Chrome 2024 Zero-Days
- CVE-2024-2886 (UAF issue in WebCodecs)
- Demonstrated at March hacking contest Pwn2Own Vancouver 2024
- CVE-2024-2887 (type-confusion issue in WebAssembly)
- Demonstrated at March hacking contest Pwn2Own Vancouver 2024
- CVE-2024-3159 (out-of-bounds memory access in V8)
- Demonstrated at March hacking contest Pwn2Own Vancouver 2024
- CVE-2024-0519 (out-of-bounds memory access in Chrome JavaScript engine)
How OrdrAI Helps
OrdrAI CAASM+ integrates with your existing infrastructure utilizing API calls to gather software information from numerous vendors. Further, Ordr’s lightweight, patented script and primary data source, Software Inventory Collector, delivers a high-fidelity software inventory. Then, OrdrAI CAASM+ provides out-of-the-box dashboards to continuously monitor your environment. Correlating all these data sources Ordr provides comprehensive and accurate deduplicated asset visibility, thus preventing exposures.
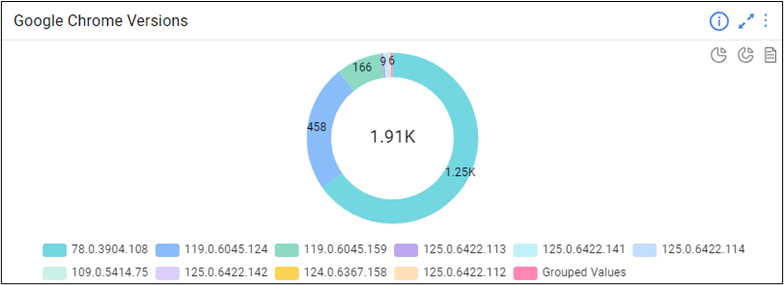
History shows Google Chrome’s recent streak of zero days will repeat itself. Web Browers, Adobe, and Java products have historically been at the top of the list of most vulnerable third-party software. But with OrdrAI CAASM+ you can track all browser versions in your environment.
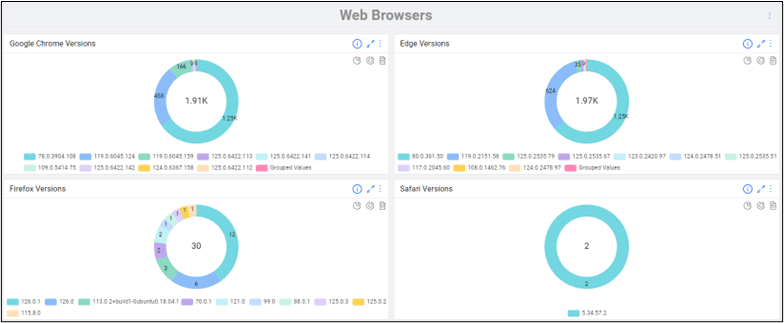
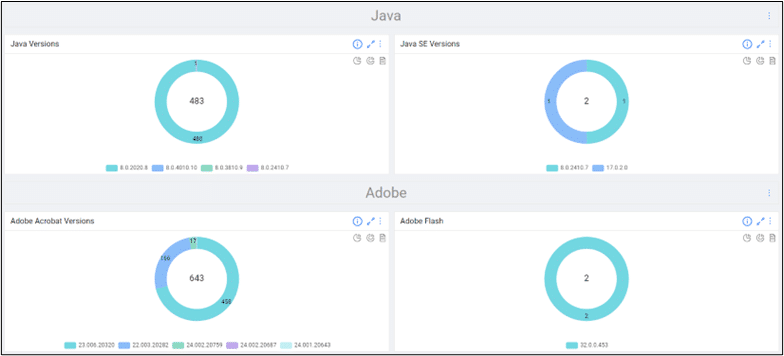
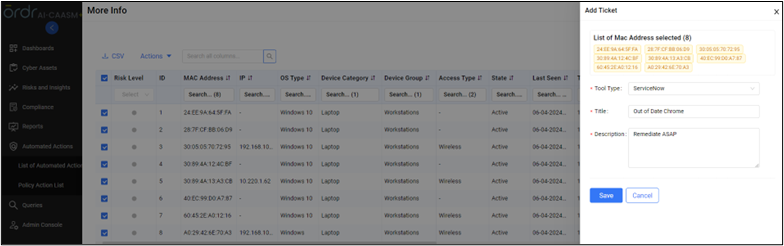
Ordr’s out-of-the-box comprehensive software inventory allows your remediation teams to define scope and begin remediation in just a few clicks, and Identify and track devices with out-of-date browser versions in your environment. With a simple search, you can then add this as a widget and dig deeper into these devices for remediation, identifying the blast radius in case these vulnerabilities are exploited.
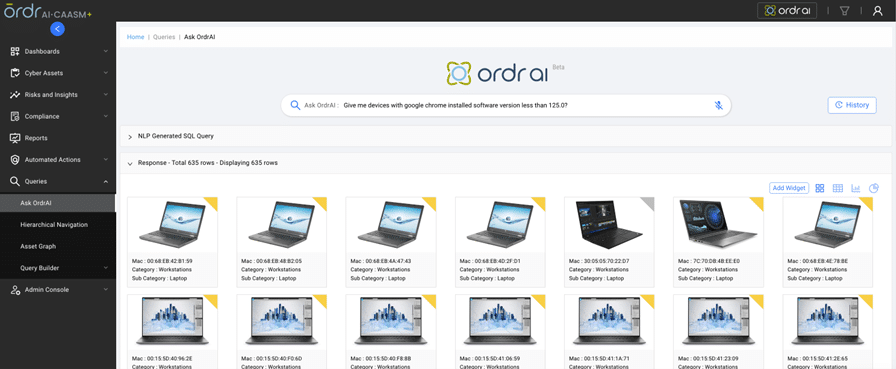
You can also track updates or installation of new browsers based on version number correlated with Install date/Update time.
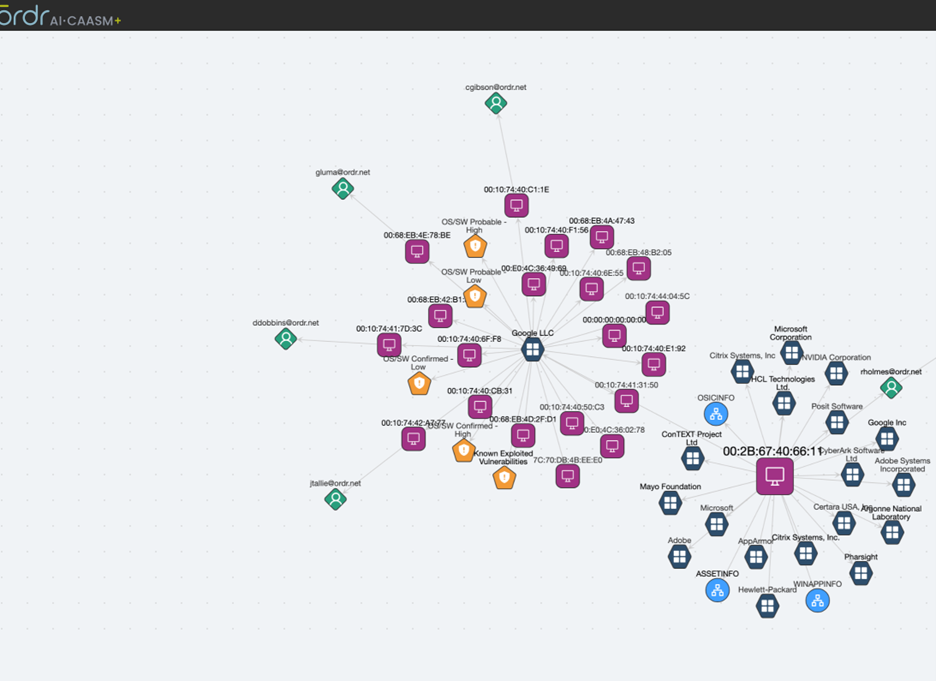
Customers can also get a detailed view of the blast radius via the “Asset Graph” feature, identifying devices, users, and applications associated with a vulnerable asset.
OrdrAI lets you assign a variety of actions to appropriate remediation teams to patch out of date devices.
Actions Supported by OrdrAI CAASM+
OrdrAI CAASM+ allows easy management of vulnerabilities, including assignments and status of the vulnerabilities thanks to deep integration with vulnerability management tools like ServiceNow VR module, providing real-time status updates based on reconciled data.
Furthermore, OrdrAI CAASM+ delivers vital capabilities, like muting or removing a vulnerability from the system when information is not available or is hidden from publicly available dashboards. This is usually done when admins are not ready to patch and are waiting for validation from the manufacturer. OrdrAI also lets you assign vulnerabilities to individual users along with priority and due date. All this information can be shared with CMDB or any other asset management vendors.
Finally, OrdrAI CAASM+ reduces time-to-remediation and risk to the organization with the help of Integration with messaging/collaboration tools and ticketing systems and providing a range of asset specific actions.
OrdrAI CAASM+ is your single source of truth, enabling your teams act with confidence. Contact us for more information.
Pandian Gnanaprakasam
Pandian has more than 20 years of product and engineering leadership experience and is also a serial entrepreneur. Before founding Ordr, he was the Chief Development Officer at Aruba, responsible for all of engineering and product management functions. Aruba, an enterprise mobile wireless company, was acquired by HPE for $3 Billion in March 2015. Before Aruba, Pandian served as the head of engineering for Cisco’s multi-billion-dollar Wi-Fi business unit and before that as VP of engineering for low-end switching product lines. He graduated with a master’s degree in Electrical Engineering from IIT, Chennai, India and holds several patents to his credit in various networking technologies.
Interested in Learning More?
Subscribe today to stay informed and get regular updates from Ordr Cloud
Ready to Get Started?








