Search Results:
”Quiz 2024 SAP C-ARSOR-2308: Marvelous SAP Certified Application Associate - SAP Ariba Sourcing Valid Dumps Book 🐮 Open ▷ www.pdfvce.com ◁ and search for ➥ C-ARSOR-2308 🡄 to download exam materials for free 🏑C-ARSOR-2308 Customizable Exam Mode”
-
 BlogOrdr and Mayo Clinic: Securing IoMT and Health Tech Devices
BlogOrdr and Mayo Clinic: Securing IoMT and Health Tech Devices…and management from the pre-purchase stage to decommissioning Tools Deployment: Creating a security specific manual for devices, documenting what tools need to be deployed for different device types and models Fleet…
Customer Story
Ordr and Mayo Clinic: Securing IoMT and Health Tech Devices
3Min ReadBy Matilda Ortiz
Securing IoMT and HIoT Assets with Mayo Clinic. From new cybersecurity frameworks to patch management, learn how Mayo Clinic overcame unique challenges of securing IoMT and HIoT assets. While watching Keith Whitby, Section Head of Healthcare Technology Management Cybersecurity and Operations at Mayo Clinic, and Pandian Gnanaprakasam, Chief Product Officer at Ordr, discuss strategies for securing connected devices and HIoT in a recent webinar, I found the following to be insightful information that you can apply to your organization’s cybersecurity efforts.
Gaps in Medical Device Security
One of the first steps in securing IoMT and healthcare technology (health tech) devices is accounting for the gaps in medical device security. Evaluating equipment coming in, understanding the security risks related to those, and building a plan of mitigating controls that should be applied to equipment are all important aspects of device security, but they must be operationalized.
At Mayo Clinic, previous security assessments were done on an asset by asset basis. This lack of operational framework limited the implementation of device security procedures. Once Mayo Clinic created a standardized process across the organization, the framework could be followed for all medical equipment and new IoT and OT devices.
The Unique Nature of Medical Devices and Health Tech
Medical equipment, systems, and health tech are different from standard IoT and IT systems. Hospitals must follow regulatory guidelines from the U.S. Food and Drug Administration (FDA), College of American Pathologists (CAP) and Joint Commission on Accreditation of Healthcare Organizations (JCAHO), while medical devices in physicians’ offices do not have to follow the same rules. HloT devices come with their own unique challenges, from unsupported devices to service keys being required.
Security Challenges: Size and Scope
Medical organizations can span large geographical areas, including multiple states and hundreds of buildings. They can also have tens of thousands of connected medical devices, hundreds of vendors and thousands of models. The magnitude of medical device networks challenges IT teams to efficiently secure many devices at once. Networks of devices can have inventory discrepancies, and mismatched data from their CMMS and NAC.
Medical devices have complex systems that require intensive work to patch and manage vulnerabilities. Part of the process of setting a framework for securing health tech devices involves figuring out who will be implementing security standards and applications. Health tech devices need both specially trained IT technicians and unique applications to deploy security solutions.
Mayo Clinic: HTM Role in Cybersecurity
At Mayo Clinic, the cybersecurity team in Healthcare Technology Management is the operational arm of IT. The team has developed a structured system and standardized approach to securing medical equipment and health tech systems. They ensure equipment meets organizational and cybersecurity requirements throughout its lifecycle.
- Core Team: Mayo Clinic’s Core Team of HTM Cybersecurity developed a security framework for IoT and health tech based on National Institute of Standards and Technology (NIST) and Association for the Advancement of Medical Instrumentation (AAMI) standards. They also developed a HTM vulnerability management program guide, so that when a vulnerability is found, there is a clear process for remediation.
- Information Security Engineers: Besides technicians, the HTM team also has HTM associate infosec engineers, who create vulnerability management procedures, apply controls to medical devices and add new equipment to Mayo’s network.
- SPAD: The Security, Privacy, Architecture, Data team, or Security Assessment Team manages medical device purchases, device intake assessments, and helps to construct security lifecycle profiles at Mayo Clinic.
Cybersecurity Execution
Over the past two years, the HTM Cybersecurity Program has added significant security value, improving intake process efficiency, establishing an algorithm to calculate and track security risks, and more.
Mayo Clinic developed their IoT/health tech device security through proactive security, building upon multiple areas of cybersecurity, including:
- Policy & Process: Setting device security standards and leveraging known security incidents, regulatory compliance as well as internal audit observations
- Lifecycle Profile: Addressing security issues within the equipment lifecycle, creating Security Lifecycle Profiles that provide a roadmap for device security and management from the pre-purchase stage to decommissioning
- Tools Deployment: Creating a security specific manual for devices, documenting what tools need to be deployed for different device types and models
- Fleet Risk Assessment: Adopting a fleet approach rather than device by device security
- Vulnerability Management: Maintaining device security, tracking vulnerabilities and prioritizing remediation
- SPAD: Initial intake triage and categorization of hardware and software, and routing those devices to the appropriate review groups
- Patch Management: Deploying a medical device patch installation automation utility tool
- Training & Industry workgroups: Participating in industry workgroups to contribute medical device security knowledge
How Ordr Can Help
Mayo Clinic identified Ordr as a key tool to execute and automate security operations. Ordr is able to improve data quality for asset inventory, detect networked devices, classify devices, provide insights into connected device actions and help micro-segmentation efforts.
The Ordr Systems Control Engine (SCE) gives organizations the power to enable visibility and security of their network-connected devices, with a simple and powerful solution to identify, classify, profile the behavior and risk and automate action for every network-connected device in the enterprise. To learn more about how Ordr can enable an effective IoT security strategy for your organization, request a demo today to start the conversation.
Matilda Ortiz
Interested in Learning More?
Subscribe today to stay informed and get regular updates from Ordr Cloud
Ready to Get Started?
-
 NewsOrdr Integrates With Cisco’s Flagship Catalyst 9000 Series Switches
NewsOrdr Integrates With Cisco’s Flagship Catalyst 9000 Series Switches…real-time asset inventory, address risk and compliance and accelerate IT initiatives. Ordr is backed by top investors including Battery Ventures, Wing, and TenEleven Ventures. For more information, visit www.ordr.net and…
Ordr Integrates With Cisco’s Flagship Catalyst 9000 Series Switches
Simplifies Deployments and Accelerates Cisco ISE and SDA Initiatives
3Min ReadSanta Clara, CA – May 3, 2022 – Ordr, the leader in connected device security, announced the availability of the Ordr Sensor as a hosted application on the Cisco Catalyst 9000 series switches. The company’s latest integration with Cisco extends seamless visibility, comprehensive insights and security for connected devices in every environment – including data center, campus, and branch offices. Ordr and Cisco have a deep and long standing partnership, in which Ordr provides deep visibility and context that enables customers to leverage the full power of Cisco’s infrastructure – including Cisco Meraki, Cisco Identity Services Engine (ISE), Cisco Software-Defined Access (SDA) and Cisco Trustsec – to secure their IT, IoT (Internet of Things), OT (Operational Technology) and IoMT (Internet of Medical Things) devices.
“You cannot secure the modern enterprise without understanding what devices are connected to your network, what they are doing, and what vulnerabilities they have,” said Pandian Gnanaprakasam, Chief Product Officer and co-founder of Ordr. “It has been operationally challenging for some organizations to gain this level of visibility for all devices, in all locations. Now, in any environment with Cisco Catalyst 9000 series switches, Ordr enables IT organizations to immediately see and secure all these devices.”
Ordr makes it easy to keep the connected enterprise secure by showing customers exactly what devices are in their environment, the systems they communicate with, and the risks they bring, while providing automated policies to secure them. Ordr not only identifies devices with vulnerabilities, weak ciphers, expired certificates, and active threats, but also uses machine learning to continuously baseline normal behavior. The combination of device and risk insights, behavioral analysis, and automated policy creation accelerates Cisco ISE and SDA deployments.
“Embedding Ordr within the Cisco Catalyst 9000 allows customers to discover and secure connected devices in locations where it is not possible or not practical to deploy a hardware sensor, such as a branch office or other remote location. This, combined with Ordr’s strengths in accelerating Cisco ISE and SDA deployments, will streamline Zero Trust security for every organization,” said Chris Kuhl CTO and CISO, Dayton Children’s Hospital.
“The explosive growth of connected devices means companies are more invested than ever in visibility and security solutions,” added Rob Parsons, Director, Network and Security Practice/Portfolio at Insight. “Remote offices are often underserved by security because they lack integration with core security tools. Ordr’s connected device security platform and Cisco’s industry-leading switching products combine to create a powerful value proposition for our clients. The results are simplified deployments, comprehensive visibility across every office, and accelerated Zero Trust and Cisco ISE initiatives.”
With this integration, even in smaller office locations, enterprises gain comprehensive visibility into connected assets, risks, network connectivity, device behavior, and utilization, as well as the ability to apply segmentation to the network edge.
Key Ordr and Cisco Catalyst 9000 Integration Benefits
- Secure More Devices: Extend Ordr to secure connected devices in data center, campus, branch office, or other remote locations.
- Quick Deployment: The Ordr sensor is deployed in a matter of minutes as a pre-packaged Docker container application hosted on any Cisco Catalyst 9000 switch, and can be easily deployed to hundreds of switches from the Cisco DNA Center.
- Reduced Footprint and Cost: By leveraging existing Cisco Catalyst 9000 switches as distributed Ordr sensors, the deployment footprint and costs are reduced.
- No Performance Impact: Ordr takes advantage of Cisco Catalyst 9000’s dedicated application hosting compute, storage, and memory – so there’s no impact to switch performance.
Accelerating Security Across the Cisco Product Suite
Ordr’s close relationship with Cisco includes integrations with multiple products, including the Cisco ISE, Cisco SDA, Cisco Catalyst 9000 switching family, Cisco Meraki, Cisco TrustSec, Cisco Secure Network Analytics (Stealthwatch), and Cisco Prime Infrastructure.
In addition, Ordr has recently become a Cisco Meraki Ecosystem Partner. Now available on the Cisco Meraki Marketplace, Ordr helps customers analyze their Meraki cloud data to see, know, and secure all connected devices, across all campus, branch, small office/home office (SOHO), and VPN connections.
Ordr’s deep integrations across the Cisco portfolio help customers add the end-to-end visibility and security needed to accelerate the deployment of Cisco ISE and SDA solutions. Ordr’s device classification, network awareness, security intelligence, and ability to auto-generate enforcement rules simplify the process of creating, provisioning, and managing an IoT, IoMT and OT segmentation policy.
For more information about how Ordr can help strengthen the visibility, security and overall management of all your Cisco deployments, please visit www.ordr.net/partners/cisco.
About Ordr:
Ordr makes it easy to secure every connected device, from traditional IT devices to newer and more vulnerable IoT, IoMT, and OT. Ordr Systems Control Engine uses deep packet inspection and advanced machine learning to discover every device, profile its risk and behavior, map all communications and protect it with automated policies. Organizations worldwide trust Ordr to provide real-time asset inventory, address risk and compliance and accelerate IT initiatives. Ordr is backed by top investors including Battery Ventures, Wing, and TenEleven Ventures.
For more information, visit www.ordr.net and follow Ordr on Twitter and LinkedIn.
Interested in Learning More?
Subscribe today to stay informed and get regular updates from Ordr Cloud
Ready to Get Started?
-
 BlogReducing Attack Surface Risks with Accurate, Automated Inventory
BlogReducing Attack Surface Risks with Accurate, Automated Inventory…And when incidents do occur, it is challenging for security and IT teams to quickly identify which assets are impacted and understand the connections to other devices on the network,…
Blog
Reducing Attack Surface Risks with Accurate, Automated Inventory
Strengthening the Enterprise Security Posture
3Min Read
By Srinivas Loke
The definition of a cyber asset has evolved significantly, expanding beyond network devices to encompass a wide array of elements such as users, applications, SaaS, and cloud resources. The shift to a distributed, hybrid workforce further complicates matters as administrators need visibility into assets that traditional, on-premises security controls do not protect. As a result, security and IT teams are now tasked with managing hundreds, thousands, and even millions of cyber assets to protect their organizations from cybersecurity threats. Unfortunately for CISOs and their teams, this broadening definition has expanded the cyber asset attack surface, making it larger and more diverse, creating new challenges for enterprise security teams, including:
- Incomplete asset inventory leading to network blind spots, particularly with IoT, OT, and IoMT devices.
- Duplicate asset entries and inaccurate inventories due to reliance on tracking assets using IP addresses.
These challenges hinder incident response and make it difficult to understand—and limit—an attack’s blast radius. They also complicate the task of identifying security gaps, vulnerabilities, and prioritizing cyber risk management. And when incidents do occur, it is challenging for security and IT teams to quickly identify which assets are impacted and understand the connections to other devices on the network, leaving them to rely more on guesswork than data-driven analysis.
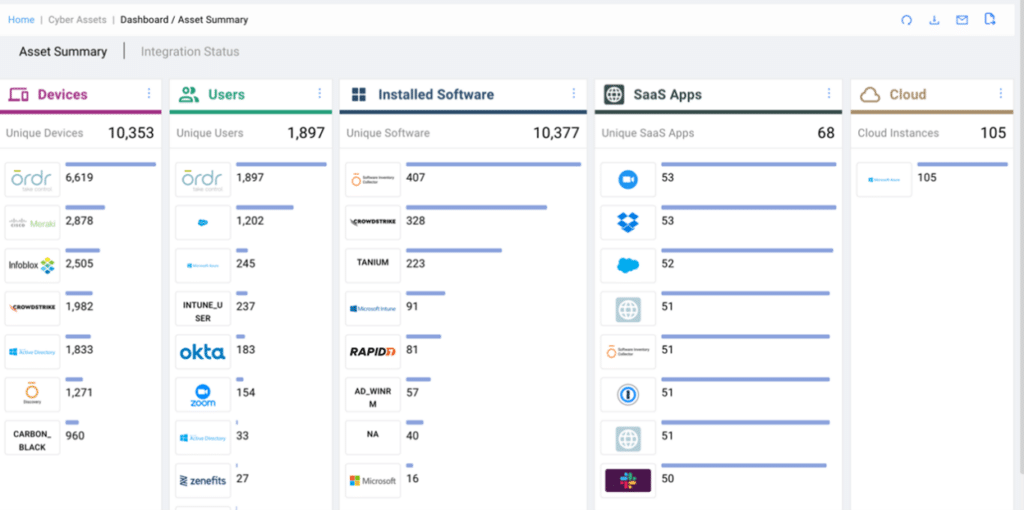
OrdrAI CAASM+ Enables Enterprise Teams to Improve Their Security Posture and Reduce the Attack Surface
Going beyond API-only solutions, OrdrAI CAASM+ provides security teams with complete visibility and data for all assets, including devices (IT, IoT, OT, IoMT), cloud, installed software, SaaS, and users. Then, utilizing a combination of over 180 security and IT ecosystem integrations a proprietary discovery technology and AI/ML classification, Ordr empowers security teams with a unified platform to address critical asset management questions such as:
- How many cyber assets do I have?
- What software is running on my devices?
- What is the blast radius of a compromised cyber asset?
To help enterprise organizations maintain up-to-date asset information and enhance overall security posture, Ordr recommends integrating with a variety of data sources, including:
- CMDB
- IPAM
- EDR
- MDM
- AWS for cloud assets
- Network infra integration (SNMP)
- Active querying from Ordr
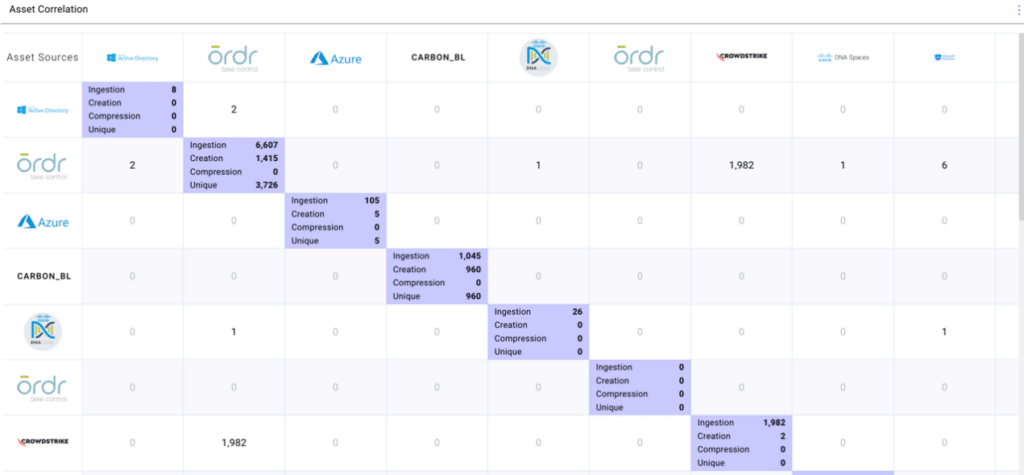
OrdrAI CAASM+ Deduplicates, Normalizes, and Aggregates Asset Data and Correlates it into a Single Source of Asset Intelligence
Merely seeing an organization’s entire asset inventory is not enough. What enterprise organizations need is comprehensive, accurate asset visibility coupled with in-depth asset context to tackle critical security and IT use cases head-on. To provide this data, Ordr uses a multi-level de-duplication technique to consolidate and compress the asset data based on the set of attributes to provide an accurate asset count. This eliminates issues with duplicate assets such as when data is collected from EDR using MAC addresses and VA using IP addresses, resulting in duplicate entries.
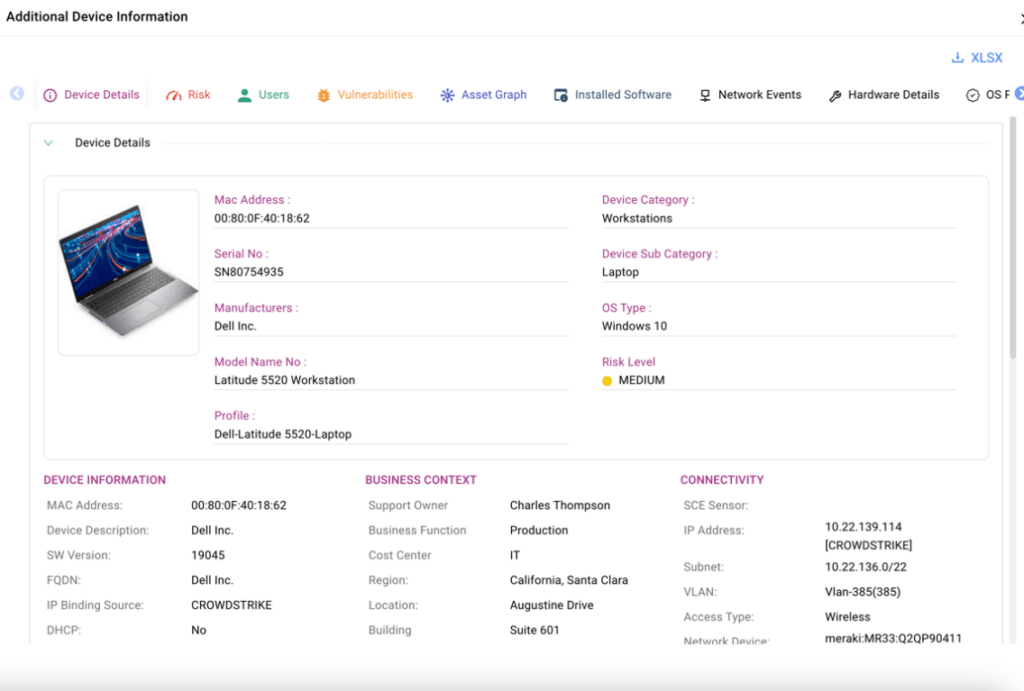
Tracking all assets independently and displaying this data within the platform, CAASM+ provides teams with the necessary asset insights to determine the blast radius of an exposed asset. The information is readily available in the user interface, as shown below, and can be accessed for any type of asset with a simple click of a button.
Using AI/ML Classification, Ordr Provides In-Depth Asset Context to Reveal Security Issues and Coverage Gaps in Asset Management
Over the last six years, Ordr has built a crowd-sourced asset repository—the Ordr Data Lake—comprising data from over 1.5 million different assets across networks from all industries. Leveraging our proprietary AI/ML technology, Ordr classifies and assigns a three-level hierarchy for every asset. This classification enables Ordr to assign a risk score based on business context and asset criticality. Additionally, it allows the enterprise security admins to easily find and identify security infrastructure gaps, eliminating guesswork by clearly defining security control boundaries. This allows teams to distinguish which devices require Endpoint Detection and Response (EDR) and which already have it installed. This differentiation is crucial, as it ensures that teams do not waste time on devices that cannot support EDR installation.
https://www.youtube.com/watch?v=FnNP0_QTxIwWhen starting from a foundation of comprehensive, accurate asset inventory, enriched with in-depth context and business insights, security teams can better address critical challenges in cyber asset visibility and management. OrdrAI CAASM+ empowers organizations by providing:
- Actionable asset data and detailed business insights, such as make, model, OS, serial number, connectivity and more. This data can be easily share with CMDBs and other IT tools to reconcile asset data and easily identify missing assets, update records, and remove outdated information.
- Generative-AI powered natural language search to easily obtain answers about your security posture and identifying security issues.
- Asset risk scores to prioritize and remediate risks and exposures based on asset context, CVSS scores, vulnerability exploitability, type of data (encrypted), location, and more.
- Streamlined remediation through automated workflows integrated with ITSM, SIEM, and SOC, ensuring actions are assigned to the appropriate device owner.
Do these challenges sound familiar? Schedule a meeting with our team of security experts to learn how you can leverage Ordr’s automated, accurate asset inventory management solution to proactively prioritize and reduce risks and exposures, streamline incident response, and enhance your overall security posture.
Thanks for joining us for another blog in our series on CAASM+ use cases. Stay tuned as we explore more of these critical use cases in the coming weeks and discuss how Ordr addresses them.
Srinivas Loke
Srinivas Loke is Vice President of Product Management at Ordr. Srinivas has a passion for cybersecurity with a deep understanding of network, end point, cloud and IoT security. Prior to Ordr, he led product teams at Aruba, Pulse Secure, FireEye and McAfee. He loves taking 1.0 products to the market and furthering cutting edge technologies that are solving customer problems.
Interested in Learning More?
Subscribe today to stay informed and get regular updates from Ordr Cloud
Ready to Get Started?
-
 BlogSee, Know, and Secure Your Asset Attack Surface
BlogSee, Know, and Secure Your Asset Attack Surface…growing larger, more complex, and more diverse; and the mix of hardware, software, and innovative new tools used to manage and secure those enterprises are pushing aside the legacy systems…
Security Strategy
See, Know, and Secure Your Asset Attack Surface
3Min Read
By Danelle Au

Learn about the new cyber asset attack surface management (CAASM) market category emerging in the cybersecurity industry and what it means to you. Then learn how Ordr helps you to see, know, and secure your enterprise’s unique and expanding attack surface to minimize cyber risk. Things move fast in tech. Enterprise infrastructure is growing larger, more complex, and more diverse; and the mix of hardware, software, and innovative new tools used to manage and secure those enterprises are pushing aside the legacy systems that have failed to keep up. The old saying, “You need a scorecard to keep track of the players” would apply but for the fact that the scorecard is probably out-of-date, too.
The CAASM is Growing
Just in case you weren’t paying attention, there’s a new market category—and associated acronym—that has emerged to describe a fast-evolving corner of the cybersecurity industry. Gartner, which coins terms faster than the Franklin Mint, saw activity reaching critical mass in addressing the need to track, secure, and manage the growing number of devices connecting to and comprising the modern enterprise, and defined a new category: cyber asset attack surface management, or CAASM (which you’ll probably want to pronounce like “chasm”).
Richard Stiennon, cybersecurity author and analyst, recently moderated a panel on CAASM as part of the Demo Forum, participated by Ordr’s VP Systems Engineering, Jeremy Haltom.
It’s good to see this space getting attention. Ordr’s mantra, “See. Know. Secure.” is a simple description of the CAASM approach needed to rein-in complexity to make it easier to secure. As enterprises get populated with devices, known and unknown, managed and unmanaged, the attack surface is also growing. That makes it harder for IT security and operations teams to do their jobs. You can’t protect what you can’t see, and it’s hard to know if the things you can see are compromised unless you have a clear understanding of what it is, what risks it brings, and how it is supposed to behave.
Without Visibility You’re Flying Blind
Absent a way to effect complete asset discovery, track the ephemeral nature of the attack surface in real-time, and manage those assets based on actual data that can tell indicators of compromise from a baseline of normal behavior, you are flying blind. And that’s not where a CTO, CISO, or CSO wants to be.
What’s interesting to us is that the Ordr System Control Engine was conceived as a solution to the challenges inherent with protecting connected systems and the networks they were connecting to. This was a big problem for healthcare organizations that rely on a mix of medical devices—the internet of medical things or IoMT—that defy traditional approaches to IT security and management. If a certain piece of equipment is operating with obsolete, unsupported software that makes it vulnerable to attack, there may be restrictions keeping IT from making any needed modifications. And if a device is in active use, it may be impossible to turn off.
Ordr SCE and the Power of Data
That was the challenge we set out to solve when Ordr was founded. But as Ordr gained traction in healthcare and other industries, our customers found that our platform was excellent at discovering and tracking assets wherever they were in the organization. We heard stories of hospitals that found equipment that had been missing for years, while others took the business intelligence they’d gathered from Ordr SCE to support asset requisition and allocation management decisions. That’s the power of data when it is complete, accurate, and in granular, contextual detail.
We know that the challenges associated with seeing, knowing, and securing cyber-assets are not going to diminish. At last count, devices were being acquired and attached to networks and the internet at more than 125 per second, with an expected 75 billion “things” connected by 2025. That’s a lot of devices, and for those organizations driving that growth through the adoption of IoT, IoMT, OT, and other connected devices, that’s a lot of attack surface to monitor, manage, and secure.
With Ordr You Aren’t Alone
So, whether you were aware of CAASM specifically or intuitively, you already know it has to be a part of an effective cybersecurity strategy. The good news is you don’t have to face the challenge alone. Get in touch with us and we’ll show you how you can see, know, and secure your cyber-asset attack surface with OrdrAI CAASM+.
Danelle Au
Danelle Au has more than 20 years of experience bringing new technologies to market. Prior to Ordr, she was CMO at Blue Hexagon, a deep learning for malware protection company, and CMO at SafeBreach where she helped build the marketing organization and and define the Breach and Attack Simulation category. Previously, she led strategy and marketing at Adallom, a cloud security company acquired by Microsoft. She was also Director, Security Solutions at Palo Alto Networks, driving growth in critical IT initiatives like virtualization, network segmentation and mobility. Danelle was co-founder of a high-speed networking chipset startup, co-author of an IP Communications Book and holds 2 U.S. Patents. She has an MSEE from UC Berkeley
Interested in Learning More?
Subscribe today to stay informed and get regular updates from Ordr Cloud
Ready to Get Started?
-
Knowledge BaseRipple20: How to identify and protect vulnerable devices
…been used and trusted for decades. They demonstrate the need for proactive protection and deep visibility. Ordr Systems Control Engine (SCE) is a solution for organizations that need to protect…
Ripple20: How To Identify And Protect Vulnerable Devices
5Min ReadIt’s one thing to hear about theoretical security vulnerabilities that could impact IoT devices. It’s another to know that serious security flaws have existed for decades in a software library that is widely used in the IoT ecosystem.
That’s exactly what happened in the case of Ripple20, a series of security vulnerabilities that impact hundreds of millions of IoT devices. This article explains what Ripple20 is, why it’s dangerous and how companies can help mitigate threats like Ripple20 within their network.
What is Ripple20?
Ripple20 is the name that security researchers at JSOF gave to a collection of vulnerabilities that they discovered within a software library first developed in the 1990s by a company called Treck. The library is a lightweight implementation of a TCP/IP stack, meaning that it provides the core functionality that devices need to connect to networks.
Researchers at the cybersecurity firm JSOF discovered the vulnerabilities in 2020. They named the vulnerabilities Ripple20 because of their potential to cause a “ripple effect” across supply chains of which IoT devices are a part. In other words, the vulnerabilities impact not just end-user devices (like printers or home security systems), but entire operational networks that include IoT hardware at any layer. For example, IoT sensors that help manage environmental conditions on a manufacturing floor and are affected by Ripple20 could have a ripple effect that compromises the security of “downstream” participants in the supply chain of which the facility is a part.
Although the Ripple20 vulnerabilities did not come to light until 2020, researchers believe that they have existed for at least twenty years.
What is Treck?
Treck is a nearly ubiquitous embedded TCP/IP that works well on devices with limited hardware resources. That feature made it a very popular solution for IoT devices, which typically lack the resources to run the more demanding types of software that are common on PCs or servers.
The library is consequently in widespread use, and likely places “hundreds of millions” of devices at risk, according to JSOF. Those devices represent a broad category of IoT use cases, from home and enterprise printers, to Industrial Control Systems (ICS), to healthcare equipment and beyond.
What are the effects of Ripple20?
As noted above, the Treck library impacted by Ripple20 powers the network communications of devices that use it. Because networking is at the core of device operations, Ripple20 vulnerabilities expose devices—and users who depend on them—to a range of potential attacks.
Perhaps one of the most serious is remote-code execution attacks, in which threat actors take control of an affected device in order to harvest private data from it or run malicious software on it. Making matters worse from a security standpoint, remote-code attacks can be executed from external networks, which means attackers need not have breached a company’s network perimeter or firewalls in order to exploit Ripple20 vulnerabilities.
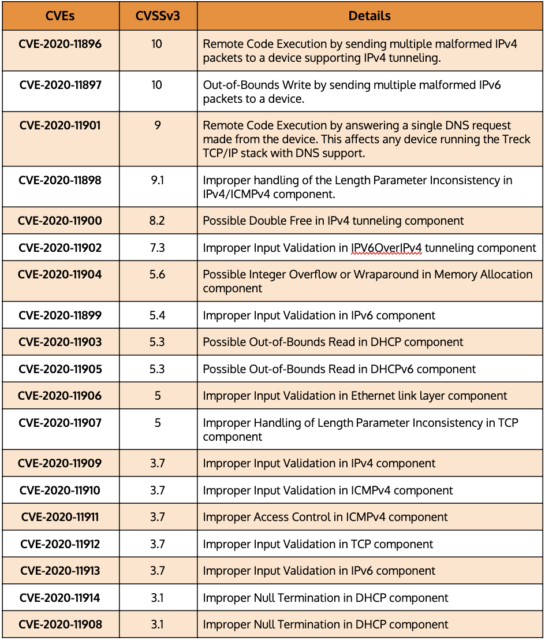
The following table displays a number of common vulnerabilities and exposures (CVE) that correspond to specific types of attacks and risks that have emerged from Ripple20.
CVEs that correspond to active Ripple20 attacks
In practice, Ripple20’s effects could include attacks such as the theft of personal data from Internet of Medical Things (IoMT) devices, or the interference with dosage levels distributed by such devices to patients. Or, if attackers use Ripple20 to take control of a manufacturer’s network, it could disrupt operations, leading to downtime and significant financial loss.
The list of potential attack scenarios could go on. The takeaway is that Ripple20 creates an unusually large and serious set of vulnerabilities that impact virtually every niche within the IoT ecosystem. JSOF has confirmed that Ripple20 affects IoT devices manufactured by fifteen specific vendors, including Baxter, Intel, Caterpillar, Cisco, Aruba, HP, and Xerox, but many others manufacturers’ products are likely to be at risk as well.
Identifying devices vulnerable to Ripple20
Because Ripple20 became publicly known only in 2020, many organizations are still in the process of assessing their exposure and risk. To do so, they must start by building an asset inventory within their infrastructure. Then, they must determine which devices are impacted by Ripple20.
There are two main ways to identify affected devices. One is to consult advisories from device manufacturers who have determined that their devices are impacted. But because not all manufacturers have issued advisories yet, equally important is proactive monitoring of devices in order to discover whether they are using the Treck TCP/IP stack and appear vulnerable to Ripple20. Ordr has developed novel techniques to discover devices that have Ripple20 vulnerabilities regardless of whether advisories from device manufacturers exist.
Once companies identify vulnerable devices, they can typically address the Ripple20 vulnerabilities by installing patches provided by device manufacturers. If a patch does not yet exist, the vulnerable devices can be taken offline until one becomes available or, at a minimum, segmented from other devices in order to mitigate the potential impact.
How to detect Ripple20
Because attackers can execute Ripple20 exploits from external networks, traditional firewalls and Network Access Controls (NACs), which filter traffic only along the boundary between the public Internet and a company’s internal network, provide little protection.
This is why novel Ripple20-detection techniques like those developed by Ordr are so important. In addition to looking for the presence of impacted Treck software on devices themselves, Ordr also baselines device behavior to determine malicious or suspicious patterns and will flag this activity. Ordr provides a level of protection against Ripple20 that a firewall and NAC solutions alone cannot deliver.
How to protect vulnerable devices from Ripple20
Although identifying devices that are impacted by Ripple20 and patching them is an obvious step for responding to the Ripple20 vulnerabilities, organizations must take broader steps to ensure that their networks are hardened against threats like Ripple20. That includes embracing the principles of Zero Trust security. It’s a safe bet that similar vulnerabilities exist in the wild but have not yet been discovered. Zero Trust helps ensure that your network will be resilient against such attacks, regardless of which form they take.
Zero Trust means that networks are configured in such a way that, whenever a new device appears on a network, or an existing device’s configuration changes, the device has no access to the network or the hosted resources until a security administrator has verified that the device should be granted access.
In addition, network administrators should adhere to several other best practices associated with Zero Trust:
- Do not rely on firewalls or private IP addresses to establish which devices are “safe.” Instead, identify each device that exists on a network and ensure that it can be trusted before you grant it access to network resources.
- Implement least-privilege access. Grant devices only the minimal access privileges they need to operate.
- Use Multi-Factor Authentication (MFA). MFA is a security enhancement that requires a user to present two or more pieces of evidence when logging in to an account.
- Implement microsegmentation. Grant access privileges to each device on a highly granular basis, rather than assigning broad access rights. Policies are tailored to the individual needs of each device on the network.
Proactive protection of IoT devices with Ordr
The Ripple20 vulnerabilities highlight just how much risk IoT and unmanaged devices face, even when they run software that has been used and trusted for decades. They demonstrate the need for proactive protection and deep visibility.
Ordr Systems Control Engine (SCE) is a solution for organizations that need to protect their network and devices from Ripple20 and other vulnerabilities. Ordr SCE can:
- Discover all network-connected devices.
- Identify vulnerable assets impacted by Ripple20.
- Detect and flag anomalous behavior using a built-in intrusion detection engine.
- Proactively protect devices from Ripple20 attacks by dynamically generating policies and enforcing them on next-generation firewalls or NAC solutions.
Interested in Learning More?
Subscribe today to stay informed and get regular updates from Ordr Cloud
Ready to Get Started?
-
PagesRetail and Hospitality
…SaaS apps, and users—critical for a modern retail and hospitality customer experience: Gain real-time, accurate asset data and insights for devices, users, applications, SaaS and cloud, including hard-to-discover IoT and…
- INDUSTRY
- RETAIL AND HOSPITALITY
Enable A Seamless Customer Experience By Securing Retail And Hospitality Assets
Ordr empowers retail and hospitality businesses to secure all assets to protect brand value and enable a positive customer experience.
REQUEST A DEMO
Secure, modern retail and hospitality environments in-store and online with comprehensive cybersecurity asset management
Expansion of Attack Surface
Most security solutions have blind spots with IoT and OT devices such as point-of-sale devices (PoS), smart displays and sensors used to deliver a seamless customer experience. Ordr offers comprehensive asset visibility and security tailored for every asset within tretail and hospitality environments.
Safeguarding PII and PCI data
The retail and hospitality sectors gather, process, and store significant volumes of sensitive customer data, including personally identifiable information (PII) and payment card data (PCI) that need to be protected. Ordr can identify assets with this information, and reduce the scope of compliance via segmentation.
Identifying and Responding to Threats
Identifying not only known threats, but also when an asset deviates from its normal behavior, is paramount for early threat detection and response. Ordr enables you to effectively detect anomalies, pinpoint malicious communications or active threats, and accelerate incident response.
SEE
Discover and Classify Every Asset
Ordr delivers real-time visibility into all devices, cloud assets, applications, SaaS apps, and users—critical for a modern retail and hospitality customer experience:
- Gain real-time, accurate asset data and insights for devices, users, applications, SaaS and cloud, including hard-to-discover IoT and OT
- See granular device details like manufacturer, model, serial number, OS, support owner, connectivity and more.
- Identify issues like rogue or banned devices, and devices with outdated operating systems
- Pinpoint security coverage gaps such as endpoints missing MDM/EDR agents
- Map and analyze risky communications between assets and to the Internet
- Enrich CMDB with real-time asset visibility

KNOW
Automatically Surface Your Risks & Exposures
Maintain a seamless customer experience and minimize business downtime by identifying and prioritizing top vulnerabilities and threats. Ordr provides retail and hospitality organizations with comprehensive visibility into the vulnerability landscape for both managed and unmanaged devices. Enable efficient incident response across global retail and hospitality teams with a prioritized list of vulnerabilities including risk scores and automated workflows assigned to the correct device owner. Detect known and unknown threats.
- Gain comprehensive coverage of all vulnerabilities, including those on IoT and OT devices
- Prioritize vulnerabilities based on multiple asset and organizational risk factors and automate remediation for the right owners
- Detect active exploits and risky communications with an integrated IDS and threat intelligence feeds
- Identify devices behaving abnormally, based on baseline known-good communications
SECURE
Segmentation To Manage Risks
In the retail and hospitality industry, segmentation is a cybersecurity best practice to reduce lateral movement and secure mission-critical assets. Accelerate your Network Access Control (NAC) and Zero Trust initiatives by deploying Ordr to establish segmentation policies tailored to your business requirements. Implement macro segmentation to isolate specific types of assets, while adopting Zero Trust segmentation to restrict vulnerable devices to baseline communications. Fine-tune policies based on enforcement points such as firewalls, NAC, or switches, optimizing security measures for your unique operational environment..
Accelerate NAC, Segmentation and Zero Trust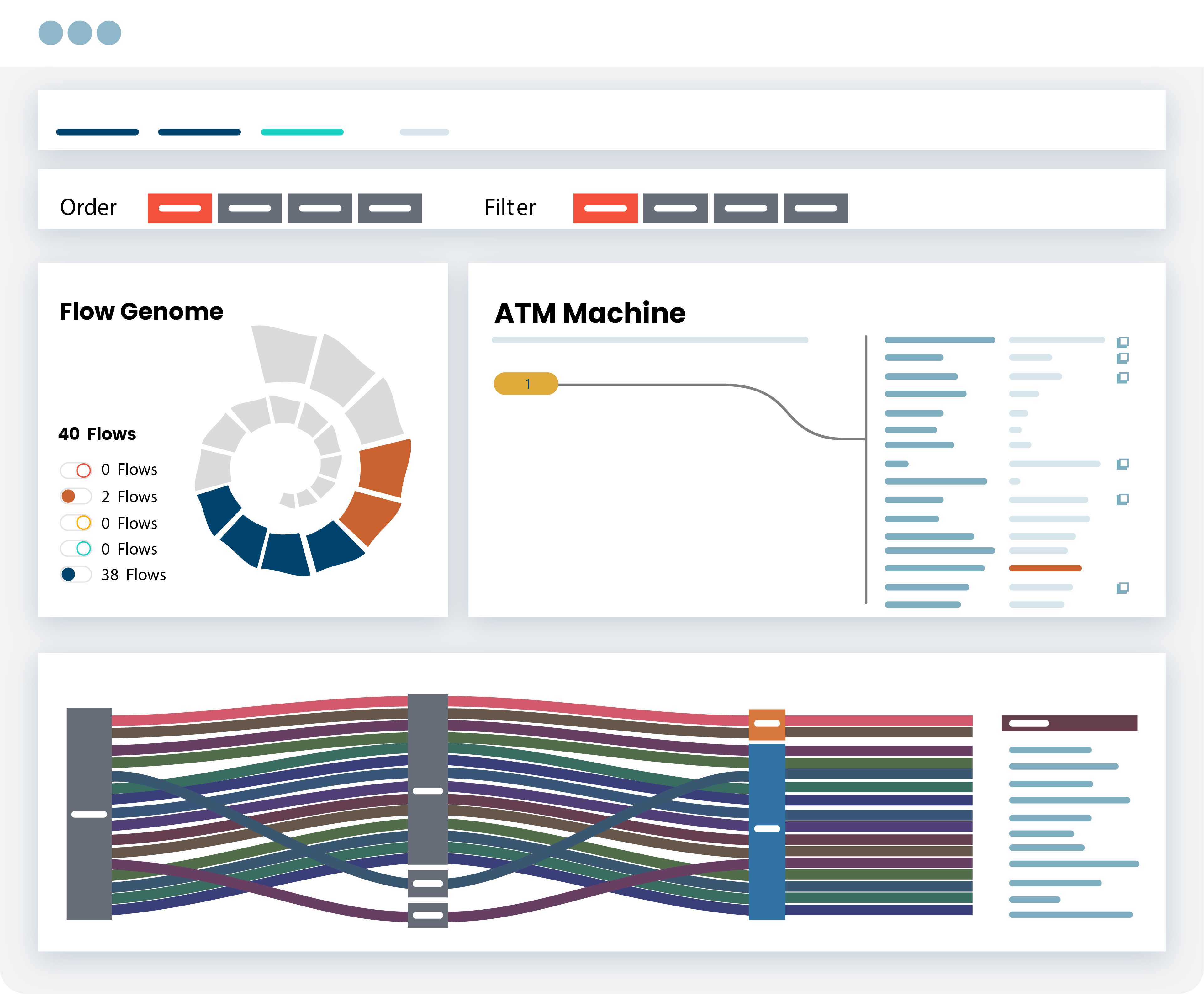
SECURE
Protect customer data and maintain compliance
Compliance can be a challenge for the retail and hospitality sectors, because of the myriad of assets that may include sensitive PII or PCI data. With limited resources, automation is key to efficiently managing security controls and coverage gaps. Automate inventory and identify assets with PII or PCI data. Simplify compliance across various frameworks, such as NIST, PCI DSS, and other standards with Ordr’s comprehensive reporting tools designed to streamline the compliance process. Dashboards and reports can be customized based on the business’s specific needs.
Automate Regulatory Framework Compliance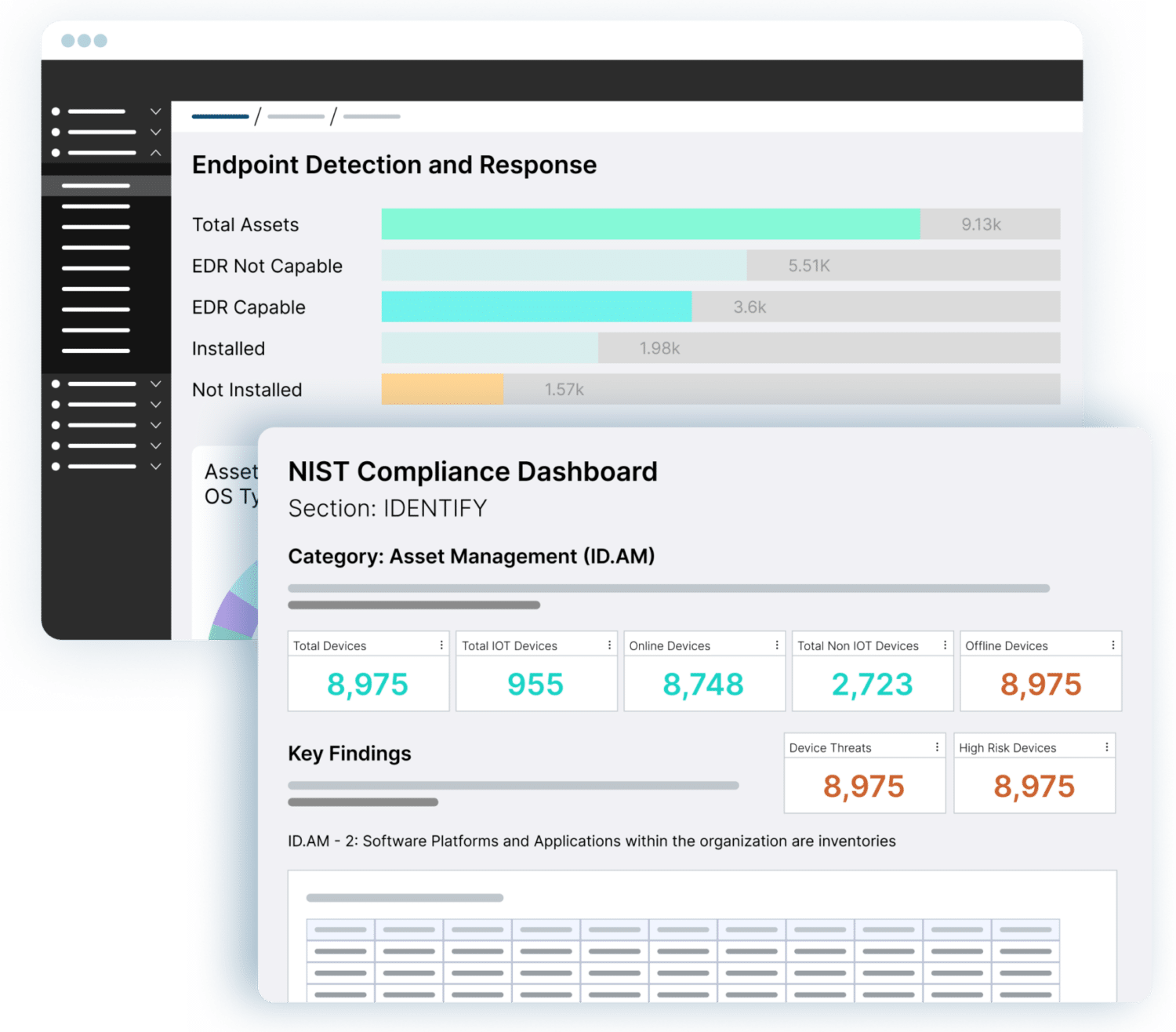
Ready to Start Securing Your Assets?
-
 BlogCISA Mitigation Guide for Healthcare Organizations: Part One
BlogCISA Mitigation Guide for Healthcare Organizations: Part One…Healthcare Officer Wes is responsible for driving Ordr’s engagements in healthcare. Previously he was the CTO for Imprivata, and prior to that VP and CTO at Sutter Health, a 26…
Healthcare Security
CISA Mitigation Guide for Healthcare Organizations: Part One
4Min Read
By Wes Wright
A lack of medical device and cyber asset visibility puts hospitals and healthcare organizations at risk. Our experts break down the recently published CISA threat mitigation guide to show how Ordr helps follow the recommendations. Build your cybersecurity strategy on a solid foundation of asset visibility and segmentation
On November 20, 2023, the Cybersecurity Infrastructure and Security Agency (CISA) issued guidance for healthcare delivery organizations (HDOs) struggling to secure their data and systems against a growing and pernicious onslaught of attacks from threat actors across the globe. The purpose of CISA’s Mitigation Guide: Healthcare and Public Health (HPH) Sector is to articulate “best practices to combat pervasive cyber threats affecting the Healthcare and Public Health (HPH) Sector.”
The Mitigation Guide follows on the heels of CISA’s Cyber Risk Summary: Healthcare and Public Health (HPH) Sector Calendar Year 2022 in which the agency identified six common weaknesses in healthcare cybersecurity, including:
- Web application vulnerabilities
- Encryption weaknesses
- Unsupported software
- Unsupported Windows operating systems (OS)
- Known exploited vulnerabilities (KEVs)
- Vulnerable services
To help HDOs and other healthcare enterprises create and execute more effective cybersecurity strategies to address these weaknesses, the Mitigation Guide calls out strategies for improving security, with focus areas for each. We’ll be analyzing each of the guidelines provided by CISA in a series of blogs, starting with the first Mitigation Strategy: Asset Management and Security.
Mitigation Strategy #1: Asset Management and Security
Focus Area 1: Asset inventory
At the top of CISA’s list is an issue that is at the core of Ordr’s mission, namely gaining visibility across the enterprise for identifying, inventorying, and securing all of an organization’s assets. Without real-time visibility and complete, accurate details, of every asset on the network (including Internet of Medical Things (IoMT), operational technologies (OT), Internet of Things (IoT) devices, you are building your security program on a foundation of sand. The Mitigation Guide highlights the reason gaining visibility across the IT estate and compiling a thorough asset inventory is vital to improving cybersecurity when it says:
Organizations that have not implemented or maintained an asset management policy risk exposing vulnerabilities or services that could be exploited by threat actors to gain unauthorized access, steal sensitive data, disrupt critical services, or deploy ransomware, causing significant harm to patients and the organization’s reputation.”
Establishing a complete and accurate asset inventory has been a major challenge for HDOs because of the highly varied nature of the technologies that connect to and operate within healthcare networks. HDOs not only have all the traditional systems and devices of other enterprises: servers, routers, desktop and laptop computers, tablets and handheld devices, and the like, but they also have a wide array of Internet of Medical Things (IoMT), operational technologies (OT), Internet of Things (IoT) devices that are critical to patient care services. These can include devices like patient monitors, respirators, imaging and surgical equipment, and therapeutic devices as well as HVAC, security, communications, environmental control, and other equipment.
CISA recommends utilizing active scans, passive processes, or both to discover these devices, but we believe organizations should use a passive approach in order to not impact the operations of sensitive medical devices, IoT and OT. This is consistent with the medical profession’s “do no harm” philosophy, as active scanning can be detrimental to the performance of some equipment. In fact, one organization I’m familiar with experienced a catastrophic failure of its telephone system after active scanning was applied that interfered with the telephony/IP interface.
Furthermore, many systems are either incompatible with active scanning, or may have prohibitions in place due to FDA rules. For these reasons it is best to avoid active scanning. Ordr’s passive scanning approach has proven effective at discovering and identifying all connected assets, has no negative effect on performance or communications, and enables real-time tracking and monitoring of all devices on the network.
Focus Area 2: Securing your assets
CISA recommends that, once a complete and accurate device inventory is compiled, healthcare organizations segment their networks to keep medical devices separate from other technologies. This prevents attackers that succeed in compromising traditional IT from using IoMT to move laterally to their target destination.
I was happy to see that CISA ranked segmentation so high as a priority action. Too often organizations will try to tackle tasks like risk evaluation first, but for every minute the healthcare organization operates with a flat network, those critical devices are vulnerable to attack. By segmenting medical equipment as a second step after compiling a complete inventory, you’ve already increased network security and improved patient safety by disassociating those assets from traditional IT and OT.
Although network segmentation is a great best practice, the reason most organizations put it off–or avoid it completely–is that (as CISA’s schematic and description implies), it can be difficult to do using traditional approaches. Ordr simplifies segmentation. You can start off with macrosegmentation based on asset type, and then evolve to microsegmentation by enabling the creation and automation of Zero Trust segmentation policies to control what devices can connect and communicate with across the network. Segmentation policies created with Ordr can be enforced through integrations with NAC, switches and firewalls.
Stay Tuned for Part Two
In my next segment I’ll discuss CISA’s Mitigation Strategy #2: Identity Management and Device Security and offer some insights and approaches for achieving the goals of that portion of the Guide. The good news is, with the right tools, healthcare organizations can do what is needed with less trouble than they might think.
In the meantime, you might want to check out our new white paper, Mapping Ordr Capabilities to CISA Mitigation Guide: Healthcare and Public Health (HPH) Sector. It goes into much greater detail of how the Ordr platform can be used to quickly and easily do what the CISA Mitigation Guide suggests, while serving as a roadmap for formulating a strategy to align organization policy with CISA guidelines.
Wes Wright
Chief Healthcare Officer
Wes is responsible for driving Ordr’s engagements in healthcare. Previously he was the CTO for Imprivata, and prior to that VP and CTO at Sutter Health, a 26 hospital network in Northern California. Prior to Sutter, Wes was CTO and then CIO at Seattle Childrens’, which, to this day, he says was his most gratifying work experience.
Interested in Learning More?
Subscribe today to stay informed and get regular updates from Ordr Cloud
Ready to Get Started?
-
 BlogProtect Operational Technologies and Critical Infrastructure
BlogProtect Operational Technologies and Critical Infrastructure…are doing. Unlike users, devices have deterministic communications patterns for their “roles” Architect/Create Zero Trust policies – This has to be automated to prevent errors, and to scale for hundreds…
Security Bulletin
Protect Operational Technologies and Critical Infrastructure
Organizations Must Act Now
3Min Read
By Greg Murphy

A recent CISA security alert highlights advanced persistent threats against internet connected operational technologies (OT), including industrial control systems (ICS) and supervisory control and data acquisition (SCADA) devices targeting critical infrastructure. Legislation and national policy changes are necessary, but organizations can’t wait for them to take effect
A recent security alert from the U.S. Cybersecurity & Infrastructure Security Agency (CISA) highlighting advanced persistent threats against internet connected operational technologies (OT), including industrial control systems (ICS) and supervisory control and data acquisition (SCADA) devices, raises the stakes for the federal government to mandate stricter security standards for manufacturers of internet-connected devices.

In response to the growing number of threats to its governmental agencies, critical infrastructure, healthcare institutions, and businesses of every type and size, the White House and lawmakers have introduced stiffer standards, clearer guidance, updated policies, and legislation to compel organizations to increase their security posture, and to design more secure products. These include memos on achieving Zero Trust, the PATCH Act to increase medical device security, NIST whitepapers redefining critical infrastructure, the IoT Cybersecurity Improvement Act, and an Executive Order on Improving the Nation’s Cybersecurity, to name a few.
Troubling Trends
Ordr has voiced its support for these measures because it is clear that business-as-usual in cybersecurity is not getting the job done. Here are some numbers that illustrate the growing threat to the integrity of connected devices and the people and organizations that rely on them:
- According to the United Nations, cyberattacks against healthcare organizations has increased 600% worldwide since the start of the pandemic in 2020;
- There are more than 4,000 ransomware attacks every day, and an organization falls victim to a ransomware attack every 14 seconds;
- The total costs of cybercrime, which were estimated at $6 trillion in 2021, are expected to exceed $10 trillion by 2025;
- The FBI’s Internet Crime Complaint Center (IC3) investigated 649 successful ransomware attacks on U.S. critical infrastructure organizations in 2021; and,
- Researchers tracked a 110% increase in vulnerabilities in connected devices in healthcare environments since 2019, and a 55% increase in attacks against the healthcare industry.
These are just a few of the troubling trends that demonstrate the need for a strong, national response for improving cybersecurity. But legislation and policies take time to draft, pass, and implement. In the meantime, organizations that rely on devices that make up the realm of OT, the internet of things (IoT), the internet of medical things (IoMT), and other systems and devices that connect to public networks must take steps now to harden their existing infrastructures against threats that target such systems.
A New Approach is Needed–And Available
Operational technologies form the backbone of modern industrial productivity. Many of the connected devices and cyberphysical systems that run production lines, keep facilities operating, and that support transportation and logistics were not designed with cybersecurity in mind. But as formerly air-gapped systems have become dependent on data and connectivity, they have become vulnerable. That is reflected in the attacks we see increasing on OT environments, which often can start with IT and IoT devices, and do not require sophisticated approaches to be successful. But they do require a new approach to security.
The emphasis on achieving a Zero Trust posture for IT architectures is vital. The growing number and sophistication of the elements of today’s IT estates, including connected IT, IoT, IoMT, and OT devices means it is impossible for traditional, human-centric approaches to security to succeed. Zero Trust requires machine learning and automation to achieve complete visibility across all aspects of technical infrastructure and to respond to indicators of compromise affecting devices.
When threats are detected, security policy enforcement can isolate affected systems and segment those that are mission critical to allow operations to continue while mitigation unfolds, thereby limiting an organization’s vulnerable attack surface and limiting risks. Ordr’s technology has been proven more than capable of providing this level of performance, allowing organizations to see across their network, know what devices are connected and their level of vulnerability, and to secure those devices from attack by addressing four key aspects of cyber asset attack surface management:
- Identify your complete attack surface – Know what devices are in the network and risks they bring.
- Map the transaction flows – Understand what devices are doing. Unlike users, devices have deterministic communications patterns for their “roles”
- Architect/Create Zero Trust policies – This has to be automated to prevent errors, and to scale for hundreds of thousands of devices in the network.
- Monitor/maintain the network – Continue to discover devices, and monitor them for risks and anomalies.
When device security must be a priority—whether government, healthcare, manufacturing, or other critical infrastructure environments—organizations around the world trust Ordr for protecting their OT, IoT, IoMT and other connected devices. We can help your organization identify, inventory, assess, and protect your connected devices within minutes. Contact us today to get the conversation started.
Greg Murphy
Greg joined Ordr as CEO in December 2018. Previously, he was VP Business Operations for the HPE Aruba Group, the 4,000 person networking and IoT business unit of Hewlett Packard Enterprise. In that role, Greg was responsible for leading the business integration of Aruba and HP Networking following HP’s $3 billion acquisition of Aruba Networks in 2015. Greg held multiple prior senior executive positions within Aruba, including SVP Business Operations, GM of network management software, GM of outdoor and mesh products and VP of Marketing. Greg joined Aruba in 2008 through its acquisition of AirWave Wireless, a network management software provider that Greg founded and led. Greg received his M.A. from Stanford University and his B.A. from Amherst College.
Interested in Learning More?
Subscribe today to stay informed and get regular updates from Ordr Cloud
Ready to Get Started?
-
 NewsOrdr Named in the 2021 Gartner Market Guide
NewsOrdr Named in the 2021 Gartner Market Guide…For more information, visit www.ordr.net and follow Ordr on Twitter and LinkedIn. Interested in Learning More? Subscribe today to stay informed and get regular updates from Ordr Cloud You Might…
Ordr Named in the 2021 Gartner Market Guide
For Operational Technology (OT) Security
3Min ReadSANTA CLARA, Calif., February 17, 2021 — Ordr, the leader in security for all connected devices, has been named a Representative Vendor in the 2021 Gartner Market Guide for Operational Technology Security.
The Gartner Market Guide identifies the convergence of IT and OT, calling for the need to address identifying all network connected devices, understanding how they are communicating and properly assessing the risks associated with them.
According to Katell Thielemann, Wam Voster, Barika Pace, and Ruggero Contu (the authors of the report), “Gartner end-user inquiries suggest that, across all industry verticals except for the most highly regulated, about 60% of organizations are still in the awareness phase, about 30% are in the discovery to firefighting phases, and only about 10% are truly in the integration and optimization phases. The proliferation of OT in a wide number of different verticals, ranging from medical to fast-moving consumer goods, and critical infrastructure further complicates the situation.”
As described in the report, the OT/CPS security journey aligns with six key phases. “Once they enter the “Oh Wow!” Phase [3], organizations realize that security — whether IT, OT, physical or supply chain — needs a whole-of-enterprise focus. Historical IT and OT functional differences are becoming a liability when security is involved. Due to design, age or function, the unique requirements of OT systems now add to IT security concerns in ways that can no longer be ignored. Modernization efforts bring risk, reliability and safety discussions to the forefront. As a result, leading organizations are starting to elevate OT security requirements into their enterprise risk management (ERM) efforts by adopting an integrated security strategy across IT, OT, CPS, physical security and supply chain security.”
Phase 3. “The “Oh Wow!” Moment: Invariably, proof of concepts (POCs) become eye openers. For example:
- Unmanaged assets are connected everywhere.
- OT networks that were initially designed to be highly segregated have become flatter than realized.
- Ports on all kinds of systems in all kinds of remote locations are wide open.
- OEMs are accessing the machines they sold remotely and no one is managing it.
- Disclosed vulnerabilities on old OSs have never been evaluated for possible patching.
- The functional silos between separate security disciplines (e.g., cybersecurity, physical security, supply chain security, product security, health and safety) are creating seams that bad actors can exploit.
- The realization sets in that operational environments where security is lacking are centers of value creation for most organizations; however, no centralized governance exists to start making sense of it all. Recognition develops that roles and responsibilities for a wide variety of (security related) processes and decisions have never been clear, let alone agreed on.”
“We take a whole-enterprise approach with our customers, starting with continuous and real-time asset discovery,” said Greg Murphy, CEO of Ordr. “Ordr’s platform is differentiated by our use of deep packet inspection to classify and provide visibility to all the connected devices – from traditional servers, workstations and PCs to IoT and OT devices — that can serve as attack vectors. We not only classify every device, we also profile device behavior using advanced machine learning, to risk score every communication flow and surface anomalies. Further, our customers have access to automated policy creation and proactive segmentation of devices or device groups for business-critical devices that cannot be taken out of service.”
Gartner Disclaimer
Gartner does not endorse any vendor, product or service depicted in its research publications, and does not advise technology users to select only those vendors with the highest ratings or other designation. Gartner research publications consist of the opinions of Gartner’s Research & Advisory organization and should not be construed as statements of fact. Gartner disclaims all warranties, expressed or implied, with respect to this research, including any warranties of merchantability or fitness for a particular purpose.
About Ordr
Ordr makes it easy to secure every connected device, from traditional IT devices to newer and more vulnerable IoT, IoMT, and OT. Ordr Systems Control Engine uses deep packet inspection and advanced machine learning to discover every device, profile its risk and behavior, map all communications and protect it with automated policies. Organizations worldwide trust Ordr to provide real-time asset inventory, address risk and compliance and accelerate IT initiatives. Ordr is backed by top investors including Battery Ventures, Wing, and TenEleven Ventures. For more information, visit www.ordr.net and follow Ordr on Twitter and LinkedIn.
Interested in Learning More?
Subscribe today to stay informed and get regular updates from Ordr Cloud
Ready to Get Started?
-
 NewsOrdr Publishes Connected Device Security Maturity Model
NewsOrdr Publishes Connected Device Security Maturity Model…of maturity. We understand the complexities that security teams in healthcare struggle with everyday – and we’re proud to share our insights with the community, to be used as a…
Ordr Publishes Connected Device Security Maturity Model
Guide for Healthcare Organizations on the Path to Zero Trust
3Min ReadSanta Clara, CA – November 29, 2022 – Ordr, the leader in connected device security, today published a maturity model aimed at helping healthcare organizations benchmark their connected device security efforts and develop a strategy to improve the efficiency and strength of their security programs.
Entitled “A Practical Guide: Implementing Connected Device Security for Healthcare Organizations,” the document serves as a framework for healthcare security teams, helping them understand where their organization is on the connected device security maturity curve, and where to focus efforts to make improvements. The guide organizes the stages of maturity into five steps, including detailed descriptions, requirements, and the potential business value realized at each stage. Recommended actions, technical considerations, and helpful insights are included as well, to help teams learn how to improve their security posture, become more resilient, and advance their security efforts as they move toward Zero Trust.
Connected devices play an essential role within a healthcare organization – gathering data, providing diagnostics and therapeutic functions, and automating activities. But those same connected devices also expand the attack surface and create risk for healthcare providers. In fact, the healthcare sector faced the most ransomware attacks of any industry last year, according to the FBI’s 2021 Internet Crime Report, resulting in losses of $6.9 billion.
“A majority of healthcare organizations today rely on Internet of Things (IoT), Internet of Medical Things (IoMT), and Operational Technology (OT) devices to provide critical patient care, improve efficiencies, and manage the facility. The truth is, connected devices are everywhere in healthcare, which can make protecting them a daunting task,” said Pandian Gnanaprakasam, Chief Product Officer and co-founder of Ordr. “At Ordr, we’ve gained deep expertise working with customers of all sizes and at all stages of maturity. We understand the complexities that security teams in healthcare struggle with everyday – and we’re proud to share our insights with the community, to be used as a guide on the journey to Zero Trust.”
The five steps of the maturity model include:
- Asset Visibility: This stage includes creating a complete, accurate and up-to-date asset inventory by automating discovery and classification for all known, unknown, and new devices, in addition to identifying risks.
- Vulnerability and Risk Management: This stage encompasses creating a risk-based view of connected devices by combining device vulnerability insights, establishing device behavior baselines, and reviewing external threat intelligence inputs to gain a comprehensive view of the attack surface, guiding security efforts.
- Reactive Security: This stage uses connected device insights and the risk-based view from the previous stages, combined with business context, to help teams understand device risk in their unique environment, prioritizing risk mitigation and incident response efforts.
- Proactive Security: In this stage, teams automate policies and workflows to ensure rapid threat detection and response. Teams also develop and implement proactive measures such as Zero Trust segmentation to reduce the attack surface ahead of threats, enabling teams to focus on more complex threats.
- Optimized Security: At this stage, teams continue to build on the foundation they have created to expand and optimize their security methods with automation and proactive Zero Trust security policies, aligning and scaling with organizational demands.
“While all industries are at risk of cyberattack, the potential outcomes of attacks on healthcare organizations could be catastrophic, with real consequences for patients,” added Brad LaPorte, author of the guide and former Gartner cybersecurity analyst. “Organizations cannot expect to reach the Optimized Security stage instantly. Each stage establishes critical capabilities, builds upon previous stages, and creates value on the journey to Zero Trust. No matter where you are on this journey and what your ultimate goal is, this guide provides essential insights to understanding your security posture – and what is needed to improve.”
Interested in Learning More?
Subscribe today to stay informed and get regular updates from Ordr Cloud
Ready to Get Started?