Search Results:
”Quiz 2024 SAP C-ARSOR-2308: Marvelous SAP Certified Application Associate - SAP Ariba Sourcing Valid Dumps Book 🐮 Open ▷ www.pdfvce.com ◁ and search for ➥ C-ARSOR-2308 🡄 to download exam materials for free 🏑C-ARSOR-2308 Customizable Exam Mode”
-
 BlogWhy Healthcare Organizations Struggle with Vulnerability Management
BlogWhy Healthcare Organizations Struggle with Vulnerability Management…Ordr has comprehensive and accurate classification methods to understand a medical device’s make, model deeply, and modality (how it is configured and deployed in a specific hospital) and then accurately…
Risk Management
Why Healthcare Organizations Struggle with Vulnerability Management
13Min Read
By Pandian Gnanaprakasam

The healthcare industry is under continuous attack from cybercriminals. That is why Ordr invests in developing innovative technologies like Clinical Defender 8.1, a full-lifecycle vulnerability management platform to protect healthcare organizations from cyberthreats. Ordr protects three of the top five healthcare organizations in the U.S., and thousands of hospital sites all over the world with our connected device security platform, powered by our device knowledge base of millions of devices. We are a healthcare-first company and continue to innovate to help our customers address their connected medical device security challenges. Today, we’re excited to launch Ordr Clinical Defender 8.1, with a Full-Lifecycle Vulnerability Management Platform. This release is based on feedback from our healthcare customers, and is specifically optimized to enable HTM teams to see, prioritize and address all connected medical vulnerabilities and clinical risks.
Why is this a priority?
Quite simply, when you secure your devices, you secure patient care. The more efficient HTM teams are at managing and addressing vulnerabilities for healthcare devices, the better the organization is at delivering safe, connected care. But vulnerability management in healthcare is challenging. The exploding growth of connected devices, coupled with increasing vulnerabilities, a rise in cyberattacks and limited resources introduce various complexities.
In this blog, I discuss why this is a monumental challenge for many organizations, how Ordr is solving it, and the best practices you should consider. Here are the key topics, for those who want to skip to the sections important to them.
1. Vulnerability Management in Healthcare Is Complex
At the healthcare organizations Ordr work with, we see medical devices with a wide variety of make, model, and modalities from multiple manufacturers. Hospitals have at least about 2000 unique medical device types with 20 possible operating system variations. Each of the OS embedded has numerous variations with different levels of patching. It is not uncommon to see the total number of vulnerabilities as a multiplication of the number of device types and the associated vulnerabilities for each to amount to tens of thousands. This is a huge challenge unless a robust program (combined with technology) tackles it efficiently with the right prioritization methodology.
Moreover, growing ransomware attacks and the recently introduced cybersecurity bill indicate an urgency for quickly and efficiently tackling device vulnerabilities. However, this can be daunting for Healthcare Technology Management (HTM) professionals tasked with managing and maintaining the vast assortment of hospital tools and devices.
2. Medical Device Full-Lifecycle Vulnerability Management
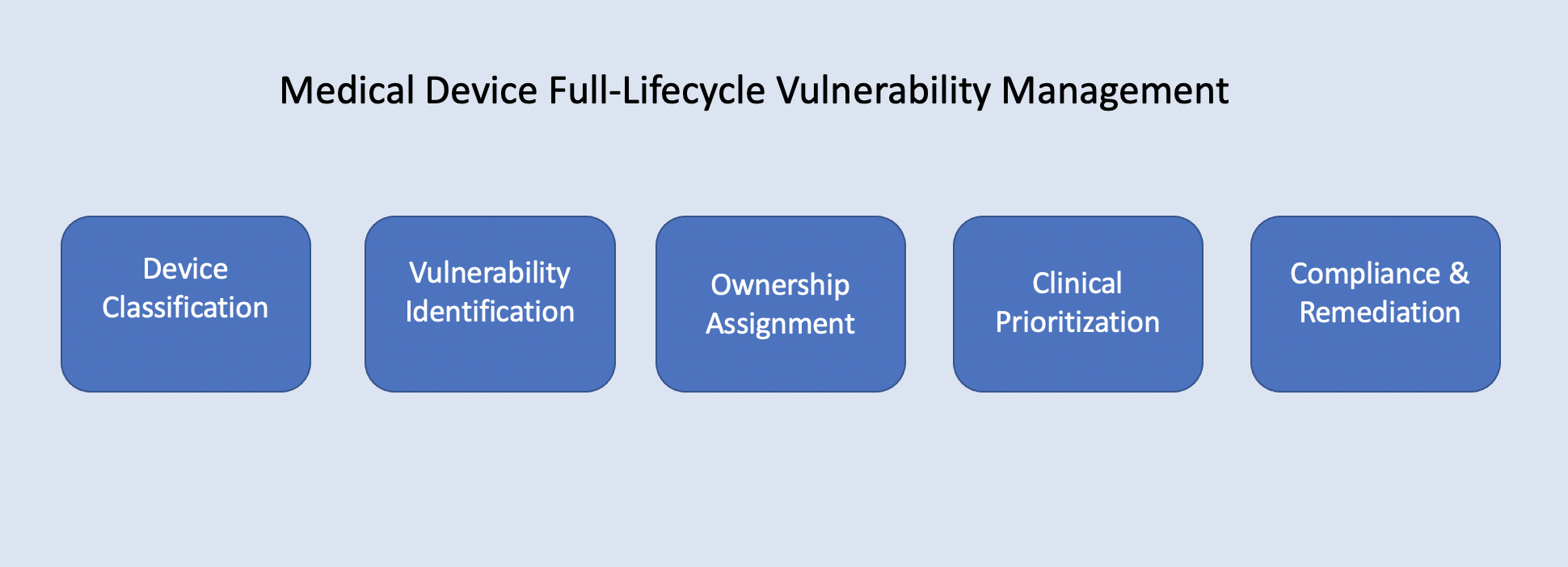
2.1 Device Classification
It is critical that every device connected to a hospital environment is accurately accounted for and monitored 24×7. Ordr’s passive technology using packet captures and deep packet inspection provides the most comprehensive and granular inventory of devices in a healthcare environment. No other platform can confidently track and monitor 100% of every single connected device in a hospital. Other tools like Vulnerability Scanners only know about the devices they scan, and endpoint agents only know about the devices they are installed on. Ordr moves this process from a one-time activity that happens periodically to continuous monitoring of devices connecting to the network and continuous tracking of new vulnerabilities published daily.
Ordr has comprehensive and accurate classification methods to understand a medical device’s make, model deeply, and modality (how it is configured and deployed in a specific hospital) and then accurately understand the underlying OS down to its patch levels. Once a device’s OS and patch level are determined, Ordr’s vulnerability matching engine compares that to publicly available vulnerability databases, FDA notices, manufacturer’s declarations, etc., to get a complete list of all vulnerabilities. This is one of the most challenging aspect of vulnerability management that Ordr simplifies for HTM users.
2.2 Vulnerability Identification for the Whole Hospital
Vulnerability management starts with visibility. It is critical to be able to gain granular visibility and complete asset inventory for every device in the hospital.
- Medical devices – The complexity of vulnerability management with most hospital equipment is trifold.
- Medical equipment very often cannot be scanned like IT endpoints that run standard operating systems. An utterly passive mechanism is needed to understand their vulnerabilities based on how they operate. Since these medical devices provide patient care 24×7, any scanning attempt that intensely interrogates the devices with various deep and continuous scans can cause severe disruption in the device’s performance and more often brings down the device in the middle of providing patient care.
- Patch Tuesday isn’t an option. Hospital IT teams cannot simply download a patch from OS providers like Microsoft. Every change in the underlying OS needs some level of retesting of the medical device for recalibration of the performance and could also trigger an FDA validation for critical compliance. Usually, manufacturers provide patches; in practice, that patch is hard to come by quickly when a vulnerability is detected. Patching is an activity that needs to be done in close cooperation with the manufacturer and is a carefully planned activity so as not to disturb the patient care workflow.
- Medical manufacturers do not always provide a Software Bill of Materials (SBOM), Manufacturer Disclosure Statement for Medical Device Security (MDS2), and other field-deployment-related guidance on risk, which could make the vulnerability management life cycle complex in the long run.
- OT devices – While all enterprises depend on operational systems like building management, elevators, HVAC, UPS, etc., to function smoothly, the criticality is exponential in healthcare. Imagine an operating theater without power or access to elevators and an ER without the ability to admit new patients or access diagnostic systems. A hospital is a single unified inter-dependent entity where all systems need to function at the highest level of resiliency. An attack on one is an attack on all. Identifying vulnerabilities on these devices requires passive methods of understanding the OT systems. For instance. OT systems like building management systems need to be accurately inventoried and classified to understand its make/model/OS/patch levels and its associated vulnerabilities correlated to well-known vulnerability repositories like ICS-CERT.
- IoT devices (including office equipment and security/surveillance devices) – While these include everything from office equipment (printers, phones, video conferencing systems), sound bars to treadmills, vending machines, and gaming devices in rec rooms, hospital IT teams typically do not isolate these systems very well. The criticality of video cameras, badge readers, security alarms, and digital wall clocks is still high in hospitals but has the same issue as standard office equipment. Most scanning solutions do not offer the make and model details. Again, passive techniques to detect their device type make/model/OS/patch level are needed to assess their vulnerabilities accurately.
- Combined and interconnected with other medical equipment, they pose a massive challenge as it is easy for a hacker to compromise them and move laterally. For instance accessing these insecure devices and then, quickly laterally move and take over a Picture Archiving and Communication System (PACS) server that has thousands of patient scan images would be mission impacting
- Understanding the exact device types of IoT like make/model/OS/patches and associated vulnerabilities require various additional techniques like making direct queries to the device using protocols these devices speak to, interrogating and getting their operational characteristics and executing probes to get an accurate picture of the OS/patch level and the software installed on those devices.
- IT devices – Most scanning tools can periodically scan IT devices, understand their vulnerabilities, and generate a report. Ordr has APIs built for well-known vulnerability scanning platforms to kick start a scan, pull information from it, correlate it to devices in Ordr’s device database, and store it for management. However, IT devices need to be monitored continuously, covering the complete software stack installed on them and accurately tracking users logging on to the devices and local accounts created that are not under the control of the AD/Domain controller.
Every device everywhere (including those at remote clinics, and behind VPN/gateways)
More importantly, being unable to manage vulnerabilities for IT devices going off the grid and dialing back in from remote locations leaves enormous blind spots. This also applies to telemedicine and remote clinics. A care provider’s laptop while off grid accessing precious medical records is still a high risk one that needs to be monitored continuously. Vulnerability scanners need the device connected to the corporate network to send scanning packets to extract data based on their response. This is done both with full authentication and sometimes without authentication. But if the device is remote, there is no way to run scans continuously.
With the changing remote-hybrid work landscape, laptops connecting to insecure sites, possibly pulling malicious software, making an update or running wrong patches, and inaccurate/outdated inventory of software installed on that machine while they are off the grid pose a considerable risk. The nature of hybrid means they may not come and connect back to the corporate network any time soon and only click through VPN and other means.
Ordr “whole hospital” approach enables visibility for every device connected to the healthcare network – medical devices, OT devices, IoT devices to traditional IT systems. Clinical Defender 8.1 introduces our Ordr Software Inventory Collector. This feature uses features available in each device’s OS to send reports of software inventory of those systems along with the latest OS patch level for continuous monitoring. This enables visibility for Windows, MAC, and Linux devices connected via VPN even if they are offline.
Utilizing Vulnerability Scanners Effectively in a Clinical Environment
Unleashing any scanner in a hospital environment can be a dangerous move. The chance of knocking down a clinical device is exceptionally high. Unfortunately, vulnerability scanners do not have good visibility into the type of device and tend to scan all the devices broadly in a sweep in a specific subnet.
The Ordr platform provides the orchestration layer to send scan jobs to the vulnerability scanners with a list of IPs that excludes critical medical devices for scans and then pull those reports for storage in the Ordr platform.
2.3 Ownership Assignment Using a Centralized Platform
Consolidating vulnerabilities
The need for a central platform to be a repository of all devices and their associated vulnerabilities is paramount now, given the increase in attacks and the complexity associated with vulnerability management in healthcare settings.
Vulnerability scanning platforms typically produce a report each time they scan using a set of IP addresses. When vulnerability scans happen every quarter or six months, during which the IP address of devices changes, there is no way to correlate two consecutive scan reports from a vulnerability scanner to understand the progress made in vulnerability management.
Ordr is the only platform that correlates these IP addresses to MAC addresses, and then the device makes/model/type to help prioritize and understand clinical business risk.
Assigning ownership
Sometimes ownerships cross the device type boundaries and can be complicated. An HTM department may own almost all medical and office-connected devices in a building that even includes phones, printers, nurse call stations and endpoints in clinical diagnostics. It is not a simple case of assigning ownership based on device group or type. A flexible, scalable, and easy transfer of ownership based on region and location is essential. Also, asset/CMDB data like ownership, cost center, and business criticality need to be considered while assigning ownership. Each department within a hospital that takes ownership of the vulnerabilities must assign further these vulnerabilities to each person responsible for those devices to prioritize and focus the work accordingly.
Enhancements to Ordr Data Shaper allow each HTM user to focus on the devices and insights that align precisely with their specific business function group and role. For instance, vulnerabilities are prioritized and assigned to individual HTM personnel based on device type, hospital ID, department, cost center, etc. Ordr Custom Tags help improve workflows, for instance moving the vulnerabilities from one person to another, adjust severity, add comments, and track state change. The product customizes itself to show only those vulnerabilities on the front dashboard to track progress and provides summary management reports at many levels.
2.4 Clinical Prioritization to Improve Patient Care
With hundreds of thousands of devices reporting hundreds of vulnerabilities, organizing and prioritizing becomes daunting. A disciplined approach is needed to prioritize them according to business impact and assign them to the right owners inside the organization.
For risk prioritization, the CVSS is an excellent proxy for understanding the severity of vulnerabilities. Still, it is also essential to look at other frameworks such as ANSI, AAMI, NIST, ISO, FAIR, Risk IT, or JGERR, for supplemental guidance and a more comprehensive understanding to recalibrate them, going back to the foundational principles of Integrity, availability, and confidentiality.
Since healthcare organizations have complex organizational boundaries based on clinical and patient care and not according to the IT needs of a typical enterprise, organizing the data according to ownership is essential.
Ordr’s deep and comprehensive visibility of devices, their operating context, and traffic flows provides a number of key indicators to answer the following considerations for prioritization. Ordr insights can be used as a way to flexibly assess the risk score of a device. Risk score customization helps to prioritize and assign resources to work on the most pressing vulnerabilities.
- How widely does this vulnerability affect the device population of an enterprise?
- What is the level of business criticality concerning cost or other metrics?
- What is the impact to hospital brand and service if impacted – send ambulances to nearby hospitals and postpone elective surgeries?
- How well is the vulnerability exploited in healthcare – like the MAUI ransomware from Korea was targeting healthcare very closely?
- How open these systems are to the external world from a firewall policy perspective?
- How open these devices are to other device in the network with respect to isolation and segmentation perspective?
- How much PHI/PII these devices, that includes medical workstations and servers have? the more they serve as a central server, the more priority they need to get to resolve their vulnerabilities quickly.
- How tightly these devices are configured with respect to open ports?
- How well they are managed with domain controllers; If the device is not part of the domain controller scrutiny should be made more closely on those devices?
- How well they follow data encryption standards and how well they use strong ciphers while transferring data?
Clinical risk assessment
In the hospital, the risk is derived from various device related factors and operating conditions. While understanding the cyber threat is foundational, the clinical context in which the device operates in a patient care setting is a critical consideration. Business impact needs to be quantified on how quickly and broadly these risks affect the operational resilience and how well one can safeguard the devices carrying PHI/PII data. Without this clinical risk-driven prioritization, patient care availability and safety cannot be guaranteed.
Ordr Clinical Risk Scores deliver the following details about devices and clinical risks, and can be customized by every organization:
- Aggregate Cyber Risk (vulnerabilities, external access to phishing/C&C type sites), Internal Communications (access from unprotected non-medical devices, the criticality of the device)
- Environmental Risk (Polluted medical VLAN, isolated or segmented device, access thru wireless, etc.)
- PHI Exposure Risk (sending data without encryption or with weak ciphers, based on manufacturers’ disclosure, device portability, etc.)
- Clinical, Operational Risk (Physical Risk, equipment in ER vs. OR vs. stroke protocol center, is the device mission criticality of the device, what mitigations are applied, and location of the device)
2.5 Compliance and Remediation with Maximum ROI
Once healthcare organizations have a central platform with vulnerability information from different sources independent of how it is collected, workflow organization is critical.
Some of the critical capabilities essential to managing vulnerabilities efficiently can be found using the new “Business Function Grouping” feature in Ordr Clinical Defender 8.1. They include the ability to:
- Assign vulnerable devices based on hospital ID, department (HTM, endpoint, infosec, facility, etc.). Each department needs to focus and work on the devices they are responsible for and assign individuals who would work on those vulnerabilities. It is also possible to completely restrict those individual users to only those devices that they are responsible for. You also need a platform to do this much more dynamically, filtering by any business function grouping of devices.
- Create a focus group. For example, if this month’s goal is to work on all medical servers (like PACS) that house a lot of PHI data, then filter and have only those devices present every time one logs into the tool that month.
- Assign custom tags to draw attention to a co-worker, so the device passes from one person to another.
- Temporarily ignore some vulnerabilities. Often manufacturer-provided patches are unavailable immediately, or these devices are in the research department, not put into routine patient care, and are isolated from the rest of the hospital operation
- Modify risk, although the original risk per the attached CVE could be very high based on the operator’s judgment. Ability to clear vulnerabilities once patches are applied. Sometimes it is conceivable to increase the risk and priority of vulnerabilities of specific devices like CTs and ultrasounds in stroke protocol trauma centers.
- Track the status of vulnerabilities that fixed, assigned, or ope with the name of the person working on it.
Reporting and Compliance Enterprise-Wide
While manpower and budgets are a key consideration to determine the return on investment, the time it takes to remediate is also a critical as the longer there is an exposure window, the greater the chance of a breach. Resources need to be applied in an intelligent way to remediate critical vulnerabilities and get maximum return on investment.
Ordr offers an ability to keep a close watch on progress using various metrics and reporting as follows:
- Generate reports on-demand. For example, the flexibility to run select region, hospital, department, ownership, OS, and device type allows running reports on the fly.
- Customize reports for senior management visibility.
- Provide APIs that send data to a central corporate-wide tracking database.
Ordr makes reporting and customizations easy with a customizable risk score to adjust the weight ages for vulnerabilities, executive reports to provide summary insights into vulnerable devices, and a dedicated vulnerability report highlighting the impact of new open vulnerabilities on the organization.
Ordr also integrates and exchanges information with leading enterprise vulnerability scanners like Tenable and Rapid7 to provide enterprise wide reporting capability. Ordr also integrates with CMDB solutions like ServiceNow and their vulnerability management systems, allowing healthcare organizations to run corporate-wide reports for governance. Ordr collects medical and other device data and sends all the granular classification details, vulnerabilities, context, security, and operating details to these platforms.
Remediation
Based on various prioritizations, a project plan needs to be maintained, and remediation efforts tracked. Ordr provides an easy way to clear a vulnerability, change the state of the device and a comment field to add notes on the multiple steps towards remediation (called the vendor, the patch is available at this date, etc.
3. Best Practices for Vulnerability Management in Healthcare
Ordr recommends creating focus groups for each owner, with dedicated efforts on addressing critical vulnerabilities within 30 days, and with continued efforts by a few focus groups at a time. Once critical vulnerabilities are addressed, drill into high-risk vulnerabilities with the same focus group and ownership approach and remediate them within 60 days, It is always good to test the patches in a test or lab scenario before incorporating them on devices in clinical setting to reduce risks of downtime.
Ordr also recommends understanding device types and designing a strategy according to the device groups such as:
- IT systems that are not in clinical function – it is highly recommended that those devices are updated with the latest and most secure OS levels and associated patch levels.
- Medical devices that run Windows (a large device group in a hospital) – it may be impossible to upgrade the OS versions as it might trigger calibration and certification; in this case apply all the patches within their OS level.
- Medical devices that are unique versions supplied by the manufacturer — a patch request must be made to the manufacturer; it is important to fix these vulnerabilities ASAP
- IoT and OT – since neither the IT teams nor the supplier may be available to provide patches, the best course would be to segment them into specific network segments or VLANs, and closely control their interactions with the rest of the clinical devices.
Whether patches are available or not, it is best practice to follow the following proactive prevention best practices:
- Restrict external connections and allow only those absolutely critical connections to manufacturer’s sites at the perimeter firewall
- Understand supervisory protocols like RDP that are sometimes opened for manufacturing diagnostics and closely watch and close those just as soon as the maintenance window is over.
- Watch for all supervisory protocols like SSH, Telnet, RCP, etc., and make sure they are all only allowed from admin jump servers handled by authorized admins.
- Apply zero trust policies to only allow the most crucial and relevant communications for every device at the switch level if they are wired, at the AP/wireless-controller level if they are connected thru wireless, or at the firewall level both at the perimeter and the data center.
Ordr Clinical Defender with Vulnerability Management
Ordr is the only comprehensive and integrated platform that simplifies vulnerability lifecycle management for healthcare organizations of all sizes. We introduced Clinical Defender earlier this year, addressing HTM challenges with precision focus, and have now proudly added vulnerability management as we continue to innovate and address our customers’ most critical challenges. Clinical Defender now aggregates vulnerabilities for various device groups across all vulnerability management solutions, organizes them by hospital/department/owner, prioritizes by risk, and tracks the complete lifecycle from the initial assessment of a device to final remediation.
We are grateful to the various healthcare users that worked with our engineering and PM teams on this release.
To learn more about Ordr Clinical Defender 8.1 and how it can help your HTM team stay on top of connected device security, visit the Clinical Defender page.
Side Note: In a typical HTM department, inherent operating system (OS) vulnerabilities due to unpatched systems are the highest priority, much before tackling other security issues that may require implementing zero trust segmentation policies. This article discusses only vulnerabilities related to inherent OS/Patch levels. Check out other behavior and traffic flow related vulnerability discussions:
- Detecting Ryuk Ransomware with Ordr – Security Bulletin
- Solving IoT Security Challenges with Behavioral Analytics – Blog Post
- Ordr Security Brief and Response to Maui Ransomware – Blog Post
- Building a Better Second Line of Defense – Blog Post
Pandian Gnanaprakasam
Pandian has more than 20 years of product and engineering leadership experience and is also a serial entrepreneur. Before founding Ordr, he was the Chief Development Officer at Aruba, responsible for all of engineering and product management functions. Aruba, an enterprise mobile wireless company, was acquired by HPE for $3 Billion in March 2015. Before Aruba, Pandian served as the head of engineering for Cisco’s multi-billion-dollar Wi-Fi business unit and before that as VP of engineering for low-end switching product lines. He graduated with a master’s degree in Electrical Engineering from IIT, Chennai, India and holds several patents to his credit in various networking technologies.
-
 BlogDesign Thinking – How to Make Complex Data, Simply Useful
BlogDesign Thinking – How to Make Complex Data, Simply Useful…abilities, and dispositions. We expect this diversity will continue to expand and increase in complexity. Scoping data coming into the UI based on a user role allows us to reduce…
Security Strategy
Design Thinking – How to Make Complex Data, Simply Useful
8Min Read
By Pandian Gnanaprakasam

Design thinking is a team-based iterative process and the basis for a five-stage framework Ordr uses to develop and deploy our IoT security platform. Those stages are Empathize, Define, Ideate, Prototype, Test. Here’s why that results in a superior IoT security platform. Introduction
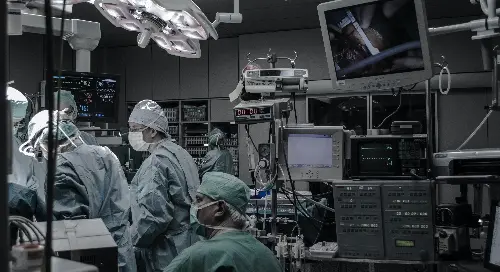
As Ordr has gained momentum over the years, the breadth and depth of our data lake have exponentially grown, with more customers adopting Ordr and extending our solution to protect more parts of their environments. More customers and more departments of each customer’s environment mean more devices, which means more data being ingested to our platform. The growth of our data lake can also be attributed to more external inputs as we increasingly take in new sources of device context data to provide deeper insights and help our customers understand risk.
The rate of data growth we have seen creates unique challenges on the visualization side. Recently we paused to think about how our solution could better organize and present vast amounts of rich analytical data in a way that is both accessible and valuable for our users. It is truly an art indeed on how to balance the desire for simplicity with the appetite for the rich context that goes with it.
As our user base expands to new roles and personas, the product must adapt to different outcomes relevant to each user. Each user’s level of expertise and area of interest may vary, and workflows must cater to these users seamlessly. A product must meet the needs of different roles without the need to fork and build a dedicated version to satisfy the diverse needs of each user. A daunting task is less often discussed but is nevertheless critical to maximizing value for users.
With full awareness of our challenge, we set off to radically improve how we present our ever-increasing data in the most impactful, simple way to our expanding universe of users.
The Approach
As part of our product design process, we decided on an iterative approach called “design thinking,” a process defined as:
A bottom-up, non-linear, team-based iterative process that seeks to understand and empathize with users deeply, challenge existing assumptions, redefine problems, and brainstorm innovative solutions to prototype and test with customers.
Design thinking gave us a framework of 5 stages that include:
Empathize > Define > Ideate > Prototype > Test
With the design thinking framework, we set up a series of workshops and enrolled a range of users from our customers and prospects representing a variety of user roles to provide us both depth and breadth of insights and feedback we needed to collect requirements.
We started the process by asking our users the simple question:
How can we design a better user experience to make the data we provide in Ordr simple to understand and valuable for you and your role?
Some of the key requirements we heard from our design partners included:
- Organize information to fit my role and help me filter out the noise so I can focus on the information I need.
- Surface insights most relevant to my role and make them clear. Insights are the road signs that help me make decisions as I look at data.
- Allow me to “shape” and organize data to fit my needs in a fast and fluid way.
- Help me maintain the context of my data so I don’t “lose my place” as I move around the application.
- Let me see different views so I can analyze data from different perspectives and uncover insights that might otherwise be missed.
- Prioritize content over color to me understand the structure of my data without unnecessary visual distractions.
The New Model Emerges
A key takeaway from the workshops was understanding that one user’s noise is often another user’s signal. It was clear that the new model needed to present data in a simple, customizable way without sacrificing the impact or richness of the data.
A query language approach is a good option, but it could not address the signal-to-noise problem without impacting other user requirements we had gathered during the workshops. For a query language approach to be successful, a user needs to know what they’re looking for and needs to become proficient in the new syntax and semantics of the language. This impacts adoption and time to value – two things we were not willing to sacrifice.
Our analytics engine is rooted in the foundational principle of surfacing a constant stream of prioritized insights in real-time vs. waiting for a user to “ask” for data using a query. In our view, the solution would come from a comprehensive understanding of the intersection between increasing data richness and a variety of UI/UX information retrieval approaches working together to achieve the desired result.
Pillars of the Model
From our learnings in the workshops, we defined the following seven pillars that guided the design of the UI/UX presentation model.
PILLAR 1: Create a clear consolidated experience for each role
Our users have distinct roles, backgrounds, traits, abilities, and dispositions. We expect this diversity will continue to expand and increase in complexity.
Scoping data coming into the UI based on a user role allows us to reduce the less relevant data (noise) and deliver a clean baseline of data (signal) for each user. With this in mind, we established a persona-based user experience, which requires filtering data from the data lake for a specific role and persona.
Persona-based filtering is easier said than done. The whole platform needs to run dynamic queries in the backend to customize itself on the fly. For example:
- An inventory and asset management workflow requires data on devices and relevant vulnerabilities.
- A security incident response workflow requires data on the latest alarms across all assets.
- A forensics workflow requires data on traffic flows and patterns.
For example, we designed a user role for Healthcare Technology Management (HTM) that switches the entire UI dashboard and shows only data relevant to their role and daily workflow needs.
The UI adapts to these wildly diverse use cases and data requirements while catering to each user’s role.
PILLAR 2: Provide each user with contextual insights
Insights offer users top-level guidance like a road sign to separate the signal from the noise. Our model uses computationally intensive methods to surface insights in real-time, tailored explicitly for each role.
Each user requires a different dashboard and depth of context for the workflow they are interested in to be presented as top-level data.
PILLAR 3: Allow each user to shape data relevant to their role
Data Shaping controls the scope of data allowing each user to either explore data or “set and forget” a view for specific workflows. Data Shaping reduces clutter by reducing the number of devices displayed, making it easier to slice and dice the data more cleanly.
For example, in our system, setting the data shaper to a specific location only shows the devices in that location and associated data. Whether the user is in a sub-section of the product or moving across the hundreds of panels, they see only data relevant to that location.
Another example is a radiology technician using the shaper to focus on radiology-related devices. The entire product today customizes itself to radiology devices across all panels and screens. That radiology technician can now work on security, traffic analytics, vulnerability management, risk management, or policy provisioning without being shown the “noise” created by other non-radiology devices.
PILLAR 4: Enable context-aware search across the entire UI
When the data set accumulates over time into several terabytes, launching a generic search that takes more processing time to respond back after several seconds does not usually present a good user experience. But tailoring the search function to each panel where the user is currently focused on reduces the data set to search and narrowing search parameters resulting in faster query time as well as better user experience.
As an example, in each table and each panel, search parameters differ as follows:
- Device detail table provides a search function on thousands of device attributes.
- The security alarm panel provides a search capability using alarm categories as parameters.
- The traffic analytics panel provides a search capability related to traffic/flow parameters.
- The application panel provides a search based on destination URL or application protocol details like port numbers.
- Search enabled in every column of a table with parameters within that column for further quick deep dive of data.
Implementing context-aware search in each panel when there are hundreds of panels is a huge undertaking. But now that it is designed in, it is well worth the effort to minimize complexity for the user.
PILLAR 5: Allow users to easily share findings and views
Once a user has reduced a view to a list of devices that need further action, that view, including the entire context, can be easily shared with others as a URL. Another user clicking that URL comes back to the same screen with a list of devices without having to search and filter for attributes. This is a perfect example of how context gets naturally amplified with the power of sharing. Our system today allows users to save the context at various places in the navigation workflow and share it with their colleagues.
PILLAR 6: Allow users to enforce policies quickly without losing context
The action framework allows users to take quick action on any device, alarm, or vulnerability without losing context in the UI. For example, today with this release, a user can identify a list of vulnerable devices and move that complete list to a quarantine VLAN with a single click. Another example is too easily clear a series of alarms associated with devices that have the same make and model with one click. Invoking an action that requires multiple steps in action sequence right within the context without losing focus is critical to get workflows accomplished quickly.
PILLAR 7: Allow users to define their own region/location for easy aggregation
Ordr gathers location information from various sources including switches, access points, and network management systems. Device location is extremely granular in Ordr and is helpful to track a device as it moves through an organization or locates a device that has gone missing. It is critical to know exactly where a device that is affected by malware/ransomware is connected in the network (switch/port or AP/SSID or VPN (Virtual Private Network) or external).
But for manageability purposes, users want to use location to view all devices in a specific region, site, or location within that site. A location means something different from user to user, so customization is critical. The need to present data based on business function was a key driver for this, and it avoids all the clutter. For example, a user responsible for the Phoenix division can use location to focus on the devices in the Phoenix location only and not have to see devices in other locations. Our ability to aggregate micro-locations into administrative regions is very well received by our customers, given the distributed nature of the various hospital chains as well as the continuous changes in organizational hierarchy due to mergers and acquisitions.
Combining the Pillars
Ordr provides users with details on over a thousand attributes for each device. Attributes include details such as device OS, software stack, vulnerabilities, where the device connects from, connection methods, what the device communicates with internally and externally, risks based on behavior, context information from various tools, and users who have logged into the device.
Ordr is indeed a complex and dynamic system with vast amounts of data and potentially limitless insights. Using all seven pillars in combination, we believe our approach dramatically improves the signal for each user and does so in the context of their specific workflows to ensure they can use our platform and insights efficiently. This platform approach also supports our quest to make the complex problem of securing every connected device simple.
We recently launched Ordr 8 Clinical Defender with persona-based workflows designed for healthcare HTM users. With this new release, we applied the pillar framework above and created a foundation for a scalable platform that will produce many persona-based workflows operating on a single customizable and robust backend data set.
We received some excellent feedback as we shared our latest release and here are some of the things we heard:
“It is refreshing to work with a vendor that listens and empathizes with issues and pain points from customers. It’s exciting to see the rubber meet the road regarding suggestions and requests.”
“Loved what I saw in the review of new GUI.”
“Data shaper simplifies my current operation dramatically.”
“I like simplified search and its’ consistency throughout the product.”
“Location-based shaper is huge both for remote clinic management and for M&A (Mergers & Acquisitions) situations.”
Moving forward, we will keep working with our customers and prospects as design partners in this “design thinking” framework to continually evolve our platform. In the end, it is all the constant customer feedback that makes Ordr an excellent product.
We will be back soon with more updates on how the Ordr platform continues to evolve.
Pandian Gnanaprakasam
Pandian has more than 20 years of product and engineering leadership experience and is also a serial entrepreneur. Before founding Ordr, he was the Chief Development Officer at Aruba, responsible for all of engineering and product management functions. Aruba, an enterprise mobile wireless company, was acquired by HPE for $3 Billion in March 2015. Before Aruba, Pandian served as the head of engineering for Cisco’s multi-billion-dollar Wi-Fi business unit and before that as VP of engineering for low-end switching product lines. He graduated with a master’s degree in Electrical Engineering from IIT, Chennai, India and holds several patents to his credit in various networking technologies.
Interested in Learning More?
Subscribe today to stay informed and get regular updates from Ordr Cloud
Ready to Get Started?
-
PagesAbout
…the CTO for Imprivata, and prior to that VP and CTO at Sutter Health, a 26 hospital network in Northern California. Prior to Sutter, Wes was CTO and then CIO…
About Ordr
We bring “Ordr” to the chaos and complexity of securing connected assets. By filtering out noise and pinpointing critical risks, Ordr empowers you to safeguard every asset — in the cloud, on-premises, or in SaaS environments– and enable cyber resilience.
Our Mission
To make the connected world a safer place.
Our Vision
To protect every connected asset throughout its entire lifecycle.
Meet Our Leadership Team
Jim Hyman
CEOJim Hyman joins Ordr bringing more than 20 years of experience building and managing world-class teams in enterprise software and Saas businesses with a specific expertise in cybersecurity.
Read MoreJim Hyman
CEOJim Hyman joins Ordr bringing more than 20 years of experience building and managing world-class teams in enterprise software and Saas businesses with a specific expertise in cybersecurity. Prior to taking the helm as Ordr’s CEO, Jim was at Synack, the leader in crowdsourced security testing as their Chief Operating Officer. Jim has successfully driven revenue generation at high growth start-ups and mid-market companies through innovative go-to-market strategies. Previously, Jim was at Trusteer (acquired by IBM in 2013), Z-Scaler (IPO in 2018), and Ironport Systems (acquired by Cisco in 2007). Jim’s experience spans sales, alliances, M&A, finance, venture capital and operations working in the US and internationally. Jim received his B.A. from The University of Pennsylvania and his M.B.A. in finance from The University of Southern California.

Gnanaprakasam Pandian
Chief Product Officer & Co-FounderPandian has more than 20 years of product and engineering leadership experience and is also a serial entrepreneur.
Read MoreGnanaprakasam Pandian
Chief Product Officer & Co-FounderPandian has more than 20 years of product and engineering leadership experience and is also a serial entrepreneur. Before founding Ordr, he was the Chief Development Officer at Aruba, responsible for all of engineering and product management functions. Aruba, an enterprise mobile wireless company, was acquired by HPE for $3 Billion in March 2015. Before Aruba, Pandian served as the head of engineering for Cisco’s multi-billion-dollar Wi-Fi business unit and before that as VP of engineering for low-end switching product lines. He graduated with a master’s degree in Electrical Engineering from IIT, Chennai, India and holds several patents to his credit in various networking technologies.

Sheausong Yang, PhD
Chief Scientist & Co-FounderBefore starting Ordr in 2015, Sheausong was the Chief Architect and VP of Technology at Aruba Networks, an HP Company and has over 28 years of industry experience.
Read MoreSheausong Yang, PhD
Chief Scientist & Co-FounderBefore starting Ordr in 2015, Sheausong was the Chief Architect and VP of Technology at Aruba Networks, an HP Company. He has over 28 years of industry experiences in wired and wireless networking, cellular communication, system management software, and cloud computing software. Sheausong held both technical and management positions in Cisco System, AT&T Bell Labs, and several startup companies. He received his M.S. and Ph.D. in Computer Science from Northwestern University, and B.S. in Electrical Engineering from National Taiwan University.

Raymond Lim
Chief Financial OfficerAs CFO, Raymond brings more than 20+ years of financial management and operational leadership experience guiding several VC-backed SaaS startup companies through rapid growth and transitional stages.
Read MoreRaymond Lim
Chief Financial OfficerAs CFO, Raymond is a key contributor to the company’s business strategy and overseer of all financial operations. He brings more than 20+ years of financial management and operational leadership experience guiding several VC-backed SaaS startup companies through rapid growth and transitional stages. He also brings expertise managing high-multiple strategic transactions. Prior to Ordr, he was the CFO of PerimeterX, the leading provider of solutions that secure digital businesses against automated fraud and client-side attacks, which was acquired by HUMAN Security in July 2022. Previous to that, he was the CFO for several VC portfolio companies backed by Norwest Venture Partners, Scale Venture Partners and Goldman Sachs. Earlier in his career, he held various financial, engineering and project management positions at ECbridges and Compuware.

Kevin Arsenault
Chief Revenue OfficerKevin Arsenault joins Ordr with over 20 years of leadership experience building and scaling high performance sales teams for successful SaaS based cyber security companies.
Read MoreKevin Arsenault
Chief Revenue OfficerKevin Arsenault joins Ordr with over 20 years of leadership experience building and scaling high performance sales teams for successful SaaS based cyber security companies. Prior to Ordr, Kevin held impactful sales leadership roles over 8.5 years at cyber security leader CrowdStrike, recently as VP of North America. He helped the firm celebrate a successful IPO in June of 2019. Prior to CrowdStrike, Kevin helped build compliance and cyber security firm Proofpoint to its IPO in April of 2012, rising to Worldwide VP of Advanced Security and Information Governance. Kevin also lead successful sales teams at Internet Security Systems (ISS) through its acquisition by IBM in August of 2006. Throughout his career, Kevin has maintained a maniacal focus on customer satisfaction with an emphasis on helping customers solve their IT/cybersecurity problems. Kevin received his Bachelor of Science from Boston College Carroll School of Management.

Wes Wright
Chief Healthcare officerWes is responsible for driving Ordr’s engagement in healthcare. Prior to Sutter, Wes was CTO and then CIO at Seattle Childrens’, which, to this day, he says was his most gratifying work experience.
Read MoreWes Wright
Chief Healthcare officerWes is responsible for driving Ordr’s engagement in healthcare. Previously he was the CTO for Imprivata, and prior to that VP and CTO at Sutter Health, a 26 hospital network in Northern California. Prior to Sutter, Wes was CTO and then CIO at Seattle Childrens’, which, to this day, he says was his most gratifying work experience. Prior to his tenure at Children’s, Wes was Executive Director, IS at Scripps Health in San Diego, and prior to that, he served in various CIO and CTO capacities with the United States Air Force, retiring as a Major. He has several publications and presentations to his credit, and has been a member of CHIME since 1998. Wes has a Masters in Business Administration from The University of New Mexico. Away from work, he enjoys traveling, jogging, napping and playing with his Boys – he’s a life member of “Marathon Maniacs,” but is not active anymore. 
Carla Wasko
VP of Human ResourcesAs Ordr’s Vice President of Human Resources, Carla Wasko is a results-driven leader accomplished in building HR strategies, cultures and infrastructures that enable business growth.
Read MoreCarla Wasko
VP of Human ResourcesAs Ordr’s Vice President of Human Resources, Carla Wasko is a results-driven leader accomplished in building HR strategies, cultures and infrastructures that enable business growth. Prior to Ordr, Carla’s breadth of experience includes over 20 year of HR leadership positions with several network and application security companies including WhiteHat Security, Infoblox, Blue Coat Systems and Packeteer.

Senthil Arunachalam
VP EngineeringSenthil has more than 20 years of experience in wired and wireless technologies.
Read MoreSenthil Arunachalam
VP EngineeringSenthil has more than 20 years of experience in wired and wireless technologies. Before joining Ordr in 2015, Senthil was the Director of Engineering at Aruba Networks, where he was responsible for the software development of Wireless and SDN products. Prior to Aruba, Senthil held engineering leadership positions at Cisco’s Enterprise and Data Center Switching business units. During his tenure, he led the development of Cisco’s flagship products, Catalyst 2K , 3K line of switches and was instrumental in building this multi-billion-dollar product line. He holds a B.S in Electrical Engineering from National Institute of Technology, Trichy, India, and M.S in Electrical Engineering from California State University, Northridge.

Dirk Campbell
VP Customer Success and ServicesDirk Campbell has extensive work experience in customer success and services roles, with special emphasis on customer satisfaction and operating cost-effective global technical support and customer success organizations.
Read MoreDirk Campbell
VP Customer Success and ServicesDirk Campbell is Vice President of Customer Success and Services at Ordr. He has extensive work experience in customer success and services roles, with special emphasis on customer satisfaction and operating cost-effective global technical support and customer success organizations. Prior to this, he was the Senior Director of Customer Success at ESS, Inc. and the Global Director of Support Services at Aruba, a Hewlett Packard Enterprise company. Dirk has also held positions as Vice President of Global Customer Advocacy at Pluribus Networks, Senior Director of Global Technical Support at Aruba Networks, Director of Worldwide Technical Support at Juniper Networks, Director of Worldwide Customer Advocacy at Neoteris, Inc, and Director of Customer Care at Blue Coat Systems (acquired by Symantec). His work over his career has helped build several of the best in class and most respected Services and Support organizations in the industry.
Meet Our Board of Directors
Jim Hyman
CEOJim Hyman joins Ordr bringing more than 20 years of experience building and managing world-class teams in enterprise software and Saas businesses with a specific expertise in cybersecurity.
Read MoreJim Hyman
CEOJim Hyman joins Ordr bringing more than 20 years of experience building and managing world-class teams in enterprise software and Saas businesses with a specific expertise in cybersecurity. Prior to taking the helm as Ordr’s CEO, Jim was at Synack, the leader in crowdsourced security testing as their Chief Operating Officer. Jim has successfully driven revenue generation at high growth start-ups and mid-market companies through innovative go-to-market strategies. Previously, Jim was at Trusteer (acquired by IBM in 2013), Z-Scaler (IPO in 2018), and Ironport Systems (acquired by Cisco in 2007). Jim’s experience spans sales, alliances, M&A, finance, venture capital and operations working in the US and internationally. Jim received his B.A. from The University of Pennsylvania and his M.B.A. in finance from The University of Southern California.

René Bonvanie
Executive Chairman, OrdrRené is an executive-in-residence based in Battery’s Menlo Park office. A 35-year technology-industry operating executive, he has had a front-row seat for most of tech’s major transition points, working in senior executive roles at Silicon Valley companies including Ingres, Oracle, Business Objects, SAP, Salesforce and Palo Alto Networks.
Read MoreRené Bonvanie
Executive Chairman, OrdrRené is an executive-in-residence based in Battery’s Menlo Park office. A 35-year technology-industry operating executive, he has had a front-row seat for most of tech’s major transition points, working in senior executive roles at Silicon Valley companies including Ingres, Oracle, Business Objects, SAP, Salesforce and Palo Alto Networks. Most recently, before joining Battery, René—who got his start in technology when he founded a software business in his home country of the Netherlands in 1983—worked in senior executive roles at cybersecurity company Palo Alto Networks. He served as its founding chief marketing officer (CMO) for 10 years, growing the company from a tiny startup to one with nearly $3 billion in annual revenue. René also played a key role in the company’s initial-public offering in 2012 and served for a year as executive vice-president of strategic accounts. Before Palo Alto Networks, he was a senior vice-president at Serena Software, Salesforce.com and SAP, as well as CMO of Business Objects and a senior vice-president of worldwide marketing at VERITAS Software. Prior to that, René’s experience was focused on databases. He joined Oracle Europe in 1992 as the company’s international marketing lead; then, four years later, former CEO Larry Ellison convinced him to move to Silicon Valley. There, he ran marketing for Oracle’s technology business, including the Oracle database and developer program, and developed Oracle’s internal CRM stack. He joined Oracle from INGRES, where he ran European product marketing for eight years. His first software-development business, started in 1983, used the Ingres database system first developed at the University of California at Berkeley. Over the years, René has also carved out a niche as a go-to advisor for many startups, including Armis, Acronis, Bionic, Bitwarden, Nexthink and others. René holds a degree in economics, with an emphasis on mathematics, from Amsterdam’s Vrije Universiteit and speaks four languages. He is also a devoted Star Trek aficionado.
Dominic Orr
Board Member, OrdrDominic Orr has an impressive track record of leading some of the industry’s most successful and innovative companies, taking them from venture-backed startups to high valuation IPOs and acquisitions. Most recently, Dominic was President of Aruba Networks, an HPE company
Read MoreDominic Orr
Board Member, OrdrDominic Orr has an impressive track record of leading some of the industry’s most successful and innovative companies, taking them from venture-backed startups to high valuation IPOs and acquisitions. Most recently, Dominic was President of Aruba Networks, an HPE company. Prior to Aruba’s acquisition by Hewlett Packard Enterprise, Dominic served as the company’s Chairman and CEO from an early stage startup in 2006 through a successful public offering on the Nasdaq in 2007, through the HPE deal in 2015. Prior to Aruba, Dominic was president of the Personal Internet Group at Nortel networks following its 2001 acquisition of Alteon WebSystems, an industry leading network infrastructure company that Dominic led as Chairman and CEO from its beginnings in 1996 through the Nortel acquisition, including an historic Nasdaq IPO in 1999. Dominic has also served as a board director for a number of companies, including Chairman of the Board of Ruckus Wireless from 2004 to 2009. Dominic has a BS in Physics from the City College of New York, and a Master of Science and PhD from Caltech. Dominic received the Distinguished Alumni honor from Caltech in 2010.

Alex Doll
Founder & Managing General Partner, TenEleven VenturesAlex is the Founder of Ten Eleven Ventures, the industry’s first venture capital fund that is focused solely on investing in digital security. Alex has been in security, software and finance roles in Silicon Valley for over 20 year
Read MoreAlex Doll
Founder & Managing General Partner, TenEleven VenturesAlex is the Founder of Ten Eleven Ventures, the industry’s first venture capital fund that is focused solely on investing in digital security. Alex has been in security, software and finance roles in Silicon Valley for over 20 years. He was the co-founder of PGP Corporation serving as board member, COO, CFO and VP Business Development from 2002 until its sale to Symantec in 2010. He has continued his involvement with security companies as an angel investor, independent director, entrepreneur-in-residence at Khosla Ventures, and private equity firm consultant with KKR. Alex received his MBA from Stanford’s Graduate School of Business and graduated cum laude from the University of Pennsylvania’s Management & Technology program with a B.S. in Systems Engineering from the Moore School and a B.S. in Finance from the Wharton School.
Dharmesh Thakker
General Partner, Battery VenturesDharmesh joined Battery Ventures in 2015 to focus on early-venture and growth-equity investments in areas including cloud infrastructure, big data, security and next-generation enterprise applications. Prior to Battery, Dharmesh was a managing director at Intel Capital, where he led the firm’s global cloud and big-data practice and made early- and later-stage investments in companies globally.
Read MoreDharmesh Thakker
General Partner, Battery VenturesDharmesh joined Battery Ventures in 2015 to focus on early-venture and growth-equity investments in areas including cloud infrastructure, big data, security and next-generation enterprise applications. Prior to Battery, Dharmesh was a managing director at Intel Capital, where he led the firm’s global cloud and big-data practice and made early- and later-stage investments in companies globally. Before joining Intel Capital, Dharmesh spent almost a decade in product management and go-to-market roles with enterprise-software companies like Keynote Systems, Manhattan Associates and two other startups leading to their acquisition. In 2016, Dharmesh was named to the Forbes Midas Brink list of up-and-coming venture capitalists, and in 2018 he was included on Business Insider’s 23 Top Venture Capitalists in Enterprise Tech list. A graduate of the University of Texas at Austin, where he received a BS in electrical engineering, Dharmesh also holds an MBA from the Wharton School of Business.
Peter Wagner
Founding Partner, Wing Venture CapitalAs a founding partner at Wing Venture Capital, Peter led investments in dozens of early stage companies, more than 25 of which have gone on to complete IPO’s or successful acquisitions including Nimble Storage, Redback Networks, Riverbed, Arrowpoint Communications, and Infinera
Read MorePeter Wagner
Founding Partner, Wing Venture CapitalAs a founding partner at Wing Venture Capital, Peter led investments in dozens of early stage companies, more than 25 of which have gone on to complete IPO’s or successful acquisitions including Nimble Storage, Redback Networks, Riverbed, Arrowpoint Communications, and Infinera. Before founding Wing, Peter helped lead Accel Partners for 15 years as Managing Partner. Peter holds an A.B. in Physics from Harvard College, summa cum laude, and an M.B.A. from Harvard Business School, where he was a Baker Scholar.

Gnanaprakasam Pandian
Chief Product Officer & Co-FounderPandian has more than 20 years of product and engineering leadership experience and is also a serial entrepreneur.
Read MoreGnanaprakasam Pandian
Chief Product Officer & Co-FounderPandian has more than 20 years of product and engineering leadership experience and is also a serial entrepreneur. Before founding Ordr, he was the Chief Development Officer at Aruba, responsible for all of engineering and product management functions. Aruba, an enterprise mobile wireless company, was acquired by HPE for $3 Billion in March 2015. Before Aruba, Pandian served as the head of engineering for Cisco’s multi-billion-dollar Wi-Fi business unit and before that as VP of engineering for low-end switching product lines. He graduated with a master’s degree in Electrical Engineering from IIT, Chennai, India and holds several patents to his credit in various networking technologies.
Awards and Recognition





Ready to Get Started?
-
 BlogThe Rise of Ransomware in Healthcare
BlogThe Rise of Ransomware in Healthcare…and propagate through file deployment and execution by PsExec. Once on the Domain Controller, they deploy a command to all connected devices to download Anti-Anti-Virus and Anti-Backup scripts along with…
Healthcare Security
The Rise of Ransomware in Healthcare
Tactics, Techniques, Procedures and Recommendations
8Min ReadBy Jeff Horne
Hospitals and healthcare organizations are lucrative targets for ransomware gangs as evinced by a sevenfold increase in attacks from 2019 to 2020. As ransomware attacks continue to rise, get insights, and learn how to protect your organization Tactics, Techniques, Procedures and Recommendations of How to Triage
Perspective on the increase in ransomware attacks
Ransomware continues to make the headlines as researchers warn of a seven-fold increase compared to 2019. Healthcare is a very lucrative target, with attacks increasing by 350% in Q4 of 2019 (compared to Q4 2018) and continuing to rise through 2020. The pandemic provided a significant opportunity for any threat actor looking to target healthcare providers, as the focus shifted from a holistic look at patient care, health outcomes, experience, revenue, and security to health outcomes. In addition, there has been a mass influx in connected devices deployed in facilities without the proper purview of IT and Security teams, leading to an incomplete asset inventory and clear visibility of how/where devices are communicating.
Ransomware as a viable threat to healthcare organizations has led to sophisticated attackers with complex and targeted campaigns. The recent wave of ransomware campaigns looks more like a hands-on hack than an autonomous piece of malware propagating across the network. The operators facilitating the recent ransomware attacks are heavily incentivized to make sure their malware is extremely effective at propagating diverse networks. We have seen simple pieces of malware like trojan droppers install remote control functionality and backdoors which allow these ransomware operators to then get on to the healthcare network and then run tools like Cobalt Strike to privilege escalate themselves to admin. Once admin privileges have been granted, these ransomware operators begin turning off the malware detection and incident response programs on the infected devices. We’ve seen these operators use tools like Mimikatz to dump memory and gather local admin passwords or common user passwords on systems. Once common passwords have been gathered, the network is theirs for the taking. In organizations that use Remote Desktop Protocol (RDP) on workstations and servers, we’ve seen these compromised local administrator accounts used to install and distribute the ransomware. We’ve also seen these attackers run PsExec and PowerShell scripts remotely by mounting remote shares (like IPC$ and C$) using the compromised credentials. If local or commonly utilized credentials cannot be gathered from initially infected host we’ve seen them pivot to other hosts, or use common exploits kits to propagate throughout the network. These operators are skilled and unfortunately most healthcare providers and healthcare delivery organizations are trivial to compromise once these ransomware operators are inside.
Healthcare organizations that have vulnerable services on the edge of their network get compromised easily by autonomous scripts that are constantly scanning the internet. Once compromised, the script drops a payload that includes all of the tools the operators need for privilege escalation, exploitation, and lateral movement. Many healthcare organizations have flat networks, and utilize common local administrator accounts on largely unpatched systems. It is common to find legacy and largely unsupported operating systems like Windows XP running on both workstations and critical medical devices which cannot be patched and are running vulnerable services like SMBv1 that are available to the entire network. Simply put, once the initial compromise happens, it is largely trivial for these ransomware operators to infect an entire healthcare organization within a few hours.
Let’s discuss the 3 most common ransomware campaigns that are targeting healthcare providers and healthcare delivery organizations and what their TTPs are:
Zeppelin
Brief Description:
The Zeppelin ransomware is believed to be operated by a Russian cybercrime group however very little is known about the operators. The initial infection code checks to make sure it will not infect machines located in Belorussia, Kazakhstan, Russian Federation, or Ukraine. The Zeppelin ransomware code is largely is based on a purchasable ransomware variant known as VegaLocker which is available on multiple hacking and ransomware as a service websites and forums. The initial infections of Zeppelin began in the beginning of 2019.
What does a Zeppelin Compromise typically look like (TTPs):
- Typically, a spam or phishing email is received by an organization that includes an infected document that download and installs malware onto the system.
- Some initial infections appear to be Vidar Spyware or the CobaltStrike penetration tester toolkit.
- Recently the Zeppelin operators appear to be exploiting vulnerable RDP, Apache Tomcat, and Oracle Weblogic servers available on the internet.
- Once connected to the infected system the operators will install PowerShell scripts and PsExec.
- In some Zeppelin instances a legitimate remote desktop application called ScreenConnect is initially installed (if it doesn’t already exist). The Zeppelin operators will connect to the ScreenConnect service and install the PowerShell scripts, privilege escalation tools, and PsExec.
- The Zeppelin operators will run a set of PowerShell Anti-Anti-Virus scripts and turn off logging to prevent detection and subsequently dump memory looking for local accounts that can be used to either propagate throughout the network or compromise the domain controller.
- Typically, the Zepplin operators attempt to compromise the domain controller and once compromised they create a domain admin account to distribute the Zeppelin ransomware throughout the network.
- The domain admin account that is typically created is called “SQLSvc”.
- If the domain controller is difficult to compromise, they attempt to distribute the Zeppelin ransomware using compromised credentials dumped from memory of infected systems and propagate through file deployment and execution by PsExec.
- Once on the Domain Controller, they deploy a command to all connected devices to download Anti-Anti-Virus and Anti-Backup scripts along with the Zeppelin ransomware.
- The Zeppelin operators utilize the certutil command on Windows to download and infect machines with the scripts and ransomware.
- Finally, the scripts and Zeppelin ransomware is executed on all connected devices via PsExec.
Ryuk
Brief Description:
The Ryuk (aka Conti) ransomware is known to be operated by Russian cybercrime group. The Ryuk ransomware was largely based on a previous ransomware codebase known as Hermes which was possibly created by a North Korean hacking group and is purchasable from multiple hacking and ransomware as a service websites and forums. The Russian cybercrime group started targeting healthcare organizations in late 2018.
What does a Ryuk Compromise typically look like (TTPs):
- A spam or phishing email is received by an organization that includes an infected document that drops a trojan downloader/bot that includes several tools for remote access, privilege escalation, and lateral movement.
- The Ryuk operators gain access to the Emotet/TrickBot compromised machine typically through a PowerShell script that launches a reverse shell that connects to the Ryuk operators.
- Once on the infected system the Ryuk operators turn off all PowerShell logging and run Anti-Anti-Virus scripts to prevent detection.
- Common lateral movement, privilege escalation, and exploit kits are downloaded onto the infected machine.
- It is common for the Ryuk operators to utilize the PowerShell Empire post exploitation kit.
- The Ryuk operators dump the infected machines memory looking for local accounts that are used on Workstations and Servers throughout the network.
- If local credentials are not found, the operators will use common exploit kits.
- Lateral movement and infection happen either via RDP or through PsExec.
- Typically, the domain controller is initially targeted and if compromised the domain controllers will typically be used to distribute the scripts and Ryuk ransomware to all connected users/computers.
- Anti-Anti-Virus and Anti-Backup/Recovery scripts are run on soon to be infected machines in order to prevent both detection and recovery from the Ryuk ransomware.
- The Ryuk ransomware is deployed to all machines using PsExec and a local service is created and started to run the Ryuk binary.
- The Ryuk operators sometimes oversee the infection to ensure that it is successful and once infected they start emailing employees informing them of the infection and to reach out to them via an anonymous email where payments are later discussed. The payment amounts typically vary depending on the size and the revenue of the organization that is infected.
Sodinokibi/Sodin/REvil
Brief Description:
Sodinokibi (aka Sodin, REvil) is another ransomware-as-a-service operation which started in April of 2019 and is believed to be created and operated most likely by the same Russian group behind the popular GandCrab ransomware. In early 2019 the Sodinokibi group is believed to have hired affiliate hackers with a guaranteed payment of $50,000 USD and between 60% to 70% cut of the revenue after payments were secured from victims. The developers of this ransomware regularly post updates and new functionality to their code. Once installed, Sodinokibi ransomware initially looks for the computers language settings and will not infect if the set language is used in most former Soviet Union or Middle Eastern countries. The Sodinokibi ransomware has been seen using several TTP’s including manual and automated drive-by compromises using spam/phishing attacks, common exploits, and previously compromised passwords.
What does a Sodinokibi Compromise typically look like (TTPs):
- It is difficult to describe the typical attack method used to deploy the Sodinokibi ransomware as there are several which leads some security professionals to believe that Sodinokibi is being operated by multiple cybercrime organizations.
- Sodinokibi has been seen distributed as a spam or phishing email that is received by an organization that includes a heavily obfuscated malicious JavaScript that includes PowerShell scripts that will turn off logging, disable antivirus functionality, and ultimately installs the Sodinokibi ransomware.
- The Sodinokibi operators also appear to be exploiting vulnerable WebLogic and RDP servers available on the internet.
- After the initial infection the Sodinokibi operators drop various exploit and privilege escalations kits to laterally move throughout the network.
- Similar to Zeppelin the Sodinokibi operators typically use the certutil command on Windows to download their scripts, exploit kits, and ransomware payload to infected machines.
- Once infected with the Sodinokibi ransomware, the malicious binary deletes all file shadow copies on the infected system and disables recovery mode in order to ensure that the encrypted files could not be restored from a local backup.
- The Sodinokibi ransomware includes several persistence and Anti-Anti-Virus and Anti-Backup/Restore functionality making the installation easy. This functionality makes it more autonomous for the operators which is why we sometimes see Sodinokibi installed in simple drive by attacks on vulnerable internet facing servers and services.
One concerning tactic that most ransomware as a service operators are starting to employ is to exfiltrate several important files from an infected organization and threaten to both publicly disclose the breach and publish the important documents on their blogs typically hosted on the Dark Web. We’ve seen many ransomware operators publicly announce and release sensitive material for companies that did not pay the ransom.
Recommendations on using Ordr to Protect Against Ransomware
- Discover and identify your weak points
- Identify devices running legacy versions of Windows that are running SMBv1 (such as Windows XP and Windows 7) The Ordr IoT Discovery Program allows you to quickly identify these devices. In Ordr’s Rise of The Machines Report, we identified that 15-19 percent of our deployments had IoT devices running on legacy operating systems Windows 7 (or older).
- Identify devices with known vulnerabilities as attackers will try to exploit them them. Use Ordr’s built-in scanner or take advantage of our integration with vulnerability management solutions like Rapid7 and Tenable.
- Identify high-risk and vulnerable devices that cannot be patched. Using Ordr integration with winRM, you can identify device operating systems and status of patches.
- Enable proactive segmentation
- Using Ordr, systems that cannot be patched need to be isolated. Ordr allows you to easily create segmentation policies that restrict devices to only sanctioned communications required for their functions.
- Work with Ordr and our firewall and networking infrastructure partners to enforce these segmentation policies in your existing infrastructure.
- Monitor for Ransomware Indicators
- Identify anomalous communication using the Ordr Flow Genome. This can include discovery of sequential scans on the internal network, and anomalous SMB, RDP, and RPC communications utilized in lateral movement.
- Alert on common exploits and known ransomware payload URLs used in lateral movement such as EternalBlue.
- Alert on common C2 communications to known ransomware payload servers; when infected machines reach out to these malicious sites, the Ordr product will alert on them.
- Track user logon/logoff activities using Ordr. Our platform provides a mechanism to pull user logon and log off activities from Active Directory and also track locally created users. This allows you to ensure the right users have access to vulnerable machines and identify any anomalous user accounts created within the network by threat actors
If you’ve already been attacked by ransomware, here are recommendations on how to deal with it, as described previously in this blog, A Primer on Preparing for and Responding to Ransomware for Users of IoT and IoMT. Note that with ransomware examples in this blog, there are no decryptors available at this time.
If you have questions about ransomware protection, please contact us at info@ordr.net. We work with a number of excellent integrators and managed security providers who specialize in protecting healthcare and other industries that are heavily invested in the use of connected devices.
Jeff Horne
Jeff Horne is currently the CSO at Ordr where he is responsible for security direction both within Ordr products and internal security. Prior to Ordr Jeff was the VP of Information Security for Optiv where he was responsible for all Security Operations, Governance Risk and Compliance, Endpoint, Internal Incident Response, Physical Security, and Employee Security Awareness groups. Before Optiv Jeff was the Senior Director of Information Security for SpaceX where he was responsible for the overall security strategy of SpaceX and managing the Information Security, Compliance (ITAR), Security Operations, and Physical Security groups. Previous to SpaceX Jeff was the Vice President of R&D and Chief Architect for Accuvant LABS where he managed teams of researchers and consultants specializing in reverse engineering, malicious code, incident response, breach analysis, and vulnerability assessment. Prior to Accuvant Jeff was the Director of Threat Research at Webroot Software where he led several teams of malware researchers, reverse engineers, and a development organization specializing in creating anti-malware functionality and detection signatures for all Webroot products. Jeff began his career as a Vulnerability Researcher at Internet Security Systems where he was responsible for vulnerability discovery, exploit creation, IDS evasion research, and behavioral detection of malware. Jeff is well known for his insight in interviews for numerous news channels and publications, speaking roles at various security conferences, as well as authoring several vulnerability disclosures and patents.
Interested in Learning More?
Subscribe today to stay informed and get regular updates from Ordr Cloud
Ready to Get Started?
- Typically, a spam or phishing email is received by an organization that includes an infected document that download and installs malware onto the system.
-
Knowledge BaseWhat is Healthcare Cybersecurity?
…control access to healthcare systems and data and reduce risk. Zero Trust principles can be applied to users, devices, data assets, and services in order to restrict communication and mitigate…
What is Healthcare Cybersecurity?
10Min ReadThe healthcare industry relies on connected devices to deliver patient care, and power hospital operations. These devices – from infusion pumps and MRIs to video cameras and HVAC systems need to be protected from cyberattacks such as ransomware. Additionally, these devices may include protected healthcare information (PHI) that need to be secured.
In order to ensure patient safety and protect all of these devices from abuse and attack, healthcare organizations need a whole hospital cybersecurity strategy. A whole hospital healthcare cybersecurity strategy ensures that every connected medical device and any device that includes data that qualifies as Protected Healthcare Information (PHI) or Personally Identifiable Information (PII) is secured.
As this article explains, the proliferation of connected devices makes it challenging to develop healthcare cybersecurity strategies that address all security requirements related to PHI, and can protect them against attacks to ensure patient safety. But with the right tools and methodologies, organizations can overcome these challenges to ensure they meet–or, even better, surpass–the minimal data security and privacy mandates that apply to PHI and PII in healthcare.
What is healthcare cybersecurity?
Healthcare cybersecurity measures are the tools and strategies that healthcare organizations use to ensure patient safety and maintain the privacy of sensitive healthcare data. Healthcare cybersecurity ensures that sensitive healthcare data stays restricted, and can only be accessed by parties like a patient’s doctor.
Healthcare cybersecurity protects healthcare organizations from external threats, like ransomware or hackers seeking to steal sensitive personal information to sell on the Dark Web. It also safeguards information against internal threats: these include malicious internal actors like disgruntled employees of a hospital, as well as users who inadvertently place sensitive information at risk. For example, hospital employees who fall prey to phishing schemes could risk hackers gaining access to sensitive patient information.
To deliver complete protection against data security risks, healthcare cybersecurity must be able to enforce data protection requirements over any and all systems used by medical organizations. For example, in a hospital, healthcare cybersecurity tools typically need to protect the following:
- Prescribing systems, which hospital doctors use to generate and manage prescriptions.
- Practice management support systems, which store patient healthcare information.
- Clinical decision support systems, where doctors manage information related to patient care.
- Radiology information systems, which store medical images and radiology data associated with individual patients.
- Internet of Medical Things devices, such as infusion pumps and remote patient monitoring devices, which collect healthcare data from individuals.
- Operational Technology devices, such as HVAC systems and elevator control infrastructure, could impact hospital operations, delay medical procedures, or put patient safety at-risk if compromised.
- Internet of Things devices such as smart speakers and smart screens, which may also collect data that can be associated with individual patients. Plus, attackers may use these devices as an initial threat vector, and use lateral movement to move deeper into a network.
These connected devices are critical to patient safety or empowering hospital operations, have the potential to generate and store PHI or PII, and must be protected against cyber attacks and data exfiltration risks.
In addition to securing diverse types of systems, healthcare cybersecurity must address the needs of multiple stakeholders. Hospital staff members must understand healthcare cybersecurity policies and resources to ensure they manage sensitive data responsibly, and keep abreast of constantly evolving cyber threats. For example, HTM and biomedical teams can leverage insights from healthcare cybersecurity tools to help with their day to day tasks, such as locating medical devices, identifying those with vulnerabilities, and taking advantage of utilization details to better plan patching and maintenance work.
Vendors who supply digital services and resources to healthcare organizations, too, have a role to play in healthcare cybersecurity. They are responsible for following robust cybersecurity practices to protect data that is stored or managed within their systems and devices. The same is true of healthcare security and IT teams, who play the leading role in hardening IT systems that store PHI or PII, as well as in identifying and responding to cybersecurity attacks.
To understand what healthcare cybersecurity looks like in practice across various contexts, let’s look at a few common examples of specific systems and devices that healthcare cybersecurity strategies typically need to cover.
Email
Although you may not think of email as a type of sensitive medical data storage system, the reality is that email inboxes store information like patient data. For that reason, email must be secured in order to meet mandates related to PHI and PII security.
In addition, email can be an attack vector for hackers who distribute malware or execute phishing campaigns via email. For that reason, it’s critical to secure email systems as part of healthcare cybersecurity in order to prevent the theft of private data.
Medical Devices
It’s common for hospitals and doctors’ offices to use a variety of medical devices to deliver healthcare. For example, nurses may use medical PC stations to keep track of patient records, or doctors might carry tablets to issue prescriptions.
If malicious actors gain physical access to these devices, they could access sensitive data stored within them or gain unauthorized access to other systems and data in the organization. They may even plant malware to carry out remote attacks later. Healthcare cybersecurity solutions must protect these devices against both types of threats.
Connected IoT devices
In addition to traditional IT devices, a wide variety of connected or smart devices are used across healthcare organizations, like Internet-controlled HVAC sensors and elevator controllers. If these devices aren’t properly monitored, secured, and patched as part of a healthcare cybersecurity strategy, they will be compromised.
Legacy systems
A legacy system is any type of system that is no longer supported by its manufacturer, but that is still in use: for example, an operating system that has reached its “end of life” date or an application whose vendor has gone out of business. Updating healthcare technology tends to be a complicated and expensive process. This means that healthcare organizations frequently depend on legacy systems until they find the time or resources to migrate to newer ones.
Legacy systems are vulnerable to attack because they no longer receive security updates or patches. Documentation about maintaining the systems is typically out of date.
Nonetheless, to protect against all potential cyber threats, healthcare cybersecurity tools must be able to protect data stored in legacy systems, even if support from the systems’ developers is no longer available.
Healthcare cybersecurity threats
For healthcare organizations today, it’s not a question of if they will face cyber attacks, but when. Breaches and attempted breaches against healthcare organizations are at an all-time high. That’s largely due to the fact that healthcare data presents such alluring targets for hackers, who encrypt sensitive data and hold it hostage for exorbitant ransoms.
Attackers use a variety of techniques in their efforts to access prized healthcare information. Some of these techniques include:
Malware
Malware is malicious software that gives attackers unauthorized access to systems or information stored on them. Malware enables threat actors to steal credentials, collect data, or gain control of systems in order to move laterally or cause disruption to services.
Ransomware
Ransomware is a special type of malware designed to encrypt data, rendering it unusable to the organization that owns it. After encryption occurs, attackers demand a ransom from the organization in order to decrypt the victim’s files. Unless the targeted organization has proper backups in place, it’s forced to choose between paying the ransom or suffering a major disruption to its operations.
Phishing
Phishing is a cyber attack technique in which threat actors trick users into sharing sensitive information. For instance, they might send emails impersonating IT staff or with malicious links to convince employees to share usernames and passwords. If the phishing attack succeeds, the hackers can then use the sensitive data to gain unauthorized access to systems and exfiltrate data, plant malware, or execute ransomware attacks.
Data exposure
Data exposure occurs when lost laptops, insecure physical systems, or IT breaches make sensitive information accessible to unauthorized parties. Data exposure is not an attack, per se, because it’s not the result of a malicious activity by hackers. But the end result–the exposure of sensitive information–is the same as it would be in the case of conventional cyber attacks.
Insider threats
Insiders, like hospital staff, have legitimate access to various systems. If employees intentionally or accidentally misuse those systems, they place sensitive data at risk. This is especially true if the systems are configured with excess permissions that grant internal users more access than they need.
System vulnerabilities
Unpatched software, out of date software, recalled devices, and banned devices could be subject to system vulnerabilities. Information about vulnerabilities is often published in public databases, recall information is available from manufacturers, and banned devices are available from organizations such as the FDA. Hackers can easily find and exploit these known vulnerabilities and vulnerable devices to plant malware or gain access to vulnerable systems, and place the entire organization at risk.
Healthcare cybersecurity best practices
Although every healthcare organization’s security risks and requirements are different, there are healthcare cybersecurity best practices that every healthcare organization should follow to mitigate the risk to patient safety and of the misuse of PHI and PII.
Achieve visibility
You can’t protect what you can’t see. For that reason, maintaining comprehensive and continuously up-to-date visibility across the whole hospital is the first step in healthcare cybersecurity.
Comprehensive visibility means knowing about all assets that are connected to your organization’s network, the services those assets provide, the data those devices collect, manage or access, and which security safeguards are (or aren’t) in place to protect the devices. Visibility also ensures that you are aware of vulnerabilities that place devices, services, and data at risk. This way, you have a complete view of the attack surface and can assess for vulnerabilities and potential risks and monitor for threats.
Perform risk assessments
Risk assessments are systematic evaluations of healthcare cybersecurity vulnerabilities and threats that exist and the level of risk each one poses. Risk assessments may also be used to document measures that organizations have taken to prevent breaches.
Healthcare organizations should perform risk assessments on a regular basis–at least once a year, if not more often–as part of their security strategy and may be required to meet compliance requirements or to obtain cyber insurance. Risk assessment procedures should be updated whenever new devices or services are deployed.
Implement security controls
Security controls, meaning tools and procedures that organizations use to harden systems against attack, go a long way toward minimizing healthcare cybersecurity risks. Foundational security control measures include tools such as antivirus software, which can help to prevent malware attacks. Data backup and restoration platforms recover compromised data following a ransomware breach. Data encryption, network firewalls, incident response planning, and multi-factor authentication also help to establish baseline security defenses for healthcare systems.
Connected device security tools and solutions, such as Ordr, are also critical to discover and classify every device in healthcare systems, inspect East-West traffic for malware or communications to a malicious domain, and identify vulnerabilities within devices. In particular, within a healthcare environment, these connected device security tools MUST be designed to operate in a healthcare environment – for example, the discovery and vulnerability identification process cannot impact sensitive medical device operations. Therefore, these devices must offer an “agentless, passive” approach to security.
Zero Trust
Many modern healthcare organizations have adopted Zero Trust as a core cybersecurity strategy. With Zero Trust the minimum necessary permissions are put in place to control access to healthcare systems and data and reduce risk. Zero Trust principles can be applied to users, devices, data assets, and services in order to restrict communication and mitigate the risk of abuse.
An example of Zero Trust is the use of network access control (NAC) to control device and user access to the network and services. Another example is network segmentation, sometimes referred to as microsegmentation, a technique that isolates devices on the network and prevents unnecessary communications.
Educate staff
Education such as cybersecurity awareness training ensures that healthcare workers are aware of risk and follow best practices to protect patients, services, and data. Healthcare staff should know how to spot threats, like phishing emails, and to react appropriately. They must also be aware of the risks posed by both external and internal threats.
Staff education is also a means of spreading awareness of legal requirements related to healthcare cybersecurity, such as those imposed by HIPAA, so that workers can do their part to adhere to compliance rules.
Healthcare cybersecurity laws and regulations
HIPAA, or the Health Insurance Portability and Accountability Act, is the best-known of several laws and regulations that governing bodies created to enforce healthcare cybersecurity best practices. Although complying with these mandates is not the only reason why healthcare organizations should protect sensitive data, it’s often a core motivator. This means that a familiarity with healthcare laws and regulations is an important component of healthcare cybersecurity.
HIPAA contains several provisions that impact the security of healthcare data. One, known as the Privacy Rule and defined in 45 CFR Part 160 and Subparts A and E of Part 164, establishes permitted and required uses and disclosures of PHI. It also deems PHI to be individually identifiable, and therefore subject to specific security requirements.
In addition, 45 CFR Part 160 and Part 164, Subparts A and C set forth specific security requirements related to PHI that are stored electronically, since most healthcare data is stored this way today. These requirements are referred to as the HIPAA Security Rule. Finally, HIPAA imposes (in 45 CFR §§ 164.400-414) a Breach Notification Rule that generally requires organizations to notify affected users in the event of a cybersecurity breach involving PHI.
Beyond HIPAA, other legal regulations may apply to healthcare data. For example, 42 CFR Part 2 is a law that protects patient records created by programs that receive federal funding to treat substance use disorders. It establishes very specific and extensive privacy requirements related to PHI in this context.
Additionally, the National Institute of Standards and Technology’s (NIST) Framework provides guidance, guidelines, and practices for organizations to reduce their cybersecurity risk. Developed in 2014 and updated in 2018, the framework also helps organizations and businesses better manage risk and cybersecurity communications. Overall, the NIST framework gives organizations a common language and systemic methodology for risk management.
The framework itself is made of three components: core, tiers, and profiles. The core helps organizations manage and reduce risks in a way that compliments their current cybersecurity practices. The profiles allows organizations to identify areas where existing processes can be optimized and new processes can be implemented. Finally, the tiers asks organizations to consider how strictly their cybersecurity program will comply with NIST standards.
Likewise, the HHS 405(d) Health Industry Cybersecurity Practices (HICP), which is integrated into the NIST framework, lays out specific guidelines for healthcare cybersecurity standards. According to the HHS, the top threats for cybersecurity are:
- Email phishing
- Ransomware attacks
- Loss or theft of equipment
- Accidental or intentional data loss
- Connected medical device attacks that impact patient safety
Both the NIST framework and the HHS 405(d) operate to protect healthcare agencies and patients.
Protect Your Whole Hospital
Healthcare cybersecurity threats come in many forms and apply to a wide variety of systems. For that reason, healthcare organizations should establish a comprehensive cybersecurity strategy including protections that can defend all of their assets–ranging from conventional IT systems, Internet Medical of Things devices, and unsupported legacy systems to connected facilities devices, Internet of Things devices, and beyond–against all types of attacks, risks, and threats. Organizations must also maintain comprehensive visibility across the entire organization including high risk assets and whether they are secure. And they must be aware of specific regulatory mandates and implement protections necessary to comply.
Ordr can help with a whole hospital approach to healthcare cybersecurity. By automatically discovering and accurately classifying all connected devices that healthcare organizations depend on, we maintain a continuously updated inventory to provide comprehensive visibility into healthcare systems, vulnerabilities, and risk. In addition, Ordr can help organizations enforce healthcare cybersecurity best practices based on Zero Trust principals, helping organizations protect critical data and services, meet strict compliance and data privacy mandates and ultimately, ensure patient safety.
Interested in Learning More?
Subscribe today to stay informed and get regular updates from Ordr Cloud
Ready to Get Started?
-
 BlogSolving IoT Security Challenges with Behavioral Analytics
BlogSolving IoT Security Challenges with Behavioral Analytics…and most behavioral analysis systems fall short. To achieve positive controls, we must understand and use automation to control behavior. There are too many devices and network segments for security…
Security Strategy
Solving IoT Security Challenges with Behavioral Analytics
7Min Read
By Pandian Gnanaprakasam

Behavioral analytics are vital to understanding the IT estate, and detecting/preventing threats. Ordr’s own Gnanaprakasam Pandian describes why complete asset discovery, accurate operational data ingestion, and real-time behavioral analytics are key to threat detection and prevention. Organizations spend more than ever on security, yet the rate and impact of attacks continue to grow. Is a positive or negative security model the right approach to address today’s concerns, specifically to protect IoT devices?
SPOILER ALERT: you need a hybrid model based on behavioral analytics.
Traditional approaches to cybersecurity simply can’t keep pace with attackers becoming increasingly specialized, organized, and sophisticated. Security leaders and practitioners know that a new approach to security is needed, but navigating the myriad buzzwords and claims about artificial intelligence (AI), machine learning (ML), and behavioral analytics can be challenging. With that in mind, I want to explain how and why a new approach using behavioral analytics (including AI/ML analytics algorithms) solves real-world security problems today.
The Negative Security Model
A negative security model will “allow everything” by default while attempting to identify the “bad.” This approach is a mainstay of security tools such as antivirus software or IDS/IPS and has dominated cybersecurity for most of its brief history.
Just as credit card companies use rules and known attributes to identify fraud, negative security controls use rules and signatures to identify known threats previously seen in the wild. When the threat is seen again, security tools can detect and block the malicious traffic, malware, exploit, URL, etc.
Negative security controls are good at identifying known threats. However, tools using these controls can only identify and block what they are told to block. A signature must exist, or a tool must be configured to block malicious activity. Ongoing care and feeding are required to keep tools up to date with the latest signatures and configurations to detect and stop threats.
A negative security model alone is essentially defenseless against widespread zero-days such as the recent Log4j vulnerability, which impacted thousands of enterprise products and created massive exposure for virtually every modern organization.
Depending entirely on negative controls for threats has some serious limitations, and organizations need both negative and positive controls to protect their assets and environments.
The Positive Security Model
A positive security model is the opposite of a negative security model and works by defining allowed actions. Instead of defining a blocklist of “bad” actions, the positive security model defines what is “good” or allowed. Think of positive security as the doorman at an invitation-only party as a simple analogy. Instead of identifying and blocking “bad” attendees, the positive security doorman uses the guest list to define who should be let in.
A network firewall is a classic example of a positive security tool. Only specific, required network ports are open, while all other ports and traffic are denied by default.
A tool using the positive security model can address the shortcomings of a tool using the negative security model by providing a far more proactive approach to security. Instead of constantly chasing the “bad,” a positive model focuses on what applications, users, and devices need to do their job. Everything else is flagged or blocked. It doesn’t matter if an attacker targets a zero-day vulnerability – anything that doesn’t match the “good” list or vastly differs from normal activity will be denied.
As a simple example, attackers often gain initial access to an environment by using phishing emails to get a user to click a link or open an attachment. The attacker can easily evade negative security controls by altering a URL or malware payload. As controls become more sophisticated, so do attackers by changing their tools and methodologies.
Once on a user’s device, the attacker will target other assets in the environment in an attempt to move laterally, often using protocols such as SMBv1 or RDP. Since this movement is outside the norms of valid activity, positive security controls can recognize and deny the abnormal behavior without prior knowledge of the methods used or the specific threat.
Blending Security Models With Behavioral Analytics
To meet today’s security challenges, a blend of negative and positive controls is essential. More importantly, behavioral analytics must be applied to enable a positive security model, control an organization’s complex communication patterns and address security challenges in ways never possible before.
Positive security is more complicated than simply allowing communications or opening ports on a firewall. Instead of focusing on individual traits or indicators, positive security requires understanding the more complicated world of behavior.
Consider the different scenarios of medical devices in a research facility, outpatient care, and a critical care environment. Some of the devices may be similar in make and model; however, their use and criticality in each environment will dictate different requirements, priorities, and risk tolerance.
A system needs awareness of a device’s purpose, the services or assets it needs to access, and how similar devices in the environment behave to provide the right level of protection.
In recent years, anomaly detection and behavioral analytics have been hot topics in security but have delivered mixed results. The ultimate goal for successful solutions today is to leverage behavioral analytics for truly reliable and valuable insights. For that, we need to cover three essentials.
1. Get all the right data from the best sources
Instead of simply identifying specific behavior as abnormal, the goal of positive security is to enforce controls that keep devices and data safe while ensuring each device can function in the environment as needed. Positive security requires a deep understanding of what each device is, its role, purpose, and communication patterns. To get this level of deep understanding requires large amounts of ground truth data. Arguably, the network provides the most accurate and reliable source of data needed to understand this level of detail.
An agent-based approach will result in blind spots across the exploding population of unmanaged devices that include IoT, IoMT, OT, and other connected devices. Agents are notoriously painful to manage, and for many unmanaged devices, agents are either not available or difficult to develop. It’s virtually impossible to ensure agent compatibility with the myriad combinations of connected device hardware, software, and firmware. Agents impact performance in the best case and completely disable devices in the worst case.
Understanding device behavior requires a “show me, don’t tell me” approach, and looking at device communication flows over the network provides the best source of truth.
To quote Batman, “It’s not who you are underneath, it’s what you do that defines you.”
Normal behavior informs the positive security model for a specific device profile, and normal behavior can be determined by baselining communications flows and understanding the systems it communicates with. With this understanding, policies can align with a zero trust framework limiting device communications to the required systems and nothing else.
Ordr collects and analyzes network data to create a baseline of normal behavior, and map communication flows for every device. The baseline for each device is automatically tuned, updated, and compared to the device’s historical behavior and similar devices in the environment. Device flow information is enriched with device context, threat insights (threat intelligence, third-party vulnerability databases, and reputation data), network data (from switches, routers, and wireless controllers), and additional data (IPAM, DNS, CMDB, Active Directory) as we continuously analyze the activity of every device. All of this data is collated into the Ordr Data Lake and continuously analyzed to identify any changes in behavior.
2. Organize the data for effective analysis
We need to know every device’s “what, where, and why.” An algorithm won’t magically generate needed answers from massive amounts of data. Getting valuable insights requires organizing data hierarchically with relationships properly established.
Is the device a patient monitor, a security camera, or a printer?
Where is the device located, and why does it behave the way it does?
What data and systems does the device serve, and what does it require?
Ordr organizes data to see the interrelationships between devices, the network, and how data flows in all directions to answer these questions. Ultimately, all this context is organized in terms of the device itself. While analyzing hundreds of thousands of records may still be required, analyzing organized data is far more manageable and focused than iterating over massive amounts of data.
Analyzing organized data enables focus on specific types of devices and behaviors to uncover valuable security insights. Analyzing organized data can be used to learn how patient monitors behave as a generic device and a specific model of monitor. We can understand how other similar devices in the network behave to identify unique traits and specific needs in each organization.
Analyzing organized data can help answer important questions that drastically change a security team’s ability to respond to an event. For example, when a hospital sees a malicious outbound DNS request, there may be no need for action if the request is from a visitor’s laptop on the guest network. On the other hand, it would cause serious concern if the malicious request came from a hospital-owned infusion pump. Ordr provides these insights by properly organizing and analyzing data.
3. Understanding and explaining behavior
Once we know where to look, we need to understand what we see in terms of behavior on the network. Having partial information for security is not helpful, and this is where most cybersecurity behavioral analysis attempts fall short. If a security tool can’t explain in detail what was detected, an analyst has to do the work to understand what happened. A tool that generates anomalies it can’t explain will quickly drown security analysts in work or, more likely, cause them to miss critical events. It’s not enough to say a learning algorithm triggered an alert. More context is required to instill confidence and to ensure priority for action.
Ordr analyzes network data to create a baseline of behavior for each device in an environment. That baseline is then combined and analyzed with the baseline of other devices. With this approach, Ordr identifies activity outside of normal behavior for the device, its cohorts in the environment, or similar devices deployed globally.
Additional details such as the specific device, physical location, internal and external connections, and communication information are critical to ensure that incident response teams have enough detail. Proving this detail in an easy-to-understand, graphical way with the flexibility to customize the view is critical for any AI-based tool to be useful.
Analysis to uncover attribution and explainability is complicated. Making this easy for security teams is one of the essential traits of Ordr. The image below shows the enormous scale of analysis needed for a single Ordr customer deployment.
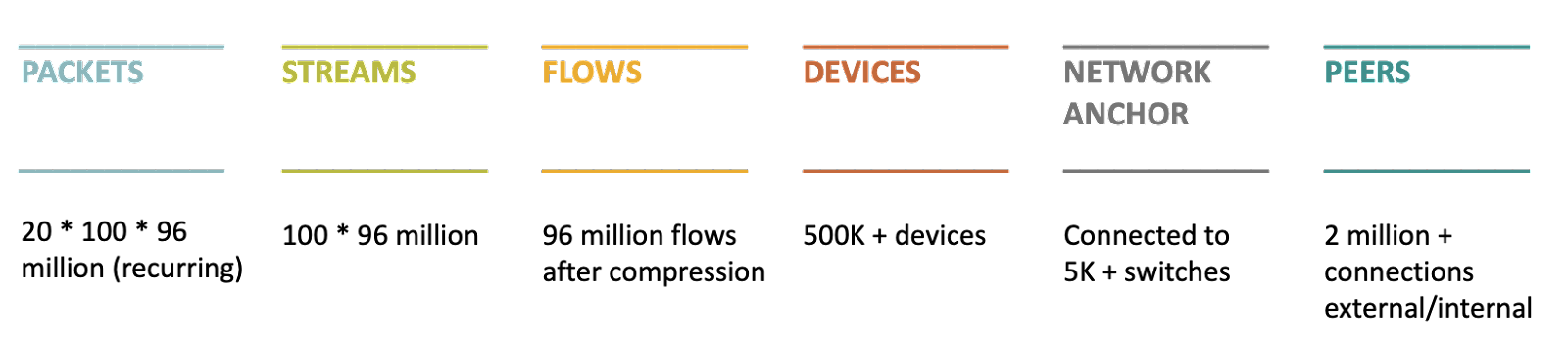
Ordr ultimately rolls behavior up to the device level. The center of the diagram above highlights the Ordr database of behavioral patterns for over 500,000 devices.
Understanding the behavior of these devices requires the analysis of 96 million network flows. However, to truly perform attribution and achieve understanding, we need to analyze the 100 streams that make up each flow and the packets that make up each stream. This essential task is where the analysis gets complex, and most behavioral analysis systems fall short.
To achieve positive controls, we must understand and use automation to control behavior. There are too many devices and network segments for security teams to understand the complexities of each one. Instead, security tools must understand and control behaviors in the same set-it-and-forget-it way that traditional firewalls control network ports.
Providing this level of simplicity to security teams requires a new type of analysis and a new type of security solution. One that we at Ordr continue to build and optimize.
Ordr’s Unique Approach to IoT Security
While most behavioral analytics solutions have failed to live up to the hype, Ordr provides actionable and practical answers to secure your connected devices without creating new headaches for users or security teams.
To illustrate, consider blending the positive and negative security models along with behavioral analytics to detect the multiple stages of a ransomware attack kill chain. In most instances, Indicators of Compromise (IoCs) are not available immediately after detecting an attack in the wild. In these cases, a positive security model compliments a negative security model by providing greater insight into a potential problem in the network and the attack timeline. Once IoCs are defined, they can be validated using the negative security model.
The screenshot below shows the detection of stages of the kill chain using different security models.
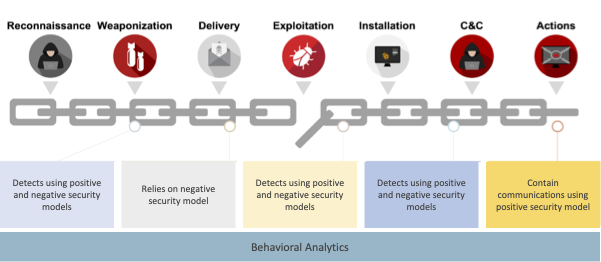
If you have thoughts or questions about this blog, or simply want to learn more about Ordr, reach out to the team for a deep dive discussion.
Pandian Gnanaprakasam
Pandian has more than 20 years of product and engineering leadership experience and is also a serial entrepreneur. Before founding Ordr, he was the Chief Development Officer at Aruba, responsible for all of engineering and product management functions. Aruba, an enterprise mobile wireless company, was acquired by HPE for $3 Billion in March 2015. Before Aruba, Pandian served as the head of engineering for Cisco’s multi-billion-dollar Wi-Fi business unit and before that as VP of engineering for low-end switching product lines. He graduated with a master’s degree in Electrical Engineering from IIT, Chennai, India and holds several patents to his credit in various networking technologies.
Interested in Learning More?
Subscribe today to stay informed and get regular updates from Ordr Cloud
Ready to Get Started?
-
Knowledge BaseIoT in Manufacturing: How OT/IT Convergence is Changing the Industry
…processes. Digital twins can also be used to mirror processes and model diagnostics. For example, a business may want to understand the effect of changing the speed of a specific…
IoT in Manufacturing: How OT/IT Convergence is Changing the Industry
7Min ReadThe Internet of Things (IoT) and other connected devices have been integral to the efficient operation of manufacturing lines for decades. Security of the production line was maintained by isolating equipment in what was known as the Purdue Methodology—air gapping the network to keep it out of reach from threat actors. But as digital supply chains required hyperconnectivity to enable data exchange and greater levels of automation, the air gap was bridged, and manufacturers became vulnerable. A new Purdue Method is needed.
Fortunately, the means to protect connected devices on the production line is available. The following article offers insights and best practices to help guide an IoT security strategy for manufacturers.
The use of IoT in manufacturing continues to accelerate and evolve, as do the threats that come with the convergence of OT and IT. Recently, NSA and CISA released an alert warning manufacturers of potential security vulnerabilities in their OT systems. The alert cited an increase in the number of threats to OT assets including ransomware, spear phishing attacks, and the modification of control logic parameters, among others.
The primary driver of the emerging threats to OT is the unification of OT devices and systems with IT and IoT, or as NSA describes it, the proliferation of “internet accessible operational technology.” This increase in the number of OT devices and systems that integrate with IT is the result of developments in technology, evolving features and capabilities, the movement of network access control vendors into OT, as well as mergers and acquisitions.
In this article, we look at some of the use cases for IoT in manufacturing, as well as the challenges and opportunities that manufacturers face at the intersection of OT/IT. But first, a couple of quick definitions.
https://www.youtube.com/embed/Ex1_s6bsYr8?feature=oembedWhat is IoT in manufacturing?
IoT in manufacturing is the subset of the industrial internet of things (IIoT) specific to manufacturing applications. IIoT is the network of sensors and devices that connect to computer systems and industrial software applications.
While IIoT refers to industries such as retail, utilities, or transport, IoT in manufacturing specifically applies to the Internet-connected sensors and devices used to track and produce goods more efficiently.
Both IoT in manufacturing and IIoT are themselves part of the broader internet of things (IoT), which comprises all the internet connected devices and sensors across domains. When people talk about IoT in practice, however, they’re typically referring to the consumer applications—such as smart home devices—so we’ll stick to using the term IIoT for sake of clarity.
What is operational technology (OT)?
Operational technology (OT) consists of hardware and software components that monitor, control, and create changes in industrial equipment, devices, assets, processes, or events. OT technology systems may control industrial elements such as engines, conveyors, valves, or machines that are directly connected to the manufacturing process.
While OT systems were once commonly siloed from IT (or at least thought of as distinct from IT), the present trend is toward more integration of IT and OT systems. Three primary factors are driving this convergence of IT/OT:
- Increased reliance on/availability of remote operations and monitoring
- Outsourcing OT asset management and/or maintenance
- Decentralized workforces
The trend toward more unified OT/IT systems and greater IoT connectivity in manufacturing brings new capabilities and control for manufacturers, but also some risks. In the next section, we’ll explore some IoT in manufacturing use cases, benefits and challenges, as well as some of the ways manufacturers can mitigate these risks.
Use cases: IoT in Manufacturing
The digital transformation of the manufacturing industry is changing the way production environments and supply chains work by improving efficiencies, automating processes, and adding intelligence.
But challenges accompany these opportunities, and manufacturers will need a strategy if they are to successfully capitalize on these benefits without compromising security or efficiency. Before we look at some specific use cases, it’s important to consider some of the needs manufacturers will face as IT/OT continue to converge:
- Visibility – Decisions about which OT devices and systems will be used are increasingly being made by multiple stakeholders in the supply chain. Manufacturers need visibility into all of these devices, as well as a system for asset discovery, classification, and segmentation for those with security vulnerabilities.
- Compliance – IoT, IT, and OT compliance depends on navigating an increasingly complex system of regulations. Understanding which devices are governed by each specific set of standards can help manufacturers cultivate robust security and remain in compliance.
- Efficiency – Aging devices put manufacturers at risk of losing efficiency as operating systems become obsolete or outdated. Recognizing which devices can still be secured can increase their longevity and avoid downtime.
- Intellectual property – As the number of attacks on OT and IoT devices continues to increase, manufacturers are at increased risk for theft of intellectual property. Manufacturers need a strategy for identifying business-critical devices and flagging abnormal behavior in order to protect their most valuable assets.
Manufacturers already rely on IoT devices and connectivity to drive production, quality control, and machine utilization, and additional use cases continue to evolve as OT/IT merge. These include the rise of predictive maintenance, real-time monitoring, remote management, and the collection of consumer insights.
Predictive maintenance
With the aid of sensors and the increase in data from manufacturing equipment, companies can now detect and predict failure before it occurs. For example, an analytical model may find that a machine has a high probability of failing when it breaches a specific temperature threshold. With this information, the monitoring applications can alert the machine operators when the event occurs, and they can then promptly replace it before causing larger issues with production.
According to Fortune Business Insights, the global market for predictive maintenance is expected to grow at a CAGR of 29.8% through 2026. That makes predictive maintenance one of the most rapidly expanding aspects of IIOT technology.
Monitoring in real time
Anyone in the production process can have access to data in real-time, which means anticipating and rapidly responding to changes or incidents that may impact production. Ultimately, this kind of real-time monitoring helps prevent down time and speeds up production.
Remote management
IIoT connected devices and digitally controlled machinery allow for fully remote operation of a production line. Many businesses choose a hybrid approach, in which some parts of the production line are automated and/or remotely controlled, with others operated by humans. Remote management has become more prevalent now that workforces are becoming less centralized.
Supply chain asset management and tracking
IIoT devices can help businesses understand how different parts of the supply chain are operating by tracking and monitoring how both raw materials and finished products move through the different production and transportation processes. This can not only help understand the overall state of production, but also glean insights into areas that could be optimized or costs that could be reduced.
For example, a complex supply chain may receive raw materials from numerous different vendors. A backup in just one of these deliveries can cause a bottleneck in production and cause expensive delays. By tracking how all materials are moving through the organization, management can quickly understand exactly where the issue is and make necessary adjustments to resolve it before causing larger delays.
Digital twins
Digital twins are computer-modeled simulations of a physical object or process. For example, a 3-D model of a building is a digital twin of the actual facility. While traditionally used to plan the structure and characteristics of a physical manufactured product, a digital twin can be used in conjunction with IoT systems to map out the digital representation of a production line to test and simulate changes to the manufacturing processes. Digital twins can also be used to mirror processes and model diagnostics.
For example, a business may want to understand the effect of changing the speed of a specific process. Using a digital twin and data from IIoT sensors, it could rather run a computer simulation to understand the impact of the speed change on the rest of the production line.
Building and operational systems
Manufacturing environments include a variety of operational technologies and devices, including HVAC, surveillance, access control, and energy systems. IIoT systems can be added to these to monitor their status and even adjust them remotely.
By doing so, these operational technologies can become intertwined with the broader supply chain and digital models. For instance, the climate systems may have an effect on the quality of the production process and therefore that data can be combined with the machinery data to run predictive maintenance and other types of models that may otherwise be difficult without the environmental context.
Collecting consumer insights
Manufacturers can use connected tools to gather data on consumer usage and track demand patterns. As a result, business managers remain agile and able to adjust the product to stay ahead of these trends. This increased responsiveness allows even large companies to be nimble and maximize customer satisfaction.
Challenges to IIoT in manufacturing
The merging of OT and IT technologies, as well as the increased accessibility of IoT devices present manufacturers with opportunities to minimize disruptions, streamline production, remotely access and monitor data, and ultimately drive revenue. But there are other considerations that manufacturers must take into account if they are to fully realize all the potential that OT, IT, and IoT offer.
Security & threat protection
According to Gartner, 75% of all OT security solutions will be provided by multifunction platforms that integrate with IT by 2025. With the exponential growth of connected devices in manufacturing facilities, these IIoT devices create an expanded attack surface. Threat prevention will become even more important as more OT devices interface with IT.
The threat of attacks has far reaching implications for manufacturers: in addition to disrupting production processes, attacks can also impact revenue and—in the worst-case scenario—compromise employee safety on the manufacturing floor. The security of these devices is critical to maximize uptime and optimize manufacturing processes, particularly as many remain in service for years and may become more vulnerable to attacks as they age.
Asset management
Manufacturers have an increasingly large inventory of assets to discover, evaluate, classify, and manage. The proliferation of IoT-accessible OT devices will only increase as the number of decision-makers in the supply chain expands, remote management of facilities and processes becomes more prevalent, and workforces become less centralized. Knowing exactly which assets are vulnerable is critical for providing adequate security measures and for maintaining production processes.
Operational resilience
According to a recent Gartner Risk Management Survey, one of the most common risk priority areas identified by respondents is the need for improved operational resilience for OT systems. That means understanding risks, anticipating potential disruptions, and planning for business continuity in the event of an incident, attack, or other breakdown in the production process. As the number of internet accessible OT devices increases, planning for operational resilience will become more complex.
Regulatory compliance
The patchwork of regulations governing OT/IT/IOT devices can be particularly challenging for manufacturers, and this problem will only continue as more and more devices and processes are integrated into the IIOT. Being able to map each device or component to the correct regulations plays a critical role in maintaining security and meeting regulatory requirements.
Secure all your connected devices
Manufacturing companies are embracing the convergence of IT and OT in hopes of capitalizing on the benefits brought by internet accessible OT devices. These benefits include more control over production processes, access to real-time data from remote locations, the ability to decentralize their workforce, and improved efficiencies that drive revenue growth.
As more OT devices become IoT-compatible, and as OT and IT security protocols continue to merge, manufacturers should have a plan for discovering and assessing all of their connected devices, including those used throughout their supply chains.
Most importantly, these devices must be evaluated and secured against the growing threat of security breaches. Ordr Systems Control Engine (SCE) can enable visibility and security of all your connected manufacturing devices. Try a demo of Ordr to learn how to keep your manufacturing devices—and the data they collect and share—safe and secure.
Interested in Learning More?
Subscribe today to stay informed and get regular updates from Ordr Cloud
Ready to Get Started?
-
PagesPrivacy Policy
…to: Provide access to the Ordr Solution to communicate with you Personalize, customize, measure, and improve Ordr’s products, services, content, and advertising Prevent, detect, and investigate potentially prohibited or illegal…
Privacy Policy
Last Updated: May 26th, 2022
The Ordr Privacy Policy was updated on May 26th, 2022.
Ordr, Inc. its affiliates and subsidiaries (collectively “Ordr,” “we”, “our” or “us”) knows you care about how your Personal Information is used and shared, and we take your privacy seriously. Please read the following to learn more about our Privacy Policy. By using or accessing Ordr’s Website or by using any of Ordr’s hosted products (the “Ordr Solution”) or through communicating with Ordr regarding its software (the “Ordr Software”) in any manner, you acknowledge that you accept the practices and policies outlined in this Privacy Policy, and you hereby consent that we may collect, use, and share your information in the following ways.
Changes to this Privacy Policy
Ordr may make changes to this Privacy Policy. The most current version of the Privacy Policy will govern Ordr’s use of information about you and will be located at https://www.ordr.net/privacy-policy. If Ordr makes material changes to this Privacy Policy, Ordr will notify you by posting a notice on our website and may send an email to the address Ordr has on file for your account, if applicable.
This Privacy Policy explains:
- Our privacy policy was updated on May 26, 2022
- Changes to this privacy policy
- The type of information we collect
- How Ordr collects your information; tracking and cookies
- How Ordr uses your information
- Correcting and updating your information
- Consent to commercial electronic messages
- Rights to object or restrict processing of Personal Information
- Right to be informed of appropriate safeguards where personal information is transferred to a third country or to an international organization
- Who we may share information with
- How we handle “Do Not Track” requests
- Linked sites and Ordr solution
- Data security
- Retention of your information
- Notice of privacy rights to California residents
- Notice of privacy rights to residents of the European Economic Area
- How to contact us
Type of Information we collect
Ordr may collect information that you provide to Ordr in connection with your use of the Ordr Solution or the Ordr Software when you:
- Register your account with Ordr as a user of the Ordr Software or the Ordr Solution (including through registration as an employee, contractor or other user of the Ordr Software or the Ordr Solution on behalf of a Ordr customer (“Customer”)
- Make changes to your user profile information
- Send email messages, forms, or other information to Ordr or other users using the Ordr Solution or the Ordr Software, or
- Install, use or otherwise interact with the Ordr Solution.
This information may include your first and last name, your address, email address, telephone number, your location, and any additional information you provide to Ordr during the account registration process or via the Ordr Solution.
Ordr may also collect certain technical information about your use of the Ordr Solution. This technical information may include technical information about your device(s), browser type and version, geo-location information, computer and connection information, statistics on page views, traffic to and from the Ordr Solution, ad data, Wi-Fi connection information, internet protocol (“IP”) address, and standard web log information.
Additionally, when expressing an interest in obtaining additional information about the Ordr Solution or the Ordr Software or registering to use the Ordr Solution or the Ordr Software, we or a Customer may require you to provide us with personal contact information, such as your name, company name, address, phone number, and email address (“Required Information”). Although Ordr uses third party service providers to process payments, when purchasing access to the Ordr Solution or the Ordr Software, we may require a Customer to provide our payment processing service providers with financial and billing information, such as billing name and address, credit card number, and the number of employees within the Customer that will be using the Ordr Solution or the Ordr Software (“Financial Information”). We may also ask an actual or prospective Customer to provide additional information, such as company annual revenues, number of employees, or industry (“Optional Information”). Required Contact Information, Billing Information, and Optional Information about Customers are referred to collectively as
“Customer Data.”How Ordr Collects Your Information; Tracking and Cookies
When you register for an account with Ordr either directly or through a Customer, we may ask you to provide us with certain information in order to create your account, and to provide you with our Ordr Solution or the Ordr Software. This information is collected by us when you fill out forms that may be provided to you through the Ordr Solution.
Ordr, and third parties we interact with, including our third-party service providers, may use cookies, web beacons, hashed identifiers derived from email addresses for the purposes of cross-device tracking for targeted advertising, local shared objects (sometimes called “flash cookies”), and similar technologies in connection with your use of the Ordr Solution to provide and support the Ordr Solution (collectively referred to in this policy as “Cookies”). Cookies are small data files that may have unique identifiers, and reside, among other places, on your mobile device, in emails we send to you, and on our applications. Locally shared objects or “flash cookies” are data files that can be created on your computer by the websites you visit and are a way for websites to store information for later use. Locally stored objects are different than cookies because they are stored in different parts of your computer than cookies. Web beacons are small strings of code that provide a method for delivering a graphic image on a web page or in an email message for the purpose of transferring data.
If Cookies are used, they may be used to collect information about you and your use of the Ordr Solution, such as your browser type, preferences, data relating to content that has been displayed to you or that you have clicked on, and the date and time of your use. Cookies may also be used in order to further features and processes on the Ordr Solution, provide authentication and security for your transactions using the Ordr Solution, store your preferences, facilitate relevant advertising, and help us learn more about how users engage with the Ordr Solution.
We sometimes use service providers to help us provide certain products and services or to integrate other features. These third-party providers may collect information when you view or use them, including information about you and your device or browser. They may do this using Cookies or similar technologies. These third-party providers also may use these technologies to help share information with us, like how you use their website or application. To learn more about the information they collect or receive, review their privacy policies.
As part of using our Ordr Solution, Ordr’s Customers may submit to Ordr electronic data or information (“Submitted Data”) that constitutes personal information of other individuals. Such data may include an individual’s name, email address, phone number or any other data that the Customer chooses to submit to us. Ordr generally has no direct relationship with the individuals to whom Submitted Data may pertain. Ordr processes Submitted Data on behalf of our Customers and any uses of Customer Data by Ordr are done so pursuant to our Terms and Conditions or a separate agreement in place between Ordr and the applicable Customer, which governs our treatment of
Submitted Data.How Ordr Uses Your Information
Ordr may use your information to:
- Provide access to the Ordr Solution to communicate with you
- Personalize, customize, measure, and improve Ordr’s products, services, content, and advertising
- Prevent, detect, and investigate potentially prohibited or illegal activities or a breach of the applicable agreement(s) between you and Ordr
- Analyze the accuracy, effectiveness, and usability of the Ordr Solution or the Ordr Software
- Generate and review reports and data about Ordr’s user base and Ordr Solution usage patterns
- Compile aggregate data for internal and external business purposes
- Resolve disputes and troubleshoot problems; and
- Contact you with information, including promotional, marketing, and advertising information and recommendations that Ordr believes may be of interest to you.
Consistent with applicable laws, including United States CAN-SPAM laws, if you do not wish to receive commercial emails, you may unsubscribe following the instructions on any email. We may still send you administrative notices, however.
We endeavor to protect the privacy of your account and other Personal Information we hold in our records, but unfortunately, we cannot guarantee complete security. Unauthorized entry or use, hardware or software failure, and other factors, may compromise the security of user information at any time. In particular, you acknowledge that Ordr is not responsible for any loss of any passwords or login information which you receive for access to the Ordr Solution which results from your failure to keep that information secure
Correcting and Updating Your Information
Customers may update or change their account information through their account settings accessible using the Customer account page included in the Ordr Solution. Access to your Ordr account page will require your Ordr Solution username and password. To update your Information or to delete your account information, please email notices@Ordr.net.
You can access or change your profile and contact information or delete your account through the Ordr settings page. If you choose to delete or deactivate your account, you can no longer retrieve content or reactivate your account.
You have the right to request access to any Personal Information which Ordr may have about you by contacting notices@Ordr.com. The information will be provided in a machine-readable format. You may also ask that we transfer the Personal Information to a third party, which we will do if technically feasible.
You also have the right to review, add and update your Personal Information. You may also request the deletion of your Personal Information where
- the personal information is no longer necessary in relation to the purposes for which it was collected or otherwise processed,
- you withdraw consent to Ordr’s possession of the information on which the processing is based and where there is no other legal ground for Ordr’s retention of the information,
- you object to Ordr’s possession of the information and there is no overriding legitimate basis for the retention,
- the personal information has been unlawfully obtained or processed, or
- the personal information has to be erased for compliance with a legal obligation in the European Union or other law to which Ordr is subject.
When you update information, however, we may maintain a copy of the unrevised information in our records. Some information may remain in our records after your deletion of such information from your account. We may use any aggregated data derived from or incorporating your Personal Information after you update or delete it, but not in a manner that would identify you personally.
If your individual personal information has been submitted to us by a Customer as Submitted Data and you wish to exercise any rights you may have to access, correct, amend, or delete such data, please first inquire with the Customer (or his/her organization) directly
Consent to Commercial Electronic Messages
If you provide us with an email address, you expressly consent to receiving Commercial Electronic Messages from Ordr about your use of the Website, the Ordr Solution, the Ordr Software and our Products. If you have any questions about Ordr’s Commercial Electronic Messages, you can contact Ordr at:
Ordr, Inc.
2445 Augustine Dr.
#601
Santa Clara, CA 95054
Attention: Privacy Officer or by emailing notices@ordr.netIn addition, you may opt out of receiving Commercial Electronic Messages at any time by emailing notices@ordr.net.
Rights to Object or Restrict Processing of Personal Information
If Ordr has your Personal Information as a result of your relationship with one of Ordr’s Customers, you should first contact that Customer before contacting Ordr. You may, however, at any time revoke your consent to the collection, processing and use of your Personal Information by emailing notices@Ordr.net. Upon receipt of your request, Ordr will delete your personal data provided Ordr may retain any data which is required for billing and accounting purposes or which is subject to legal retention requirements. In addition, if you discover any errors in data, you may contact us by emailing notices@Ordr.net and we will correct it. You can always opt not to disclose information to us, but keep in mind some information may be needed to take advantage of product features or may be required by your relationship with one of Ordr’s customers.
Right to be informed of appropriate safeguards where Personal Information is Transferred to a Third Country or to an International Organization
Ordr enters into agreements with its customers regarding the safeguards that have been put in place to protect your Personal Information for transfer outside of Switzerland or the European Economic Area. For transfers to countries without an adequacy decision by Switzerland or the European Commission, Ordr puts appropriate safeguards through contractual obligations..
Who We May Share Information With
Ordr may disclose the information we collect from you to the following third parties:
Users of the Ordr Solution; Public Information.
When you share information with us via the Ordr Solution, Ordr may share your information to other users, in accordance with the privacy settings you or the respective Customer has chosen for your account or that are applicable to that information. To the extent you share any information to a public audience or via a publicly accessible portion of the Ordr Solution such as an online customer community or forum, that information may be available to anyone who has access to that customer community or forum..Ordr’s solution Providers.
Ordr may share your information with third-party contractors, agents, collaborators, or service providers who provide certain services to Ordr or on Ordr’s behalf, such as operating and supporting the Ordr Solution. Ordr may also request your information from a previous service provider, which we need to provide our services to you. Alternatively, Ordr may pass on your information to a service provider that Ordr Customers have chosen to
replace Ordr.Companies that Acquire Ordr’s Business or Assets.
If Ordr becomes involved in a merger, acquisition, sale of assets, securities offering, bankruptcy, reorganization, or dissolution or if the ownership of all or substantially all of Ordr’s business relating to the Ordr Solution otherwise changes, Ordr may provide your information to a third party or parties in connection with the applicable transaction.Ordr’s Affiliates.
Ordr may share some or all of your information with Ordr’s parent company, subsidiaries and corporate affiliates, joint ventures or other companies under common control with Ordr.Ordr Customers.
If Ordr has received your information as part of Submitted Data, Ordr may share that information, or any modifications or revisions to that information with that Customer.Switching Ordr Solution Providers.
Ordr may request your information from your previous service provider, which we need to provide our services to you. Alternatively, Ordr may pass on your information to a service provider that you have chosen to replace Ordr.Aggregate Information.
Ordr may share information relating to our visitors and users with affiliated or unaffiliated third parties on an aggregate basis, however this information will not identify you personally.Legal Requirements.
Ordr may share your information with law enforcement, governmental agencies, or authorized third parties, in response to a request relating to a criminal investigation or alleged illegal activity or any other activity that may expose Ordr, you, or any other Ordr user to legal liability, or to protect Ordr’s rights or property, or during emergencies when safety is at risk. Ordr may also share your information in response to court orders, subpoenas, or other legal or regulatory requests, and Ordr may provide access to your information to Ordr’s legal counsel and other consultants in connection with actual or potential litigation. Ordr shall remain liable under the Principles if its agent processes such personal information in a manner inconsistent with the Principles, unless Ordr proves that it is not responsible for the event giving rise to the damage.How We Handle “Do Not Track” Requests
You may be able to adjust your browser settings or other settings so that “do not track” requests are sent to our websites and mobile applications. Ordr does not use any tracking technology that would respond to any “do not track” requests that are sent to our services. Ordr does not collect personally identifiable information about your online activities over time and across different websites when you use the Ordr Solution; however, certain service providers that use Cookies may collect your personally identifiable information over time and across
different websites.Linked Sites and Ordr Solution
Ordr’s website or application may, from time to time, contain links to and from the websites of our partner networks, advertisers and affiliates. If you follow a link to any of these websites, please note that these websites have their own privacy policies and that we do not accept any responsibility or liability for these policies. Please check these policies before you submit any personal data to these websites.
Data Security
Ordr takes reasonable measures to protect the information you provide to Ordr or submit through the Ordr Solution against misuse, loss, theft, unauthorized use, disclosure, or modification. Unfortunately, the transmission of information via the internet is not completely secure. Although we will do our best to protect your personal data, we cannot guarantee the security of your data transmitted to our site; any transmission is at your own risk and your information may be disclosed to third parties in unforeseeable situations or situations that are not preventable even when commercially reasonably protections are employed, such as in the case that Ordr or if the Ordr Solution are subject to a hacking or other attack. Once we have received your information, we will use strict procedures and security features to try to prevent unauthorized access.
Retention of Your Information
We retain information about you only for as long as it is necessary and relevant for Ordr’s operations, and for Ordr’s customers to work with their consumers. Information about you that is no longer necessary and relevant for Ordr’s operations will be disposed of securely. Ordr may also retain information collected from you to comply with the law, prevent fraud, resolve disputes, troubleshoot problems, assist with any investigation, and take other actions permitted by law or disclosed in this Privacy Policy.
Notice of Privacy Rights to California Residents
TThe California Consumer Privacy Act requires businesses to disclose whether they sell Personal Data. As a business covered by the CCPA, we do not sell Personal Data. We may share Personal Data with third parties or allow them to collect Personal Data from our sites or Services if those third parties are authorized service providers or business partners who have agreed to our contractual limitations as to their retention, use, and disclosure of such Personal Data, or if you use Ordr sites or Services to interact with third parties or direct us to disclose your Personal Data to third parties.
California law requires that we detail the categories of Personal Data that we disclose for certain “business purposes,” such as to service providers that assist us with securing our services or marketing our products, and to such other entities as described in Sections 8 and 10 of this Privacy Statement. We disclose the following categories of Personal Data for our business purposes:
Identifiers;
Commercial information;
Internet activity information;
Financial information; and
Inferences drawn from any of the above information categories.
California law grants state residents certain rights, including the rights to access specific types of Personal Data, to learn how we process Personal Data, to request deletion of Personal Data, and not to be denied goods or services for exercising these rights.
If you are a California resident under the age of 18, you may ask us to remove content or information that you have posted to our website(s). Please note that your request does not ensure complete or comprehensive removal of the content or information, because, for example, some of your content may have been reposted by another user.
For information on how to exercise your rights, please refer to Section 15 of this Privacy Statement. If you are an authorized agent wishing to exercise rights on behalf of a California resident, please contact us using the information in the “Contacting Us” section above and provide us with a copy of the consumer’s written authorization designating you as their agent.
We may need to verify your identity and place of residence before completing your rights request.
Notice of Privacy Rights to Residents of the European Economic Area
You have the right to ask us not to process your personal data for marketing purposes. We will usually inform you (before collecting your data) if we intend to use your data for such purposes or if we intend to disclose your information to any third party for such purposes. You can exercise your right to prevent such processing by checking certain boxes on the forms we use to collect your data. You can also exercise the right at any time by contacting us at notices@Ordr.net.
How to Contact Us
If you have questions or complaints regarding Ordr’s Privacy Policy or practices, please contact notices@Ordr.net or via postal mail at
Ordr, Inc.
2445 Augustine Dr.
#601
Santa Clara, CA 95054
Attention: Privacy Officer -
PagesIntegrations
…inventory, identifies and prioritizes asset risk, and tracks and risk-rates asset communications patterns. Ordr transmits this critical security context to Fortinet FortiGate, FortiManager, and FortiNAC, allowing administrators to create and…
- PLATFORM
- INTEGRATIONS
Enable Faster ROI With Ordr Integrations
Ordr integrates with 180+ security, networking, infrastructure, IT, and clinical solutions to unify device details, enrich device context, and extend the value of your existing investments.
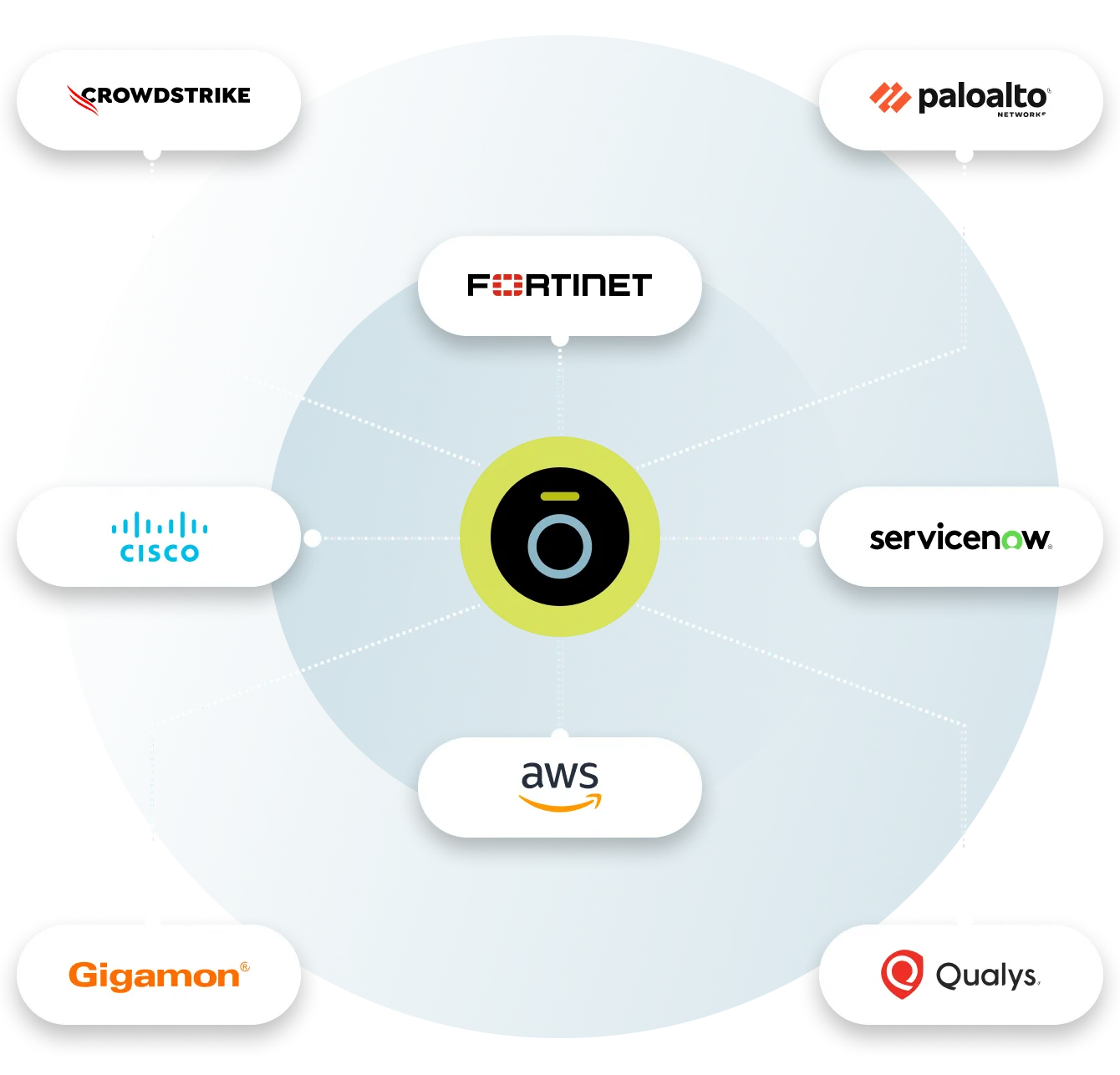
Aruba
With Ordr and HPE Aruba ClearPass Policy Manager (CPPM), organizations can quickly gain complete visibility into every connected device and deploy segmentation to proactively protect and reactively respond and mitigate threats. This includes Zero Trust policy enforcement and microsegmentation to isolate groups or individual devices from non-essential access while protecting them from attack and compromise on existing networking and security infrastructure
How it works
The integrated Ordr SCE and HPE Aruba CPPM solution makes it easy to get rich visibility for IoT and unmanaged devices and to simplify segmentation projects. The solution provides detailed classification and context for every connected device, automatically groups devices into CPPM policy groups for role-based access and facilitates software-defined segmentation to provide more precise controls for every IoT device in the network. By providing continuous, multi-level security monitoring of all device communications, Ordr SCE detects anomalous behavior and shares this information with ClearPass to implement network access control based on vulnerability, threat, and risk ratings. Ordr SCE also integrates with HPE Aruba CPPM to streamline the process of containing threats based on the organization’s access policy such as blocking unauthorized devices, quarantining them, or limiting their network access.
Benefits
- Automating IoT inventory discovery, classification, and categorization, and sharing detailed device context with ClearPass
- Providing rich analytics about the behavior of all devices that guides segmentation design, streamlines the segmentation implementation, and audits the result to assure accuracy and effectiveness
- Quickly contain threats and protect at-risk devices
- Accelerating ClearPass deployments with powerful yet easy-to-use tools that provide accurate device information and automate steps that are traditionally error-prone and labor intensive
CrowdStrike
Integration between Ordr and CrowdStrike ensures the security of all managed and unmanaged devices with comprehensive device visibility, detailed vulnerability insights, an understanding of risk, and the ability to enforce policy to mitigate active threats and improve security across all connected devices
How it works
Ordr analyzes network flow data to automatically discover and classify every connected device, profile behavior, and identify active threats. Security telemetry from the CrowdStrike Falcon platform, is shared with Ordr to enhance device insights, and provide a centralized, deep understanding of each device and its associated risk. Ordr uses multiple factors to calculate risk for each device based on business context, asset criticality, vulnerabilities, and overall threat details. With additional device data from the Falcon platform, Ordr provides a highly accurate risk score for each device. By continuously synchronizing device risk scores with CrowdStrike’s enriched security data, Ordr enables teams with an up-to-date view of risk to help them focus on the most critical devices.
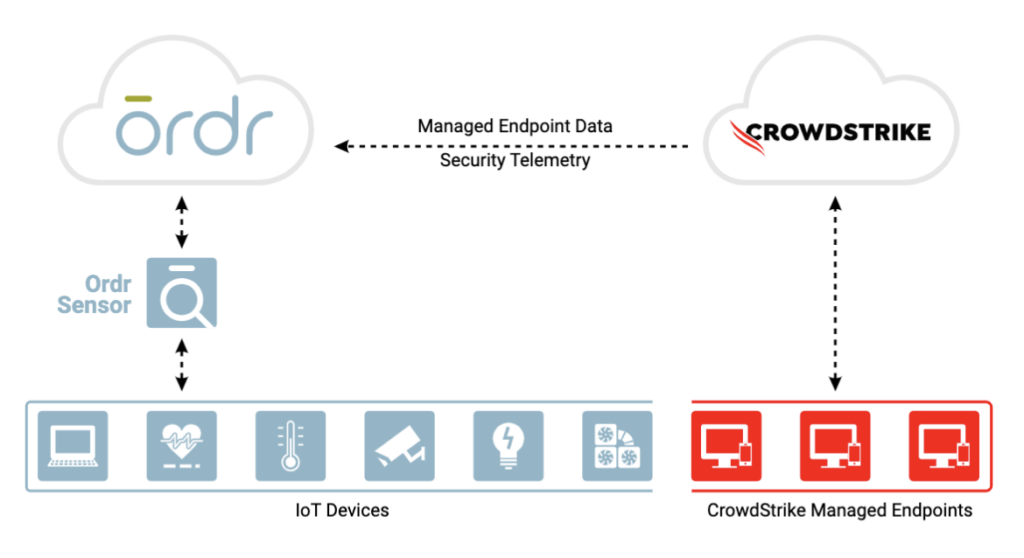
Benefits
Gain complete device visibility
- See into all devices – agentless and agent-based
- Track both online and offline devices continuously
- Identify unmanaged devices without CrowdStrike agent for compliance
Minimize risk with better insights
- Improve Ordr risk score accuracy with supplemental event data from CrowdStrike
Remediate faster
- Improve threat detection and incident response time with a combination of Ordr endpoint flow & CrowdStrike process data
- Block/quarantine/segment managed endpoints in Ordr for rapid remediation via the network
Fortinet
Fortinet and Ordr have partnered to deliver an industry-leading IoT and unmanaged device security solution by integrating FortiManager, FortiGate and FortiNAC with Ordr Systems Control Engine (SCE)
How it works
Automated Visibility and Security of All Connected Devices
Ordr SCE automatically creates a complete asset inventory, identifies and prioritizes asset risk, and tracks and risk-rates asset communications patterns. Ordr transmits this critical security context to Fortinet FortiGate, FortiManager, and FortiNAC, allowing administrators to create and apply firewall and NAC policies using business-relevant groups, classifications, and device names, while understanding the full risk profile and impact of each change. Ordr further reduces administrative costs by automatically updating asset groupings as devices join and leave the network, as well as by creating and transmitting security policies directly to FortiGate and FortiManager for enforcement.
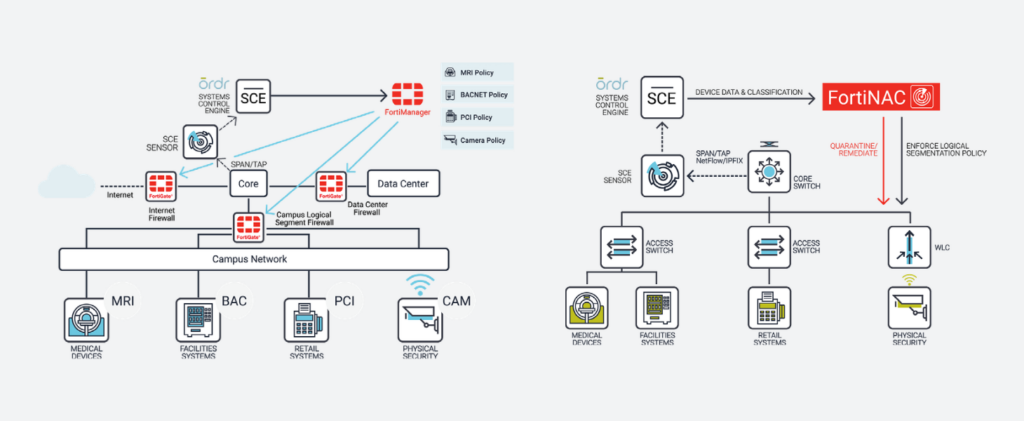
Benefits
With the integration, joint customers can now:
- Discover and inventory every connected network asset, including the massive volume of IoT and unmanaged devices, and make available across the Fortinet Security Fabric, from endpoint to edge, through FortiNAC, FortiManager, and FortiGate
- Establish comprehensive security controls that restrict IoT devices to known-good network behaviors
- Manage firewall and NAC policies using business-relevant context such as device type, manufacturer, location, risk, and function rather than IP addresses
- Automate updates of firewall groups and address info to ensure consistent policy enforcement regardless of device location, VLAN, or IP assignment, thus drastically reducing operational costs and downtime
- Protect critical devices with automated, zone-based segmentation and microsegmentation within zones
SentinelOne
Ordr integration with SentinelOne enables collection of managed device data, vulnerabilities and threat insights for comprehensive device visibility and a better understanding of risk.
How It Works
Ordr discovers and secures every connected device—from traditional IT to new or vulnerable IoT, IoMT, and OT devices. With the SentinelOne integration, Ordr collects managed device data, vulnerabilities, and threat insights from the Singularity Platform delivering comprehensive device visibility, a better understanding of risk, and the ability to enforce policy to mitigate active threats and improve security across all connected devices.
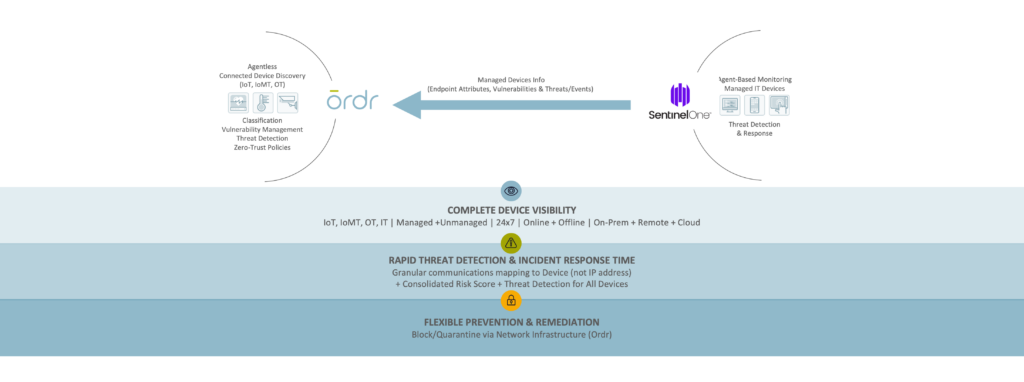
Benefits
Gain Complete Device Visibility
- See granular details for all agentless and agent-based devices.
- Track both online and offline devices continuously.
- Identify unmanaged devices without the SentinelOne agent to meet compliance requirements.
Minimize Risk with Extended Insights
- Improve risk score accuracy with supplemental event data from SentinelOne.
Remediate Faster
- Improve threat detection and incident response with combined Ordr endpoint flow and SentinelOne process data.
- Block/quarantine/segment managed endpoints in Ordr for rapid remediation via the network.
Gigamon
A basic tenet of network security and regulatory compliance is that “You cannot secure what you cannot see.” Gigamon and Ordr have teamed to deliver unsurpassed visibility and control into every thing connected to your network.
How It Works
The Gigamon Visibility and Analytics Fabric (VAF) optimizes data collection of all north-south and east-west traffic across branch, campus, data center and cloud. Collected data is delivered to Ordr for analysis to ensure comprehensive device classification and visibility into all device communications. Integration with Gigamon VAF also eliminates concerns of SPAN security and potential impact to network infrastructure with “yet another SPAN port or session.”
By integrating with Gigamon VAF, customers can significantly reduce the number of Ordr sensors required to comprehensively discover and monitor every network-connected device, simplifying your network and security monitoring architecture.
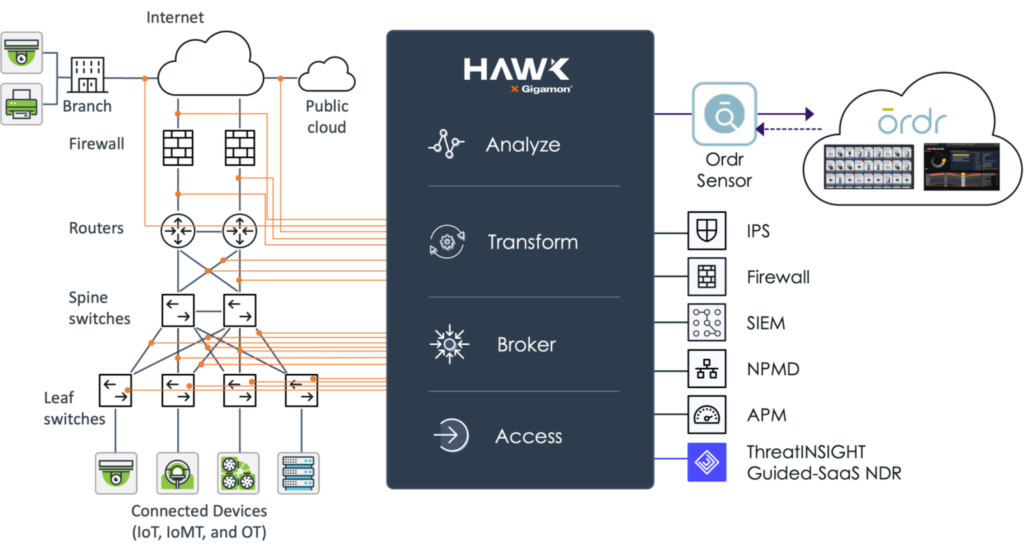
Benefits
- Real-time asset inventory – Ordr continuously analyzes device traffic sent from Gigamon to passively discover an automatically classify every device connected to the network to help you maintain an up-to-date and accurate inventory.
- Connected device risk – using the traffic captured and optimized by Gigamon Hawk, Ordr calculates device risk scores and uncovers connected devices with risk such as outdated operating systems, unpatched software, weak passwords, and manufacturer recalls. Ordr also maps and baselines device communications to identify risk and stop attacks.
- Accelerate Zero Trust – working together, Gigamon and Ordr can map and baseline all IT, IoT and other device communications. Ordr can then dynamically create Zero Trust policies to simplify and accelerate NAC and segmentation projects. These policies can be enforced with popular security and network devices to integrate with existing infrastructure tools.
Palo Alto Networks
Rapid7
Ordr works with Rapid7 to seamlessly discover all connected assets including IoT, IoMT, and OT devices. The joint solution enables Rapid7 to perform the right scan at the right time regardless of the device type, location, criticality or role within the organization. Many vulnerable IoT/OT devices discovered by Rapid7 cannot be patched or updated. Ordr automates the application of compensating controls to safeguard these devices by sending protection policies directly to firewalls, switches, wireless, or NAC systems. Similarly, infected devices can be quickly isolated through existing network and security devices.
How It Works
The integration with Ordr and Rapid7 InsightVM provide ongoing bi-directional synchronization for managing vulnerabilities with rich device context. Ordr discovers every connected device, profiles device behaviors and risks, and automates remediation responses. Rapid7 InsightVM provides visibility into the vulnerabilities and clarity on how those vulnerabilities translate into business risk. Combining Ordr’s unique device intelligence with Rapid7’s advanced vulnerability intelligence provides organizations with the ultimate solution to efficiently manage risks while reducing service disruption and time to remediate.
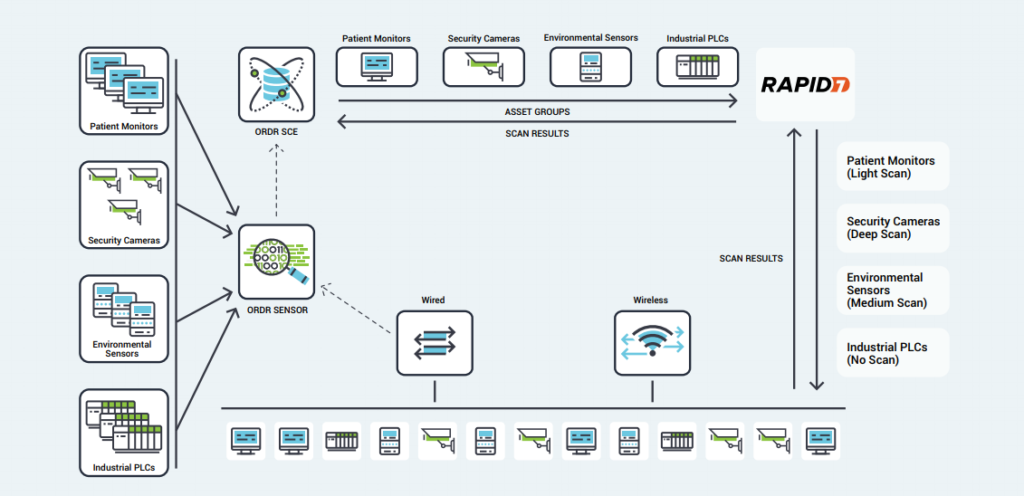
Benefits
- Comprehensive Coverage – Ordr’s identification and classification of lightweight, agentless devices allows administrators to quickly exclude specific IoT devices or categories from active Rapid7 scans, opening network segments to vulnerability scanning that had previously been excluded.
- Optimized Scanning – Using Ordr’s detailed insight into device types, scan sensitivity, and their critical role within the organization, Rapid7 scans can be tailored to each device.
- Proactive Protection – Rather than blocking or quarantining critical IoT devices after infection, Ordr’s segmentation policies create barriers that protect vulnerable devices while still enabling essential services.
- Smart Scheduling – Ordr tracks utilization patterns for critical devices, allowing administrators to schedule vulnerability scans for times when devices are not in use, minimizing disruption and operational risk.
Splunk
Ordr integration with Splunk allows you to leverage Ordr’s rich device data to create alerts, reports, and custom analyses. Ordr transmits security alerts, device information, and other critical information. Splunk ingests the feed for better event management.
VMware
Ordr leverages the vSphere API, which provides access to server management, virtual machine provisioning, monitoring, and more. Ordr collects datacenter asset details including the servers (hosts), individual virtual machines (guests), operating systems, shared compute resources (CPU, memory, disk), status, and compatibility.
The extended visibility to VMware workloads running in public, private, and hybrid cloud environments delivers a ‘whole hospital’ or ‘whole enterprise’ approach to security ensuring that no device or connection remains unknown.
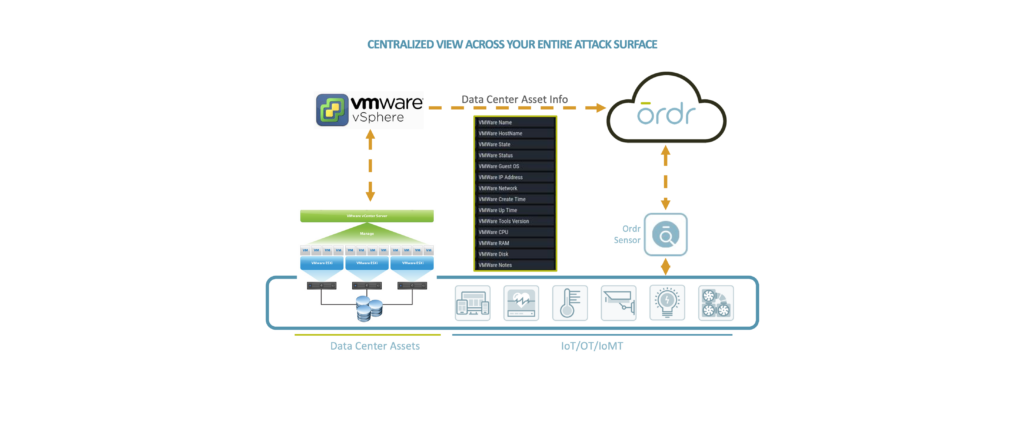
Microsoft
Ordr integrates with multiple Microsoft solutions to enhance device context and improve risk insights to keep your organization secure.
Ready to Get Started?
-
PagesTechnology
…complete asset inventory, identifies and prioritizes asset risk, and tracks and risk-rates asset communications patterns. Ordr transmits this critical security context to Fortinet FortiGate, FortiManager, and FortiNAC, allowing administrators to…
- PARTNERS
- TECHNOLOGY
Enable Faster ROI With Ordr Technology Integration Partners
Ordr integrates with 180+ security, networking, infrastructure, IT, and clinical solutions to unify device details, enrich device context, and extend the value of your existing investments.
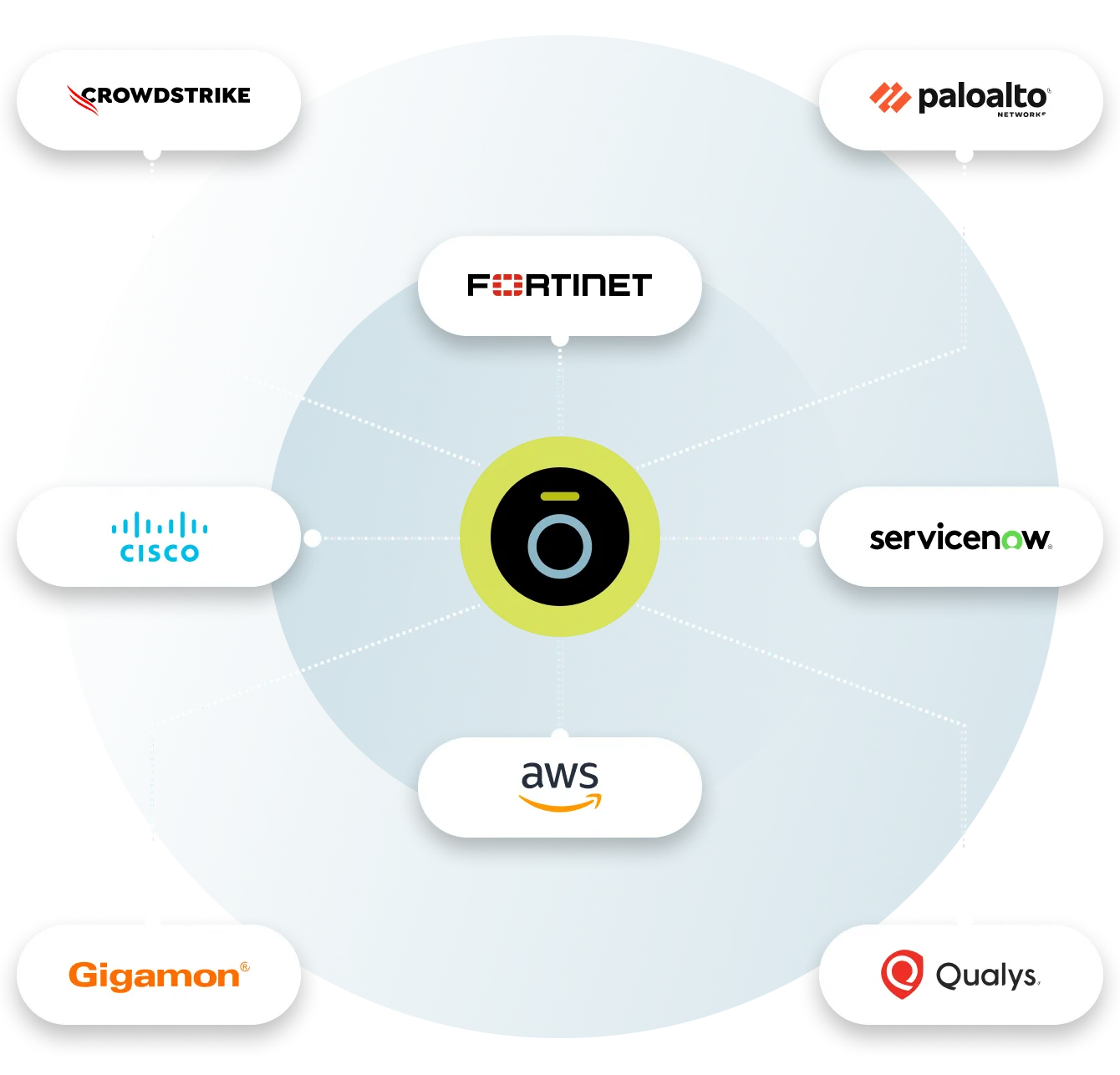
Aruba
With Ordr and HPE Aruba ClearPass Policy Manager (CPPM), organizations can quickly gain complete visibility into every connected device and deploy segmentation to proactively protect and reactively respond and mitigate threats. This includes Zero Trust policy enforcement and microsegmentation to isolate groups or individual devices from non-essential access while protecting them from attack and compromise on existing networking and security infrastructure
How it works
The integrated Ordr SCE and HPE Aruba CPPM solution makes it easy to get rich visibility for IoT and unmanaged devices and to simplify segmentation projects. The solution provides detailed classification and context for every connected device, automatically groups devices into CPPM policy groups for role-based access and facilitates software-defined segmentation to provide more precise controls for every IoT device in the network. By providing continuous, multi-level security monitoring of all device communications, Ordr SCE detects anomalous behavior and shares this information with ClearPass to implement network access control based on vulnerability, threat, and risk ratings. Ordr SCE also integrates with HPE Aruba CPPM to streamline the process of containing threats based on the organization’s access policy such as blocking unauthorized devices, quarantining them, or limiting their network access.
Benefits
- Automating IoT inventory discovery, classification, and categorization, and sharing detailed device context with ClearPass
- Providing rich analytics about the behavior of all devices that guides segmentation design, streamlines the segmentation implementation, and audits the result to assure accuracy and effectiveness
- Quickly contain threats and protect at-risk devices
- Accelerating ClearPass deployments with powerful yet easy-to-use tools that provide accurate device information and automate steps that are traditionally error-prone and labor intensive
CrowdStrike
Integration between Ordr and CrowdStrike ensures the security of all managed and unmanaged devices with comprehensive device visibility, detailed vulnerability insights, an understanding of risk, and the ability to enforce policy to mitigate active threats and improve security across all connected devices
How it works
Ordr analyzes network flow data to automatically discover and classify every connected device, profile behavior, and identify active threats. Security telemetry from the CrowdStrike Falcon platform, is shared with Ordr to enhance device insights, and provide a centralized, deep understanding of each device and its associated risk. Ordr uses multiple factors to calculate risk for each device based on business context, asset criticality, vulnerabilities, and overall threat details. With additional device data from the Falcon platform, Ordr provides a highly accurate risk score for each device. By continuously synchronizing device risk scores with CrowdStrike’s enriched security data, Ordr enables teams with an up-to-date view of risk to help them focus on the most critical devices.
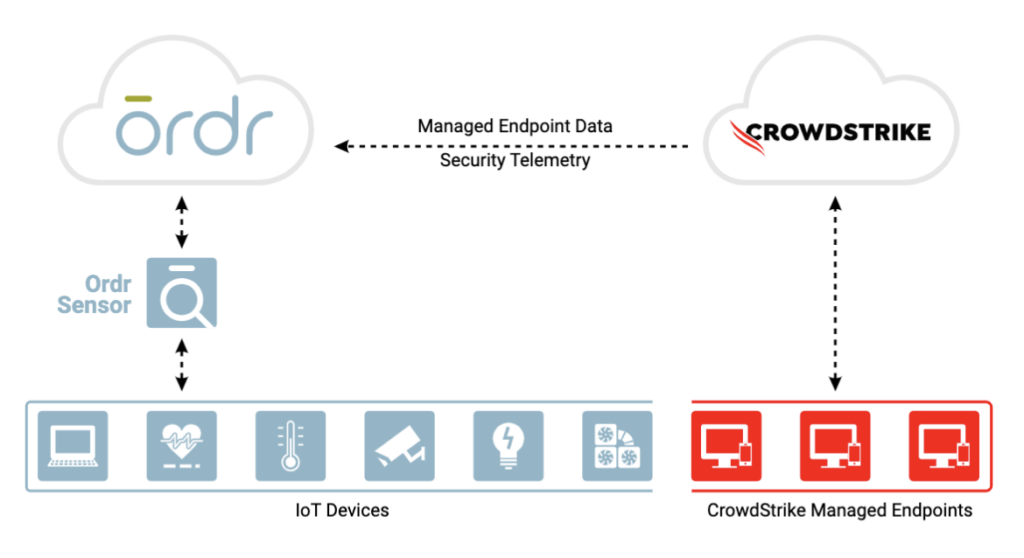
Benefits
Gain complete device visibility
- See into all devices – agentless and agent-based
- Track both online and offline devices continuously
- Identify unmanaged devices without CrowdStrike agent for compliance
Minimize risk with better insights
- Improve Ordr risk score accuracy with supplemental event data from CrowdStrike
Remediate faster
- Improve threat detection and incident response time with a combination of Ordr endpoint flow & CrowdStrike process data
- Block/quarantine/segment managed endpoints in Ordr for rapid remediation via the network
Fortinet
Fortinet and Ordr have partnered to deliver an industry-leading IoT and unmanaged device security solution by integrating FortiManager, FortiGate and FortiNAC with Ordr Systems Control Engine (SCE)
How it works
Automated Visibility and Security of All Connected Devices
Ordr SCE automatically creates a complete asset inventory, identifies and prioritizes asset risk, and tracks and risk-rates asset communications patterns. Ordr transmits this critical security context to Fortinet FortiGate, FortiManager, and FortiNAC, allowing administrators to create and apply firewall and NAC policies using business-relevant groups, classifications, and device names, while understanding the full risk profile and impact of each change. Ordr further reduces administrative costs by automatically updating asset groupings as devices join and leave the network, as well as by creating and transmitting security policies directly to FortiGate and FortiManager for enforcement.
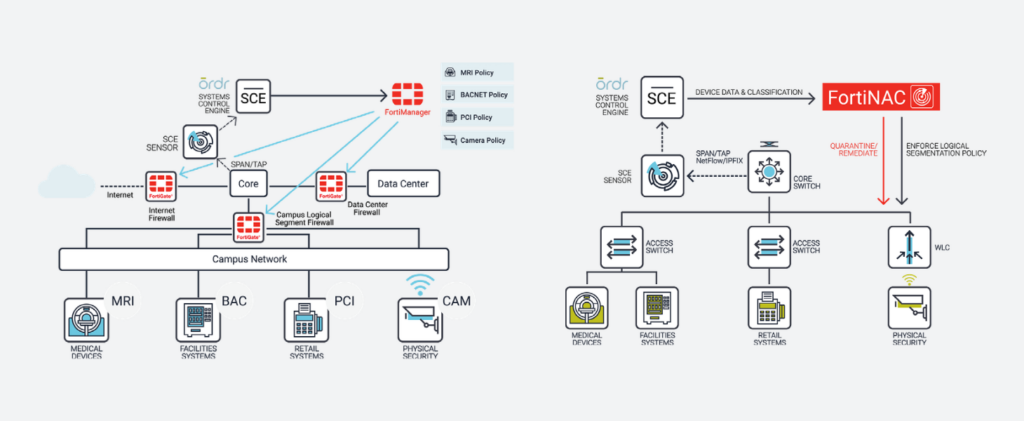
Benefits
With the integration, joint customers can now:
- Discover and inventory every connected network asset, including the massive volume of IoT and unmanaged devices, and make available across the Fortinet Security Fabric, from endpoint to edge, through FortiNAC, FortiManager, and FortiGate
- Establish comprehensive security controls that restrict IoT devices to known-good network behaviors
- Manage firewall and NAC policies using business-relevant context such as device type, manufacturer, location, risk, and function rather than IP addresses
- Automate updates of firewall groups and address info to ensure consistent policy enforcement regardless of device location, VLAN, or IP assignment, thus drastically reducing operational costs and downtime
- Protect critical devices with automated, zone-based segmentation and microsegmentation within zones
SentinelOne
Ordr integration with SentinelOne enables collection of managed device data, vulnerabilities and threat insights for comprehensive device visibility and a better understanding of risk.
How It Works
Ordr discovers and secures every connected device—from traditional IT to new or vulnerable IoT, IoMT, and OT devices. With the SentinelOne integration, Ordr collects managed device data, vulnerabilities, and threat insights from the Singularity Platform delivering comprehensive device visibility, a better understanding of risk, and the ability to enforce policy to mitigate active threats and improve security across all connected devices.
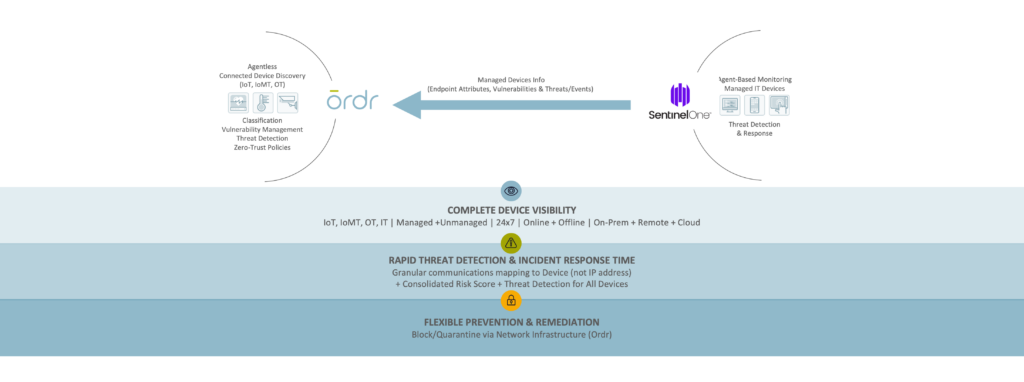
Benefits
Gain Complete Device Visibility
- See granular details for all agentless and agent-based devices.
- Track both online and offline devices continuously.
- Identify unmanaged devices without the SentinelOne agent to meet compliance requirements.
Minimize Risk with Extended Insights
- Improve risk score accuracy with supplemental event data from SentinelOne.
Remediate Faster
- Improve threat detection and incident response with combined Ordr endpoint flow and SentinelOne process data.
- Block/quarantine/segment managed endpoints in Ordr for rapid remediation via the network.
Gigamon
A basic tenet of network security and regulatory compliance is that “You cannot secure what you cannot see.” Gigamon and Ordr have teamed to deliver unsurpassed visibility and control into every thing connected to your network.
How It Works
The Gigamon Visibility and Analytics Fabric (VAF) optimizes data collection of all north-south and east-west traffic across branch, campus, data center and cloud. Collected data is delivered to Ordr for analysis to ensure comprehensive device classification and visibility into all device communications. Integration with Gigamon VAF also eliminates concerns of SPAN security and potential impact to network infrastructure with “yet another SPAN port or session.”
By integrating with Gigamon VAF, customers can significantly reduce the number of Ordr sensors required to comprehensively discover and monitor every network-connected device, simplifying your network and security monitoring architecture.
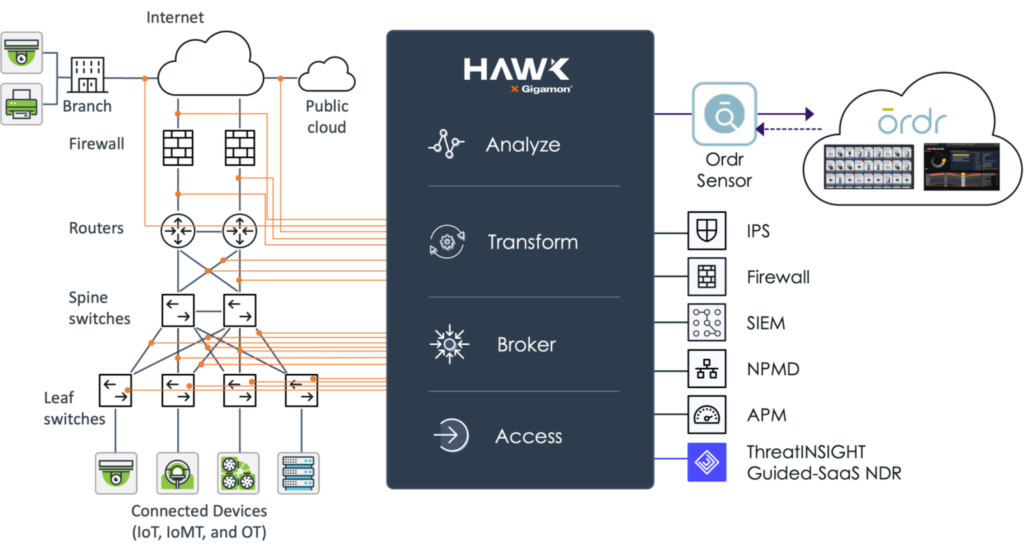
Benefits
- Real-time asset inventory – Ordr continuously analyzes device traffic sent from Gigamon to passively discover an automatically classify every device connected to the network to help you maintain an up-to-date and accurate inventory.
- Connected device risk – using the traffic captured and optimized by Gigamon Hawk, Ordr calculates device risk scores and uncovers connected devices with risk such as outdated operating systems, unpatched software, weak passwords, and manufacturer recalls. Ordr also maps and baselines device communications to identify risk and stop attacks.
- Accelerate Zero Trust – working together, Gigamon and Ordr can map and baseline all IT, IoT and other device communications. Ordr can then dynamically create Zero Trust policies to simplify and accelerate NAC and segmentation projects. These policies can be enforced with popular security and network devices to integrate with existing infrastructure tools.
Palo Alto Networks
Rapid7
Ordr works with Rapid7 to seamlessly discover all connected assets including IoT, IoMT, and OT devices. The joint solution enables Rapid7 to perform the right scan at the right time regardless of the device type, location, criticality or role within the organization. Many vulnerable IoT/OT devices discovered by Rapid7 cannot be patched or updated. Ordr automates the application of compensating controls to safeguard these devices by sending protection policies directly to firewalls, switches, wireless, or NAC systems. Similarly, infected devices can be quickly isolated through existing network and security devices.
How It Works
The integration with Ordr and Rapid7 InsightVM provide ongoing bi-directional synchronization for managing vulnerabilities with rich device context. Ordr discovers every connected device, profiles device behaviors and risks, and automates remediation responses. Rapid7 InsightVM provides visibility into the vulnerabilities and clarity on how those vulnerabilities translate into business risk. Combining Ordr’s unique device intelligence with Rapid7’s advanced vulnerability intelligence provides organizations with the ultimate solution to efficiently manage risks while reducing service disruption and time to remediate.
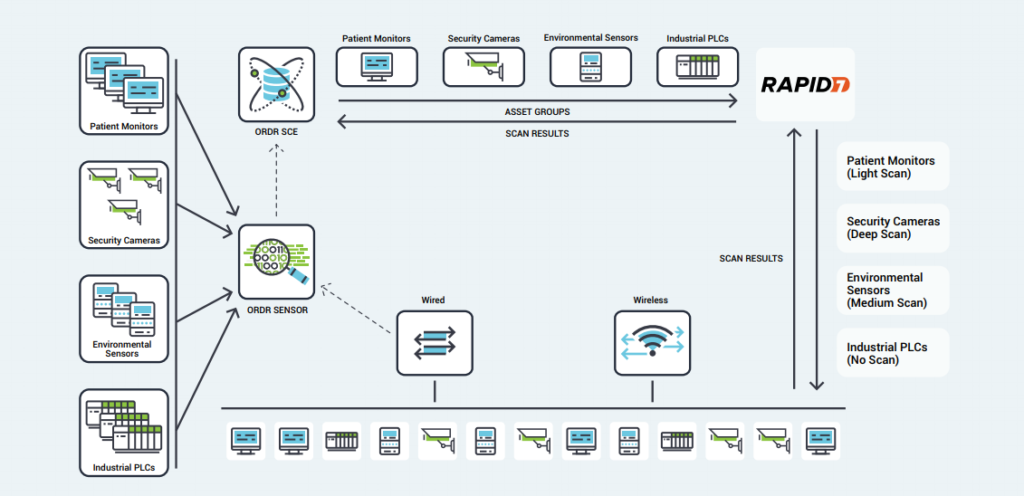
Benefits
- Comprehensive Coverage – Ordr’s identification and classification of lightweight, agentless devices allows administrators to quickly exclude specific IoT devices or categories from active Rapid7 scans, opening network segments to vulnerability scanning that had previously been excluded.
- Optimized Scanning – Using Ordr’s detailed insight into device types, scan sensitivity, and their critical role within the organization, Rapid7 scans can be tailored to each device.
- Proactive Protection – Rather than blocking or quarantining critical IoT devices after infection, Ordr’s segmentation policies create barriers that protect vulnerable devices while still enabling essential services.
- Smart Scheduling – Ordr tracks utilization patterns for critical devices, allowing administrators to schedule vulnerability scans for times when devices are not in use, minimizing disruption and operational risk.
Splunk
Ordr integration with Splunk allows you to leverage Ordr’s rich device data to create alerts, reports, and custom analyses. Ordr transmits security alerts, device information, and other critical information. Splunk ingests the feed for better event management.
VMware
Ordr leverages the vSphere API, which provides access to server management, virtual machine provisioning, monitoring, and more. Ordr collects datacenter asset details including the servers (hosts), individual virtual machines (guests), operating systems, shared compute resources (CPU, memory, disk), status, and compatibility.
The extended visibility to VMware workloads running in public, private, and hybrid cloud environments delivers a ‘whole hospital’ or ‘whole enterprise’ approach to security ensuring that no device or connection remains unknown.
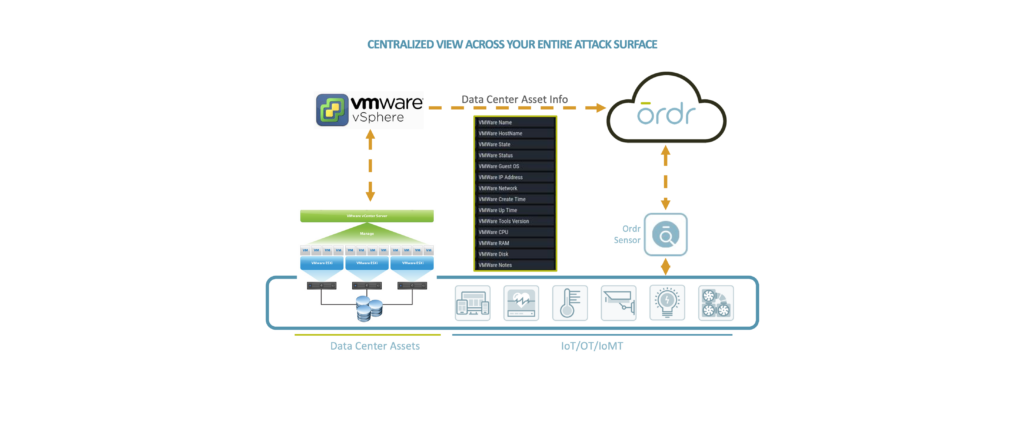
Microsoft
Ordr integrates with multiple Microsoft solutions to enhance device context and improve risk insights to keep your organization secure.
Ready to Get Started?