Search Results:
”Quiz 2024 SAP C-ARSOR-2308: Marvelous SAP Certified Application Associate - SAP Ariba Sourcing Valid Dumps Book 🐮 Open ▷ www.pdfvce.com ◁ and search for ➥ C-ARSOR-2308 🡄 to download exam materials for free 🏑C-ARSOR-2308 Customizable Exam Mode”
-
 BlogConnected Device Security – Zero Trust is a Journey, not a Destination
BlogConnected Device Security – Zero Trust is a Journey, not a Destination…classify every device, and map its flows. Step Two – Vulnerability and Risk Management: used to extend the capabilities of the organization to effectively see and know about all the…
Security Strategy
Connected Device Security – Zero Trust is a Journey, not a Destination
Ordr Use Case Series
3Min Read
By Chris Westphal

Hospitals and other healthcare delivery organizations are under constant assault from cybercriminals and other threat actors. In response, Ordr offers a framework for healthcare cybersecurity with A Practical Guide: Implementing Connected Device Security for Healthcare Organizations. If Ralph Waldo Emerson had been a CISO and not a poet, he might have said, “Like life, Zero Trust is not a destination, but a journey.” And he’d be right, of course. For all the love Zero Trust has gotten from zealous marketers who promise that an investment in their cybersecurity product will deliver Zero Trust, the fact is that enterprises are far too dynamic for any one product to achieve that state. In fact, Zero Trust is not a static state, but an ideal that must be as dynamic as the environment in which it prevails.
Dynamic Environment, Dynamic Tool
When Ordr talks about Zero Trust, it is within the context of the challenges of protecting organizations that are increasingly reliant on connected devices to manage and run their operations. Devices within the domains of the Internet of things (IoT), Internet of medical things (IoMT), and operational technology (OT) are, by their nature, dynamic. They connect to and disconnect from networks often, finding a home where they are needed. They move around and increase an enterprise’s attack surface as they aggregate and grow in number. That kind of changeability and complexity requires a security platform like Ordr that has the speed and intelligence to discover, identify, and secure every device operating in the network.
According to the FBI, healthcare was the industry most targeted by ransomware gangs in 2021.
This is especially important for healthcare organizations that rely on IoT, IoMT, and OT devices to manage their facilities and provide a high level of care to patients. These devices gather data, provide diagnostics and therapeutic functions, and automate activity at all levels. But those devices also expand the attack surface of the organizations that deploy them, and threat actors have been taking advantage. According to the FBI, healthcare was the industry most targeted by ransomware gangs in 2021, affecting more than 550 organizations, compromising the protected health information (PHI) of more than 40 million people, and inflicting financial losses of $6.9 billion.
Wisdom of Old CISOs
Standing up to the threat requires thoughtful investments in security tools that address the specific needs of each organization, backed by a deliberate and strategic plan that maximizes the efficacy of those tools to achieve and maintain a continuous Zero Trust posture. And as Emerson said Zero Trust is a journey, another famous CISO, philosopher Lao Tzu said the journey of a thousand miles to Zero Trust begins with a single step. Fortunately for healthcare organizations looking to protect their IoT, IoMT, and OT assets, that single step is one of five in a connected device security maturity model that Ordr has outlined in a new ebook entitled A Practical Guide: Implementing Connected Device Security for Healthcare Organizations.
Five Easy Pieces
Authored by Gartner veteran and Ordr strategic advisor Brad LaPorte, with close consultation by many of our own subject matter experts, “A Practical Guide” includes recommended actions, technical considerations, and helpful insights that complement each of the five steps of maturity for connected device security, which are:
- Step One – Asset Visibility: a foundational exercise that must be launched and operationalized to discover and classify every device, and map its flows.
- Step Two – Vulnerability and Risk Management: used to extend the capabilities of the organization to effectively see and know about all the devices present in the environment.
- Step Three – Reactive Security: prioritization of activities necessary, such as blocking specific inbound and outbound communications to mitigate risks, risks.
- Step Four – Proactive Security: establish automated policies to ensure rapid threat detection and prevention, and begin to implement proactive Zero Trust segmentation policies.
- Step Five – Optimized Security: use of real time analysis and micro-segmentation to automate dynamic policy changes, scale protections reflective of an environment’s current state, and enable continuous improvement.
As you can see, each step in the maturity model builds on the previous step in sequence; there are no shortcuts. And the speed with which an organization progresses from Step One to Step Five will differ. It’s also important to recognize that, when starting from a place of no or incomplete connected device visibility, each step of the journey represents a significant improvement toward Zero Trust. And when a connected device security strategy is implemented and fully matured, it can be applied holistically across an entire organization or focused on multiple critical areas, in sequence or in parallel.
When starting from a place of no or incomplete connected device visibility, each step of the journey represents a significant improvement toward Zero Trust.
If you want to read A Practical Guide: Implementing Connected Device Security for Healthcare Organizations, you can download it here with our compliments.
Chris Westphal
Head of Product Marketing
Chris is the Head of Product Marketing at Ordr where he helps drive awareness for connected device security and the value of the Ordr solution. Chris brings more than two decades of experience to his role with a background in enterprise security, cloud, and data center technologies. Most recently, Chris was head of product marketing at Salt Security, the leader in API protection, and has held product marketing leadership roles at companies including VMware, Illumio, and Adallom (acquired by Microsoft).
Interested in Learning More?
Subscribe today to stay informed and get regular updates from Ordr Cloud
Ready to Get Started?
-
 BlogGartner Names Ordr a Representative Vendor
BlogGartner Names Ordr a Representative Vendor…IT and OT calls for the need to address identifying all network connected devices, how they are communicating and properly assess the risk associated. This is why Gartner named Ordr…
Company News
Gartner Names Ordr a Representative Vendor
2021 Market Guide for Operational Technology Security
3Min Read
By Corin Imai

Read why Gartner Named Ordr Representative Vendor 2021 Market Guide for Operational Technology Security. More than a decade ago, operational technology (OT) was d only used in manufacturing and industrial environments and airgapped from the rest of the organization. Today, the convergence of information technology (IT) and OT, and the growth of the internet of things (IoT) is revolutionizing the way organizations monitor systems, share and analyze data, and efficiently make decisions based on near real-time information. While this transformation brought about a modernization of how IT, IoT, and OT systems share invaluable data to empower business operations, it also brought about the alarming realization that none of these devices were created with security in mind. With ubiquitous connectivity comes the increase in ways to exploit them to gain access to sensitive data.
The convergence of IT and OT calls for the need to address identifying all network connected devices, how they are communicating and properly assess the risk associated. This is why Gartner named Ordr as a Representative Vendor in the Market Guide for OT Security.
As described in the Gartner report, the OT/CPS (Cyber Physical Systems) security journey for organizations aligns with six key phases. “Once they enter the “Oh Wow!” Phase [3], organizations realize that security — whether IT, OT, physical or supply chain — needs a whole-of-enterprise focus. Historical IT and OT functional differences are becoming a liability when security is involved. Due to design, age or function, the unique requirements of OT systems now add to IT security concerns in ways that can no longer be ignored. Modernization efforts bring risk, reliability and safety discussions to the forefront. As a result, leading organizations are starting to elevate OT security requirements into their enterprise risk management (ERM) efforts by adopting an integrated security strategy across IT, OT, CPS, physical security and supply chain security.”
Phase 3. The “Oh Wow!” Moment: Invariably, proof of concepts (POCs) become eye openers. For example:
- Unmanaged assets are connected everywhere.
- OT networks that were initially designed to be highly segregated have become flatter than realized.
- Ports on all kinds of systems in all kinds of remote locations are wide open.
- OEMs are accessing the machines they sold remotely and no one is managing it.
- Disclosed vulnerabilities on old OSs have never been evaluated for possible patching.
- The functional silos between separate security disciplines (e.g., cybersecurity, physical security, supply chain security, product security, health and safety) are creating seams that bad actors can exploit.
- The realization sets in that operational environments where security is lacking are centers of value creation for most organizations; however, no centralized governance exists to start making sense of it all. Recognition develops that roles and responsibilities for a wide variety of (security related) processes and decisions have never been clear, let alone agreed on.
At Ordr we’ve helped top global organizations address visibility and security with a whole-enterprise approach — from traditional servers, workstations and PCs to IoT, IoMT and OT devices. We have created a solution that passively and in real-time discovers what devices are on the network, profiles device behavior and risks, and then automates the appropriate action. Our relationship with our customers has been one of mutual benefit, we have worked together to evolve our solution and address new use cases. As a result, we’re grateful and proud to serve our customers and be been named in the Market Guide for OT Security as a solution addressing device visibility and security.
Gartner Market Guide for Operational Technology Security, Katell Thielemann, Wam Voster, Barika Pace, Ruggero Contu,13th January 2021
Gartner does not endorse any vendor, product or service depicted in its research publications, and does not advise technology users to select only those vendors with the highest ratings or other designation. Gartner research publications consist of the opinions of Gartner’s research organization and should not be construed as statements of fact. Gartner disclaims all warranties, express or implied, with respect to this research, including any warranties of merchantability or fitness for a particular purpose.
Interested in Learning More?
Subscribe today to stay informed and get regular updates from Ordr Cloud
Ready to Get Started?
-
 BlogA Proactive Strategy to Mitigate Medical Device Vulnerabilities
BlogA Proactive Strategy to Mitigate Medical Device Vulnerabilities…continue to function correctly. Ordr is one such tool. Ordr is able to scan a hospital’s network and detect and identify all the devices that are connected and operational, providing…
Risk Management
A Proactive Strategy to Mitigate Medical Device Vulnerabilities
No Time to Waste for Enterprise Security
3Min Read
By Benjamin Stock

Medical device manufacturers can’t keep up with the growing list of discovered vulnerabilities affecting the equipment they ship to market. Hospitals and other healthcare organizations need to implement proactive strategies that recognize and address these risks before they are victimized by threat actors. It has become painfully obvious that medical device manufacturers (MDMs) can’t keep up with the ever-expanding list of discovered vulnerabilities affecting the equipment they make and ship to market. Security researchers recently published a report claiming that as many as 75% of 200,000 devices reviewed have security flaws that make them vulnerable to exploitation by threat actors. More than half of those had multiple vulnerabilities, including many that have been known since at least 2019.
Healthcare delivery organizations (HDOs) like hospitals, urgent care clinics, private practices, and more have taken note. And while they rely on the capabilities that connected medical devices provide to deliver a superior quality of treatment, they also recognize that they can’t count on MDMs to address vulnerabilities promptly. Flaws in operating systems and software used to create the devices may include vulnerabilities that aren’t discovered until long after equipment is put in service. And once in service, it may be difficult to patch devices because they are in use providing critical care.
A Bad Time for Healthcare Security
These findings could not come at a worse time for the healthcare industry, which is already besieged by risk. In another recent report, security researchers found that the industrial control systems and other network-connected systems—devices comprising the internet of things (IoT), operational technologies (OT), and the internet of medical things (IoMT)—used in hospital and healthcare environments had seen a 110% increase in vulnerabilities since 2019. And that was before cybercriminals took advantage of the chaos brought on by the Covid-19 pandemic, increasing cyberattacks on healthcare organizations by 55%, along with an expected spike in attacks associated with the war in Eastern Europe.
This dilemma has necessitated a need to find alternative methods to ensure vulnerable medical devices, critical to the treatment of patients, are secured from threats and that the organizations and patients that rely on them are protected. Rather than wait for fixes, organizations have learned that they can take action now to execute security policies capable of segmenting at-risk devices on the network, allowing them to remain in services, and ensuring only the communication necessary for the device to function are allowed.
See. Know. Secure.
The process of isolating medical devices through network segmentation sounds simple, but it is not. Many MDMs lack complete knowledge of how, once deployed, their devices communicate within their respective hospital networks. The communication patterns, although similar, are not the same even for devices that have similar functions. At the same time, HDOs often lack the tools necessary to understand what devices they have and how they work in every given environment. They may not even know how many devices they have operating on their networks as our own research has shown a visibility gap of as large as 30%.
This has created a market for tools that can passively identify devices and automate the process of segmentation, while ensuring medical devices can continue to function correctly. Ordr is one such tool. Ordr is able to scan a hospital’s network and detect and identify all the devices that are connected and operational, providing full visibility of the organization’s complete asset inventory. That includes not only connected medical devices, but building controls, vending machines, exercise equipment, and even consumer-grade devices that may be in use.
Take Action to Mitigate Risk
Once all devices have been identified and inventoried, they are monitored and compared against a baseline of expected activity. This is done either because a certain device is already known to Ordr, or operations are established through use. Because medical devices must operate within narrow parameters, anomalies are easier to identify. Ordr can then apply security policies that keep medical devices on secure VLANs, isolated from other systems. Should an attack occur, automated response ensures that mission critical systems are kept out of harm’s way, limiting an attack’s “blast radius” within the connected environment.
If your organization is concerned over its potential risk exposure due to the use of vulnerable medical equipment, or if you need to take steps to fortify your network against the increasing threat of cyberattacks, get in touch with us. Many of the world’s most respected healthcare providers trust Ordr to protect their networks, patients, and reputations from the effects of a cyberattack. We can help you, too.
Benjamin Stock
Benjamin Stock is the Director of Healthcare Product Management at Ordr. Previously, Ben worked as the Director of Clinical Equipment Systems and Project Support at SSM Health St. Louis, MO. With more than 15 years of experience in healthcare technology management, his wealth of knowledge in the Clinical Engineering space allows him to be a wonderful advocate for Ordr healthcare customers. Ben is also a Certified Biomedical Equipment Technician (CBET).
Interested in Learning More?
Subscribe today to stay informed and get regular updates from Ordr Cloud
Ready to Get Started?
-
 BlogClosing the IoT Security Gap – Cadre and Ordr
BlogClosing the IoT Security Gap – Cadre and Ordr…unique IT environment. To do that requires a complete understanding of the IT estate; and a complete understanding of the IT estate requires device discovery that delivers total visibility into…

As a trusted advisor for cybersecurity, it’s important to be able to develop security strategies that match the challenges inherent in each customer’s unique IT environment. To do that requires a complete understanding of the IT estate; and a complete understanding of the IT estate requires device discovery that delivers total visibility into the estate.
In organizations that rely heavily on internet connected devices—the Internet of Things (IoT)—that level of visibility can be elusive. And for the unprepared, it’s going to get worse. That’s because there’s been a huge increase in IoT use across industry, and in healthcare and manufacturing especially. IoT deployments worldwide were at 10 billion in 2018 and are predicted to exceed 25 billion by the end of 2021. Some believe that number could more than triple by 2025, driven by the advent of 5G network connectivity.
Overcoming Historical Challenges
At Cadre we work with manufacturing and healthcare organizations with complex environments and a significant need to secure connected devices. Historically, protecting IoT devices in manufacturing and healthcare was a hard thing to do. Most organizations chose to either air gap their networks, or use a well-protected jump host to access the environments. On the manufacturing shop floor, where industrial sensors and controllers are used to maintain production, devices remained segregated from corporate networks.Now you have devices that are communicating not only internally with the owner, but out on the internet to supply chain partners. That dynamic has upended the Purdue Enterprise Reference Architecture (PERA) model, dramatically increasing organizational risk of malware infections and attacks by malicious actors. The stakes are even higher when the equipment you’re protecting is used for medical care. From an IT security perspective, you can’t treat a patient monitor or ventilator the same way you treat an HVAC controller.
When we learned about Ordr and its approach to securing IoT devices in these complex environments, we were intrigued. It was important to us that they are a Check Point integration partner with a strong, stable organization and track record of success. Our experience with the Ordr Systems Control Engine (SCE) has been great, so when we had a chance to evaluate Ordr’s IoT Discovery Program, a complete kit of zero-touch, cloud-managed IoT sensor and Ordr Core software, we were on board.
Ordr Core Lives Up to the Claim
Ordr Core quickly and easily discovers the full extent of an organization’s IoT asset inventory, allowing us to automatically populate the customer’s configuration management database (CMDB) with the profile of every device connected to the network. From there we can automatically generate and enforce appropriate policy based on device risk.Ordr Core has already become an indispensable tool for us to see into the customer’s environment, control the chaos, and implement complex security strategies like device segmentation at a level of granularity that was unattainable before.
Every time we run Ordr Core in a customer environment, or when evaluating prospective engagements, we find devices that were unknown to the CIO and CISO. Often these are older devices that had fallen out of view and were forgotten, but we also find unauthorized devices like consumer electronics that have no business being on the network in the first place.
Discover, Profile, Evaluate, Protect
Once Ordr Core discovers these devices, we are able to profile them and observe things like communications flow, and identify and evaluate the inventory of legacy devices. It’s easy to forget that, while the IoT market is in the midst of a renaissance, networked controls and sensors have been in use for decades. Many organizations rely on equipment that was made by companies that no longer exist, or that operates with obsolete operating systems or firmware that cannot be patched. All of this is easily understood by Ordr, and it gives us a clear view into the health, availability, and risk of the network and allows us to close a security gap that network access controls can’t handle natively.Ordr Core gives Cadre a competitive advantage with the ability to see across the entire IoT estate and derive insights that were not available before. We know there’s no slowdown in sight for the adoption of IoT, and every organization that relies on them has a compelling need to control and protect each device to keep it from becoming a point of entry for malicious actors.
If you’d like to see what your IoT environment looks like and take informed action to address the vulnerabilities you knew were there but couldn’t find, you can request your free zero-touch, self-provisioning Ordr Core sensor here.
Ken Dickey
Ken Dickey heads the Business Development department at Cadre. With over 29 years of experience in information technology, Mr. Dickey has established himself as an expert on IT security architectures and design.
Interested in Learning More?
Subscribe today to stay informed and get regular updates from Ordr Cloud
Ready to Get Started?
-
 BlogAligning Healthcare Cybersecurity for Connected Medical Devices
BlogAligning Healthcare Cybersecurity for Connected Medical Devices…to establish baseline best practices and measures of device maturity and process effectiveness, communicate complaints and discovered vulnerabilities, and institute remediation procedures. Episode Three of CHIME’s Medical Device Security webinar…
Security Bulletin
Aligning Healthcare Cybersecurity for Connected Medical Devices
New Federal Cybersecurity Law – Public Law 116-321
3Min ReadBy Ty Greenhalgh
A guest blog from Cyber Tygr’s Ty Greenhalgh addresses how to align strategies for operating and securing connected medical devices, IoMT, and other healthcare technologies with a new healthcare cybersecurity law that attempts to address exploitable weaknesses in healthcare IT. The second episode of the seven-part CHIME Medical Device Security webinar series aired last week. The episode addressed the topic of aligning healthcare cybersecurity for connected medical devices with a new cybersecurity law for healthcare. Once again, I moderated the episode under my new role as, Senior Account Executive with Nuvolo. I was joined by two industry experts who weighed in on the subject. Erik Decker, the CISO of Intermountain Healthcare, former Board Chair of the Association for Executives in Healthcare Information Security (AEHIS), and co-leader of the HHS task group implementing the Cybersecurity Act of 2015. Returning from Episode One was Rob Suárez, CISO of Becton Dickinson (BD) and chairman of the Medical Device Innovation Consortium’s (MDIC) Cybersecurity Steering Committee and the Advanced Medical Technology Association’s (AdvaMed) Cybersecurity Work Group.
The Cybersecurity Act of 2015, in particular its 405(d) provision, expressly calls out the healthcare industry. While the name “405(d)” offers little insight as to the legislation’s relevance to medical device security, Mr. Decker is uniquely positioned, perhaps more so than anyone else, to elaborate on its significance. As he explained, healthcare is officially designated as critical infrastructure and simply requires more protection. Cyber-attacks to hospital operations are direct threats to patient safety, and compromises to highly sensitive electronic health information threatens patient privacy rights. Ransomware attempts against healthcare are increasing, rising 123% in 2020, incurring $20.8 billion in downtime costs. 405(d) mandates the formation of an industry-led task group to publish a compendium of cybersecurity best practices, frameworks, methodologies, technologies, and other recommendations to serve as a set of Federally recognized cybersecurity practices that afford legal safe harbor to Health Delivery Organizations (HDOs) when implemented. In the words of Mr. Decker, “It’s a way to draw a line in the sand and say, ‘here is an example of what you can do that demonstrates best practice’; and if you do it, you get a benefit for it; and if you don’t, you might be hindered by it.” The cornerstone publication of the 405(d)-task group is Health Industry Cybersecurity Practices (HICP, pronounced liked ‘hiccup’). Comprised of three primary volumes, HICP has a main document providing a high-level summary of the threats and recommendations, and two technical volumes prescribing specific practices, including connected medical devices, to be implemented by IT specialists of small, medium, and large HDOs. Under the new law, Public Law 116-321, following the best practices for medical device security detailed in HICP will require the Office of Civil Rights within the HHS (OCR) to consider reductions in fines, audits and post breach oversight.
Next, Mr. Suárez discussed the Medical Device and Health IT Joint Security Plan (JSP), authored by a Healthcare and Public Health Sector Coordinating Council (HSCC) task group in 2019, which Mr. Suárez co-chaired. The JSP document proposes a voluntary framework in which responsibility for medical device security is disseminated across healthcare stakeholder organizations. Under the JSP, MDMs proactively aid their customers by developing and communicating processes, personnel training recommendations, device life-cycle strategy, vulnerability patches, decommissioning plans, and incorporating HDO feedback into future product design. HDOs work with their vendors to establish baseline best practices and measures of device maturity and process effectiveness, communicate complaints and discovered vulnerabilities, and institute remediation procedures.
Episode Three of CHIME’s Medical Device Security webinar series airs on Thursday, August 5th. If you missed Episodes One, you can view my recap here, or register for the entire series at https://store.ignitedigital.org/product?catalog=medical_device_security_webinar_series.
Acronym Glossary
- 405d: A provision within the Cybersecurity Act of 2015 (CSA). The CSA 405(d) document aims to raise awareness, provide vetted practices, and foster consistency in mitigating the most pertinent and current cybersecurity threats to the sector. It seeks to aid the Healthcare and Public Health (HPH) sector organizations to develop meaningful cybersecurity objectives and outcomes.
- AdvaMed: Advanced Medical Technology Association
- AEHIS: Association for Executives in Healthcare Information Security
- BD: Becton Dickinson
- CHIME: College of Healthcare Information Management Executives
- HDOs: Health Delivery Organizations
- HHS: Health and Human Services
- HICP: Health Industry Cybersecurity Practices
- HSCC: Healthcare and Public Health Sector Coordinating Council
- JSP:Medical Device and Health IT Joint Security Plan
- MDIC: Medical Device Innovation Consotium
- MDM: Medical Device Manufacturers
- OCR: Office of Civil Rights within the HHS
- Public Law 116-321: An act to amend the Health Information Technology for Economic and Clinical Health Act to require the Secretary of Health and Human Services to consider certain recognize security practices of covered entities and business associates when making certain determinations, and for other purposes
Ty Greenhalgh
For the last 4 years, Ty has been the CEO of Cyber Tygr, a company dedicated to improving and protecting the privacy, cybersecurity and compliance of our nation’s Health Industry by operationalizing advanced technologies. As a result of his intensive efforts in supporting the cybersecurity posture of healthcare medical devices and facility equipment, Nuvolo has brought him on board to spearhead their new Cyber OT module. Mr. Greenhalgh is an active member in several groups and associations, such as Healthcare and Public Health Sector Coordinating Council’s Joint Cybersecurity Workgroup, the Department of Health and Human Services 405(d) Workgroup and the Department of Commerce National Information and Telecommunications Agency.
Interested in Learning More?
Subscribe today to stay informed and get regular updates from Ordr Cloud
Ready to Get Started?
-
PagesEnterprise
…real-time visibility into all devices, cloud assets, applications, SaaS apps, and users—critical to deliver efficient, modern enterprise customer experiences and maintain business operations: Gain real-time, accurate asset data and insights…
- INDUSTRY
- ENTERPRISE
See. Know. Secure. Every Connected Asset in your Entire Enterprise.
Ordr delivers a building block approach to address enterprise organizations’ entire asset management journey on a single platform —from asset visibility all the way to Zero Trust.
REQUEST A DEMO
See, Know, Secure Every Asset in Your Enterprise
Incomplete Asset Inventory
Security teams find themselves investing considerable time and manual efforts in correlating data from various sources to answer questions about their security posture. Most asset management solutions cannot identify IoT and OT, leading to cybersecurity blind spots. Ordr unifies API, DPI and proprietary Ordr Discovery methods to deliver comprehensive and accurate asset insights on devices, users, applications, SaaS and cloud.
Attack Surface Reduction
Enterprise organizations face challenges in identifying and prioritizing vulnerabilities, exposures, and security gaps. Ordr provides a solution by automating the identification and providing context needed for remediation of critical risks, high-risk vulnerabilities, shadow IT, security coverage gaps, and non-compliant controls, allowing organizations to secure their attack surface effectively.
Identifying and Responding to Threats
Identifying not only known threats, but when an asset deviates from its normal behavior is crucial for early threat detection and response. During a security incident, swift response is essential. With Ordr, you can effectively detect anomalies, identify exploits or active threats, and automate your incident response process, ensuring the security and resilience of your enterprise.
SEE
Discover and Classify Every Asset
Utilizing API integrations and Ordr’s Discovery Engine, CAASM+ delivers real-time visibility into all devices, cloud assets, applications, SaaS apps, and users—critical to deliver efficient, modern enterprise customer experiences and maintain business operations:
- Gain real-time, accurate asset data and insights for devices, users, applications, SaaS and cloud, including hard-to-discover IoT and OT
- See granular device details like manufacturer, model, serial number, OS, support owner, connectivity and more.
- Identify issues like rogue or banned devices, and devices with outdated operating systems
- Pinpoint security coverage gaps such as endpoints missing MDM/EDR agents
- Map and analyze risky communications between assets and to the Internet
- Enrich CMDB with real-time asset visibility

KNOW
Reduce Risks and Exposures and Accelerate Incident Response
Ordr provides enterprise organizations with comprehensive visibility into the vulnerability landscape for both managed and unmanaged devices. Translate vulnerabilities into a prioritized action plan with risk scores and automated workflows assigned to the correct device owner, enabling efficient response actions. Detect cyberthreats that can pose significant risks to profitability and essential business operations, ensuring proactive threat mitigation.
- Gain comprehensive coverage of all vulnerabilities, including those on IoT and OT devices
- Prioritize vulnerabilities based on multiple asset and organizational risk factors and automate remediation for the right owners
- Detect active exploits and risky communications with an integrated IDS and threat intelligence feeds
- Identify devices behaving abnormally, based on baseline known-good communications
SECURE
Segmentation To Manage Risks
Segmentation is a cybersecurity best practice. Accelerate NAC and Zero Trust initiatives. Deploy Ordr to create segmentation policies that align to business needs – macro segmentation to isolate specific types of assets, and Zero Trust segmentation to limit vulnerable devices to baseline communications. Optimize policies based on enforcement points – firewalls, NAC or switches.
Accelerate NAC, Segmentation and Zero Trust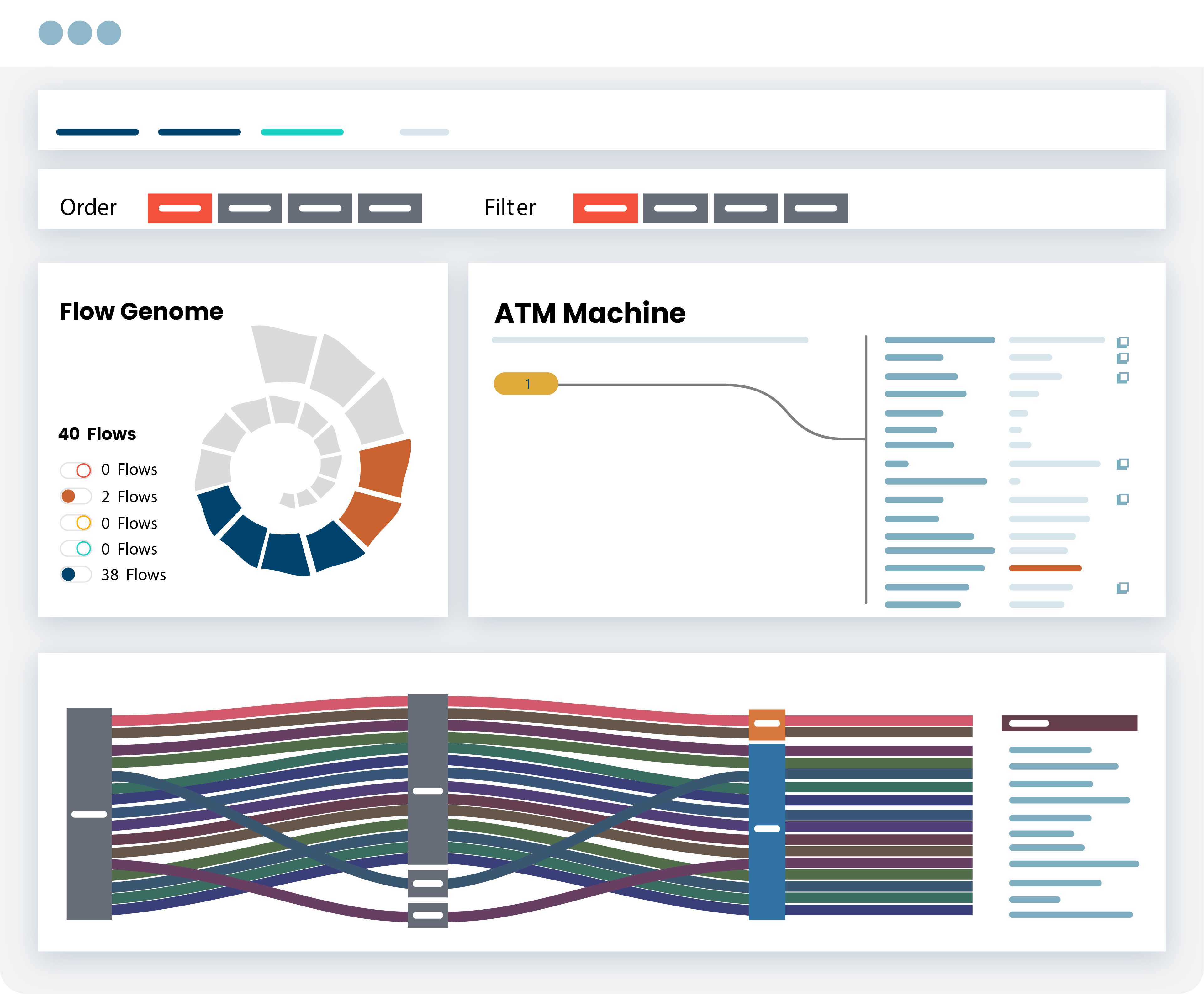
SECURE
Easily Address Compliance Regulations
Compliance can be a challenge for businesses, especially collecting data and evidence for board meetings and audits. With limited resources, automation is key to efficiently managing security controls and coverage gaps. Simplify compliance across various frameworks, such as NIST, CIS, Cyber Essentials, and other standards with Ordr’s comprehensive reporting tools designed to streamline the compliance process. Dashboards and reports can be customized based on the business’s specific needs.
Streamline Security Framework Compliance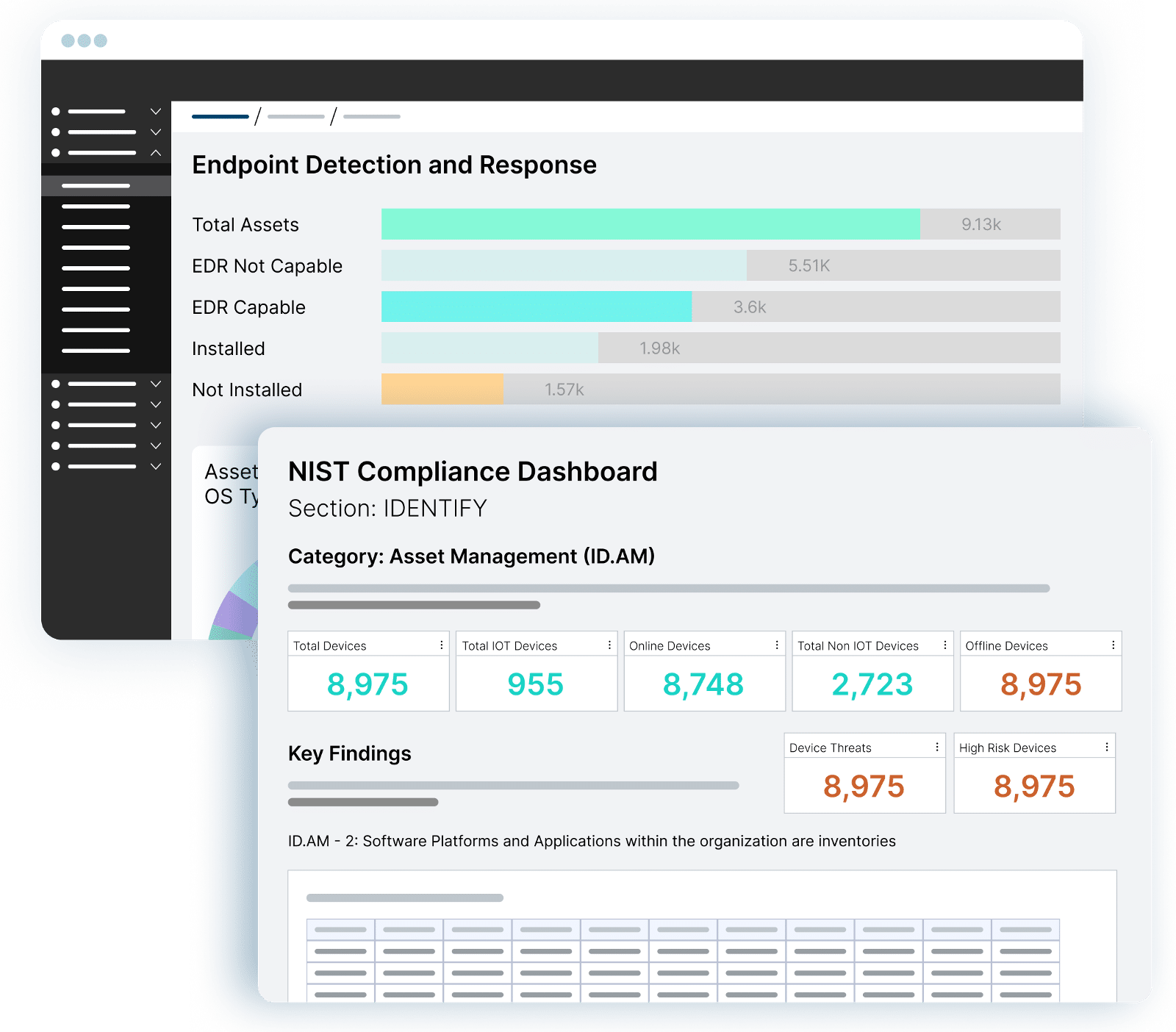
Ready to Start Securing Your Assets?
-
 BlogOrdr Named IDC Innovator for Healthcare IoT Security
BlogOrdr Named IDC Innovator for Healthcare IoT Security…healthcare organizations like Cleveland Clinic, Dayton Children’s Hospital, Mayo Clinic, Freeman Health, and many more. See why Ordr continues to earn kudos and customers, get in touch and we can…
Company News
Ordr Named IDC Innovator for Healthcare IoT Security
3Min Read
By Chris Westphal

The risks associated with a large, connected device attack surface in healthcare are hard to ignore in light of CISA and NSA threat warnings targeting OT and IoT. Tech analyst firm IDC recognized Ordr as a leading innovator in IoMT security solutions in a recent report. The risks associated with a large, connected device attack surface are getting harder to ignore. In recent weeks the U.S. Cybersecurity Infrastructure & Security Agency (CISA) and National Security Agency (NSA) issued a joint advisory on threats associated with operational technology (OT) such as the industrial control systems (ICS) that many critical infrastructure organizations rely on to run their facilities. Overseas the European Union enacted two new regulations mandating stricter cybersecurity requirements for connected medical devices, otherwise known as the internet of medical things (IoMT).
Ordr has been working hard to provide the means for organizations in industries like healthcare, financial services, manufacturing, life sciences, and government to protect themselves from those threats since 2015. And we are always happy when those efforts are recognized because it means more awareness of the dangers to critical systems and of the tools available to keep them protected.
Ordr Recognized as a Leader in Healthcare IoT Security
On September 20, International Data Corporation (IDC), one of the leading information technology market intelligence advisors, recognized Ordr as a leading innovator in IoMT security solutions in their report, IDC Innovators: Healthcare IoT Security Products, 2022.
IDC describes healthcare organizations as “high-value targets for cyberattacks. As more medical devices are connected, the attack surface that bad actors can exploit has increased dramatically and a single breach can lead to a multitude of undesirable outcomes. Meanwhile, traditional information technology (IT) cybersecurity solutions are not designed to protect the wide range of medical devices used in supporting healthcare.”
As more medical devices are connected, the attack surface that bad actors can exploit has increased dramatically. — IDC
Ordr Provides Ground-to-Cloud Protection
Ordr’s platform provides protection for those environments by enabling complete ground-to-cloud visibility of all IoMT, IoT, and OT devices whether they are on-premises or remote, no matter if they are communicating locally or across complex digital supply chains. Then, we provide precise, contextual, real-time understanding of the operations and data flows of each device on the network, automating dynamic security policy generation and enforcement in the event a threat is detected. We can do this because the Ordr Data Lake is populated with detailed operational profiles for millions of devices.
When any device strays from its deterministic parameters, Ordr detects that change and automates proscribed actions to protect the device and its operational ecosystem. This is vital to preventing attacks against connected devices, containing threats by blocking lateral movement to and from connected devices, and maintaining operational resiliency for critical infrastructure targets, like hospitals and healthcare organizations, that are frequently targeted by ransomware gangs.
Ransomware an Ever-Present Threat
“Ransomware is an ever-present threat and can be particularly devastating in the healthcare sector, where even a few minutes of downtime can have deadly consequences. Protecting connected medical devices, many of which were not designed with security in mind, is now a top priority for IT and biomedical engineering departments. Medical IoMT security products provide much needed ‘context’ about devices and how they are being used so that smart decisions can be made to reduce their cybersecurity risks,” said Ed Lee, research director, Internet of Things and Intelligent Edge: Security at IDC.
Medical IoMT security products provide much needed ‘context’ about devices and how they are being used so that smart decisions can be made to reduce their cybersecurity risks, — Ed Lee, IDC
In addition to this recognition from IDC, Ordr was named a healthcare IoT security market leader for an unprecedented third straight year by KLAS Research, recognized as a member of the CyberTech100 most innovative and pioneering companies that are helping financial institutions combat cyber threats and fraud, and is trusted by leading healthcare organizations like Cleveland Clinic, Dayton Children’s Hospital, Mayo Clinic, Freeman Health, and many more.
See why Ordr continues to earn kudos and customers, get in touch and we can provide a demonstration or answer your questions.
Chris Westphal
Head of Product Marketing
Chris is the Head of Product Marketing at Ordr where he helps drive awareness for connected device security and the value of the Ordr solution. Chris brings more than two decades of experience to his role with a background in enterprise security, cloud, and data center technologies. Most recently, Chris was head of product marketing at Salt Security, the leader in API protection, and has held product marketing leadership roles at companies including VMware, Illumio, and Adallom (acquired by Microsoft).
Interested in Learning More?
Subscribe today to stay informed and get regular updates from Ordr Cloud
Ready to Get Started?
-
 BlogWelcome to the hyper-connected enterprise
BlogWelcome to the hyper-connected enterprise…in advance to prepare for the inevitability of change and its effects of cybersecurity and risk? The history of enterprise computing is one of increasing scale, complexity and heterogeneity. First…

Every evolution in IT leaves business leaders and CISOs scrambling to protect their vital data, applications, and resources. What can your enterprise do in advance to prepare for the inevitability of change and its effects of cybersecurity and risk? The history of enterprise computing is one of increasing scale, complexity and heterogeneity. First there was client-server computing, ushering in the PC era where there was a computer for every employee and several switch ports in every cubicle. And then the mobile enterprise, with a new generation of employees using their laptops, tablets and smartphones all the time, everywhere.
With each leap forward, IT and business leaders have scrambled to catch up and to protect their most critical data, applications and resources. We’re still gasping from the effort it took to control BYOD. But as hard as that was, the challenge was fundamentally one of human scale. Most users had a small handful of devices. Some ran Windows, some IOS, some Linux. IT could assign most of those users to a relatively small number of roles (often as simple as “guests” vs. “employees”). Yes, certain classes of employees had different levels of access, but in truth IT rarely had to define more roles than there were departments on an org chart. Great vendors stepped forward with intelligent solutions to make role-based access work (mobility controllers, next-generation firewalls, NAC and identity management). A small number of insanely hard-working employees in IT and Security could keep up. Barely.
We are now experiencing the emergence of the hyper-connected enterprise, in which everything is connected. The HVAC system. Security cameras. Point of Sale devices. Digital signage. Sensors. Heart rate monitors and infusion pumps. Complex, multi-million dollar manufacturing systems. IoT devices of every kind. If these things aren’t working, productivity plummets, revenue drops and lives are impacted. And if business leaders don’t know where they are or how they are being used, they risk spending millions on unnecessary cap ex.
In every dimension, the challenge for IT and business leaders is several ordrs (sorry!) of magnitude greater than it was a few short years ago. Instead of 3-4 devices per employee, a Fortune 500 organization or healthcare system will have millions of connected devices, from hundreds of different manufacturers, many running a proprietary OS. Each class of devices is purpose-built — with specifically defined functions, unique behavior patterns and potential vulnerabilities. Where IT used to administer a small handful of user roles, these devices have no users and ‘roles’ do not apply. Instead of managing users, they need to regulate each individual device. And that means they need to define and enforce thousands of specific policies.
The resulting complexity is literally inhuman in scale. A seemingly simple task like completing an inventory of connected devices is neither simple nor feasible for human beings at such scale. It’s about as simple and feasible as counting the stars in the sky. Even if your staff could do it, the data they gathered would be out of date before their report was compiled. If humans can’t even count the devices, there’s no possible way they can monitor them, understand their myriad functions or apply appropriate security policies to them. And if the CFO asks them for a report on usage of these systems and devices as she’s preparing next year’s capital budget? Good luck.
The only way to address this inhuman complexity is by mapping the ‘device flow genome’ through the application of advanced machine learning at a truly massive scale, continuously processing enormous amounts of data to identify everything that is connected and baseline their behavior patterns. Once you can do that, you can identify unusual or dangerous patterns and using actionable AI to automatically create policies that prevent incidents from occurring. That’s what we mean by true ‘closed-loop security.’ And then, because of all the data you’d be processing, you could deliver incredibly valuable insights to business stakeholders about how those devices and systems are being used and how they are performing. That can save organizations millions and extend the life of their assets.
That may sound far-fetched, costly and difficult to implement, but it’s not. In fact, most organizations already have the necessary infrastructure and tools in place: routers and switches, wireless controllers, next-generation firewalls, NAC, and the intelligent vendor-provided systems that operate them . The problem is that even the largest organizations don’t have enough people to interact with each of those intelligent solutions to harness their power at the scale necessary. What’s been missing is a systems control engine capable of processing the massive amounts of data being generated by all of the systems and devices in the hyper-connected enterprise – and translating that information into actionable policies that your smart infrastructure can enforce.
That’s why Ordr exists and that’s what the Ordr Systems Control Engine does. At a massive scale, for the largest enterprises in the world. It’s complex. But we’re a team of networking and security veterans, and we’ve been working for years to build a solution capable of handling that complexity while making your life simple.
The hyper-connected enterprise is here. Take control.
Greg Murphy
Greg joined Ordr as CEO in December 2018. Previously, he was VP Business Operations for the HPE Aruba Group, the 4,000 person networking and IoT business unit of Hewlett Packard Enterprise. In that role, Greg was responsible for leading the business integration of Aruba and HP Networking following HP’s $3 billion acquisition of Aruba Networks in 2015. Greg held multiple prior senior executive positions within Aruba, including SVP Business Operations, GM of network management software, GM of outdoor and mesh products and VP of Marketing. Greg joined Aruba in 2008 through its acquisition of AirWave Wireless, a network management software provider that Greg founded and led. Greg received his M.A. from Stanford University and his B.A. from Amherst College.
Interested in Learning More?
Subscribe today to stay informed and get regular updates from Ordr Cloud
Ready to Get Started?
-
 BlogThe Future of Connected Devices
BlogThe Future of Connected Devices…factors are required for success — collaboration across government and industry on regulation and standards, commitment from device manufacturers to build security into design, prioritization by IT, security and device…
Security Strategy
The Future of Connected Devices
National Cybersecurity Awareness Month
3Min Read
By Danelle Au

As we wrap up Cybersecurity Awareness Month, it’s worth noting that the final week’s theme is “The Future of Connected Devices”.
The theme seems timely as this is also the same week that CISA issued an advisory on an imminent ransomware attack against healthcare organizations. In the advisory, CISA, FBI, and HHS said they had credible information that malicious cyber actors were targeting the healthcare vertical with Trickbot malware, “often leading to ransomware attacks, data theft, and the disruption of healthcare services.”
Cyber attackers thrive on confusion and chaos, and it is clear that they are taking advantage of the current rise in COVID-19 cases. As hospitals scramble to respond to the increase in cases, they are deploying more medical and IoT devices that are potentially vulnerable to cyberattacks. We now know that attacks not only impact the bottom line (example ransomware payments) but can disrupt facilities in ways that may be fatal to patients.
Which brings us back to this week’s theme; it’s clear the future of connected devices is a critical problem that needs to be addressed. While this week’s headlines are about vulnerable healthcare organizations, IoT devices are so pervasive that securing them is a challenge that needs to be addressed in all industries. The future of connected devices requires collaboration among three entities – manufacturers of these devices, IT and cybersecurity teams, and IoT security vendors (like Ordr).
IoT Device Manufacturers
IoT device manufacturers play a key role in the future of connected devices. If more devices are built with security in mind, we can eliminate some fundamental issues such as insecure software stacks (that led to Ripple20 vulnerabilities), generic default passwords, or unsecured backdoors on devices.
Requirements are being built into government and industry standards. NIST has been working on a draft of foundational security functionality that needs to be built into products. The FDA now has oversight of medical device security. And, on September 14th, the House of Representatives voted in favor of the IoT Cybersecurity Improvement Act of 2020, that will establish minimum security standards for Internet of Things devices owned or controlled by the Federal Government.
Additionally, there are several IoT industry standards being worked on by the IoT Security Foundation, the IEEE, the Trusted Computing Group, the IoT World Alliance and the Industrial Internet Consortium Security Working Group.
IT and Cybersecurity Teams
IT and cybersecurity teams need to prioritize the security of connected devices in their network for two reasons. First, these devices are typically critical to their business and any issues will impact operations. Second, the massive volume of these devices, compared to managed endpoints such as laptops and servers, means that there is a massive attack surface that is new.
In order to successfully implement an IoT security program, IT and cybersecurity teams need to work with connected device owners that can range from biomedical and HTM teams, and physical security teams, to facilities or IT Operations teams. They also need to consider a comprehensive device security lifecycle for every device their bring into their environment, and demand the highest levels of security from manufacturers.
IoT Security Vendors
IoT security vendors need to continue to innovate because IoT devices will continue to have security shortcomings. Even if security standards forced device manufacturers to adhere to security standards today, many legacy devices will continue to exist.
Ordr is playing our role in making sure that our platform is easy to deploy, supports visibility and security of all devices – IoT, IoMT, OT, and can deliver value to all stakeholders. We’re also innovating with AI — the Ordr platform was built to have the resiliency to respond at the speed and scale necessary to deal with the massive volume of IoT devices. Our machine learning technology enables us to classify devices in a way that does not require manual intervention, allows us to baseline “normal” device behavior and automate action.
In summary, the future of connected devices holds tremendous promise for many industries. However, in order to truly realize the promise of these devices requires security. This is where multiple factors are required for success — collaboration across government and industry on regulation and standards, commitment from device manufacturers to build security into design, prioritization by IT, security and device owners security teams on IoT security projects , as well as continued innovation by IoT security vendors. The future of connected devices requires that we do this on an accelerated timetable to cope with the massive growth of IoT devices expected in the next 5 years.
Danelle Au
Danelle Au has more than 20 years of experience bringing new technologies to market. Prior to Ordr, she was CMO at Blue Hexagon, a deep learning for malware protection company, and CMO at SafeBreach where she helped build the marketing organization and and define the Breach and Attack Simulation category. Previously, she led strategy and marketing at Adallom, a cloud security company acquired by Microsoft. She was also Director, Security Solutions at Palo Alto Networks, driving growth in critical IT initiatives like virtualization, network segmentation and mobility. Danelle was co-founder of a high-speed networking chipset startup, co-author of an IP Communications Book and holds 2 U.S. Patents. She has an MSEE from UC Berkeley
Interested in Learning More?
Subscribe today to stay informed and get regular updates from Ordr Cloud
Ready to Get Started?
-
 BlogImproving the Nation’s Cybersecurity: A Reflection on the Executive Order
BlogImproving the Nation’s Cybersecurity: A Reflection on the Executive Order…one of the voices speaking in support of greater federal involvement and calling out the need for greater attention to protecting public services and infrastructure. And we were pleased to…
Security Strategy
Improving the Nation’s Cybersecurity: A Reflection on the Executive Order
3Min Read
By Greg Murphy

On the afternoon of May 12, President Joe Biden issued his Executive Order on Improving the Nation’s Cybersecurity. The executive order came on the heels of a ransomware attack that shut down operation of a major U.S. refined products pipeline system, a critical infrastructure operator that supplies approximately 40% of the gasoline supply to states along the U.S. East Coast.
As gasoline stopped flowing from suppliers to service stations, prices shot up, shortages broke out and drivers rushed to fill their tanks, unsure of how long the effects would last. The impact of this attack was consequential, dramatically illustrating the vulnerability of key pieces of our economy, but it was not an isolated event. The Executive Order on Improving the Nation’s Cybersecurity was not a knee-jerk reaction to a singular event. It is the result of years of attacks on government, industry, and individual organizations and of a steady cry from both the public and private sector to enlist the resources of our federal government in the fight against cybercrime.
Ordr has been one of the voices speaking in support of greater federal involvement and calling out the need for greater attention to protecting public services and infrastructure. And we were pleased to see that the new executive order called out the need to focus attention not just on information technology (IT), but on operational technology (OT), and the importance of Zero Trust.
OT Security
Operational technologies are the industrial hardware and software systems that form the backbone of industry. Manufacturing equipment, scientific equipment, facilities management controls, transportation and logistics infrastructure, and, yes, the valves and monitors and other gear essential to managing critical operations.
In many cases these systems were not designed with cybersecurity in mind and have been in place for decades. But, as our world grows more interconnected and dependent on technology, the lines between IT and OT have blurred. Those vulnerable systems are an attractive target for threat actors who can exploit weaknesses in IT infrastructure to move laterally into OT networks and execute attacks intended to extract valuable data, or disrupt operations through sabotage or extortion. Read Jamison Utter’s article on 90% of OT Security attacks being primarily common attacks like ransomware, and our Dir of Product Management Srinivas Loke’s response to DarkSide to understand our perspective more.
Zero Trust for Connected Devices
We are also pleased to see Zero Trust called out as one of the key architectural tenets within the executive order. When it comes to the volume of connected IT, IoT, IoMT and OT in particular, it is impossible for any security team (even the government) to “react” to potential security alerts with these devices. Visibility into devices and their risks, along with proactive Zero Trust policies for mission-critical or vulnerable devices will limit the attack surface and mitigate risks, reducing the Security Operations Center (SOC) or Cyber Security Incident Response Team (CSIRT) burden of investigating alerts.
We’ve been advocating for Zero Trust for connected device security for several years now, and in fact, our platform is designed to make it simple to not only create Zero Trust network policies but also ensure that they can be properly enforced across existing networking and security infrastructure.
The executive order has set a number of priorities, including:
- Improve the Federal Government’s ability to detect vulnerabilities and incidents on federal government networks;
- Standardize the playbook for responding to cybersecurity vulnerabilities and incidents; and,
- Improve the Federal Government’s investigation and remediation capabilities following cyberattacks.
At first glance, the Executive Order on Improving the Nation’s Cybersecurity seems to set overly ambitious goals for meeting these objectives on aggressively accelerated schedules. In fact, the clock is already ticking on deadlines that arrive in as little as 14 days. But the experience and innovation that has been happening within the private sector puts these goals well within reach.
For our part, Ordr already works with many federal agencies to achieve the goals and objectives the White House has articulated. Our technology is adept at identifying the many vulnerabilities that plague OT, and at executing real-time response to detect and isolate attacks that occur, preventing threat actors from moving laterally to gain the information and leverage they need to disrupt operations. We are also proven in our ability to execute Zero Trust policies in industries like healthcare, manufacturing, financial services, education, and more. We are eager, excited and ready to be a part of the mobilization effort that improves the nation’s cybersecurity.
Greg Murphy
Greg joined Ordr as CEO in December 2018. Previously, he was VP Business Operations for the HPE Aruba Group, the 4,000 person networking and IoT business unit of Hewlett Packard Enterprise. In that role, Greg was responsible for leading the business integration of Aruba and HP Networking following HP’s $3 billion acquisition of Aruba Networks in 2015. Greg held multiple prior senior executive positions within Aruba, including SVP Business Operations, GM of network management software, GM of outdoor and mesh products and VP of Marketing. Greg joined Aruba in 2008 through its acquisition of AirWave Wireless, a network management software provider that Greg founded and led. Greg received his M.A. from Stanford University and his B.A. from Amherst College.
Interested in Learning More?
Subscribe today to stay informed and get regular updates from Ordr Cloud
Ready to Get Started?