Search Results:
”Quiz 2024 SAP C-ARSOR-2308: Marvelous SAP Certified Application Associate - SAP Ariba Sourcing Valid Dumps Book 🐮 Open ▷ www.pdfvce.com ◁ and search for ➥ C-ARSOR-2308 🡄 to download exam materials for free 🏑C-ARSOR-2308 Customizable Exam Mode”
-
 BlogFive Security Takeaways from Ordr 2021 Rise of The Machines Report
BlogFive Security Takeaways from Ordr 2021 Rise of The Machines Report…and secure via the network to complement your endpoint security solution. What’s important to remember is that ALL devices/assets need to be identified and profiled. Yes, if you’re in healthcare,…
Security Strategy
Five Security Takeaways from Ordr 2021 Rise of The Machines Report
4Min Read
By Danelle Au
Five takeaways from Ordr’s Rise of The Machines 2021 report provide insights that show the risks of operating in a hyperconnected world. Learn what devices are attaching to organizations in all industries—whether IT management knows or not. Then learn what you can do to keep your enterprise safe. Last week, we announced the availability of Ordr’s 2nd annual Rise of the Machines 2021 Report “State of Connected devices — IT, IoT, IoMT and OT”. This year’s report analyzed connected device security risk and adoption for 12 months (June 2020 through June 2021) across more than 500 Ordr deployments in healthcare, manufacturing, financial services organizations and more.
What were the learnings from the Rise of the Machines? Here are the five security takeaways from the 2021 Report.
1. A “whole organization” approach to connected device security is critical
In this report, Ordr discovered that 42% of connected devices were agentless or un-agentable devices. This number increased from 32% of agentless or un-agentable devices in 2020. With almost half of devices in the network that are either agentless or un-agentable, it’s clear that a security strategy that is only focused on agent-based endpoint security is not enough. These connected devices are key to digital transformation and organizational strategic priorities, but they are not designed with security in mind, often run obsolete operating systems and cannot support endpoint security agents. The solution is to identify, detect and secure via the network to complement your endpoint security solution.
What’s important to remember is that ALL devices/assets need to be identified and profiled. Yes, if you’re in healthcare, medical devices are critical, and similarly if you’re in manufacturing, your OT devices are critical. But because threat actors can target any vulnerable device, you need to have a complete asset inventory of every “thing” in your network. The Colonial Pipeline attack showed us that when IT and IoT systems are hit by a cyberattack, your business is impacted even if your OT environment continues to function. In a hospital environment, a cyberattack impacting your elevator control systems will similarly bring down the entire healthcare operations if patients cannot be transported even if your medical devices are fine. This is what we mean by the “whole organization” approach to connected device security.
2. Beware the “Shadow IoT” and personal devices
In a sign of the times, Ordr found Pelotons, Sonos, Alexas and Teslas in the network, almost 2 times the number compared to the 2020 report. Many of these devices (with the exception of Teslas) were in fact being used for actual business operations. In fact, many of our “Smart Hospitals” were deploying Aexas in their rooms for their pediatric patients. Alexas were used for “nurse call functions”, to switch channels on TVs, and to dim or change the smart lighting in the rooms. Pelotons were being used for physical therapy in hospitals, deployed in gyms in hospitality verticals and enterprises.
What’s interesting to note is that not only do these devices have vulnerabilities (for example leaky APIs within Pelotons) for threat actors to take advantage of but there is also an overwhelming amount of data stored that could be used to target users within the organization. Threat actors are already targeting disgruntled employees to get them to unleash ransomware, imagine if they had data from personal devices (eavesdropping on Alexas or identifying health conditions on Peloton devices) to optimize their target list.
3. Understand which devices are bringing risks to your network
Outdated operating systems present the greatest risks for most organizations. We identified about 19% of deployments with devices running outdated operating systems Windows 7 and older, and almost 34% of deployments with devices running Windows 8 and Windows 10, which are expected to end-of-life in 2023 and 2025, respectively.
Within healthcare, 15% of medical devices and 32% of medical imaging devices run on outdated operating systems. This is because many medical devices remain in operation for a number of years and cannot be easily replaced for cost reasons. Segmentation is the only way to ensure security of these devices, keep them in operation and avoid the costs of replacing devices early.
Ordr makes this easy for any security organization because we create the segmentation policies automatically for you, to be pushed and enforced on switches, next-generation firewalls, wireless LAN controllers and NAC systems.
Besides outdated operating systems, you should also identify devices with weak operating systems, weak passwords or weak certificates. Again, this is an easy click of the button on the Ordr dashboard.
4. Monitoring device behaviors and communications patterns is critical to security
At Ordr, we believe in the adage “You can’t secure what you can’t see”. But visibility is not just about knowing what devices you have in the network, it’s also about understanding how it’s behaving and what it is communicating with. That behavioral understanding of what is “normal” allows you to surface anomalous behaviors such as lateral movement from the (sudden increase in SMB traffic) or a compromised device (via communications calling home to a C2 domain).
The Ordr platform not includes an integrated threat detection engine for known threats, but also the behavioral mapping of every device flow to detect unknown threats. This is not easy, we monitor almost one BILLION flows today across all our customers’ deployments. But this has allowed us to detect Darkside and Conti infections, via devices behaving suspiciously, BEFORE any indicators of compromise were even released by authorities such as the FBI.
5. Manage user access to devices and appropriate offboarding when status changes
Finally, one of the most interesting additions to the 2021 report was about 55% of our deployments having devices with orphaned users. Devices with orphan accounts retain the same access rights as when they were associated with an active user. These orphaned user accounts provide a gateway to privilege escalation and lateral movement. Therefore, as part of a robust and complete Zero Trust strategy for connected devices, you need to ensure that all devices are being utilized only by current users and those with appropriate privileged access. Check out our blog on identifying employee account misuse using Ordr.
Danelle Au
Danelle Au has more than 20 years of experience bringing new technologies to market. Prior to Ordr, she was CMO at Blue Hexagon, a deep learning for malware protection company, and CMO at SafeBreach where she helped build the marketing organization and and define the Breach and Attack Simulation category. Previously, she led strategy and marketing at Adallom, a cloud security company acquired by Microsoft. She was also Director, Security Solutions at Palo Alto Networks, driving growth in critical IT initiatives like virtualization, network segmentation and mobility. Danelle was co-founder of a high-speed networking chipset startup, co-author of an IP Communications Book and holds 2 U.S. Patents. She has an MSEE from UC Berkeley
Interested in Learning More?
Subscribe today to stay informed and get regular updates from Ordr Cloud
Ready to Get Started?
-
 NewsOrdr Secures Four Patents for Advancing Connected Device Security
NewsOrdr Secures Four Patents for Advancing Connected Device Security…“organization” using a novel technique to make it easy to examine group-to-group communication and its deviations and anomalies. This is critical for pre-segmentation planning to develop policies on what to…
Ordr Secures Four Patents for Advancing Connected Device Security
3Min ReadSanta Clara, CA – October 25, 2022 – Ordr, the leader in connected device security, has been awarded four new patents for the visibility and security of the ever-increasing number of devices accessing today’s enterprise networks.
Connected devices are transforming industries and business operations. However, each new device and connection increases an organization’s attack surface. In industries such as healthcare and manufacturing, a cyberattack impacting a connected device can easily disrupt the entire business, or become a life-threatening situation. IoT and OT devices in particular can be essential to digital transformation strategies, but present unique cybersecurity challenges because they are not always designed with security in mind.
“Ordr continues to make significant investments in our technology to enable our customers to address critical connected device security problems. These patents validate the innovation behind our platform – from visualization of a device profile, mapping of how devices are communicating, to baselining normal behavior so that anomalies can be surfaced. We have best-in-class technology, and the most mature and innovative patent portfolio in this market,” said Pandian Gnanaprakasam, co-founder and Chief Product Officer at Ordr.
Ordr’s new patents represent unique innovations that position the company and its technology as the platform of choice for connected device security, healthcare IoT and IoMT security, and cyber asset and attack surface management (CAASM) challenges:
- Determining A Device Profile And Anomalous Behavior Associated With A Device In A Network (U.S. Patent 10742687) – This patent highlights Ordr’s ability to group devices and map their communication flows in real-time for behavioral detection. Ordr uses machine learning to baseline the normal behavior of a specific device with a similar set of devices over a specific period of time, to identify anomalies. This behavioral-based anomaly detection is applicable for all agentless devices including medical devices, IT devices such as printers and phones, and IoT devices such as building management systems and video surveillance systems.
- Presenting, At A Graphical User Interface, Device Photos And Risk Categories Associated With Devices In A Network (U.S. Patent 10979447) – Ordr’s Data Lake includes a knowledge base that identifies devices based on static, dynamic, and flow-level behavioral attributes. Ordr has unique innovations in classifying millions of devices using machine learning and a novel hierarchical organization technique to scale the classification process. Ordr uses this breakthrough technology to classify devices accurately and at scale, with granular details like manufacturer, make, model and more, including the exact picture of the device on the Ordr dashboard, to facilitate asset inventory and incident response. For example, more than 28,000 printers in the Ordr knowledge base are classified with this technology, and this knowledge database grows daily with machine learning.
- Presenting, At A Graphical User Interface (GUI), A Constellation View Of Communications Associated With Node Groups In A Network (U.S. Patents 10928987, 10656795) – Ordr employs a novel approach to group devices on multiple dimensions. For example, a group can be based on devices – printers, medical devices, cameras, etc. A group can also be defined based on the VLANs they belong to, subnets, or device categories (such as infusion pumps, CT scanners, etc), or business entities such as research departments or operating theater area and so on. Ordr has patented the ability to graphically show this “organization” using a novel technique to make it easy to examine group-to-group communication and its deviations and anomalies. This is critical for pre-segmentation planning to develop policies on what to allow and deny. This is also a great visualization tool to track policy controls post-segmentation enforcement to ensure any business workflow is not affected while malicious traffic is caught immediately.
Interested in Learning More?
Subscribe today to stay informed and get regular updates from Ordr Cloud
Ready to Get Started?
-
 NewsOrdr Recognized as a Market Leader by KLAS Research
NewsOrdr Recognized as a Market Leader by KLAS Research…partnership with CMCC Centre of Excellence and expansion of its partnership with Fortinet; The launch of a guide to assist healthcare organizations to meet the amended NHS Digital’s Data Security and Protection Toolkit criteria; and,…
Ordr Recognized as a Market Leader by KLAS Research
2022 Healthcare IoT Security Report
3Min ReadSANTA CLARA, Calif., Feb. 16, 2022 /PRNewswire/ — Ordr, the leader in connected device security, has been named a market leader in the Healthcare IoT security industry for the third year running by KLAS Research – a premier healthcare IT data and insights firm. In its latest report, “Healthcare IoT Security 2022: Moving beyond Device Visibility,” Ordr was recognized for its high market energy, significant customer consideration rate, breadth of functionality beyond visibility, strong technical background, and success with the largest and most sophisticated healthcare systems.
As the number of internet-connected devices continues to grow exponentially, healthcare delivery organizations have become lucrative targets for attack. Ordr gives healthcare providers full confidence in the visibility and security of every connected device on the network. Ordr received high marks from customers in the KLAS report for:Customers interviewed celebrated Ordr’s ability to provide value beyond just device visibility.
- Breadth of functionality beyond just visibility, including abnormal activity identification, traffic monitoring, and device utilization tracking;
- High customer satisfaction rates;
- High value across multiple stakeholders including Security, Clinical/Biomed and IT;
- Helpful training and education offerings, including the Masterclass webinar series;
- User interface enhancements; and,
- Strong technical background of the Ordr team in security, healthcare and networking.
Ordr was recognized by KLAS for client list transparency, and customers interviewed celebrated Ordr’s ability to provide value beyond just device visibility. In its report, KLAS noted that “Ordr customers (often very large health systems) use the platform to do more than simply see what devices are connected to their network—they also track device utilization, identify abnormal device activity, and monitor traffic.”
When asked about Ordr, one CISO commented, “I would definitely recommend the system. The major strength is complete visibility into the endpoints for the traffic that we send through the solution. That will assist us when we get into a more stringent RADIUS authentication requirement for our wired network. Another strength is the ability to see exactly what a device has talked to from either a profile view or a specific device view. We can see what ports were used, how many times the communication happened, and what the date and time were. We can get a rather slick visual representation of that and easily export it.”
Greg Murphy, Ordr CEO, said, “We’ve worked with some of the largest and most sophisticated thought leaders in healthcare since our inception. While they have been dealing with the dual pressures of the COVID-19 pandemic and escalating cyberattacks, we have maintained our focus on technology innovation and customer success. Our customers can confidently deliver care knowing that their devices and networks are secure. This recognition by KLAS for the third year running acknowledges the hard work of our team and reflects the value of the trusted partnerships we have built with our customers. This honor reinforces the importance of our mission to keep every healthcare organization safe via comprehensive device visibility, actionable clinical and security insights, and automated policies.”
Continued Growth Highlighted by KLAS Report
Ordr’s recognition in the 2022 KLAS report as a market leader in healthcare IoT security adds to a growing list of achievements over the past year, including:
- Rapid response on cybersecurity attacks including Log4j, Ripple20, SolarWinds and more;
- Receiving SOC 2 Type 2 Compliance by meeting AICPA strict standards on keeping customer data secure;
- The unveiling of new cybersecurity features including the Ransom-Aware Rapid Assessment service™ to enable organizations to respond to cyberattacks in minutes;
- Dramatic expansion in Ordr’s channel partner portfolio, in addition to a new partnership with CMCC Centre of Excellence and expansion of its partnership with Fortinet;
- The launch of a guide to assist healthcare organizations to meet the amended NHS Digital’s Data Security and Protection Toolkit criteria; and,
- Continued product innovation, expansions to the Board, and overall company growth.
For more information on how Ordr can help healthcare organizations, please visit https://ordr.net/solutions/healthcare/. A summary of the KLAS Healthcare IoT Security Report can be found here.
Interested in Learning More?
Subscribe today to stay informed and get regular updates from Ordr Cloud
Ready to Get Started?
-
 NewsOrdr Launches Clinical Defender
NewsOrdr Launches Clinical Defender…and FDA recalls; Prioritize clinical risk patching and remediation by impact; Integrate with IT Service Management (ITSM) tools to automate process for remediation; and, Simplified sharing option to share device…
Ordr Launches Clinical Defender
To Streamline Management of Connected Medical Devices
3Min ReadSanta Clara, CA, March 2, 2022 – Ordr, the leader in connected device security, today announced the availability of Ordr Clinical Defender. Built on Ordr’s foundational asset and risk management features, and developed with best practices from the top healthcare delivery organizations (HDOs) in the world, Ordr Clinical Defender enables Healthcare Technology Management (HTM) teams to more efficiently and accurately manage their connected medical devices.
HTM teams today face significant challenges in managing the explosive growth of connected medical devices critical to patient care. There is typically a 15-20% discrepancy between assets registered in a computerized maintenance management system (CMMS), and assets deployed on the network. This increases risks for healthcare organizations as unknown devices increase the attack surface, and missing devices may contain protected health information (PHI), putting the organization in jeopardy of a costly HIPAA data breach violation.
Furthermore, HTM teams spend an average of 30-60 minutes per person, per shift, looking for equipment. At a cost of $100 per hour, reducing this time can lead to significant cost savings. In addition, addressing clinical risks like identifying devices running outdated operating systems can drag on for weeks due to the lack of accurate data, making organizations vulnerable to cyberattacks.
Ordr Clinical Defender, running on the new Ordr 8 Software release, provides focused, actionable, and accurate HTM insights and workflows, so HTM and clinical engineering teams can:
- Automate real-time asset inventory without impacting device operations;
- Address compliance by identifying missing, newly-connected, or misplaced devices;
- Mitigate risks by identifying devices with vulnerabilities and recalls;
- Accelerate remediation efforts for devices with clinical risks; and,
- Save millions of dollars by optimizing device utilization.
“The thing we were astonished by was the visualization of the Ordr data. We found quite a few devices that had very out-of-date operating systems that we were not aware of, that we’re now addressing from an upgrade standpoint. We were able to mitigate those risks before anything happens,” said Chuck Christian, VP Technology and CTO, Franciscan Alliance.
“It is refreshing to work with a vendor that actually listens and empathizes with issues and pain points from customers. It’s exciting to see the rubber meet the road in terms of suggestions and requests. Ordr’s Clinical Defender dashboard is both modern and functional. Kudos to the team,” said Jeremiah Green, Information Security Manager, University of Rochester and University Rochester Medical Center.
Ordr Clinical Defender and Ordr 8 capabilities include:
- Data Shaper for users to customize the Ordr platform and quickly zero in on the information and insights most relevant to them; for example, enabling HTM users to only view specific medical devices they are responsible for within that hospital, or location, or that are using a specific protocol or access method.
- Asset Inventory and Analysis highlights critical information for real-time visibility and compliance:
- Real-time automated asset inventory, correlated with CMMS data;
- Identify newly connected devices in the last 24 hours to ensure no new medical equipment is installed without following proper procedures; and,
- Identify medical devices with Protected Health Information (PHI) that have not been seen on the network for more than 60 days.
- Connectivity and Location Analysis pinpoints devices in the wrong zone, VLAN or subnets:
- Locate missing devices by identifying device details, and physical and network location; and,
- Monitor VLANs for rogue or misconfigured clinical equipment.
- Clinical Risk Insights and Workflows enable prioritized risk remediation:
- Identify devices with vulnerabilities and FDA recalls;
- Prioritize clinical risk patching and remediation by impact;
- Integrate with IT Service Management (ITSM) tools to automate process for remediation; and,
- Simplified sharing option to share device details with other users in the organization for further analysis.
- Device Utilization summarizes usage of devices and fleets:
- Identify appropriate schedule for maintenance;
- Identify usage of specific devices to support procurement decisions; and,
- Analyze usage to improve efficiencies of under-utilized equipment.
- Simplified action framework to enable quick enforcement of policies across a set of target devices.
- Simplified search to make it easy to identify device insights no matter where users are in the Ordr interface.
“In my previous role, I was an Ordr customer, benefitting from the power of the Ordr platform and actively participating in the evolution of the platform. Ordr’s powerful platform captures not just device information but a true lifecycle view, identifying where a device is located within the network topology and how it communicates and behaves throughout the organization. This unique lifecycle view is particularly beneficial in healthcare. The launch of the Ordr Clinical Defender will be invaluable to HTM/Biomed teams that can now more effectively manage their medical devices and clinical risks,” said Ken Koos, Optiv Consultant, ICS and IOT Product Security.
“We’ve partnered closely with the leading healthcare organizations in the world to develop a simplified and optimized product for HTM. It’s everything HTM and clinical engineering teams need to more efficiently perform their most critical tasks. We’re excited to bring the value and benefits of the Ordr platform to a new set of stakeholders,” said Gnanaprakasam Pandian, Chief Product Officer and co-founder of Ordr.
To learn more about the Ordr Clinical Defender, visit www.ordr.net/platform.
Interested in Learning More?
Subscribe today to stay informed and get regular updates from Ordr Cloud
Ready to Get Started?
-
 NewsOrdr Announces a Milestone Release of Ordr Systems Control Engine
NewsOrdr Announces a Milestone Release of Ordr Systems Control Engine…backed by top investors including Battery Ventures, Wing, and TenEleven Ventures. For more information, visit www.ordr.net and follow Ordr on Twitter and LinkedIn. Interested in Learning More? Subscribe today to…
Ordr Announces a Milestone Release of Ordr Systems Control Engine
3Min ReadSANTA CLARA, Calif., January 21, 2021 — Ordr, the leader in visibility and security of all connected devices, today announced a significant release of the Ordr Systems Control Engine (SCE), a platform that discovers every connected device, profiles device behavior and risks, and automates response. Ordr SCE 7.4.2 is the largest product launch for the company to date and includes more than 160 new features, integrations, and enhancements to provide unparalleled visibility and protection to companies and their connected devices.
As the number of connected devices — including unmanaged IoT, IoMT, and OT devices — continues to rise exponentially, so do the number of vulnerabilities and attack vectors. Organizations are struggling to maintain a real-time accurate inventory of all connected devices, not to mention the device intelligence to quickly make informed decisions.
“Ordr provides the most robust, time-to-value security solution for organizations that want to reap the benefits of network-connected devices, yet curtail increased global incidents of ransomware, phishing, credit card, and personal data breaches,” said Gnanaprakasam Pandian, co-founder and Chief Product Officer of Ordr. “We are so excited to offer extensive new integrations from dozens of security and network vendors, as well as enhanced features to our customers in healthcare, manufacturing, financial services, life sciences, retail and beyond.”
Ordr not only identifies devices with vulnerabilities, weak ciphers and certificates, and active threats, but also those that exhibit malicious or suspicious behaviors. Ordr automates responses for security and networking teams by dynamically generating policies and enforcing them on existing infrastructure, or by alerting and triggering a specific security or operational workflow.
Highlighted features and benefits of Ordr SCE 7.4.2 include:
- Reduced infrastructure footprint with “sensor-less” visibility via telemetry data from supported switches, routers, firewalls, and wireless LAN controllers. Overnight, customers can leverage key technologies that are already in place and begin the Ordr journey.
- Increased efficiency with workflow-based dashboards to help customers quickly lookup devices that match specific conditions, including manufacturer, category, and profile as well as devices with sensitive data, devices with custom tags, devices communicating with administrative protocols, devices running outdated operating systems, and more.
- Security enhancements to enable our customers in the wake of high-profile ransomware as well as espionage-like activity seen in the SolarWinds attack with access to enhanced security components, focusing on optimized detection and tracking within the platform. Customers will have the ability to visually track antivirus software activity, URLs associated with phishing, malicious communications, user-defined prohibited country communications, and quickly see devices with admin protocols and a snapshot of criticality level for devices with known vulnerabilities.
- Empowered Healthcare Technology Management (HTM) teams with actionable clinical data like medical device data from the FDA, clinical and patient risk associated with a device(s), and security risk from Manufacturer Disclosure Statement for Medical Device Security (MDS2) forms to help make informed decisions and initiate the appropriate workflows within a matter of minutes.
- New security integrations for efficient incorporation into a customer’s existing security workflows. This includes the ability to detect and track ransomware with signature improvements for expedited incident response (IR) processes. In addition, Anomali, Exabeam, Fortinet, IBM QRadar, and Ping Identity join existing partners such as Check Point, Splunk, ServiceNow, and many others, in Ordr’s integration portfolio — the most comprehensive ecosystem of integration partners in the market.
- Enhanced analytics and use case-based policy generation so customers can quickly address scenarios such as controlling access for all physical security cameras used in a retail location, segment patient care devices by hospital and healthcare division, or tag all manufacturing devices that are still running Windows XP or Windows 7.
- Acceleration of Cisco TrustSec and Cisco Software-Defined Access (SD-Access) as Cisco’s leading IoT solution partner for Cisco Identity Services Engine (ISE). Ordr is the only product on the market to provide total IoT and OT visibility to Cisco ISE and the rich device context required to dynamically define Scalable Group Tags (SGTs), automate the provisioning of group-based segmentation policies and provide SGT visualization and traffic analysis that greatly accelerates the time to value and increases strategic adoption of Cisco TrustSec and SDA.
About Ordr
Ordr makes it easy to secure every connected device, from traditional IT devices to newer and more vulnerable IoT, IoMT, and OT. Ordr Systems Control Engine uses deep packet inspection and advanced machine learning to discover every device, profile its risk and behavior, map all communications and protect it with automated policies. Organizations worldwide trust Ordr to provide real-time asset inventory, address risk and compliance and accelerate IT initiatives. Ordr is backed by top investors including Battery Ventures, Wing, and TenEleven Ventures. For more information, visit www.ordr.net and follow Ordr on Twitter and LinkedIn.
Interested in Learning More?
Subscribe today to stay informed and get regular updates from Ordr Cloud
Ready to Get Started?
-
 BlogOrdr SCE taps the power of Palo Alto Networks’ massive Cortex Data Lake
BlogOrdr SCE taps the power of Palo Alto Networks’ massive Cortex Data Lake…and resources to actually do so effectively. And with the high probability of false alarms coming from multiple applications at a rapid pace, it is increasingly difficult to effectively identify and…
Integration
Ordr SCE taps the power of Palo Alto Networks’ massive Cortex Data Lake
3Min ReadBy Brad Day

The Ordr Data Lake boasts the industry’s most extensive device intelligence. Now the Ordr Systems Control Engine (SCE) has tapped into Palo Alto Networks’ Cortex Data Lake to combine two powerhouse resources and improve enterprise cybersecurity. The Boy Who Cried Wolf is a story we’ve all heard many times in our lives. It’s a story that originated in ancient Greece, an original fable of Aesop.
It’s been told many millions of times, in countless languages and undoubtedly with endless cultural variations. Yet the core message of the fable remains: repeating false or hyperbolic threat information repeatedly serves to diminish significantly the response to the threat with each retelling; eventually and predictably, responses simply cease – creating a situation of great peril when actual danger appears. The fable is thousands of years old, but its message is startlingly applicable for today’s enterprise IT and security teams.
In the modern enterprise, teams are presented with an exaggerated array of hysterical alarms and alerts on which they are expected to act – yet few have the time and resources to actually do so effectively. And with the high probability of false alarms coming from multiple applications at a rapid pace, it is increasingly difficult to effectively identify and prioritize those that need immediate response. Even more concerning, staff resources are overwhelmed with addressing and assessing these alerts, reducing their ability to respond with urgency to every real threat. The alerts can become noise, and the entire enterprise is put at great risk.
Couple this fact with the explosion in quantity and heterogeneity of network-connected devices – the Hyper-Connected Enterprise– and it’s clear that we’re at an important tipping point in enterprise network security. Traditional agent-based and human-generated security models simply cannot scale. And the answer, despite what every new threat detection vendor tells you, is not in deploying more systems that create more alerts and further tax your already depleted resources.
The answer is, however, quite simple: take control of the intelligent security infrastructure you already have, and utilize it to regulate and protect your network on your terms.
We’re proud to introduce the Ordr Systems Control Engine (SCE) app now available on Cortex by Palo Alto Networks. In just a few minutes of configuration, Palo Alto Networks customers can begin to implement comprehensive, agentless security policies that utilize their best-in-class Palo Alto Networks Next-Generation Firewall infrastructure to regulate and protect every device connected to their enterprise network. These policies can improve the perimeter protection of the enterprise by utilizing Palo Alto Networks next-generation firewalls at the network edge, and can significantly increase the security of the entire network – and prevent any East/West propagation of nefarious activity – by utilizing additional Palo Alto Networks next-generation firewalls inside the network protecting critical assets. This AI-based policy automation and implementation can also segment and protect systems and processes by function, keeping facilities and physical security devices separate from the business-critical data infrastructure, for example.
The cloud-based Ordr SCE app seamlessly and immediately – without the need for any additional hardware such as sensors or analyzers – taps into the massive Cortex Data Lake to automatically identify and classify every device connected to your infrastructure. Every device, such as IP cameras, HVAC control systems, access badge scanners, self-service kiosks, digital signage, infusion pumps, CT scanners, manufacturing control systems, barcode scanners…EVERY device. Even the devices that find their way into your environment without your knowledge, like popular employee-owned devices such as Amazon Echo and Apple iPad. The quantity and variety of these devices is almost unimaginable in the enterprise today…and it’s going to grow by orders of magnitude into the future.
The Ordr SCE not only identifies every device, it provides incredible granularity on exactly what every device is and precisely what each is doing. We call this mapping the Device Flow Genome, a collection of incredibly valuable data that gives you the power to intelligently design and implement policies that are essential to the security of your organization.
Once you have this level of detail on what’s connected to your network, and what each is doing – and should be doing – the Ordr SCE gives you the power to take control of this vast array of devices to ensure effective protection today and into the future. The Ordr SCE gives you powerful policy automation to regulate the behavior of every class of device so none are able to communicate in such manner – either inside or outside of your network – that exposes them to risk and vulnerability. And the Ordr SCE gives you the power to fully secure each class of device by implementing micro-segmentation and threat remediation policies with sophisticated and actionable artificial intelligence.
All without any software on or need to physically touch the connected devices. All utilizing the best-of-breed Palo Alto Networks next-generation firewall infrastructure you already have. All with the power of Cortex, the industry’s only open and integrated AI-based continuous security platform.
Take Control. Visit the Cortex hub today to learn more about the Ordr Systems Control Engine app and contact us for more information.
Interested in Learning More?
Subscribe today to stay informed and get regular updates from Ordr Cloud
Ready to Get Started?
-
PagesHigher Education
…for sensitive department of defense or medical research. Ordr delivers asset inventory and insights into risks and threats, to simplify compliance and to enhance security. SEE Comprehensive Visibility For Every…
- INDUSTRY
- HIGHER EDUCATION
Empower Productivity and Collaboration In Higher Education
Ordr ensures that every asset in higher education — laptops, mobile devices, BYOD, research and development assets, cloud and SaaS – is secure. Enable productivity, collaboration and cyber resilience.
REQUEST A DEMO
Secure Explosive Growth of Assets in Higher Education
Lack of Asset Visibility
The volume and diversity of assets used in universities — from devices, cloud and SaaS applications—significantly expands the attack surface. However, visibility particularly with BYOD, IT and OT devices can be challenging. Ordr addresses this with complete asset visibility across the entire network.
Diverse Department Risks
Higher education verticals face unique risks requirements from different departments– healthcare systems, research and development, undergraduate or graduate programs. Ordr’s Asset Intelligence Platform addresses the entire asset visibility and management journey, including segmentation between departments.
Regulatory Compliance
Most higher education institutions need to adhere to specific regulatory compliance requirements, particularly if they receive government funding for sensitive department of defense or medical research. Ordr delivers asset inventory and insights into risks and threats, to simplify compliance and to enhance security.
SEE
Comprehensive Visibility For Every Asset
Ordr delivers complete, accurate visibility for every asset—devices, users, SaaS, cloud and applications—on the university network.
- Save time via a real-time inventory on all assets including IoT, OT, and IoMT devices, with ability to limit view to different departmental teams based on RBAC.
- See granular device details like manufacturer, model, serial number, OS, support owner, connectivity and more.
- Identify issues such as devices banned by the government, running outdated operating systems, missing MDM/EDR agents or located in the wrong VLAN.
- Enrich CMDB with real-time asset visibility.

KNOW
Protect Every Asset From Cyber Attacks
Reduce risks and secure every asset. Create unique asset profiles for various departments, and monitor for vulnerabilities and threats. Map vulnerabilities for every asset including IOT, OT and IOMT devices. Detect cyberthreats that can impact studies and operations.
- Gain comprehensive coverage of all vulnerabilities, based on active scans and mapping to National Vulnerability and manufacturer database
- Prioritize vulnerabilities based on asset and university risk factors and automate remediation for the right owners
- Detect active exploits and risky communications with an integrated IDS and threat intelligence feeds
- Identify assets behaving abnormally, based on baseline known-good communications
SECURE
Secure and Segment Via Automated Policies
Reduce risks and dwell time. Ordr supports a variety of proactive and reactive security policies. For example, automate security policies during a security incident, such as block ports, terminate sessions or isolate asset. Create segmentation policies to stop lateral movement between different departments or Zero Trust segmentation to limit vulnerable devices to baseline communications.
Accelerate Segmentation and Zero Trust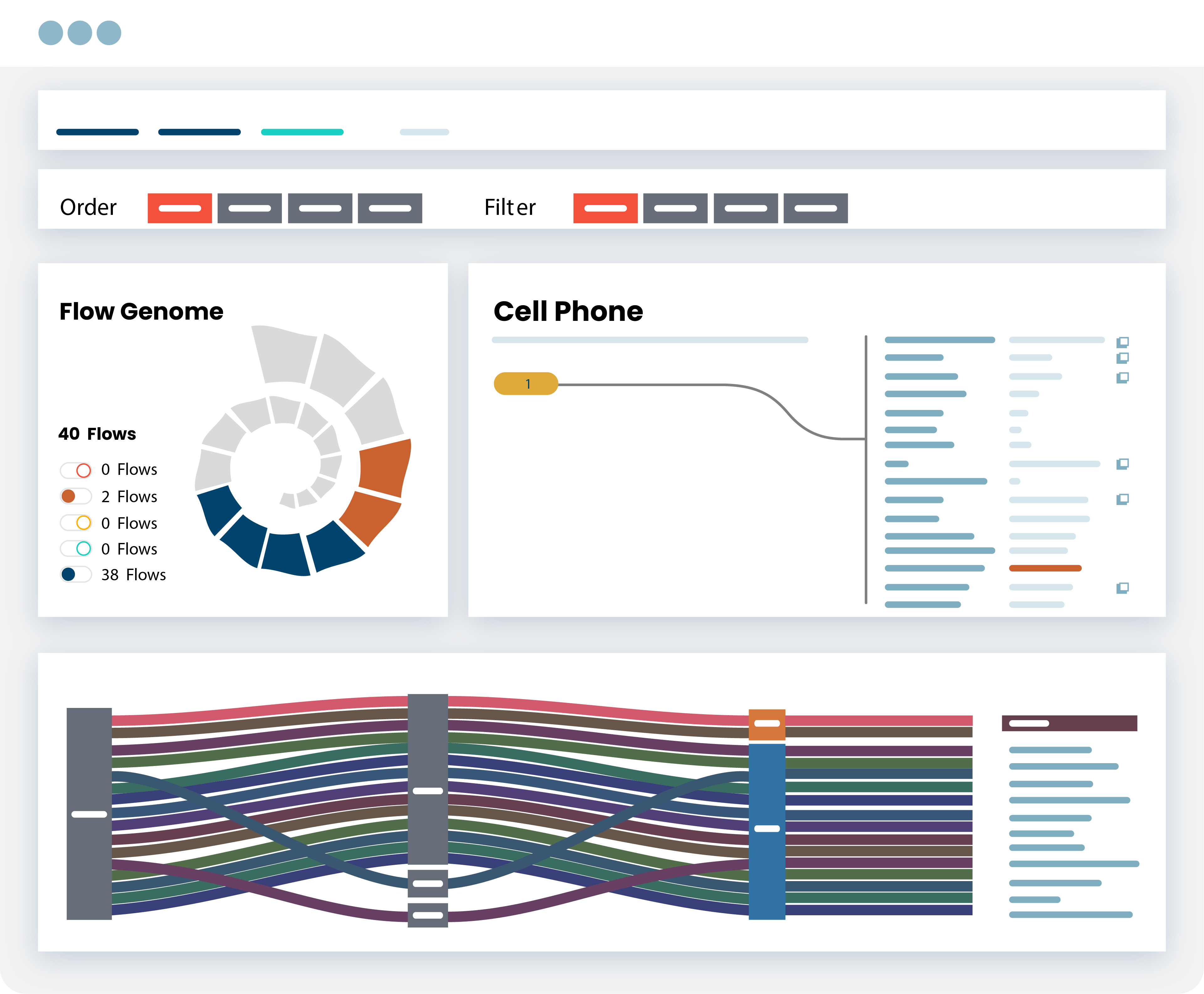
SECURE
Easily Address Compliance Regulations
Ordr delivers cyber asset and risk insights, and customizable reports, to address compliance. Colleges and universities have begun adopting the NIST 800-171 security framework (U.S) or Cyber Essentials (UK) in recent years, given their partnerships and contractual ties to federal agencies. Universities conducting highly sensitive defense or medical research will likely also adhere to CMMC requirements.
Streamline Security Framework Compliance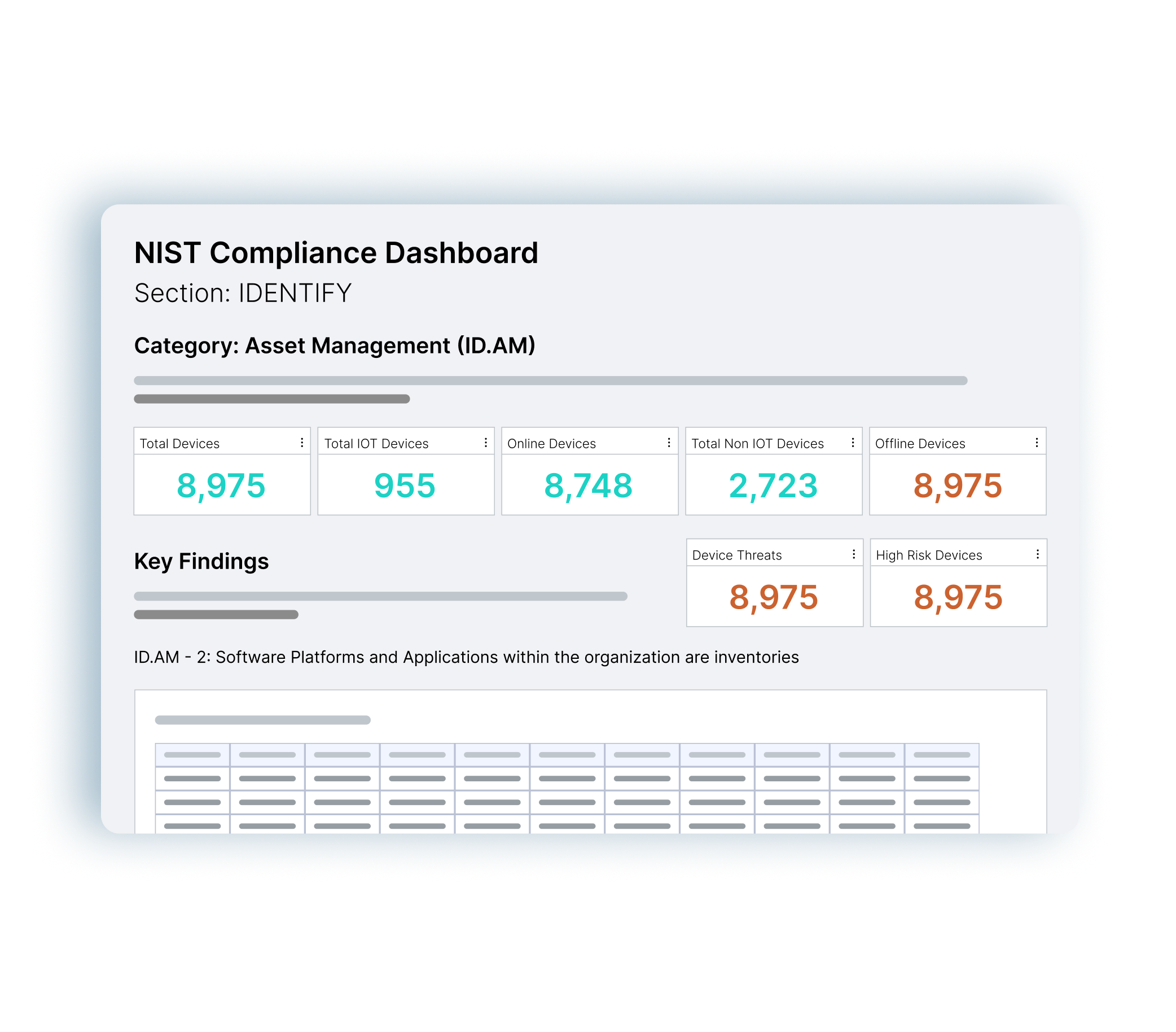
Ready to Start Securing Your Assets?
-
 BlogWindows 7 End-of-Life is Near…Are You Ready to Take Control?
BlogWindows 7 End-of-Life is Near…Are You Ready to Take Control?…see and understand the reason for the alarm. Build a specific VLAN with ACLs for this Device Type: One approach to segmentation is with a custom VLAN for a device…
Security Bulletin
Windows 7 End-of-Life is Near…Are You Ready to Take Control?
4Min Read
By Darrell Kesti

Medical devices with obsolete software and operating systems often remain in service for years, so Microsoft’s announcement that Windows 7 OS is being obsoleted means healthcare orgs with an inventory of Win7 devices need to protect those systems. Did you know that Windows 7 end of life is on January 14, 2020? This is only 300 days away, and today over 40% of the desktops deployed are still running this 10 year old OS. I can’t even imagine the number of imbedded IoT, OT, and Medical Devices where this OS is still used. This is going to be a big issue for the security community in 2019 to get their arms around this Windows 7 End of Life, the impact it will have on their security posture, and in medical and industrial fields – the safety risks it will expose to their patients and workers.
Here is a great article highlighting the EOL in more detail.
3 Ways Ordr Can Help You Take Control of Windows 7
- Ordr Discovery | Inventory | Categorization: Ordr captures the OS detail on devices as we do our automated Discovery, Inventory, Categorization and analysis of the traffic flows (Flow Genome).
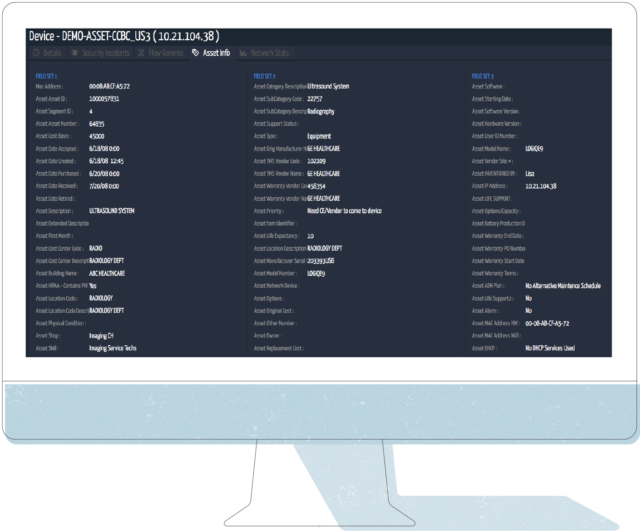
Here is an example of a GE Ultrasound Machine, but the same would apply to other systems:
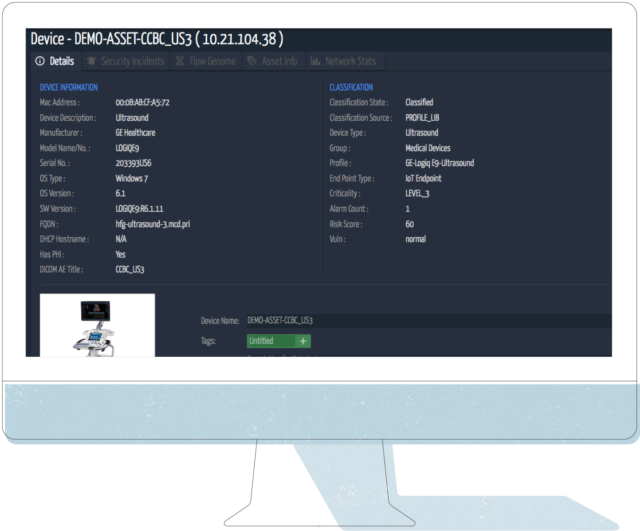
- Ordr integrates with CMDB / ITAM / CMMS Systems: If you integrate Ordr with your CMDB / IT Asset Management / CMMS system – say ServiceNow, Nuvolo, etc – you can further improve your visibility by leveraging the real-time always on view of the Ordr solution, to then update your records as you work to identify systems that need to be updated, who the device owners are, location of the equipment, where it is in its lifecycle, and perform post upgrade validation to close out the update work and document the remediation.
Here is a view of the same Ultrasound Machine as above, with the integrated asset detail from a CMMS system:
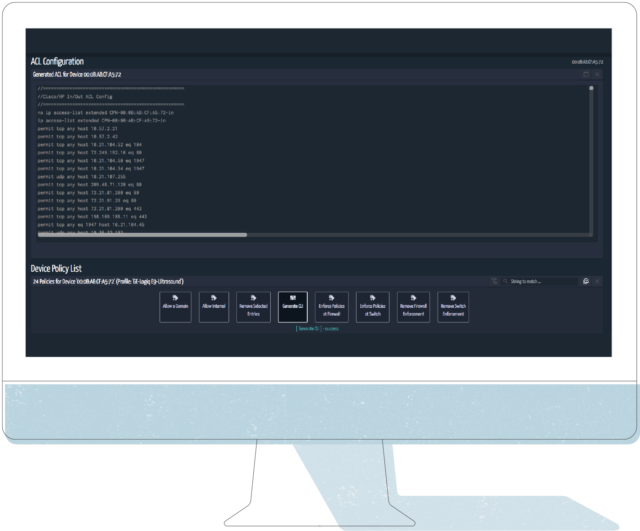
- Asset Info to Action: Armed with all this detail, Security and Network teams can start working with the appropriate lines of business (HTM in my example case), to figure out a plan to either upgrade the system, replace the system, or if can’t replace it and you are stuck with it on your network – build security controls around the device. This is where Ordr helps close the loop. One key area we can help is our capabilities around the behavior of the device in the network, the Flow Genome. Below you can see the 24 baselined normal flows Ordr has detected during this devices time on the network under monitoring.
See below, we will use this information in step 4:

Time to Take Control! OK, so you are stuck with the Windows 7 device on your network beyond 1/14/2020. You are armed with the information in steps 1 – 3. What do you do about it? How do you build in the right controls? This does depend on the environment, where there are firewall systems, NAC, network infrastructure that supports ACLs, etc. I will give you the most common actions I have seen, that should fit most of the customer environments you are working in.
Common controls Ordr can help you achieve
- Leave the device as is, but monitor it: This is probably the most common control. Monitor the device and respond to any alerts, change in behavior. There is concern especially with OT and Medical Devices around putting limiting controls in place. The good news is Ordr can alert on Behavior Violations, meaning if the device starts communicating outside of its Normal Baseline Flow. Ordr can be integrated into a workflow management system, send out email alerts on its own, fire off events to a SIEM or other Orchestration tool, or have a screen like the one below up in your SOC for human monitoring.
Below is a screen shot of our Incident Summary & Device Risk Dashboard: The Behavior Viol. count under Internal Communications is where we highlight behavior anomalies detected by the Flow Genome. All of this is linked to the events to quickly see and understand the reason for the alarm.

- Build a specific VLAN with ACLs for this Device Type: One approach to segmentation is with a custom VLAN for a device type, in this case GE Ultrasound Devices. The good part about Medical IoT, and IoT in general, is there is usually a consistent communication pattern for how it behaves on the network. In the case of a VLAN configuration with Access Control Lists for communication, the Security, HTM, and Network team could build the rule set for this ACL and limit the communication behavior. Or, you could let Ordr generate the ACL for you, that you apply in the environment. Here is an ACL based on the example system above:
- Integrate with your Network Access Control (NAC) solution: In this case Ordr can talk with your NAC system to put this device in a specific group (TAG), where there are ACL and/or TrustSec TAGs to identify and control access of this device. All of the attributes shown above can be shared, and the NAC solution can handle the controls around this device.
- Integrate with your Firewall system: Many customers are leveraging firewalls as part of their segmentation approach. Beyond the normal Internal to External (North / South) traffic control / protections from a firewall, they are putting more Firewall systems in the internal network (East / West) to segment the network. This helps with controlling the traffic flow, gives inspection points, and also gives the chance to apply other security tools of an Advanced Firewall feature set and the audit logging of the communication internally. Ordr integrates with firewall systems to either apply Firewall ACL’s to the traffic discovered by the Flow Genome, or to apply a Security TAG to the firewall. Many of these firewalls support Tagging as well for device groups, so you don’t have to build individual policies for each device. Ordr can give information to North/South and East/West firewall systems, to help with segmentation control.
What other strategies and ideas do you have to Take Control of the Windows 7 End of Life? Let us know.
Darrell Kesti
Darrell is VP Sales at Ordr. He joined Ordr as one of the original Account Executives in October of 2018 to help launch the field organization. In his prior role as Ordr’s Director of Healthcare Sales, Darrell drove significant growth in healthcare sales and helped position Ordr as the leader in connected device security. Darrell has had over 20+ years of Sales Leadership, Account Management, and Field Engineering experience supporting customers and partners while with leading security and networking organizations – ForeScout Technologies, FireEye, Mandiant, F5 Networks, and Secure Computing Corporation. Darrell earned a Bachelor of Science in Electrical and Computer Engineering from the University of Minnesota, Duluth.
Interested in Learning More?
Subscribe today to stay informed and get regular updates from Ordr Cloud
Ready to Get Started?
-
 NewsOrdr and GE HealthCare Enhance Clinical Network Performance and Security
NewsOrdr and GE HealthCare Enhance Clinical Network Performance and Security…version, etc.,) to assess risks, manage vulnerabilities, and implement mitigations; and, Locating mobile and portable devices, with many organizations spending almost an hour per person per shift searching for equipment…
Ordr and GE HealthCare Enhance Clinical Network Performance and Security
3Min ReadSanta Clara, CA – January 11, 2023 – Ordr, the leader in connected device security, today announced that it is collaborating with GE HealthCare to offer customers a solution leveraging Ordr’s market-leading platform for health systems.
The solution addresses critical patient care challenges across three key stakeholder groups: biomedical and healthcare technology management (HTM) teams, giving them the granular visibility as well as performance and utilization insights they need to improve medical device management; IT teams, helping them to monitor network connectivity and performance, while mapping device communications flows; and security teams, helping them to identify, prioritize, and self-manage responses to vulnerabilities, threats, or anomalies.
Healthcare providers rely on a wide range of network-connected devices to improve patient care and enhance clinician productivity. As the care environment becomes more complex, health systems are struggling with:
- Lack of visibility into device status, such as determining which devices are in-use, identifying new devices, or devices not yet registered in their asset inventory database;
- Monitoring and troubleshooting devices impacted by communications or performance issues;
- Lack of accurate device data (OS, software version, etc.,) to assess risks, manage vulnerabilities, and implement mitigations; and,
- Locating mobile and portable devices, with many organizations spending almost an hour per person per shift searching for equipment in need of a service action
To help ensure continuity of service for these devices, continuous monitoring of network performance and security is essential. Incorporating Ordr’s solutions will enable GE HealthCare to provide continuous network performance and security monitoring of all clinical assets connected to the CARESCAPE network. The proven, market-leading capabilities of the Ordr platform will help enable broad visibility, performance monitoring, security, and governance of all clinical assets on the CARESCAPE network, providing customers with enhanced self-management capabilities for their critical patient care devices.
“Empowering biomedical technicians, clinical engineers, and hospital IT with easy-to-use tools aimed at improving self-managed network security, productivity, and equipment uptime is key to enhancing critical patient care,” said Alla K. Woodson, GE HealthCare’s Global GM, Patient Care Solutions – Services & Consumables. “This network performance and security solution brings together the technology and scale of our two organizations to help ensure that our customers have visibility and access to actionable insights.”
“Hospitals and healthcare facilities rely on GE HealthCare’s CARESCAPE networks to host critical patient care devices. It is of the utmost importance that these networks—and everything connected to them—remain secure and operating at peak efficiency,” added Jim Hyman, CEO of Ordr. “The deep integration of the Ordr platform with the GE HealthCare CARESCAPE network will help give healthcare organizations comprehensive clinical asset visibility, security and performance capabilities they need to optimize and protect their environment of care.”
With this new service offering, healthcare organizations will be able to:
- Gain Granular Visibility to All Devices in the GE CARESCAPE network – Gain real-time visibility and automate inventories of all assets on the CARESCAPE Network, with device data that can be integrated with existing computerized maintenance management systems (CMMS). Access granular details on GE HealthCare clinical assets, such as hard-to-track patient data modules and which bedside monitors they are connected to.
- Enable Improved Device Performance and Help Reduce Downtime – Enable application-level performance monitoring of GE HealthCare Patient Care devices. Monitor HL7 application flows with actionable alerting that can speed troubleshooting and help reduce the impact of downtime.
- Monitor your Entire CARESCAPE Ecosystem – Provide a bird’s-eye view monitoring of the entire CARESCAPE ecosystem to help catch performance and availability issues with switches & UPS power supplies in near real time to help enhance uptime.
- Enable Preventative Maintenance Efficiencies via near Real-Time Data for HTMs – Eliminate the manual effort and time needed to locate networked devices and identify whether they are in use, based on near real-time network and physical data to complete Preventative Maintenance.
- Mitigate Risk and Help Improve Device Security – Full-lifecycle vulnerability management enables users to identify and focus on specific vulnerabilities affecting clinical assets under their management, prioritize vulnerabilities with Clinical Risk Scores, and self-manage the remediation process with simplified workflows and custom tags.
- Enable Optimal Device Utilization and Operational Efficiency – Understand how GE HealthCare Patient Care devices are being used, enabling teams to optimize performance and support future purchasing decisions.
Contact our team to get more information about how Ordr and GE HealthCare can help protect and optimize clinical assets on your GE CARESCAPE Patient Monitoring network.
Interested in Learning More?
Subscribe today to stay informed and get regular updates from Ordr Cloud
Ready to Get Started?
-
 BlogCountering Cyberthreats with a Whole Enterprise Security Approach
BlogCountering Cyberthreats with a Whole Enterprise Security Approach…individuals, and to safeguarding assets like finances and intellectual property. Many types of cyberattacks share common attributes and indicators of compromise (IoC) like point of entry and vector, lateral movement,…
Security Strategy
Countering Cyberthreats with a Whole Enterprise Security Approach
4Min Read
By Srinivas Loke

CISA reports that cyberthreats like ransomware are rapidly increasing. These rising threats, cyberattacks, and risks demand that all organizations apply a whole enterprise approach to cybersecurity. Ordr explains what’s required. There has been a lot of attention paid to ransomware over the last few years, and with good reason. In 2021 Fierce Healthcare reported a 470% increase in ransomware attacks on the healthcare industry in 2020 compared to the previous year. Threat actors saw an opportunity to take advantage of pandemic chaos to target a vulnerable sector of the economy and got to work. Healthcare took the brunt, but no industry was safe. The FBI’s Internet Crime Complaint Center (IC3) reported a more than 20% increase in ransomware investigations overall during that same period and said ransomware payouts increased at an even higher pace as a result. And according to Security Magazine more recent analysis shows the ransomware threat continued to rise through 2023, with more attacks, new gangs, and manufacturers emerging as a favorite target.
But ransomware isn’t the only danger to IT networks and data integrity. More common attacks, where the goal isn’t to lock down valuable information but siphon it off, remain a major threat to businesses. In fact, the most recent IC3 annual report said the FBI received 2,385 ransomware complaints accounting for losses of more than $34.3 million, while overall the Bureau fielded over 800,000 cybercrime complaints with losses of more than $10.3 billion during 2022.
A Complete, Real-Time View
Countering cyberthreats of every type is vital to protecting an organization’s business and operational interests, the safety of individuals, and to safeguarding assets like finances and intellectual property. Many types of cyberattacks share common attributes and indicators of compromise (IoC) like point of entry and vector, lateral movement, and disruptions to normal communications patterns. Identifying these can be difficult without a complete and real-time view of the assets comprising the network, and detailed profiles of each device connected to it. That is why a “whole enterprise” approach to cybersecurity must be adopted to maximize threat prevention.
Because many devices use obsolete, unsupported operating systems, they are easy to exploit and to quickly traverse the network toward their goal.
This is especially important when considering the growing reliance many organizations have on the Internet of Things (IoT) and associated technologies like the Internet of Medical Things (IoMT), Industrial Internet of Things (IIoT), operational technologies (OT), cyber physical systems, and other types of connected devices. Attackers don’t care what kind of devices the organization has deployed, only the operating system it runs. And because many devices use obsolete, unsupported operating systems, they are easy to exploit and to quickly traverse the network toward their goal.
Zero Trust Support
It makes sense, then, that a whole enterprise approach is the logical way to address cybersecurity because it includes full asset visibility combined with rich operational insights to give security teams the ability to recognize unexpected communications patterns and make informed security decisions in response. That is the Ordr See, Know, Secure philosophy to connected device security and it is why we have invested so much into building a platform that not only reveals an organization’s full connected device inventory in real-time, but layers in both intelligence and automation that enable dynamic policy creation and enforcement and support Zero Trust security initiatives.
A whole enterprise approach is the logical way to address cybersecurity because it includes full asset visibility combined with rich operational insights to give security teams the ability to recognize unexpected communications patterns and make informed security decisions in response.
That is important because connected devices are increasingly targeted by threat actors who use notoriously unsecure IoT, IoMT, OT and other devices as either an attack vector or path of lateral movement once inside the enterprise. They know that if 20% of an organization’s connected devices are outside the view of security, they are less likely to be detected and thwarted, and that their efforts stand a much higher chance of success.
Seven Keys to Fighting Back
To counter this threat, Ordr enables seven key capabilities in the fight against cyberattacks:
- Discovery of all connected devices.
- Identification of device communications with prohibited countries, prohibited IPs, and malicious URLs.
- Communications baselining and identification of communication anomalies.
- Identification of devices running vulnerable protocols with the ability to disable or monitor as needed.
- Identification of devices running unpatched and/or vulnerable software and OSes through the Ordr Software Inventory Collector.
- Segmentation or quarantining as a compensating control for devices that cannot be updated.
- Retrospective analysis to evaluate past compromised communications patterns when new IoC and threat intelligence are released.
Recent Attacks Illustrate the Threat
Several recent, high-profile threat campaigns illustrate how these capabilities and a whole enterprise approach to cybersecurity can help prevent or minimize the effects of an attack. Exploiting vulnerabilities in Fortra’s GoAnywhere managed file transfer product, Progress Software’s MOVEit managed file transfer product, and the RDStealer weapon targeting remote desktop applications allowed threat groups to plant malware, including ransomware, in hundreds of organizations and execute the exfiltration of millions of data files containing sensitive personal and corporate information. Even when attacks use zero-day vulnerabilities to compromise network security undetected, the exfiltration of data may itself trigger automated policy enforcement, minimizing the event’s impact.
Ordr is a key component in the whole enterprise cybersecurity strategies of many top healthcare, manufacturing, financial services, and other organizations that recognize their growing reliance on connected devices could leave them vulnerable. Using Ordr, they now SEE, KNOW, and SECURE their systems and data.
Srinivas Loke
Srinivas Loke is Vice President of Product Management at Ordr. Srinivas has a passion for cybersecurity with a deep understanding of network, end point, cloud and IoT security. Prior to Ordr, he led product teams at Aruba, Pulse Secure, FireEye and McAfee. He loves taking 1.0 products to the market and furthering cutting edge technologies that are solving customer problems.
Interested in Learning More?
Subscribe today to stay informed and get regular updates from Ordr Cloud
Ready to Get Started?