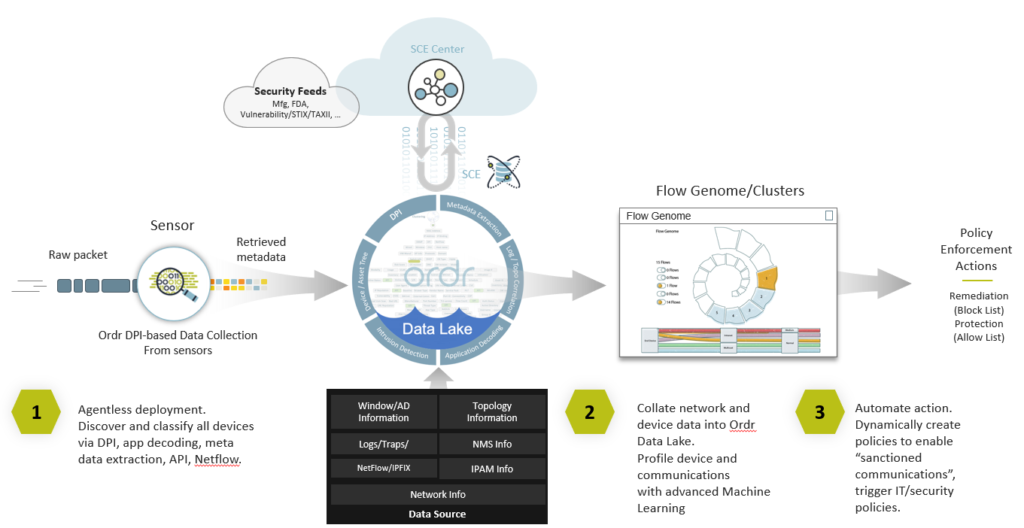
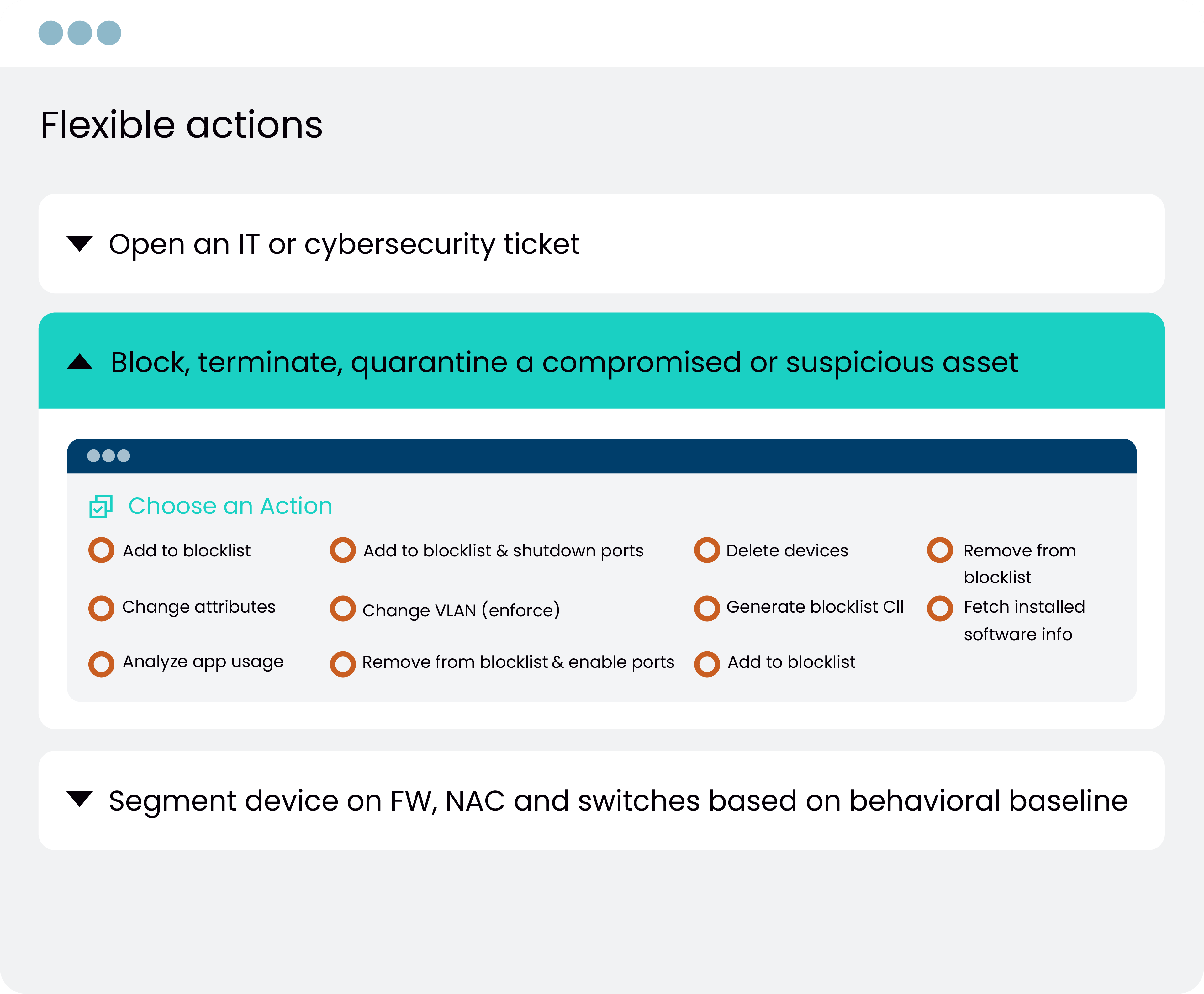
The power of the Ordr platform has always been its ability to automate device classification and behavioral modeling using AI. This is foundational to our Zero Trust and segmentation strategy.
Larry Smith Manager Cybersecurity Architecture and Engineering, El Camino Health.