Search Results:
”Quiz 2024 SAP C-ARSOR-2308: Marvelous SAP Certified Application Associate - SAP Ariba Sourcing Valid Dumps Book 🐮 Open ▷ www.pdfvce.com ◁ and search for ➥ C-ARSOR-2308 🡄 to download exam materials for free 🏑C-ARSOR-2308 Customizable Exam Mode”
-
 BlogNot All CAASMs Are Created Equal: How Ordr Is Different
BlogNot All CAASMs Are Created Equal: How Ordr Is Different…access and permissions, and what they are accessing. These insights provide CISOs and security teams with the confidence to maintain compliance, by delivering a prioritized list of vulnerabilities and risks…
Blog
Not All CAASMs Are Created Equal: How Ordr Is Different
4Min Read
By Pandian Gnanaprakasam
We launched OrdrAI CAASM+ this week. I’m incredibly proud of our CAASM solution; we’ve spent a long time working with both prospects and customers in understanding the market requirements, addressing their specific needs, and developing a solution that addresses the flaws in existing products. We’ve also built on our foundational strengths in solving asset management and security challenges in the most complex verticals.
First let’s discuss the business reasons, and then the, “What, why, and why Ordr?” questions.
The bottom line business reason for OrdrAI CAASM+ is: with the explosive growth of attack surface volume and diversity, it’s impossible to do asset inventory management without a modern software solution. Furthermore, with the rising frequency of cybersecurity incidents affecting enterprise organizations, it’s imperative that security teams not only identify what assets they own, but also know what’s running on those assets, including software operating versions, access and permissions, and what they are accessing. These insights provide CISOs and security teams with the confidence to maintain compliance, by delivering a prioritized list of vulnerabilities and risks that enable rapid, automated action.
Introduction to CAASM (Cyber Asset and Attack Surface Management)
Cyber asset management focuses on complete, unified, and accurate visibility of all assets in the enterprise, including users, devices, software applications, installed software, and cloud resources. Attack surface management focuses on identifying vulnerabilities that can be exploited by hackers. We take this a step further by providing asset intelligence that creates deep, accurate context for every single asset. We believe that asset visibility alone falls short in empowering teams to proactively safeguard their attack surface. Comprehensive asset intelligence is essential for teams to proactively surface and fix asset risks and exposures.
What does that mean? To me, asset intelligence encompasses the following:
- Accurate, deep context for every asset: this is essential to ensure that you have the most accurate and complete data available for every asset to make effective security decisions. This deep context is essential, for example, with vulnerability management — knowing the software operating system and application details of a particular asset along with the support owner is important to be able to identify if you’re vulnerable and remediate. Accurate and deep context is also the foundation to surface insights on security coverage gaps and compliance violations.
- Risk-based vulnerability prioritization: this is a critical component of asset intelligence. CAASM prioritizes risks based on business impact and provides a unified view as a single source of truth for surfacing security gaps and vulnerabilities. It serves to simplify evidence gathering for audits, and accelerates incident response should there be a breach.
Why CAASM? And why is it critical for security teams to invest in CAASM solutions now?
The expansion of attack surfaces from digital transformation is happening in every enterprise, driving two key risk factors:
- Expanding enterprise boundaries: Digital transformation is causing enterprises to grow beyond traditional borders, encompassing cloud workloads, hybrid workforces, remote offices, and supply chain integration. As the boundaries expand so does the attack surface.
- Exploding number and types of assets: The volume and diversity of assets—from managed IT, to unmanaged IoT and OT—is skyrocketing. This leads to more significant vulnerabilities, and unmanaged devices also bring with them more unpatched vulnerabilities that lead to an increased threat surface.
All of this is compounded by the massive number of third-party tools we have running. Many of these help us with managing risks and vulnerabilities but they also lead to confusion with different feeds, duplicative asset counts, and disparate sources of data.
CAASM addresses these challenges by providing comprehensive and accurate visibility, consolidating siloed information, surfacing risks and exposures, and enabling efficient risk remediation and compliance reporting.
Why OrdrAI CAASM+?
We believe we can uniquely address the asset management challenges security teams are struggling to deal with today. In enterprise environments where asset landscapes are complex and interconnected, Ordr CAASM+ bridges the gap between physical and digital assets with comprehensive, accurate visibility. Our offering extends beyond traditional API-reliant methods, capturing data for all assets including often overlooked devices, such as IoT, OT and industrial controllers, and legacy systems. Data and business insights are the foundation of the OrdrAI Asset Intelligence platform, which is grounded in three principles: comprehensiveness, extensive depth of coverage, and trusted and proven accuracy.
The problems we’re solving aren’t new. Ordr has spent a long time analyzing the requirements for CAASM and we’ve worked very closely applying that experience in combination with input from key enterprises to build our CAASM+ product. Here’s how OrdrAI differentiates against other solutions:
- Comprehensiveness: Ordr’s multidimensional data collection strategy eliminates blind spots by going beyond API-only methods, capturing data from all devices including those which cannot have agents installed, such as IoT and OT devices.
- Depth of Coverage: With a crowdsourced library of millions of assets and AI/ML classification techniques, Ordr provides accurate asset identification, eliminating duplicates and facilitating automated enterprise workflows.
- Accuracy: Ordr’s proprietary data collection method–such as Ordr Software Inventory Collector and mapping engine–empower teams with accurate, real-time asset inventory and insights needed for security practitioners to find and fix risks and exposures.
- Generative AI-Powered Queries: when a cybersecurity issue hits the headlines, or a CISO inquires about a vulnerability (for example, “Are we vulnerable to ScreenConnect or MOVEit?” “Are all my managed endpoints protected with my EDR solution?” “Are there Axis video surveillance cameras in my network?”), how quickly can you answer these questions? We’ve made it easy with Generative AI-powered queries that do not require learning a new language, or navigating countless reports or dashboards.
- Expansion to OrdrAI Protect: OrdrAI CAASM+ addresses asset attack surface management challenges. For customers with mission-critical IT, IoT, IoMT, and OT devices, we offer a building block approach to implement OrdrAI Protect for advanced threat and anomaly detection, behavioral intelligence and segmentation capabilities.
Personally, I am super excited about launching the OrdrAI CAASM+ solution. And we look forward to engaging with enterprise security teams as they deploy OrdrAI CAASM+ and benefit from our class-leading asset intelligence insights.
Pandian Gnanaprakasam
Pandian has more than 20 years of product and engineering leadership experience and is also a serial entrepreneur. Before founding Ordr, he was the Chief Development Officer at Aruba, responsible for all of engineering and product management functions. Aruba, an enterprise mobile wireless company, was acquired by HPE for $3 Billion in March 2015. Before Aruba, Pandian served as the head of engineering for Cisco’s multi-billion-dollar Wi-Fi business unit and before that as VP of engineering for low-end switching product lines. He graduated with a master’s degree in Electrical Engineering from IIT, Chennai, India and holds several patents to his credit in various networking technologies.
Interested in Learning More?
Subscribe today to stay informed and get regular updates from Ordr Cloud
Ready to Get Started?
-
 BlogAchieving a Zero Trust Posture with its Device Inventory
BlogAchieving a Zero Trust Posture with its Device Inventory…and begin executing a plan to break down their perimeters into isolated environments. 4. Applications and Workloads: Agencies treat all applications as internet-connected, routinely subject their applications to rigorous empirical…
Security Strategy
Achieving a Zero Trust Posture with its Device Inventory
The White House’s Ambitious Goals
4Min Read
By Pandian Gnanaprakasam

The White House has announced a new and ambitious plan to achieve a Zero Trust cybersecurity posture for cyber assets operating in U.S. federal networks. With the right tech capable of seeing, knowing, and securing each device, the goal is already achievable. On January 26th the White House Office of Management and Budget (OMB) issued a memo outlining a “Federal strategy to move the U.S. Government toward a ‘zero trust’ approach to cybersecurity.” The memo is a follow-up to last year’s Executive Order on Improving the Nation’s Cybersecurity in which President Joe Biden outlined a set of priorities to improve the security posture of networks operated by U.S. federal agencies.

The White House has announced a new and ambitious plan to achieve a Zero Trust cybersecurity posture for cyber assets operating in U.S. federal networks. With the right tech capable of seeing, knowing, and securing each device, the goal is already achievable. (You can read our original response to the Executive Order here, and to the subsequent NIST memo regarding defining OT as critical infrastructure.)
The gears of change turn slowly in a bureaucracy as large as the U.S. federal government, and urgency to harden government networks is long overdue, especially with the discovery and exploitation of of zero-day vulnerabilities like Log4j. And as tensions rise in Eastern Europe, including the implied threat of cyberattacks against our national IT infrastructure and politically motivated “hacktivist” attacks against other governments disrupting services, the potential consequences of a lack of readiness are all too real.
Five Pillars of Federal Cybersecurity
The OMB strategy to “achieve specific zero trust security goals by the end of Fiscal Year (FY) 2024” was developed with cooperation from senior administration officials from the OMB, NSA, CISA, and key federal IT organizations. Those goals, which CISA refers to as “five pillars,” are identified in the OMB strategy memo as:
1. Identity: Agency staff use enterprise-managed identities to access the applications they use in their work. Phishing-resistant MFA protects those personnel from sophisticated online attacks.
2. Devices: The Federal Government has a complete inventory of every device it operates and authorizes for Government use, and can prevent, detect, and respond to incidents on those devices.
3. Networks: Agencies encrypt all DNS requests and HTTP traffic within their environment, and begin executing a plan to break down their perimeters into isolated environments.
4. Applications and Workloads: Agencies treat all applications as internet-connected, routinely subject their applications to rigorous empirical testing, and welcome external vulnerability reports.
5. Data: Agencies are on a clear, shared path to deploy protections that make use of thorough data categorization. Agencies are taking advantage of cloud security services to monitor access to their sensitive data, and have implemented enterprise-wide logging and information sharing.
These are ambitious goals for any organization to achieve, let alone those within federal agencies, some of which operate the largest IT operations in the world. And, examining the second pillar—device inventory, management, and security—we already know that there are many connected devices operating within federal networks that are beyond the visibility of IT operations. This was made clear following the discovery of security cameras made in China and connected to networks within the Department of Defense that were found to be sending data back to their manufacturers.
Managing and Securing a Vast Device Inventory
How can the U.S. government achieve their Zero Trust objective for its vast device inventory? Many federal agencies have already deployed Ordr to look across their IT infrastructure to discover and identify each device—including those that are currently unaccounted for and operating in the shadows.
We’ve proven time and time again how the following best practices and five-step approach can get you to Zero Trust.
- Step 1: Passively detect and identify all known, unknown, and prohibited devices without disruption or adverse effects to operations. Ordr’s agentless deployment delivers device inventory and categorization within hours of deployment, and augments device context with additional network data and threat intelligence
- Step 2: Identify devices at-risk to reduce the attack surface. Ordr offers an integrated intrusion detection engine and integration with threat intelligence services, vulnerability management tools, and manufacturing databases to pinpoint the devices that are most likely to be targeted by attackers. By addressing known vulnerabilities, taking prohibited devices offline, or segmenting mission-critical devices, federal agencies can start to reduce their attack surface.
- Step 3: Map and baseline communications patterns for every device. Every device has deterministic functions. Ordr can profile and baseline device behavior using machine learning to reveal and alert to the presence of anomalous communications.
- Step 4: Apply appropriate Zero Trust security policies on devices. Ordr offers proactive, reactive, and retrospective policies. Ordr Zero Trust segmentation policies can be proactively and automatically (yes this means with a push of a button and without manual effort) created for devices, to only allow communications required for their functions. Ordr reactive policies applied on firewalls, NACs, and switches immediately limit exposure and mitigate risks by blocking traffic, terminating sessions, or isolating compromised devices. Finally, Ordr retrospective policies enable a time-machine view of infected devices communicating to newly announced indicators of compromise.
- Step 5: Finally, federal agencies need to continuously monitor the network to identify new devices that connect, detect indicators of compromise in operation, and automatically enforce security policies when risks are detected.
(For more details, check out our whitepaper “5 Steps to Zero Trust”.)
Success Within Reach
Given the size and scope of the U.S. federal government’s combined IT infrastructure, it may seem that the goals articulated by the White House and CISA are unrealistic within the given timeline. In fact, where accounting for and reining-in a massive device inventory is concerned, success is well within reach. Ordr is already deployed within many federal agencies where a Zero Trust device posture is in effect. We’ve proven ourselves in many environments—such as healthcare, financial services, retail, manufacturing, and more—where device security is a priority for protecting critical infrastructure and maintaining operations.
Ordr is proud to be leading the way in this priority initiative to improve national cybersecurity. And with a simple demonstration we can show your agency or organization how you can identify, inventory, assess, and protect your connected devices within minutes. Contact us at info@ordr.net.
Pandian Gnanaprakasam
Pandian has more than 20 years of product and engineering leadership experience and is also a serial entrepreneur. Before founding Ordr, he was the Chief Development Officer at Aruba, responsible for all of engineering and product management functions. Aruba, an enterprise mobile wireless company, was acquired by HPE for $3 Billion in March 2015. Before Aruba, Pandian served as the head of engineering for Cisco’s multi-billion-dollar Wi-Fi business unit and before that as VP of engineering for low-end switching product lines. He graduated with a master’s degree in Electrical Engineering from IIT, Chennai, India and holds several patents to his credit in various networking technologies.
Interested in Learning More?
Subscribe today to stay informed and get regular updates from Ordr Cloud
Ready to Get Started?
-
 NewsOrdr Named a KLAS Research Top Performer
NewsOrdr Named a KLAS Research Top Performer…to fully understand and protect the ever-expanding attack surface. Ordr empowers HTM and security teams with the insight, context, and tools needed to protect all IoT, IoMT, operational technology (OT),…
Ordr Named a KLAS Research Top Performer
Unprecedented Fourth Year for Healthcare IoT Security
2Min ReadSanta Clara, CA – July 18, 2023 – Ordr, the leader in connected device security, today announced that KLAS Research has recognized the company as a top performer in its recent report entitled “Healthcare IoT Security 2023: An Update on Vendor Performance and Deep Adopter Utilization.” This is the fourth year that Ordr has been recognized as a top performer in this report by KLAS Research.
The report provides insights into the competitive healthcare IoT security market by looking at vendor performance amid recent mergers and acquisitions, as well as early insights into how vendors meet the needs of deep adopters.
Ordr received top rankings from customers in the KLAS report, with customer feedback praising the following:
- Continually improving the user interface to simplify access to key device insights.
- Strong integration with devices and security systems, and new integration capabilities that are continually added to the road map.
- “Persona” feature that enables collaboration with multiple teams and stakeholders, including security and clinical engineering/HTM, for a “whole hospital” security.
- Automated segmentation capabilities to mitigate risks, stop lateral movement, and keep devices with outdated operating systems in operation.
“We work with the world’s largest and top ranked healthcare organizations, and are dedicated to delivering the industry’s most powerful medical device security platform to protect their patients and patient data,” said Jim Hyman, CEO at Ordr. “All the effort and expertise we put into building a platform with the intelligence and automation necessary to achieve ‘whole hospital’ security is equally focused on meeting our customers’ high expectations. As shared in the KLAS report, it is rewarding to see that customers are delighted with our ability to bring HTM and cybersecurity teams together to sustain more efficient HTM operations, address Zero Trust initiatives, and protect against advanced threats.”
When asked about Ordr, a customer CIO shared that:
“Meeting our IoT security needs is a pretty big thing, but the Ordr Platform helps us manage our other security as well as validation with our other security systems. When we find some sort of vulnerability, Ordr comes up with a solution for monitoring that type of traffic on top of our other security. They are a great partner in layered security. Recently, Ordr integrated their system with one of our partners’ systems, and that integration allows us to do segmentation in a much more automated fashion than we would have been able to do in the past. While that is a requirement for more than just IoT security, it is a value add that was a panacea for a long time and is now a reality. Without Ordr’s Platform, we would have had a huge gap in our visibility. It has been a great product for us.”
Because all connected devices in a medical facility are critical, a “whole hospital approach” to security is necessary in order to fully understand and protect the ever-expanding attack surface. Ordr empowers HTM and security teams with the insight, context, and tools needed to protect all IoT, IoMT, operational technology (OT), and traditional IT systems. Ordr helps medical facilities protect against ransomware and zero-day attacks by baselining device behavior and identifying any devices that are behaving anomalously. Incident response efforts are accelerated by immediately identifying compromised devices and dynamically creating and applying security policies. In addition, the platform supports Zero Trust segmentation efforts by enabling only required device communications from those devices already or likely to be impacted
Learn how your organization can improve connected medical device and equipment visibility and security with Ordr.
Interested in Learning More?
Subscribe today to stay informed and get regular updates from Ordr Cloud
Ready to Get Started?
-
 NewsNHS Data Security And Protection Toolkit
NewsNHS Data Security And Protection Toolkit…it mandatory for NHS organizations to now keep an up-to-date inventory of all medical devices including security vulnerabilities and data security. All organizations that have access to NHS patient data and systems…
Ordr Helps Healthcare Organizations Meet Key Criteria
NHS Data Security And Protection Toolkit
4Min ReadMEDIA ALERT
What is Being Announced?
NHS Digital has recently amended the NHS Digital’s Data Security and Protection Toolkit (DSPT) making it mandatory for NHS organizations to now keep an up-to-date inventory of all medical devices including security vulnerabilities and data security. All organizations that have access to NHS patient data and systems must adhere to the requirements in this toolkit to provide assurance that they are practising good data security and that personal information is handled correctly.
Ordr, the leader in agentless security for all connected devices, is today launching a guide to assist healthcare organizations to meet the new DSPT criteria. Healthcare organizations are particularly vulnerable to cyber-attacks such as ransomware, due to outdated operating systems running on medical, Internet of Things (IoT) and Operational Technology (OT) devices. This is due to the fact that many of these devices, in particular medical devices, remain in operation for a number of years and cannot be easily replaced for cost reasons.
Ordr in its recent Rise of the Machines report found 19% of deployments with devices running outdated operating systems Windows 7 and older, and almost 34% of deployments with devices running Windows 8 and Windows 10, which are expected to end-of-life in 2023 and 2025 respectively. Organizations need an automated way to identify these devices-at-risk and segment them to ensure security of these devices, keep them in operation and avoid the costs of replacing devices early.
What Is DSPT?
NHS Digital’s Data Security and Protection Toolkit (DSPT) is an online self-assessment tool that enables organizations to measure their performance against the National Data Guardian’s 10 data security standards. All organizations that have access to NHS patient data and systems must use this toolkit to provide assurance that they are practicing good data security and that personal information is handled correctly. This system is subject to ongoing development.
What Does It Mean for Healthcare Organizations?
DSPT compliance will force many organizations to take a fresh look at their cybersecurity programme and make changes to align with NHS Digital requirements. Core security functions such as inventory, risk management, and threat detection will be essential to maintaining compliance, and organizations should look for efficient, automated systems that can help provide coverage for all connected devices — from traditional servers, workstations, and PCs to IoT, IoMT and OT devices.
Bob Vickers, Head of UKI at Ordr commented:
“Even though data security standards ask healthcare organizations to ensure technology is secure and up to date with no unsupported operating systems, this is actually a global medical challenge for most. Connected medical devices can range widely, and often ran on outdated systems, even though they are a critical part of business operations.
We need to remember that securing medical devices will define the future of healthcare. Security teams need the right tools to increase visibility into risks, bring devices into compliance, optimize utilization and protect them from cyberattacks. spend. Here at Ordr, healthcare organizations can not only gain complete visibility into devices and risks, they can also keep track of NHS Cyber Alerts as a data feed into the Ordr Systems Control Engine (SCE) and address cyber threats such as ransomware on their network. By leveraging automation to drive efficiencies, they can ensure the highest standards of security for patient safety.”
How Can Ordr Help?
Ordr SCE can arm organizations with a powerful platform to gain visibility into their network-connected devices, automatically expose potential risk, and automatically enforce policies for rapid mitigation during cyber attacks or segment high-risk devices to only “allowed” communications, passively and without agents. Ordr is already working with the University Hospital Southampton NHS Foundation Trust (UHS) and the University Hospitals of North Midlands NHS Trust (UHNM Trust) to tackle these challenges, and to improve healthcare cybersecurity and patient safety.
Some of the key criteria that Ordr can help healthcare organizations with are: Personal Confidential Data, Managing Data Access, Responding to Incidents, Continuity Planning,
Unsupported Operating Systems and IT Protection.
The Ordr system has the following key functionality to help meet the above criteria:
- Real-time Asset Inventory: Ordr brings together a unique combination of traffic analysis and AI to automatically discover and classify every device on the network. This includes high-fidelity information such as make, classification, location, and application/port usage.
- Vulnerability Management: Ordr delivers a variety of unique capabilities in the area of vulnerability management. The platform includes a built-in vulnerability scanner to identify devices affected by a variety of industry-specific security alerts or recalls.
- Behaviour and Risk Profiling: Ordr includes a built-in IDS engine to detect threats and devices that are under active attack. Ordr also automatically learns every device’s unique communication patterns, known as its Ordr Flow Genome. This provides a baseline that can be used to find suspicious and anomalous behaviours that could be the sign of an unknown threat.
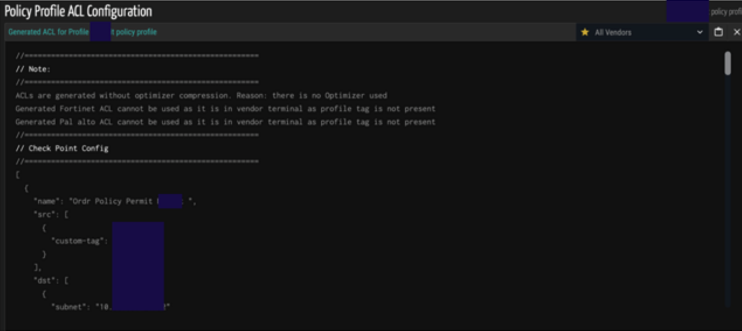
- Automated Response: Ordr can can automate the creation of NGFW policies, ACL blocks, quarantine VLAN assignment, port shutdown, or session termination with one click of a button– enforced on existing switches, wireless controllers, and firewalls, or via NAC platforms—to mitigate risks. By baselining device behaviour, Ordr can also dynamically create segmentation policies such as firewall rules that provide devices with necessary access while limiting unnecessary exposure.
Prepare today
The Data Security and Protection Toolkit is an annual self-assessment. The deadline for the 2021-22 publication is 30 June 2022. See how Ordr maps to the “Data Security And Protection Toolkit (DSPT)”.
Interested in Learning More?
Subscribe today to stay informed and get regular updates from Ordr Cloud
Ready to Get Started?
-
 NewsOrdr Secures $40 Million in Series C Funding
NewsOrdr Secures $40 Million in Series C Funding…from “detection” to “response” requires insights into the compromised device, where it’s located, and what policies can be applied. Ordr offers complete and accurate asset visibility, automates and enforces Zero…
Ordr Secures $40 Million in Series C Funding
Answers Increased Demand for Connected Device Security
4Min ReadSanta Clara, CA – June 1, 2022 – Ordr has raised an additional $40 million to meet the growing need for organizations to understand, manage, and secure the growing number of connected devices in their environment, including Internet of Medical Things (IoMT), Internet of Things (IoT), and Operation Technology (OT). The funding round was co-led by Battery Ventures and Ten Eleven Ventures, with participation from new investor Northgate Capital and continuing investors Wing Venture Capital, Unusual Ventures, Kaiser Permanente Ventures, and Mayo Clinic. Other investors in Ordr’s Series C include Silicon Valley entrepreneurs René Bonvanie, former CMO of Palo Alto Networks, Dan Warmenhoven, former Chairman and CEO of NetApp, and Dominic Orr, former Chairman and CEO of Aruba Networks. With this funding, Ordr has raised more than $90 million to date.
Ordr addresses two key enterprise initiatives associated with a growing reliance on and adoption of connected devices: digital transformation and Zero Trust. Each new device connection increases an organization’s attack surface, along with the potential for a breach or ransomware attack. In industries such as healthcare and manufacturing, a cyberattack impacting an IoT device can easily disrupt the entire business or become a life-threatening situation. For organizations to move quickly from “detection” to “response” requires insights into the compromised device, where it’s located, and what policies can be applied.
Ordr offers complete and accurate asset visibility, automates and enforces Zero Trust policies, and accelerates incident response by hours with insights into devices and risks. As a result, Ordr experienced more than 140% year-over-year growth in new customer revenue in its most recent quarter ending on March 31, 2022, is deployed in 3 of the world’s top 6 hospitals, and has been adopted across more than 150 manufacturing sites.
“Ordr has built a platform that not only solves an important market issue – the need to definitively understand and protect what is connecting to your organization’s network – but is truly scalable to keep pace with the speed of today’s businesses. We’ve worked with Ordr’s team and seen firsthand how well they’ve executed against aggressive goals. This additional funding will accelerate Ordr’s market leadership and success in the market,” said Dharmesh Thakker, general partner at Battery Ventures.
“We believe the connected device security market needs a strong, open, and independent player that prioritizes customer success, focuses on time-to-value, and integrates with all the key components of a customer’s security and network infrastructure. This funding validates our best-in-class approach and solidifies our leadership in the market,” said Greg Murphy, Ordr CEO.
Ordr plans to use the Series C funding to accelerate its sales and marketing efforts, especially in vertical markets such as healthcare, where the company has been named a market leader in the Healthcare IoT security industry by analyst firm KLAS Research for three consecutive years. The company will also look to further capitalize on steadily increasing demand from manufacturing and financial services, expand its channel and partnership programs, and accelerate investments in customer success.
“In order to advance their digital transformation goals, every organization needs to enable the visibility and security of connected devices, including IoT, IoMT, and OT. Ordr is a much-needed innovator in the market, with the ability to not only deliver granular visibility into devices, risks, and behaviors, but also automate and enforce Zero Trust policies to secure these devices from attacks,” said Justin Stebbins, partner, Northgate Capital.
“As an early investor in the company, I have witnessed Ordr’s impressive product evolution and growing traction within critical sectors, including healthcare, manufacturing, education, and extended enterprise IoT. They have developed one of the most scalable and technically robust platforms in the market, and some of the world’s leading organizations depend on it to fulfill important security needs and deliver business insights. The time is right to accelerate the company’s mission to be the leader in connected device security. We believe in their success and look forward to the next chapter.” said Alex Doll, Founder and Managing Partner of Ten Eleven Ventures.
Since its last round of funding, Ordr has experienced tremendous growth, coinciding with an increased understanding of the organizational risk represented by unknown connected devices. Some additional highlights since the last funding round include:
- Named a KLAS Research Healthcare IoT Security Market Leader for an unprecedented three years in a row.
- Named a Representative Vendor in the 2022 Gartner Market Guide for Medical Device Security Solutions for the second year in a row.
- Continued product innovation and market leadership in the healthcare industry with the launch of Clinical Defender, streamlining management of connected medical devices.
- Enhanced the company’s integrations with Cisco, making it even easier for Cisco customers to roll out Ordr across their network environments.
- Launched the Ransom-Aware Rapid Assessment to help companies quickly and accurately assess their ransomware risks.
- Successfully achieved SOC2 compliance to keep customer data secure.
“Data privacy and security are imperative IT initiatives within the healthcare industry with connected device security in particular as a critical need given the increase in connected devices in health care facilities. Kaiser Permanente Ventures is pleased to continue its investment in Ordr as a key technology leader in this space, to help protect connected devices automatically, preemptively and at scale across the enterprise,” said Chris Stenzel, executive managing director, Kaiser Permanente Ventures.
Continuing the momentum of the past year, Ordr today also strengthened its executive team with the addition of Paul Davis as the company’s new vice president of customer success. Paul has decades of experience in customer-facing roles at Axis Security, Splunk, Cisco, and other leading organizations. At Ordr, he will be responsible for managing customer relationships and ensuring the successful implementation and use of Ordr technology.
Interested in Learning More?
Subscribe today to stay informed and get regular updates from Ordr Cloud
Ready to Get Started?
-
 BlogBOD 23-01: Shedding Light on Federal Enterprise Asset Visibility
BlogBOD 23-01: Shedding Light on Federal Enterprise Asset Visibility…to ensure asset inventories are up-to-date. The philosophy behind the directive is sound. Today’s IT estates are complex and include thousands of components operating on-premises and in the cloud. Servers,…
Security Strategy
BOD 23-01: Shedding Light on Federal Enterprise Asset Visibility
4Min Read
By Chris Westphal

CISA’s Binding Operational Directive 23-01 (BOD 23-01) affirms the importance of full enterprise asset visibility. Ordr offers insights on BOD 23-01 to explain why real-time asset discovery and visibility is vital to compliance with the directive. Binding Operational Directive 23-01 can help close a government security gap
The Cybersecurity & Infrastructure Security Agency (CISA) recently issued an advisory on a dozen new exploits and vulnerabilities affecting industrial control systems (ICS) from nine different manufacturers. The warning is the latest in a growing body of evidence that critical public infrastructure–things like the power grid, transportation systems and facilities, government buildings, and public safety organizations–will soon become the primary target of threat actors in an escalation of attacks against national economic interests. In fact, some observers believe a shift in strategies in the war between Russia and Ukraine is proof that such an escalation is well underway.
It’s hard to argue that threat actors are not becoming increasingly aggressive and willing to attack targets, even when there might be a human cost. Hospitals and healthcare services providers have seen a sharp increase in attacks over the last three years, and research suggests those attacks are associated with an increase in patient mortality. Even the U.S. Federal Reserve warns that attacks on industrial enterprises and infrastructure could impede economic activity and seriously undermine confidence and stability in national financial systems.
Setting a Good Example
And so, as attention turns toward the hardening of private and public infrastructure against cyberattacks, leaders in Washington, D.C. are trying to set a positive example by updating their own security policies. When the White House issued the Executive Order on Improving the Nation’s Cybersecurity on May 12, 2021, it established the foundation for the government’s strategy to address the protection of a sprawling and complex federal IT infrastructure comprising hundreds of different agencies. Then in early March this year the White House published its National Cybersecurity Strategy to bring the issue into sharper focus.
The Cybersecurity & Infrastructure Security Agency (CISA) took a big step forward when it issued Binding Operational Directive (BOD) 23-01,Improving Asset Visibility and Vulnerability Detection on Federal Networks.
But the work toward improving the federal government’s readiness and resilience against cyberthreats was underway before the release of the National Cybersecurity Strategy. In October of 2022 the Cybersecurity & Infrastructure Security Agency (CISA) took a big step forward when it issued Binding Operational Directive (BOD) 23-01, Improving Asset Visibility and Vulnerability Detection on Federal Networks.
Connected Device Visibility is Critical

BOD 23-01, which had a deadline of April 3, 2023, requires all federal civilian executive branch (FECB) agencies to establish the means for effecting “continuous and comprehensive asset visibility” as a first step in assessing and monitoring cyber risk. CISA did not identify penalties for missing the April 3 deadline, but there are ongoing reporting and improvement timelines to ensure asset inventories are up-to-date. The philosophy behind the directive is sound. Today’s IT estates are complex and include thousands of components operating on-premises and in the cloud. Servers, routers, switches, software, application, services, and all kinds of devices, many of which are practically invisible to traditional IT management systems.
This is especially true for connected devices, including the Internet of Things (IoT), Internet of Medical Things (IoMT), operational technology (OT), and more. And what BOD 23-01 does is acknowledge that, without a complete accounting of every single device that connects to the enterprise—expected or unexpected, and for however long it remains connected—each is a potential vector for attack. Also, when connected assets are unaccounted for, an organization’s configuration management database (CMDB) will be inaccurate, leading to other IT operations and security issues that can put the enterprise at risk. Ordr’s experience with connected device discovery illustrates the wide variety of unexpected devices that can be found operating in some enterprises alongside mission-critical equipment. Vending machines and building controls, Tesla cars and Kegerators, Alexas and Pelotons, all connected to the network and communicating out to the Internet, unmanaged and unknown to IT operations and security.
See IT, Protect IT
You can’t protect what you can’t see, and so device discovery, visibility, and monitoring is vital to maintaining security at a high level. Ordr is not only able to discover and monitor these devices in real-time, but the extensive Ordr Data Lake contains detailed profiles of millions of IoT, IoMT, and OT devices, identifying their purpose and operational profile. That enables security teams to identify devices with vulnerabilities, establish a risk score for every device operating in the network, detect when devices exhibit indicators of compromise, and automate policy creation to accelerate response and prevent attacks targeting connected devices or prevent lateral movement. These capabilities support BOD 23-01’s objective to “make measurable progress toward enhancing visibility into agency assets and associated vulnerabilities… an important step to address current visibility challenges at the component, agency, and [federal civilian executive branch] enterprise level.”
These capabilities support BOD 23-01’s objective to “make measurable progress toward enhancing visibility into agency assets and associated vulnerabilities… an important step to address current visibility challenges at the component, agency, and [federal civilian executive branch] enterprise level.”
It’s good that the U.S. federal government recognizes that maximizing the effectiveness of a cybersecurity program demands a full accounting of every device operating in the network. That is the foundational tenet to Ordr’s mission, and it has been embraced by our customers, including many of the world’s largest healthcare, financial, and manufacturing organizations. And for our customers in the federal government, they had a head start on meeting (and likely exceeding) requirements ahead of CISA’s April 3 deadline.
If your agency or organization recognizes that it has blind spots it needs to address to take a full inventory of every device it has connected to its network, give us a call. We can run a demonstration that can show you every connected device on the network. And with a complete accounting of your connected assets, you can build a plan to see, know, and secure your enterprise.
Chris Westphal
Head of Product Marketing
Chris is the Head of Product Marketing at Ordr where he helps drive awareness for connected device security and the value of the Ordr solution. Chris brings more than two decades of experience to his role with a background in enterprise security, cloud, and data center technologies. Most recently, Chris was head of product marketing at Salt Security, the leader in API protection, and has held product marketing leadership roles at companies including VMware, Illumio, and Adallom (acquired by Microsoft).
Interested in Learning More?
Subscribe today to stay informed and get regular updates from Ordr Cloud
Ready to Get Started?
-
 BlogOrdr and Gigamon: Network and Device Visibility
BlogOrdr and Gigamon: Network and Device Visibility…and continually connecting more and more devices. Comprehensive visibility into the traffic, devices, behaviors, and risks allows network and security managers to take the key measurements needed to make smart…
Company News
Ordr and Gigamon: Network and Device Visibility
2Min Read
By Bryan Gillson

You can’t manage what you can’t measure. That is why real-time asset discovery and data ingestion is vital to cybersecurity. Order and partner Gigamon work together to provide a comprehensive infrastructure for network and device visibility. Peter Drucker may have directed his famous adage, “you can’t manage what you can’t measure,” to business managers, but these words ring just as true for network and security managers. Technology leaders constantly measure and manage risk, performance, capacity, and numerous other metrics.
However, there’s an important corollary: You can’t measure what you can’t see. Without visibility, measurement and management become almost impossible.
Nowhere is this more true than with enterprise networks. They are complex, constantly evolving, and continually connecting more and more devices. Comprehensive visibility into the traffic, devices, behaviors, and risks allows network and security managers to take the key measurements needed to make smart decisions. However, hooking a multitude of “monitoring solutions” to a network can create problems with performance, SPAN/Tap availability, and complexity.
This is where Gigamon and Ordr work together to provide a comprehensive infrastructure for network and device visibility.
The Gigamon Visibility and Analytics Fabric collects full-fidelity information from your physical, virtual, and cloud network infrastructures, optimizes the traffic via de-duplication and advanced filtering, and creates a consistent and centralized interface for viewing all data in motion. This can particularly benefit complex or distributed organizations, allowing centralized monitoring of east-west (internal) traffic as well as north-south (datacenter-to-internet) traffic. Enterprises benefit from full visibility into network traffic, regardless of its origin or destination.
Ordr SCE leverages the Gigamon Visibility and Analytics Fabric to passively inventory and classify every device on a network, from traditional IT devices such as workstations, printers and servers, to IoT devices such as medical devices, building automation, and security cameras, to operational technology (OT) such as manufacturing tools, sensors, and PLCs. Ordr then takes this visibility to the next level: not just identifying network devices, but identifying their behavior, their communication patterns, and their risks.
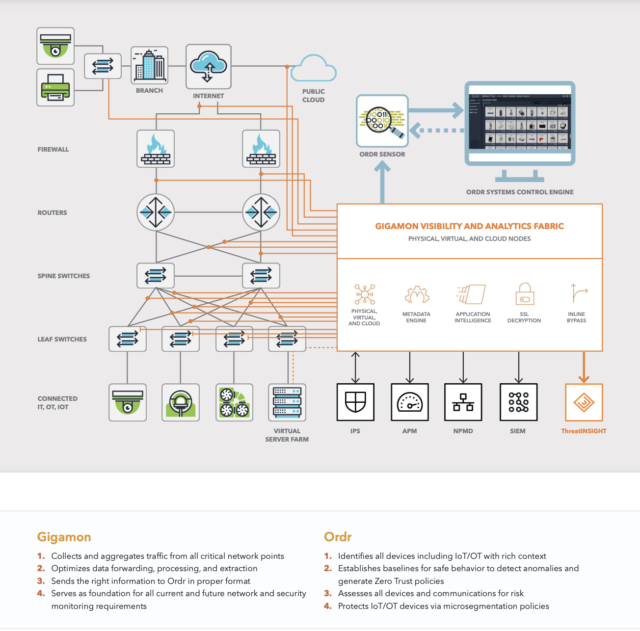
Gigamon and Ordr joint solution
When deployed onto the Gigamon infrastructure, Ordr can be deployed more quickly, with less (or less expensive) hardware, and with less contention for SPAN or TAP ports on network switches. Additionally, Gigamon’s ability to centralize traffic often means a more comprehensive inventory of devices that are connected to complex, highly distributed networks. More visibility means better management of risks.
Interestingly, encryption adds another twist to the visibility story. While internal use of TLS improves security in many ways, it can also blind network analysis tools to the data needed to identify security breaches like advanced persistent threats (APTs), remote access trojans (RATs) and crypto mining. Gigamon Visibility and Analytics Fabric addresses this challenge too. Its TLS decryption support offers a secure window into encrypted traffic, giving Ordr complete visibility into encrypted inbound, outbound, and internal networks.
Together, Gigamon and Ordr give network, security, and business-aligned technical groups (such as clinical engineering) unparalleled visibility into enterprise networks, devices, behaviors and risks. Gigamon customers seeking to identify and protect IT, IoT, IoMT, and OT devices should schedule a free demo of Ordr SCE to see how it can quickly and easily offer new levels of visibility and security for the devices in your network. Ordr customers who wish to optimize their network visibility infrastructure can reach out to Gigamon for a demo or free trial as well.
Full visibility into network flows, devices, and network behaviors with Gigamon and Ordr makes measuring and managing your risk a straightforward task. Peter Drucker would be proud.
For more information on Gigamon and Ordr, check out our solutions brief here, and watch our See, Segment, Secure webinar here:
Bryan Gillson
Bryan joined Ordr in November 2019 after spending six years as VP Strategic Alliances at Ionic Security. At Ionic, Bryan initiated and managed business relationships with system integrators such as Accenture, Deloitte, and PwC, and closed OEM partnerships with vendors in the CASB, virtualization, and data protection sectors. Previously, Bryan led product management and business operations for Symantec’s encryption products and information protection groups after integrating the acquisitions of both PGP Corporation and GuardianEdge. Prior to Symantec, Bryan led the business development team at PGP Corp. and was a VP in Merrill Lynch’s Technology Investment Banking group.
Interested in Learning More?
Subscribe today to stay informed and get regular updates from Ordr Cloud
Ready to Get Started?
-
 BlogHealthcare M&A Means Acquiring Legacy Threats
BlogHealthcare M&A Means Acquiring Legacy Threats…year. The Good and Bad of Healthcare M&A When larger hospitals acquire smaller–and especially rural–hospitals, it can have a positive effect on access to quality of care for the communities…
Risk Management
Healthcare M&A Means Acquiring Legacy Threats
5Min Read
By Darrell Kesti

As large healthcare networks acquire smaller hospitals, the acquiring organization must conduct cybersecurity due diligence to ensure previously undetected threats lurking in any acquired networks do not come with the purchase. 
Fort Kent is a town of just over 4,000 residents abutting the Canadian border in rural Aroostook County, Maine. Fort Kent is famous for being the northernmost terminus of U.S. Route One, and infamous for its long, harsh winters. It is also home to Northern Maine Medical Center (NMMC), a 10-bed hospital that has seen services cut in an effort to lower operating costs.
Maine Public Radio recently reported from a public forum held in Fort Kent’s town hall after the hospital announced plans to close its maternity ward. Residents fear NMMC will soon close; and if it does it will be part of a growing trend. The American Hospital Association (AHA) says that 136 rural hospitals have closed since 2010, and according to a recent report by the Center for Healthcare Quality and Payment Reform (CHQPR), there are more than 600 hospitals across the country in danger of closing due to financial pressures. Of those, more than 200 are in immediate danger of shutting down. That means that hospital mergers and acquisitions (M&A) are likely to continue as a trend identified by Chief Healthcare Executive magazine, which reported there were more than 50 hospital M&As in 2022, with more expected this year.
The Good and Bad of Healthcare M&A
When larger hospitals acquire smaller–and especially rural–hospitals, it can have a positive effect on access to quality of care for the communities they serve. The AHA said that nearly 40% of hospitals added services after being acquired, and that operating efficiencies helped to lower costs by an average of 3.3% after an acquisition. But along with the benefits associated with healthcare M&As come security risks. Security Magazine reported that ransomware attacks on healthcare organizations have doubled since 2016, and because rural hospitals struggle with financial and staffing constraints, they are often more easily breached by threat actors.
In her testimony to the Senate Homeland Security & Government Affairs Committee during a hearing on cybersecurity threats to rural healthcare organizations, former North Country Hospital (Vermont) CIO/CISO Kate Pierce said, “[An] alarming trend that escalated in 2022 was cyber attackers shifting focus to small and rural hospitals. While most larger health systems have implemented advanced cybersecurity hygiene to thwart attacks and are employing large cybersecurity teams with sophisticated defenses, small facilities continue to struggle.”
[An] alarming trend that escalated in 2022 was cyber attackers shifting focus to small and rural hospitals. While most larger health systems have implemented advanced cybersecurity hygiene to thwart attacks and are employing large cybersecurity teams with sophisticated defenses, small facilities continue to struggle.”
Kate Pierce, former CIO/CISO, North Country HospitalThe Lurking Threat of Acquired Risks
The dynamic nature of connected devices operating in a network complicates security and IT management issues. In healthcare, these challenges are magnified because patient safety is affected when operations are compromised. Some findings from our most recent Rise of the Machines, Enterprise of Things Adoption and Risk Report (keep your eyes peeled for our 2023 edition soon), show the dangers present when Internet of Things (IoT), Internet of Medical Things (IoMT), and operational technologies (OT) proliferate in a healthcare environment.:
- 86% of IoT and IoMT deployments have 10 or more FDA recalls.
- 15%-19% of connected devices run on obsolete/unsupported operating systems.
- 10%-15% of devices connected to the network are unknown or unauthorized.

When a larger hospital makes an acquisition, it takes on the legacy cyber risks that previously beset the smaller one, including the technology assets used to run the facility and support staff in delivering care. In the best cases, hospitals and other healthcare delivery organizations (HDOs) rely on connected medical devices that are likely vulnerable to cyberattack. And once a piece of medical equipment is put in service, it may end up running with obsolete or unsupported software for years, or new vulnerabilities may be revealed that cannot be patched quickly due to patient safety concerns.
Even when a large hospital with “advanced cybersecurity hygiene” takes over the IT and security operations of a smaller hospital, it can take time to assess and mitigate the risks associated with integrating the new organization’s IT estate. And if any of the acquired systems were compromised prior to acquisition, a lurking, undetected threat actor may be able to use the smaller hospital’s IT infrastructure as a kind of Trojan horse from which to move laterally into the new owner’s systems, much like when hotelier Marriott was breached after acquiring Starwood Hotels in 2014.
Mitigate M&A Cybersecurity Risks
With these challenges in mind, a best practice approach to cybersecurity during an M&A event involves three critical steps:
1. Discover every asset in the network
You can’t protect what you can’t see, and so the key to addressing legacy threats and vulnerabilities inherited through the acquisition of other organizations’ technology estates is to be able to discover and classify every asset. That includes all the connected devices in operation: IoMT, IoT, OT, and more. This comprehensive asset inventory may also be useful to determine duplicate systems and reduce redundancies as both organizations in the M&A consolidate their assets.
The Ordr platform performs device discovery and classification quickly, and then monitors communications and tracks changes in real-time. Ordr goes beyond mere visibility to deliver deep, granular, classification of every device, from make, model, serial number, and operating system details. It also provides vital context about where a device is connected and what other systems it is communicating with. Ordr addresses one of the most common M&A challenges of overlapping IP schemas when two organizations are combined. This challenge prevents teams from easily establishing a single view of both environments and can slow risk assessment and integration efforts.
2. Identify your attack surface
The next step is identifying and measuring the attack surface from these assets. This can include devices with vulnerabilities, devices running outdated operating systems, or those with weak passwords. By baselining devices and their communications patterns, you can determine behavior that is outside of norm, that may be an indication of a compromised device.
From a deep, granular foundation of visibility, Ordr gives a complete view of the connected device attack surface and communications in real-time. Ordr identifies which devices are vulnerable or acting in a risky manner, and assigns a risk score based on the device’s known, determinative operational parameters.
3. Implement M&A cybersecurity best practices
Once you know what devices and risks you are inheriting as part of the acquisition, you can begin to implement M&A cybersecurity best practices. The most basic M&A cybersecurity best practices may be segmentation between the two networks, until access and convergence is complete. You will also want to identify or document key risks that need to be mitigated and addressed during or post acquisition.
Ordr dynamically automates the creation and enforcement of security policies. This means that organizations using the Ordr platform can quickly block attacks, quarantine compromised devices, segment vulnerable devices, and accelerate Zero Trust projects to proactively improve security.

Cybersecurity Due Diligence
Because hospitals and HDOs are under constant risk of attack from threat actors who care nothing of the danger their actions present to patients—and, in fact, use that danger to their advantage when carrying out ransomware attacks—there is no grace period when acquiring a smaller organization. It is imperative that the acquiring hospital include cybersecurity when conducting their due diligence. The network must be inventoried, assessed, and protected as quickly as possible, and Ordr helps get that done even before a contract is signed.
Furthermore, we operate on a philosophy of continuous improvement, expanding our integrations, leveraging the most up-to-date threat intelligence, and building our library of millions of device profiles to ensure Ordr is the most comprehensive, single source of connected device truth available. Check out our M&A solution brief for more details on how we help with cybersecurity due diligence.
Darrell Kesti
Darrell is VP Sales at Ordr. He joined Ordr as one of the original Account Executives in October of 2018 to help launch the field organization. In his prior role as Ordr’s Director of Healthcare Sales, Darrell drove significant growth in healthcare sales and helped position Ordr as the leader in connected device security. Darrell has had over 20+ years of Sales Leadership, Account Management, and Field Engineering experience supporting customers and partners while with leading security and networking organizations – ForeScout Technologies, FireEye, Mandiant, F5 Networks, and Secure Computing Corporation. Darrell earned a Bachelor of Science in Electrical and Computer Engineering from the University of Minnesota, Duluth.
Interested in Learning More?
Subscribe today to stay informed and get regular updates from Ordr Cloud
Ready to Get Started?
-
 BlogConnectWise ScreenConnect CVE Vulnerabilities
BlogConnectWise ScreenConnect CVE Vulnerabilities…on CVE-2024-1709 and CVE-2024-1708, refer to the official CVE database and the advisories provided by ConnectWise and CISA. How to use Ordr to detect and respond to this threat Ordr…
Security Bulletin
ConnectWise ScreenConnect CVE Vulnerabilities
3Min Read
By Pandian Gnanaprakasam

The ConnectWise Screen Connect vulnerabilities (CVE-2024-1708 and CVE-2024-1709) put many enterprises at risk of a cyberattack. Ordr can identify and mitigate the vulnerabilities by supporting patching, segmenting affected systems, and facilitating rapid response. Background
ConnectWise ScreenConnect software is a comprehensive remote desktop access software solution that enables secure, flexible, and efficient technical support for its customers. Part of ConnectWise’s suite of IT service delivery and support products, ScreenConnect is commonly used by managed service providers (MSPs) to gain remote access to customer endpoints for services such as IT support.
ConnectWise recently announced it discovered that flaws in ScreenConnect were being actively exploited and issued a security advisory. The ConnectWise advisory reported that all versions of ScreenConnect prior to 23.9.8 contained two vulnerabilities.
Vulnerability Details
CVE-2024-1709 CVE-2024-1708 Severity Critical
CVSS: 10High
CVSS: 8.4Products affected ConnectWise ScreenConnect Software. ConnectWise ScreenConnect Software. Versions affected Up to (excluding)
23.9.8Up to (excluding)
23.9.8Details Authentication bypass using an alternate path or channel to gain unauthorized access to confidential information or critical systems. Improper limitation of a pathname to a restricted directory (“path traversal”) via a Zip Slip attack. Exploitability Score 3.9 1.7 Vector CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:C/C:H/I:H/A:H CVSS:3.1/AV:N/AC:L/PR:H/UI:R/S:C/C:H/I:H/A:H Impact Score 6.0 6.0 NVD Published Date 02/21/2024 02/21/2024 NVD Last Modified 02/22/2024 02/22/2024 Reference CVE-2024-1709 Detail CVE-2024-1708 Detail Have these vulnerabilities been exploited?
Yes. CVE-2024-1708 and CVE-2024-1709 have been exploited and, due to that evidence, have been added to the Known Exploited Vulnerabilities Catalog by CISA. Trend Micro says that multiple cybercrime groups, including the Black Basta and B100dy ransomware groups, have started exploiting the flaws.
CISA has directed that all federal civilian Executive Branch agencies must address vulnerabilities identified in this catalog by a specified due date, which for CVE-2024-1709 is Feb 29, 2024.
For detailed information and updates on CVE-2024-1709 and CVE-2024-1708, refer to the official CVE database and the advisories provided by ConnectWise and CISA.
How to use Ordr to detect and respond to this threat
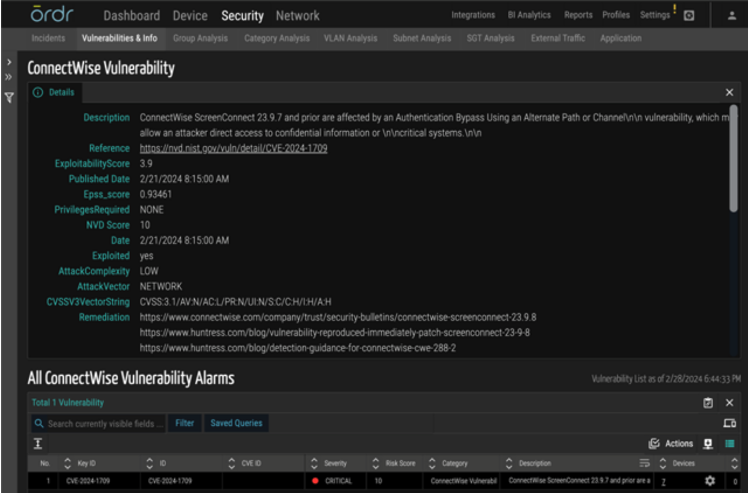
- Ordr updated its vulnerability database for all customer instances with these latest ConnectWise ScreenConnect CVEs for early identification and patching.
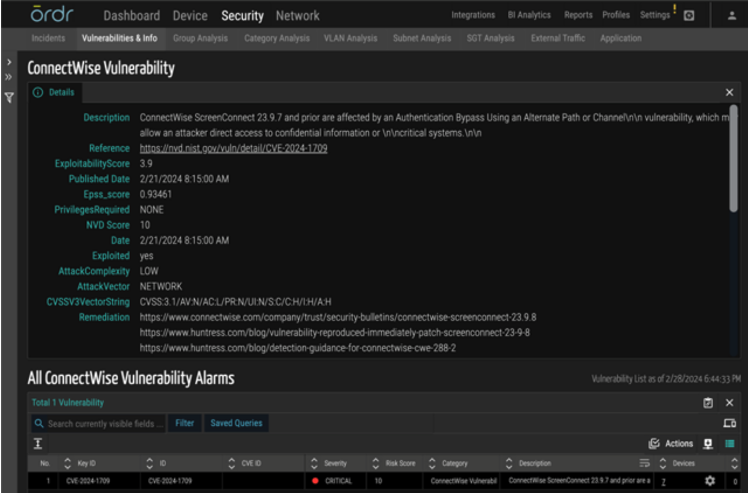
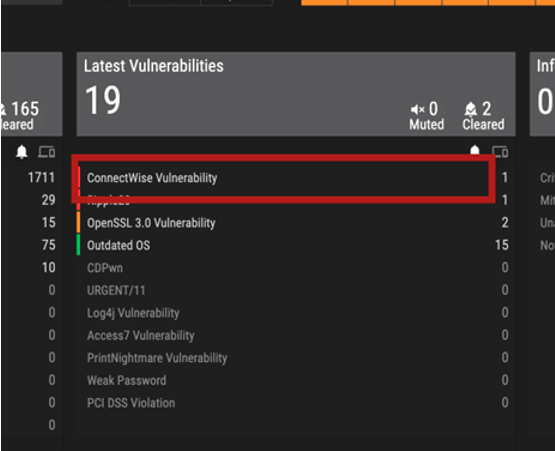
- Ordr added a new alert type in the “Latest Vulnerabilities” threat card as an easy visual indicator. Ordr analyzes the total software installed on all devices, checks for this specific version and matches with this vulnerability after a quick lookup of affected devices.
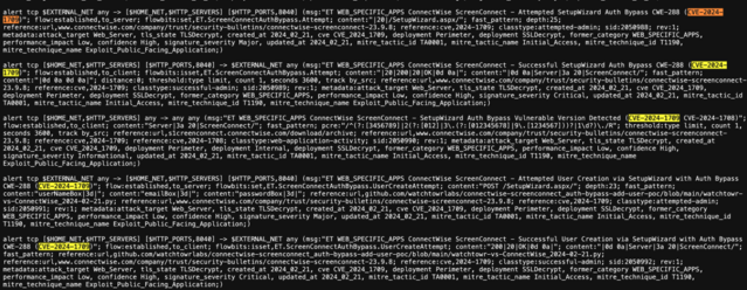
- Ordr updated its IDS rules corresponding to the exploitation of these vulnerabilities for real-time detection. As a result of this update, Ordr’s IDS engine will automatically look for relevant signatures and add a visual indication in the Ordr security page incident card if there is a match with the signature on the packet stream.
Ordr detection details and CVE lookup
The following are ways to identify if your organization has been exposed to these vulnerabilities and how to mitigate them.
Vulnerability mapping of impacted devices:
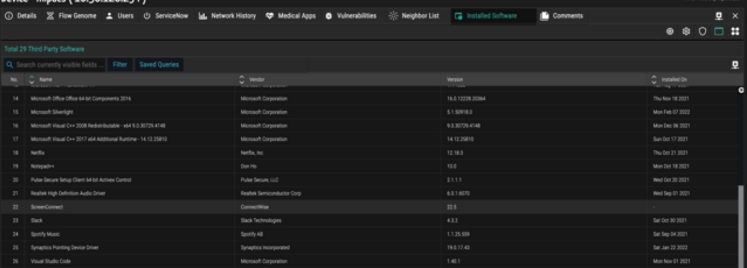
- Ordr provides visibility into all the devices running ConnectWise applications by mapping applications collected via Ordr Software Inventory Collector or 3rd party integrations like EDR, MDM, MSFT-AD, and others.
- Ordr also maintains a list of all the software packages installed on the endpoints with exact version numbers and a time stamp on which it was installed and last updated.
- Ordr matches the software version number against the various vulnerability databases to identify vulnerable versions of ConnectWise ScreenConnect applications.
This information can be looked up easily in the following ways:
- Latest Vulnerabilities Card: All devices running a vulnerable version of the software are highlighted in the Ordr Vulnerabilities and Info page in the Latest Vulnerabilities card.
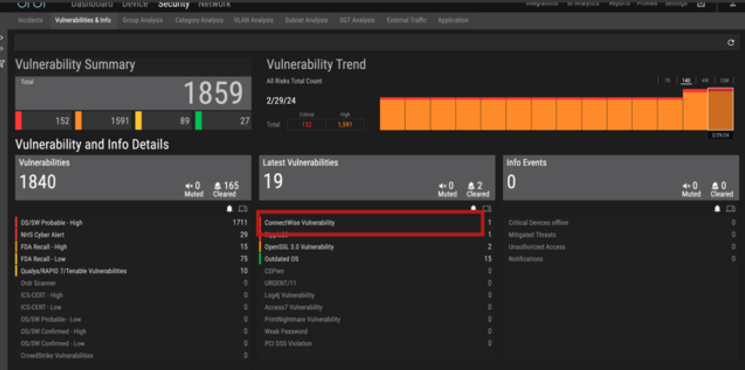
- Global CVE Search: For easy lookup in just a click, customers can search for the CVE ID corresponding to ScreenConnect vulnerabilities directly from the global CVE search in the Ordr main dashboard page.

Real-time detection of exploits using IDS, behavioral violation, and threat correlation:
The Ordr IDS engine detects this specific vulnerability using analysis of packets transacting over the wire. Ordr IDS signatures have been updated to detect ConnectWise ScreenConnect software exploitations.
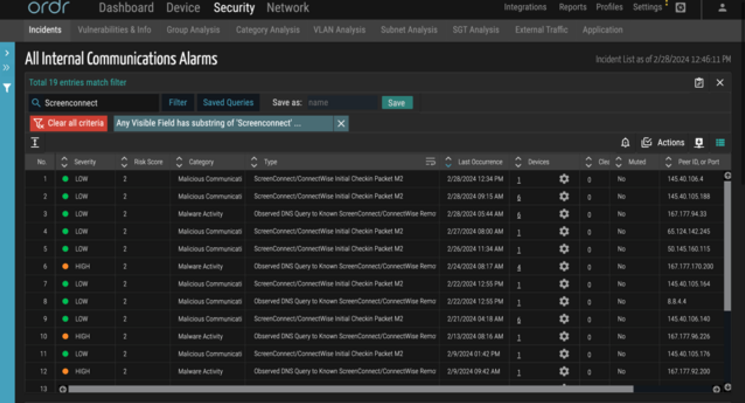
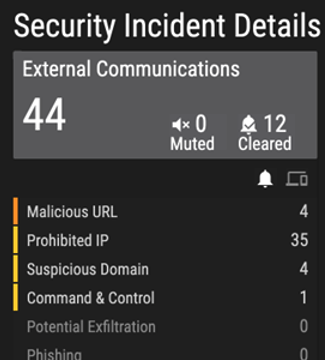
Generate alerts based on communication malicious IPs/URLs: Ordr’s external IP/IOC tracks every communication to prohibited IP/URLs in real-time. Ordr uses a continuously updated, cloud-based threat intelligence platform and all malicious communications alerts are marked accordingly in the Ordr Security Threat Card.
Mitigation actions to perform if detected:
To mitigate the risks associated with CVE-2024-1708 and CVE-2024-1709, several strategies are recommended:
- Update ConnectWise ScreenConnect software: Ensure that you are using the latest version of ConnectWise ScreenConnect above version 23.9.8. Updates often include patches for known vulnerabilities, which can prevent exploitation.
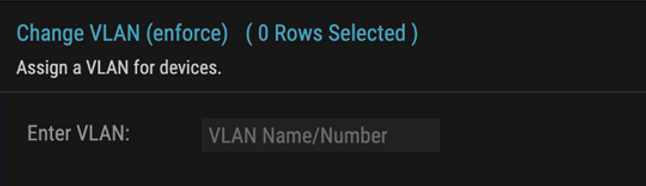
- Reactive rapid threat containment: Ordr has the capability to rapidly isolate the affected devices if it is deemed to have this vulnerability by putting the device in a quarantine VLAN, or denying its connection to the network using automation with a single click. This automation works with almost any networking, switch, or wireless controller vendor.
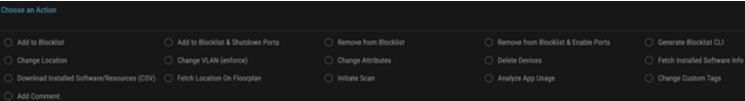
- Pro-active protection: Even if a breach happens, mission-critical assets (medical devices, industrial controls, etc.) can be protected using Ordr-enabled policies such as quarantining, or limiting communications to specific assets over certain protocols.
Ordr supports integration with multiple industry-leading NAC vendors.
- Stay Informed and Respond Quickly: Regularly check for updates from ConnectWise and security advisories from cybersecurity researchers and organizations like CISA. Responding quickly to vulnerabilities by patching can significantly reduce the risk of exploitation.
Ordr’s Call to Action for Customers
Customers are requested to monitor their environment and quickly identify the presence of the ConnectWise ScreenConnect CVEs mentioned using Ordr’s easy lookup methods, then Patch/Remediate them promptly to safeguard their organization against this rapidly known and exploited vulnerability.
Please get in touch with Ordr customer support for any queries or guidance.
Pandian Gnanaprakasam
Pandian has more than 20 years of product and engineering leadership experience and is also a serial entrepreneur. Before founding Ordr, he was the Chief Development Officer at Aruba, responsible for all of engineering and product management functions. Aruba, an enterprise mobile wireless company, was acquired by HPE for $3 Billion in March 2015. Before Aruba, Pandian served as the head of engineering for Cisco’s multi-billion-dollar Wi-Fi business unit and before that as VP of engineering for low-end switching product lines. He graduated with a master’s degree in Electrical Engineering from IIT, Chennai, India and holds several patents to his credit in various networking technologies.
Interested in Learning More?
Subscribe today to stay informed and get regular updates from Ordr Cloud
Ready to Get Started?
-
NewsOrdr Sees Increasing Industry Demand for Connected Device Security
…Technology Group. It has become harder and harder for resource-constrained IT and security teams to ensure they have a full understanding of their attack surface – and for them to…
Ordr Sees Increasing Industry Demand for Connected Device Security
3Min ReadSANTA CLARA, Calif., Aug. 30, 2023 /PRNewswire/ — Ordr, the leader in connected device security, today shared that it has experienced a significant increase in industry demand for its connected device security platform. Ordr enables security and IT teams to discover and secure every connected asset across their whole organization – from laptops and traditional IT equipment, to especially vulnerable Internet of Things (IoT), Internet of Medical Things (IoMT), Operational Technology (OT), and Cyber-Physical Systems.
“With industries as diverse as healthcare, manufacturing, financial services, smart cities, government and higher education coming to depend on connected devices to conduct their daily operations, it is no surprise that security has become a top priority,” said Jim Hyman, CEO of Ordr. “Organizations need the granular visibility that Ordr delivers, enabling teams to see what devices are connecting to their network, where they are connected, and what they’re doing when connected. It’s only with this real-time context that organizations can accurately identify their complete attack surface and mitigate risks via automated policies.”
Ordr’s AI-powered platform gives organizations a single source of truth for every connected device, revealing the entire attack surface, including vulnerabilities, exploits and anomalies. With the digital transformation-driven expansion of devices across industries, the number of connections that must be secured by an organization increases dramatically every day. In addition, in industries such as healthcare and manufacturing, connected devices have a long lifecycle, often outliving the operating system and security software installed on it and creating an instant security issue.
“Enterprises today are embracing Zero Trust as a modern cybersecurity strategy, but extending it to connected devices including IT, IoT, IoMT and OT can be increasingly challenging. We’ve been seeing great momentum bringing together our extensive cybersecurity experience with Ordr’s technology to discover every asset in the network, identify the attack surface, and automate the creation of segmentation policies to secure them. We look forward to our continued partnership with Ordr to further strengthen our customers’ security posture,” said Mark Grassmann, Cybersecurity Practice Principal, Alchemy Technology Group.
It has become harder and harder for resource-constrained IT and security teams to ensure they have a full understanding of their attack surface – and for them to have the proper policies in place to mitigate those situations. The visibility and control Ordr brings is helping reduce risks, and decrease incident response by hours, particularly when context is used to enrich CMDB, SIEMs, XDRs and security operations tools.
Ordr’s industry momentum includes:
Customer Growth
- Ordr continues to maintain its leadership position in healthcare while expanding its footprint in critical markets like manufacturing, financial services, higher education and government. Ordr enterprise ARR growth increased by 249% from 1H 2022 to 1H 2023.
Industry Recognition
- Ordr was named to the 2023 Startup 50 list, recognizing innovative technology companies that are already solving real industry problems.
- Analyst firm Enterprise Management Associates (EMA) named Ordr a “Leading Security Visionary” in its annual Vendor Vision Report.
- Ordr was selected as a 2023 Intellyx Digital Innovator Award winner by industry research firm Intellyx.
- The company was named one of the “10 Coolest IoT Security Companies: The 2023 Internet Of Things 50” by publication CRN.
- Industry publication ChannelPro named Ordr a 2023 “Vendor on the Vanguard.”
- The Ordr platform was awarded a “2022 IoT Excellence Award” in early January 2023 by IoT Evolution.
- The company was named a “Soonicorn” by Tracxn in its “Internet of Things Infrastructure Startups 2023” list of top IoT companies to watch.
Product Innovation
- Ordr recently announced version 8.2 of its platform, including new integrations with leading mobile device management, endpoint detection and response, threat intelligence, and Zero Trust providers.
- Ordr was recognized as a representative vendor in the 2023 Gartner Market Guide for Cyber-Physical Systems Protection Platforms and a July 2023 report by Gartner on Reference Architecture for Integrating OT and Modern IT.
- Ordr was recognized as a representative vendor in the 2023 Gartner Market Guide for Medical Device Security Solutions.
- Ordr was also included as a representative vendor for Cyber Asset Attack Surface Management category in the Gartner Hype Cycle for Security Operations 2023, and the Gartner Hype Cycle for Workload and Network Security 2023,
- Ordr was recognized as a top performer for an unprecedented fourth year by KLAS Research in its recent “Healthcare IoT Security 2023: An Update on Vendor Performance and Deep Adopter Utilization” report.
Industry-Leading Partnerships and Integrations
- GE HealthCare and Ordr teamed up to deliver broad visibility, performance monitoring, security, and governance of all clinical assets on GE’s CARESCAPE network, providing customers with enhanced self-management capabilities for their critical patient care devices.
- A new integration between Ordr and ServiceNow was announced, helping customers to quickly, easily, and reliably populate their CMDBs with third-party data, enabling data quality, timeliness, and scalability.
- Ordr partnered with Dubai-based Spire Solutions, the Middle East & Africa region’s leading cybersecurity solution provider and value-added distributor (VAD).
- The company partnered with U.K.- based Next Generation Security (NGS), a specialist cybersecurity reseller providing consultancy, support, and managed services.
- Ordr teamed with Sodexo Healthcare Technology Management to create a managed HTM and cybersecurity solution combining the strengths of Ordr’s connected device security platform with Sodexo’s healthcare technology management (HTM) services expertise.
- Ordr also named CDW and World Wide Technology (WWT) as its 2022 Partners of the Year, reinforcing the importance of both partnerships to the company and its customers.
Contact us for more information about how Ordr can help teams discover and secure every connected device across their organization.
Interested in Learning More?
Subscribe today to stay informed and get regular updates from Ordr Cloud
Ready to Get Started?