Search Results:
”Quiz 2024 SAP C-ARSOR-2308: Marvelous SAP Certified Application Associate - SAP Ariba Sourcing Valid Dumps Book 🐮 Open ▷ www.pdfvce.com ◁ and search for ➥ C-ARSOR-2308 🡄 to download exam materials for free 🏑C-ARSOR-2308 Customizable Exam Mode”
-
 BlogOrdr Security Bulletin: MOVEit Vulnerabilities
BlogOrdr Security Bulletin: MOVEit Vulnerabilities…Ordr IDS engine detecting the session to prohibited IPs associated with MOVEIt Track communications to compromised IP/URLs: In real-time, Ordr’s external IP/IOC tracks every communication to prohibited IP/URLs. Ordr uses…
Security Bulletin
Ordr Security Bulletin: MOVEit Vulnerabilities
5Min Read
By Pandian Gnanaprakasam

Vulnerabilities found in the managed file transfer (MFT) solution MOVEit put enterprises at severe risk of cyberattack and data breach. Thousands of customers have already been affected. Ordr can help you find, mitigate the risk. Coauthors: Srinivas Loke, Gowri Sunder Ravi
Progress Software, which makes the MOVEit Transfer app, first disclosed a vulnerability for the MOVEit application on May 31st, 2023. The MOVEit application is a managed file transfer software produced by IPSwitch (acquired by Progress Software Corporation). It encrypts and uses secure FTP to transfer data with automation. MOVEit is used by thousands of enterprises, including 1700 software companies and 3.5 million developers. MOVEit is also used significantly within the healthcare industry, with HHS recently issuing an alert on this.
1. What Are The MOVEit Vulnerabilities?
CVE-2023-34362, with a CVSS score of 9. 8, is a critical SQL injection vulnerability affecting MOVEit Transfer and MOVEit Cloud. The vulnerability allows unauthenticated attackers to control a MOVEit installation completely, potentially leading to data alteration or theft, malicious software installation, and server configuration changes. The MOVEit Transfer versions affected are:
- before 2021.0.6 (13.0.6), 2021.1.4 (13.1.4), 2022.0.4 (14.0.4), 2022.1.5 (14.1.5),
- and 2023.0.1 (15.0.1)
Following this disclosure, two additional vulnerabilities were disclosed for a total of three to date:
- CVE-2023-35708 (June 15, 2023) with patching recommendations here:
- CVE-2023-35036 (June 9, 2023) with patching recommendations here:
- CVE-2023-34362 (May 31, 2023) with patching recommendations here:
2. Has this vulnerability been exploited?
Exploits of the vulnerability have been discovered in the wild, and have been attributed to the Cl0p ransomware group (also known as FIN11 or Lace Tempest). It has been reported that attacks against this vulnerability were “zero-day attacks” and may have begun as early as May 27, 2023, before a patch was available or the vulnerability was publicly disclosed or discussed.
3. Recommendations by Progress Software
- Disable all HTTP and HTTPs traffic to your MOVEit Transfer environment
- More specifically, modify firewall rules to deny HTTP and HTTPs traffic to MOVEit Transfer on ports 80 and 443 until the patch can be applied.
- Review, Delete, and Reset
- Delete Unauthorized Files and User Accounts (Particularly looks for an event associated with human2.aspx)
- Delete any instances of the human2: aspx (or any files with the human2 prefix) and .cmdline script files.
- On the MOVEit Transfer server, look for any new files created in the C:\MOVEitTransfer\wwwroot\ directory.
- On the MOVEit Transfer server, look for new files created in the C:\Windows\TEMP\[random]\ directory with a file extension of [.]cmdline
- On the MOVEit Transfer server, look for new APP_WEB_[random].dll files created in the C:\Windows\Microsoft. NET\Framework64\[version]\Temporary ASP .NET Files\root\[random]\[random]\ directory:
- Stop IIS (iisreset /stop)
- Delete all APP_WEB_[random].dll files located in C:\Windows\Microsoft. NET\Framework64\[version]\Temporary ASP. NET Files\root\[random]\[random]\
- Start IIS (iisreset /start). Note:The next time the web application is accessed, it will be rebuilt correctly. It is normal to have 1 APP_WEB_[random].dll file located in this directory.
- Apply the Patch
4. How Ordr Can Help
Detection
Vulnerability mapping of impacted devices:
- Ordr provides application mapping via its Software inventory Collector to detect MOVEit applications in the network and uses its Vulnerability Matching engine to identify whether the organization is impacted:
- Using its Software Inventory Collector, Ordr provides visibility into all the apps installed on all enterprise or health system devices, workstations, and servers.
- Ordr maintains a list of all the software packages installed on the endpoints with version numbers and a time stamp on when it was installed/last updated etc.,
- Ordr vulnerability mapping engine assigns vulnerabilities based on the SW version collected from the endpoint. The installed application list is updated daily, and vulnerabilities are recalculated based on the new info.
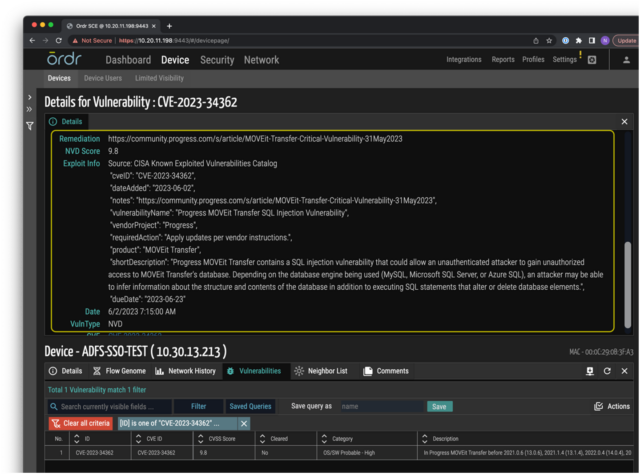
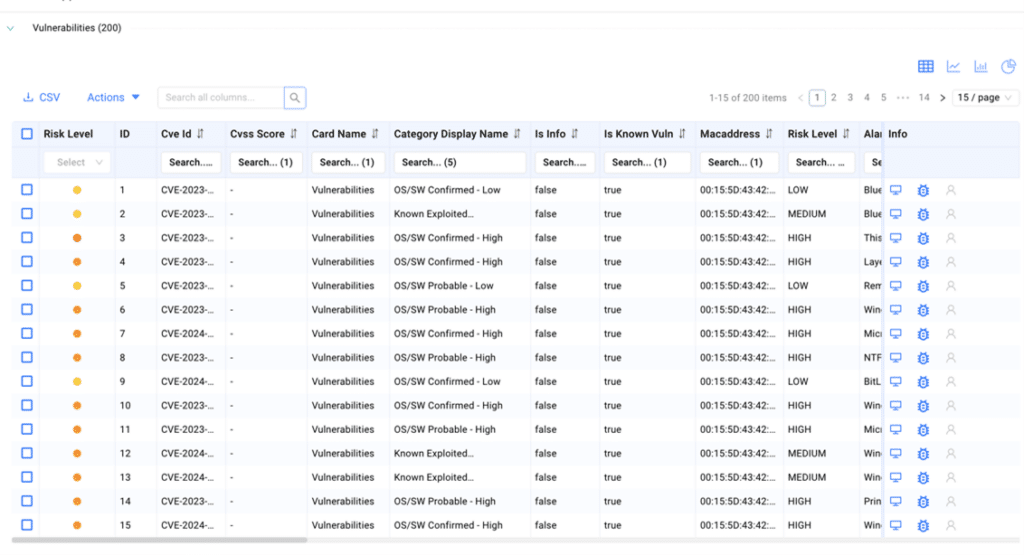
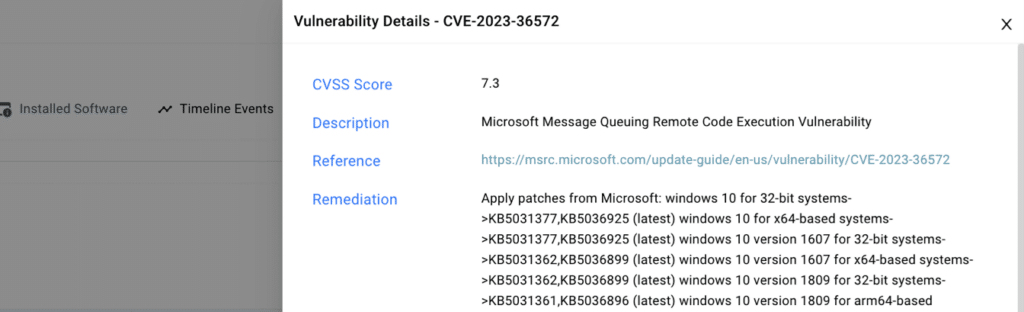
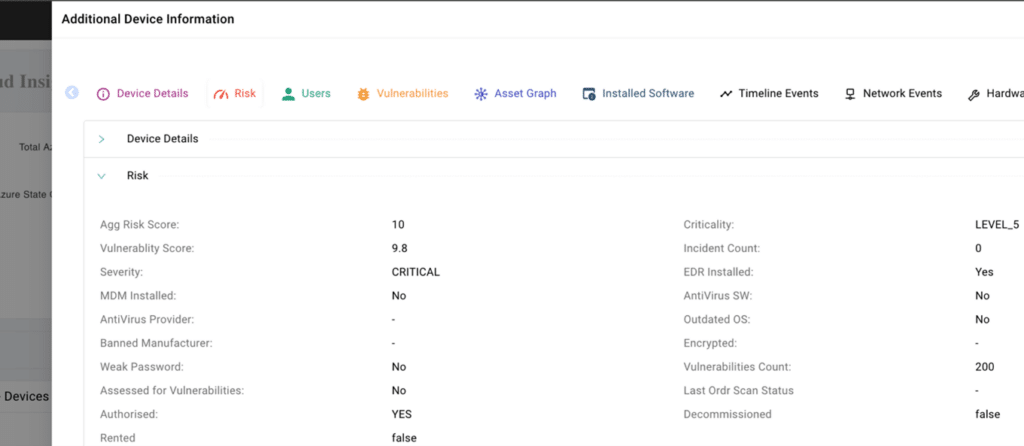
Figure 1:Details of a device affected by this vulnerability Real-time detection of exploits using IDS, behavioral violation, and threat correlation:
- Ordr has an IDS engine that can detect this specific vulnerability using analysis of packets transacting over the wire.
- Ordr IDS signatures have been updated to detect exploits of the MOVEit vulnerability
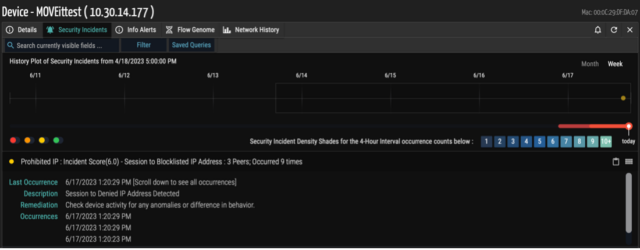
Figure 2: Ordr IDS engine detecting the session to prohibited IPs associated with MOVEIt Track communications to compromised IP/URLs:
- In real-time, Ordr’s external IP/IOC tracks every communication to prohibited IP/URLs. Ordr uses a cloud-based threat intelligence platform where the list is continuously updated, and all communications are marked accordingly in the Ordr Security Threat Card.
- Ordr scoured the internet to establish a list of MOVEit IPs/URLs and tracks all communications associated with this vulnerability with a “group” within the Ordr Traffic Analysis Tool outer ring. Ordr has named it “MOVEIT” in the classification analysis. All the lookups done using this method are retrospective in nature and map every communication to these IoCs.
- Users can easily track and tag every device communicating with malicious IPs for remediation purposes.
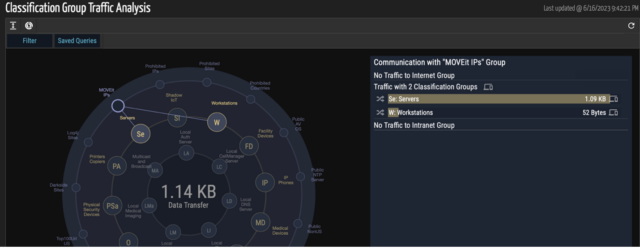
Figure 3: Traffic analysis based on communication to IPs associated with groups exploiting MOVEit Baseline communications to surface anomalies:
- Ordr also provides the capability to baseline all the communications based on profile, location, business function, or any customized entity using our AI/ML techniques. Ordr can trigger anomalies based on any deviations observed for this traffic. Ordr recommends using our behavioral anomaly and threat detection capabilities to identify anomalies while performing any incident response or remediation.
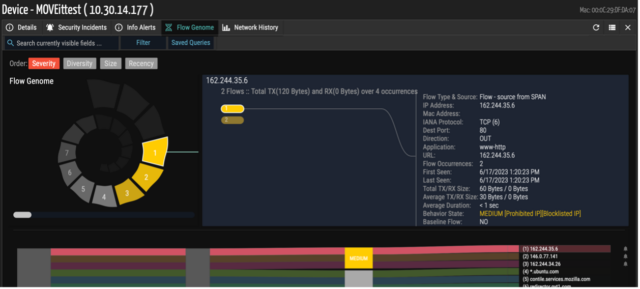
Figure 4: Ordr Flow Genome to baseline and map communications for MOVEit - Ordr adjusts the risk score of the device based on the events detected for the device along with the asset criticality. For example, Ordr assigns a higher risk score for devices with vulnerability and exploits vs. devices only with vulnerability. All of the risk scores are normalized based on the criticality.
Mitigation
- M1051 (ATT&CK) – Update Software
- Patch immediately. Refer to the Progress Software Knowledge Base above and apply the fixed versions of MOVEit Transfer.
- M1040 (ATT&CK) – Behavior Protection on Endpoint – Rapid threat containment if a breach is detected.
- Ordr tracks every device’s connectivity and keeps real-time data on where the device is connected to in the enterprise network – wired switch, wireless AP, VPN, and so on.
- When an alarm of a breach comes into the SOC team, the Ordr platform provides a one-click action to immediately get the device isolated or segmented into a quarantine VLAN.
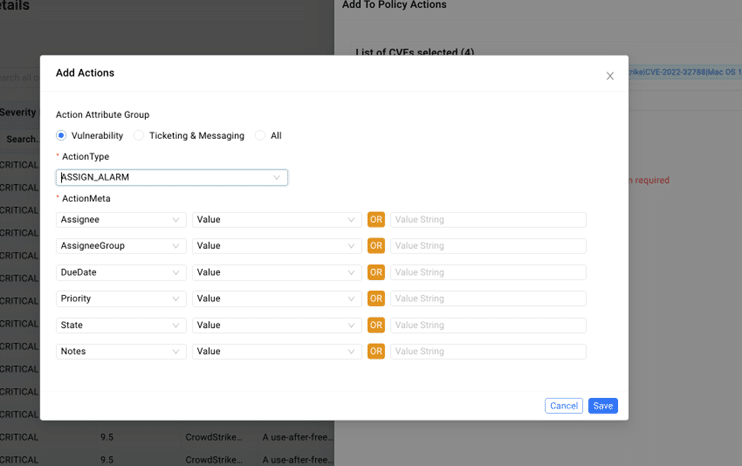
- Ordr supports a variety of threat containment actions, as shown below:
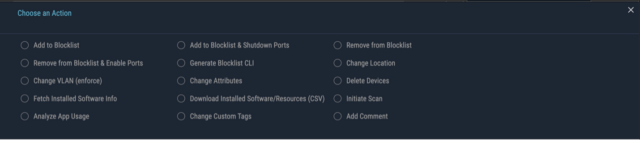
Figure 5: Ordr Mitigation Actions For MOVEit - M1037(ATT&CK) Proactive firewall policies:
- Disabling HTTP (port 80) and HTTPS traffic (port 443) to MOVEit Transfer in the interim is recommended to prevent exploitation.
- Create a policy profile with all the MOVEit servers, then build a firewall policy to block ports 80 and 443 inbounds from an external address.
- Ordr supports integration with multiple industry-leading firewall vendors. Below is a sample screenshot of one vendor.
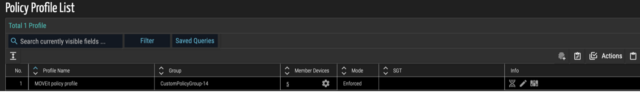
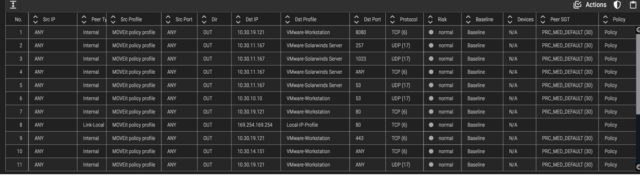
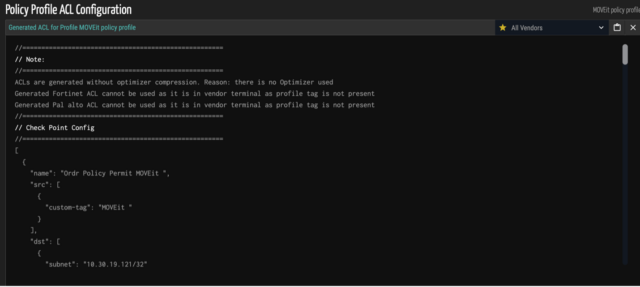
Figure 5: Create a policy profile for MOVEit servers and create policies on your firewalls (Check Point example) - M1030(ATT&CK) – Network Segmentation:
- Ordr’s segmentation policies can protect the mission-critical devices
- Even if a breach happens, mission-critical devices, for example, medical or devices in ER/OR, can be protected using Ordr policies. Only specific devices over certain protocols can communicate with these mission-critical devices.
- Ordr supports integration with multiple industry-leading NAC vendors.
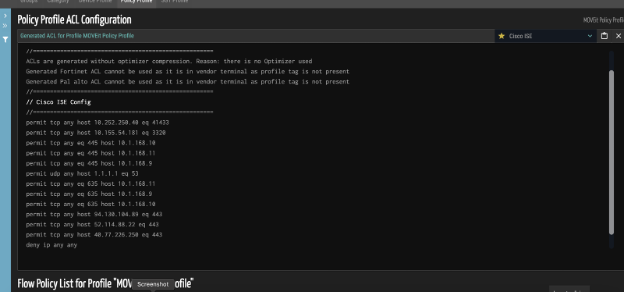
Figure 6: Create Zero Trust segmentation policies automatically, pushed on your NAC (Cisco ISE example) 6. Ordr Customer Updates
Ordr has prepared the following software configuration rules package (no software change required) and is working with customers on pushing them to their separate instances with utmost priority:
- Ordr Vulnerability Database to match against devices vulnerable to MOVEit.
- Ordr IDS engine to detect exploits related to MOVEit vulnerability.
- IoCs associated with MOVEit vulnerabilities are constantly updated and all the existing and new communications are mapped against these IoCs and are updated in the Ordr’s traffic analytics diagrams.
- All the indicators of compromise will be flagged on the Ordr’s security page and added to the alerts. Ordr constantly streams to the SOC/SIEM and sends emails to the admin if configured.
7. Helpful Links
- Detailed analysis blog
- Progress Software community advisory & Progress Software community article
- Artifacts
- POC
- Tenable Blog & CVE article
- NVD
- Talos Blog
- Other references from Sophos and First Health Advisory
Pandian Gnanaprakasam
Pandian has more than 20 years of product and engineering leadership experience and is also a serial entrepreneur. Before founding Ordr, he was the Chief Development Officer at Aruba, responsible for all of engineering and product management functions. Aruba, an enterprise mobile wireless company, was acquired by HPE for $3 Billion in March 2015. Before Aruba, Pandian served as the head of engineering for Cisco’s multi-billion-dollar Wi-Fi business unit and before that as VP of engineering for low-end switching product lines. He graduated with a master’s degree in Electrical Engineering from IIT, Chennai, India and holds several patents to his credit in various networking technologies.
Interested in Learning More?
Subscribe today to stay informed and get regular updates from Ordr Cloud
Ready to Get Started?
-
Knowledge BaseUnderstanding Agentless Asset Discovery
…have continuous, up-to-date information, you gain greater security coverage and prevent device use if they’re not in compliance. Ordr provides continuous asset discovery and allows you to drill into non-compliant…
Understanding Agentless Asset Discovery
5Min ReadWith a new wave of devices like IoT and OT, the fourth industrial revolution has created some unique issues and use cases for cybersecurity personnel. Such assets haven’t previously been connected to a network with direct internet access, but new network configurations and cyber threats have made these types of devices just as vulnerable as other IT devices. Agentless asset discovery can be used with these devices, in order to ensure that they’re secure on the network.
What is Agentless Asset Discovery?
Agentless asset discovery is the process of cataloguing each device on your network, without software installation onto each individual device. Agentless asset identification is via DPI (Deep Packet Inspection) whereby the packet and communications of a device is analyzed. With Inspection of communication flows and the application packets themselves, you can often determine make, model, software load, and even serial numbers, all without installation of an agent.Additional enrichment of this data, and further classification by machine learning and compared to a catalog of millions of devices allows for accurate device identification and classification.
Let’s look at a common, modern network use case. An employee at a sporting event receives an urgent work call. The employee uses his tablet to connect to the company network to view current information about the incident. Passive agentless asset discovery picks up this device as it monitors the network and collects metrics, such as manufacturer, make, model, and operating system. It also validates that the device hasn’t been exposed to known threats or vulnerabilities. The passive agentless discovery solution can also validate the OS, including patch levels and application inventory.
Agent vs Agentless Discovery
Agent-based asset discovery is using one or more agent software installations on the target system(s) to collect information and metrics about the target system and send that data to a centralized monitoring system, such as a hub, a collector, a server, etc. Typically, agent software must be manually installed on each target device via direct installation on the physical asset or remote installation using SSH, RPC, or other comparable methods. Some agents may be able to be installed via automation, but these agents aren’t available with all agented discovery solutions.
Both agent and agentless asset discovery collect asset information and metrics. However, agent discovery is more in-depth because it is installed directly onto the device being discovered, but it comes with a much greater deployment and maintenance overhead. Agentless discovery offers the luxury of not needing to be deployed onto each device, so it offers better resource and time efficiencies.
Performance latency must also be considered, especially in older legacy devices. While agentless discovery can cost more network overhead and can be dependent on network conditions, it does not require an agent to be deployed. Older legacy devices may not be running the right operating system to support an agent. In addition, newer devices like IoT, IoMT and OT also cannot support an agent because of the limited software footprint and performance latency impact.
Support Device Variety with Agentless Discovery
Almost any device in your network environment can be discovered using agentless discovery. There are certain situations when agentless asset discovery is clearly your best—or sometimes only—option. For example, the growing use of assets can only use agentless discovery since they simply can’t have an agent installed. Such assets include IoT, OT, and medical devices (IoMT). But whether or not the agent can be installed on the device isn’t the only consideration. In some cases, the costs, time, and/or resources associated with agent discovery for every device simply could be too high. By utilizing agentless discovery, you can meet asset discovery requirements in the most effective and efficient manner.
A solution like Ordr means your organization can rapidly discover all its assets, classify them based on type and function, and then assess them for risk. Using a product developed by Ordr allows your organization to build the most accurate and comprehensive asset inventory of what’s in your network, and identification of key risks, without impacting business operations.
Asset Transparency on a Network with Agentless Discovery
With agentless asset discovery, you gain real-time visibility to assets in the organization’s domain. Such discovery allows your organization to gain highly granular insights about the devices on the network and use those details to monitor for potential security issues.
A robust solution with agentless asset discovery makes it possible for you to dynamically create and impose segmentation on devices that are deemed high-risk. It also delivers the means to identify the compliance and risk postures for devices in the network. A solution, like Ordr, can also integrate the asset inventory with CMMS and CMDB databases for asset reconciliation, and in order to trigger workflows for any vulnerabilities that need to be addressed. Furthermore, it provides an integration with Active Directory to establish context on what device the user is on and use duration.
Monitor Traffic Flows Between Devices
Agentless asset discovery delivers unified monitoring of traffic flows between the devices connected to the network. It can classify both managed and unmanaged devices, which allows your organization to monitor the traffic flows of all connected devices. This traffic monitoring can baseline communication patterns, identify anomalous traffic such as communication made to malicious sites outside of the organization—including traffic to known security threats like malware or phishing sites, and deliver an audit trail of the device communications with other network systems.
You can’t secure what you can’t see, or don’t know about. This unified view and complete device visibility, including traffic flows, is the first critical step for your cybersecurity strategy. Ordr uses agentless asset discovery that doesn’t interfere with device function and employs device behavior monitoring using machine learning to create a flow genome—a conversation map of the communications pattern of every device connected to the network. This flow genome also learns the network topology and provides security personnel and networking groups the information they need to analyze monitored traffic. Ordr makes it easy to determine what devices are currently doing, identify their unique risk scores, and discover any vulnerability gaps.
Identify Vulnerabilities and Meet Compliance
Continuous asset monitoring is crucial. When your organization performs asset management and monitoring periodically, or as a “point-in-time” audit, it can lead to security gaps as a vulnerable device may be offline during the designated period. This visibility gap can lead to potential security issues, if the vulnerabilities on those devices are not patched. For many organizations, inventory management is performed as a periodic point-in-time audit. When you have continuous, up-to-date information, you gain greater security coverage and prevent device use if they’re not in compliance.
Ordr provides continuous asset discovery and allows you to drill into non-compliant devices and isolate them from the organization’s network. Our solution also monitors devices for risks like active threats, anomalies, bad URL/site connections, or known vulnerabilities. With Ordr, you have the complete picture of all devices on the network, including ones that belong to visitors or contractors.
Agentless Discovery and Your Organization
Agentless asset discovery gives your organization flexibility and real-time asset information for all the devices in the company’s network. It provides the ability to monitor vital traffic, identify security risks, and assist with meeting compliance or industry regulations. With a unified view of your assets and traffic at any point in time, you can detect behavior changes before a cybersecurity threat is executed.
Organizations gain a plethora of advantages from a complete, up-to-date asset inventory of devices connected to the network in real time. Ordr delivers a unified view of all the managed and unmanaged assets on your organization’s network, including IoT, OT, and IoMT devices. Not only does Ordr allow individual device behavior monitoring, but it also ensures that your devices behave as they should, based on their uniquely defined behaviors. With the added ability to integrate with your organization’s existing applications, like ITSM, CMMS, or CMDB solutions, Ordr helps you get more value out of your existing investments.
Interested in Learning More?
Subscribe today to stay informed and get regular updates from Ordr Cloud
Ready to Get Started?
-
 BlogOrdr Teams up with Cisco to Keep Connected Devices Secure
BlogOrdr Teams up with Cisco to Keep Connected Devices Secure…prompts you to question your assumptions of trust at every access attempt. This comprehensive solution to secure all access across your applications and environment, from any user, device, and location,…
Risk Management
Ordr Teams up with Cisco to Keep Connected Devices Secure
5Min Read
By Pandian Gnanaprakasam

The Cisco+Ordr collaboration embraces and enables Zero Trust – a strategic approach to security that centers on minimizing the attack surface by enforcing trust from an organization’s network architecture. Zero Trust prompts you to question assumptions of trust. Learn how Cisco+Ordr does it. Cisco has been a mainstay of Silicon Valley for decades, launched in 1984 by two Stanford University computer scientists with a vision of creating technology for the “network of networks” that paved the way for interconnecting the entire world into a single seamless system as we see today. Its fortunes have ascended as its hardware became ubiquitous. Now ranked No. 63 on the Fortune 100 list, Cisco has recently eclipsed Microsoft as the world’s most valuable company.
Not surprisingly, Cisco hardware has made its way into the digital infrastructures of tens of thousands of organizations over the past three-plus decades. The Cisco Catalyst 9000 Series is Cisco’s flagship switching portfolio. Enterprises worldwide rely on the Cisco Cat9k to power transformative solutions, not only as part of its core capabilities but also via a variety of Cisco and partner applications hosted on the switches. Today, Ordr announces the ability of our sensor to be deployed as a hosted application on the Cat9k, which not only extends visibility and insights on connected devices to any site a Cat9k switch is deployed but also extends Zero Trust segmentation to the edge. This, together with our recent offering on the Meraki Marketplace provides every Cisco Identity Services Engine (ISE) and Software-Defined Access (SDA) customer with a seamless way to accelerate their deployments.
But before we get into the details, let’s take a look at why such protections have become increasingly important in the past several years.
The Rise of Threats on Connected Devices
Many connected devices, including but not limited to IoT (Internet of Things), IoMT (Internet of Medical Things), and OT (Operational Technology) were primarily intended to communicate with each other or within a closed system. As long as the transmissions remained within the confines of a manufacturing plant, a hospital, or another facility, it was unlikely that an outsider could tap into them and cause harm.
That changed as information transmitted through connected devices evolved to provide core business functions – merging the overall IT infrastructure of an organization with its operational functions. Digital transformation has hastened this shift, potentially affecting countless devices in numerous scenarios that the term “connected devices” has been recently coined and gone mainstream. It’s meant as an umbrella term for the host of connected cyber-physical systems, not just IoT, OT, but industrial control systems (ICS), industrial devices (IIoT), medical devices (IoMT), and facilities devices controlling such things as elevator and HVAC functions and everything in between.
The threats and risks these connected devices introduce are not just theoretical. The healthcare industry is among the most frequently targeted by threat actors and is heavily reliant on connected medical devices. The average hospital has an inventory of more than 3,850 IoMT devices. The attack surface is larger and more complex than most if not all other industries. Poor security and lack of visibility can have life or death consequences as digital risk expands into having a very real physical impact.
Threats have also manifested in the manufacturing sector, which has jumped from an area largely ignored by cybercriminals a few years ago to the number one target for ransomware in 2022 according to IBM Security’s X-Force Threat Intelligence Index 2022. The jump is due largely to the shift to Industry 4.0, a term used to describe the increasing interconnectivity between manufacturing facilities and external information sources.
Attack surfaces have expanded not just for healthcare and manufacturing but for every organization that has embraced digital transformation including financial services, retail, government, education, public sector, and utilities. Whether it be protecting a connected camera, a patient’s infusion pump, a programmable logic controller (PLC) on the manufacturing floor, or host of other critical connected devices, the need for security has never been more important.
The Cisco+Ordr Solution – Establish Trust at Point of Access
The Cisco+Ordr collaboration embraces and enables Zero Trust – a strategic approach to security that centers on the concept of minimizing the attack surface by enforcing trust from an organization’s network architecture. The Zero Trust model of security prompts you to question your assumptions of trust at every access attempt. This comprehensive solution to secure all access across your applications and environment, from any user, device, and location, allowing you to mitigate, detect, and respond to risks across your entire environment.
A Zero-Trust approach:
- Establishes trust in every access request, no matter where it comes from
- Secures access across your applications and network
- Extends trust to support a modern enterprise across the distributed network
The Building Blocks…
Using the Catalyst 9000
To address the requirements of securing connected devices, Ordr has added 2 new Cisco product integrations including its sensor technology on the Cisco Catalyst 9000 Series Switches and advanced data learning from Cisco Meraki Systems Manager to extend end-to-end visibility and security across the entire organization.
The Ordr sensor for the Catalyst 9000 allows organizations to deploy the sensor as a hosted application on the switch to scale data collection across campus environments or extend Ordr to locations where it’s not possible or practical to deploy an Ordr hardware sensor – to secure devices in branch offices, smaller remote locations, and the like.
So equipped, customers know what devices are in their environment, their physical location, the essential details for each device, whether they are behaving normally, and how to secure them. Ordr gains this level of insight by continuously collecting and analyzing data from sensors as well as switches, routers, wireless controllers, firewalls, and other devices in the network. Insights from Ordr’s analysis helps teams maintain an up to date device inventory, meet compliance requirements, and quickly respond to contain active threats. Ordr insights also provide context essential to defining and implementing Zero Trust policy with solutions such as Cisco ISE.
A Cisco Meraki Ecosystem Partner
Ordr now is also a Cisco Meraki Ecosystem Partner, so customers can analyze their Meraki cloud data with Ordr and gain a central, single source of truth to see, know, and secure all their connected devices. For businesses that have switched to remote workforces since the emergence of the pandemic, this is an efficient way to safeguard from potentially dangerous devices used in home offices among other locations outside of typical corporate protections.
Integration with Multiple Solutions
Ordr’s close relationship with Cisco over the years means that it now integrates with multiple solutions. In addition to those previously named, Ordr integrates with Cisco TrustSec, Cisco Secure Networks Analytics (Stealthwatch), and Cisco Prime Infrastructure. Ordr also integrates with Cisco Adaptive Security Appliance (ASA) and Firepower Threat Defense (FTD) firewalls through Cisco ISE.
Ordr integrations across the Cisco portfolio help customers add the end-to-end visibility and security needed to accelerate segmentation and Zero Trust projects with CiscoISE and SDA solutions. Most importantly for organizations that are struggling with connected device security, Ordr’s device classification, network awareness, security intelligence, and auto-generated enforcement rules provide context needed to simplify the process of creating, provisioning, and managing connected device segmentation policies.
Quick Deployment and Improved Security
The Ordr sensor for the Catalyst 9000 is deployed in a matter of minutes as a pre-packaged Docker container on any Catalyst 9000 switch supporting application hosting. Cisco DNA Center can be used to deploy the Ordr sensor on hundreds of Cisco Catalyst 9000 switches with a few clicks, then combined with Ordr SaaS managed service, customers gain insights and improve device security across connected devices in a matter of hours.
See-Know-Secure with Ordr+Cisco
Ordr’s deep integrations across the Cisco portfolio help customers add the end-to-end visibility and context needed to protect connected devices and accelerate the deployment of Cisco ISE and SDA solutions. Ordr’s device classification, network awareness, security intelligence, and ability to auto-generate enforcement rules simplify the process of creating, provisioning, and managing IoT, IoMT, and OT segmentation policy.
Get more information about how Ordr can help strengthen the visibility, security, and overall management of connected devices across all your Cisco deployments.
Pandian Gnanaprakasam
Pandian has more than 20 years of product and engineering leadership experience and is also a serial entrepreneur. Before founding Ordr, he was the Chief Development Officer at Aruba, responsible for all of engineering and product management functions. Aruba, an enterprise mobile wireless company, was acquired by HPE for $3 Billion in March 2015. Before Aruba, Pandian served as the head of engineering for Cisco’s multi-billion-dollar Wi-Fi business unit and before that as VP of engineering for low-end switching product lines. He graduated with a master’s degree in Electrical Engineering from IIT, Chennai, India and holds several patents to his credit in various networking technologies.
Interested in Learning More?
Subscribe today to stay informed and get regular updates from Ordr Cloud
Ready to Get Started?
-
 BlogThe Six Levels of Enterprise Asset Control
BlogThe Six Levels of Enterprise Asset Control…are encrypted to protect against attacks in the network. SSH and other command applications are used to operate and debug and fix things and we can help you keep track…
There are 6 levels of control for managing network security. Device control, vulnerability control, network control, behavior control, external communications control, and application and user control. Knowing them is essential for cybersecurity. The Six Levels of Control
Aristotle, born in 384 BC, had some specific thoughts on how to formulate dramatic stories that have lasted to this day. Screenwriters still rely on its basic framework. In “Poetics”, Aristotle wrote that drama has to include a simple structure where there is always a beginning, a middle, and an end tied together with a unity of theme and purpose. Aristotle’s “Poetics” discusses further how there are six elements for a drama to be cohesive and coherent. There is a plot, character, thought, diction, music, and spectacle. A compelling story, an interesting hero, a theme, the tone, clear music and something memorable to tie it all together, it’s a formula that has stood the test of time.
Similarly, we see security in a proactive and holistic framework with six elements, in this case, six levels of control. It’s a cohesive framework which ties everything together it’s comprehensive and it ties everything together. Our six levels of control include Devices, Vulnerability, Network, Behavior, External Communications, and Application & User Control. Taken by each element alone there is some value but it’s the overall cohesiveness that makes for unity when it comes to proactive protection. Here’s our take on the six elements of control:
Device Control
First off is device control. Before we implement any security measure it helps to know exactly what we have. Hospitals with all the equipment and devices oftentimes might not really have full visibility into all their assets. Some medical systems go through mergers or divestitures and its often difficult to find all the equipment, let alone which infusion pump or MRI machine is being utilized or not.
At Ordr we do device visibility comprehensively, getting all the nitty-gritty details such as the make, model, serial number and modalities of all the assets connected to the network. Once the data is collected, it’s important to know where the devices are actually connected and we can pinpoint the exact location and even the port to where something is plugged in.
Vulnerability Control
Unpatched software and outdated operating systems can leave you vulnerable and we can tell you exactly what device needs upgrading or patching. Sometimes equipment or devices may be hiding somewhere but if it does end up being connected and starts communicating with the network, we will see it and let you know.
The problem with software versions is that there are so many upgrades to keep track of. Lingering old Windows 7 machines can be a problem since its no longer supported and we can tell you exactly which machines you need to keep track of. When we find these Windows 7 devices, we can segment it and keep its traffic within its own zone away from the regular traffic.
Network Control
The boundaries for many hospital networks are now blurred and stationary perimeter firewall protecting us from all attacks is no longer the rule. Malware can be downloaded to many devices often unintentionally by remote or telecommuting workers and damage can occur when someone reconnects to the corporate network.
Malware, once it gets in, is often programmed to perform reconnaissance and to understand devices that are near its proximity so that it can spread. This unusual side to side movement in the network is what you need to stop and contain right away before it does any harm.
Behavior Control
I’m not a psychiatrist but I know abnormal behavior when I see it. Likewise in a hospital, we know what each and every medical device should be doing and how they should act. Whether its sending images and video streams to the video servers at the data center for a camera for example or an MRI machine being accessed by lab technicians at specific times.
If there is any deviation from normal behavior, we can sound the alert. And it’s not just the changes from the daily routine that we can see, our engine can monitor how each device acts in a normal setting relative to its peer group. A thermostat talking to the finance department, that should not happen. Some traffic flow trying to disable security controls or install rootkits? We will shut it down.
External Communications Control
Traffic to certain countries should raise alarms. If someone clicks a URL and there is traffic flow to Iran, Syria, or North Korea, there could be trouble brewing and it’s something you need to know about right away. Even within the U.S., there might be well-intended sites but it can be a trap for ransomware. Now going to a different country, that is fine its just specific suspicious ones that we block proactively.
A fortified firewall is one thing but with so many RDP sessions, many of which are not closed after a remote session, and with no one actively monitoring all these sessions, a corporation can be left unprotected. As a remedy, we work hand in hand with existing firewalls as we make the firewall even smarter by providing the context behind each IP traffic, understanding what the device is and what it is doing when it ventures out to an external website. Policy updates are written automatically to that firewall, providing security managers the added peace of mind.
Application and User control
There are supervisory command applications such as Telnet, FTP, SSH, SNMP, and others. As an example, SSH works by enabling secure system administration and file transfers over insecure networks. Uses encryption to secure the connection between a client and a server. All user authentication, commands, outputs, and file transfers are encrypted to protect against attacks in the network. SSH and other command applications are used to operate and debug and fix things and we can help you keep track of all these sessions.
Understanding applications is one thing but what’s also important is to understand the flow and what is actually happening within the session. If there is a regular port 22 session with a known device that is fine but we proactively ring the alarm if the SSH session is coming from a different or even worse an unknown un-authorized person. Since plain text authentication can be readily stolen and be used to extricate massive amounts of sensitive data, we can alert you right away if there is any use of an insecure protocol and/or any extraction of any data. We can further add controls to only those who are allowed to access the data.
Proactive and Comprehensive Security, Aristotle will be Proud
At Ordr we take a holistic view of security understanding the granular details of control and having a system that learns and adapts. “We are what we repeatedly do. Excellence, then, is not an act, but a habit” said, Aristotle. Devices, Vulnerability, Network, Behavior, External Communications, and Application & User Control it all fits together with the Ordr framework and this is what we do.
Thoughtful details of traffic sessions and flow genome are factored in our engine and we ingest more information every day repeatedly to make our system smarter as we strive for excellence. Take control with Ordr.
Pandian Gnanaprakasam
Pandian has more than 20 years of product and engineering leadership experience and is also a serial entrepreneur. Before founding Ordr, he was the Chief Development Officer at Aruba, responsible for all of engineering and product management functions. Aruba, an enterprise mobile wireless company, was acquired by HPE for $3 Billion in March 2015. Before Aruba, Pandian served as the head of engineering for Cisco’s multi-billion-dollar Wi-Fi business unit and before that as VP of engineering for low-end switching product lines. He graduated with a master’s degree in Electrical Engineering from IIT, Chennai, India and holds several patents to his credit in various networking technologies.
Interested in Learning More?
Subscribe today to stay informed and get regular updates from Ordr Cloud
Ready to Get Started?
-
 BlogCISA Alert (AA20-302A) Ransomware Activity
BlogCISA Alert (AA20-302A) Ransomware Activity…Preparing for and Responding to Ransomware for Users of IoT and IoMT Threat Summary Ransomware has been around for decades and while the recent evolution in the past few years…
Security Bulletin
CISA Alert (AA20-302A) Ransomware Activity
Targeting the Healthcare and Public Health Sector
5Min ReadBy Prasanna Rajendiran

On Oct 28, 2020, the Cybersecurity and Infrastructure Security Agency (CISA) along with the Federal Bureau of Investigations (FBI) and Health and Human Services (HHS) announced an increased and imminent cyberthreat to the Healthcare and Public Health Sector. This warning comes on the heels of increased ransomware incidents in the last few months and includes information on Conti, TrickBot, BazarLoader and new Indicators of Compromise (IOCs). As healthcare continues to grow as a reliable source of income for threat actors because of the necessity to protect patient care, ransomware campaigns will continue to proliferate.
Jeff Horne, Chief Security Officer at Ordr, provides insight into the latest wave of ransomware with a series of articles:- Ransomware in Healthcare Providers and Healthcare Delivery Organizations – Tactics, Techniques, and Procedures and Recommendations of How to Triage
- A Primer on Preparing for and Responding to Ransomware for Users of IoT and IoMT
Threat Summary
Ransomware has been around for decades and while the recent evolution in the past few years has transformed into more of a service – yes, Ransomware-as-a-Service (RaaS), it can be attributed to one of the reasons there is a 25 percent increase in attacks from Q4 2019 to Q1 2020 and a 715% year-over-year increase in detected – and blocked – ransomware attacks and the average payment increased by 33%.
The distributed nature of the ransomware developer and the affiliates makes it more lethal than ever.
Ransomware developer: Who creates custom malicious code, and capabilities like lateral movement tools and scripts, and including exploit code that is sold to a ransomware affiliate for a fee or share in eventual ransom after a successful attack.
Ransomware affiliate: Starts a hosting site with custom exploit code. Identify targets and send the exploit code typically by phishing email or as an attachment.
Victim: Falls victim to the exploit code.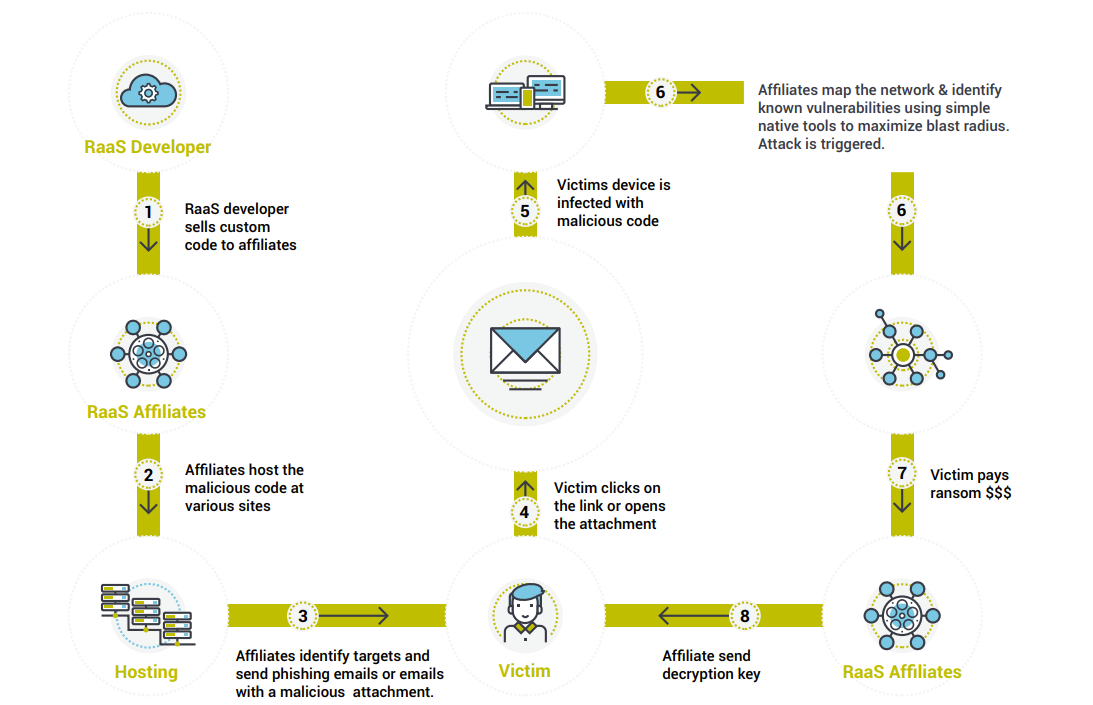
RaaS Infection Lifecycle There are several RaaS types identified by security experts. Some examples are Sodinokibi, Ryuk, Mamba, Phobos, Dharma, Snatch, etc. It is worth noting that in the actual ransomware code is usually the last piece dropped in the infection life cycle giving hope that this can be prevented. The infection usually starts with Trojans like Trickbot, will go through the baking process where the RaaS affiliates monitor and map out the network and any existing vulnerabilities and then drop the actual ransomware code.
Ordr recommendation for defense against RaaS:
There are several recommendations given by security experts. Ordr compiled the Mitigation plans and policies from the CISA advisory and others, mapped it to the NIST cybersecurity framework.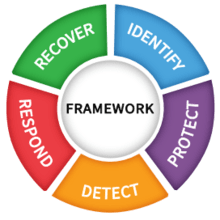
Fig-2: NIST cybersecurity framework Identify
Insightful asset management: Asset management of all the network connected assets is the first step towards defense against any threats. Insightful asset management is not about maintaining a list of IP addresses or serial numbers but a very detailed inventory containing – What the device is, where it is located, Operating System details etc. Ordr passively detects all the network connected devices creates a database with make, model, OS, location and other detailed information.
Continuous monitoring: Continuous monitoring is key for any good asset management and security programs. With the proliferation of IoT devices continuous monitoring is key to the protection of the entire Organization. A device that is not supposed to be in the network need to be detected right away and appropriate action need to be taken. Ordr detects a device the moment it is active in the network and records the same. Ordr can quarantine or disconnect a device from the network with a click of a button.
Knowledge of what is in your control and more importantly what is not: Organizations usually maintain the inventory of the assets that they control. What is largely missed are the assets that are not “owned” by the organization but still uses the critical resources of the organization – third-party managed network, vendor devices, devices and software under vendor qualification etc. Ordr detects all these devices and gives a very easy way to identify these unmanaged devices with ease.
Asset criticality: Knowing and protecting critical assets is a critical part of the security program. For healthcare Ordr provides Clinical risk metrics that helps prioritize and secure the most critical assets.Protect
Security awareness: Awareness is key to any security program. This process should cover topics from identifying malicious emails to social engineering risks. Make sure that Security awareness campaign is an ongoing process.
Understand vulnerability threat posture: Understand the existing vulnerabilities of all the devices and software in the network. Most of the ransomware damage is done using the existing vulnerabilities. One of the vulnerabilities identified as a major exploitation vector is CVE-2020-1472. Ordr identifies devices that are impacted by this vulnerability. Ordr in combination with any popular vulnerability detection software like Tenable or Rapid7 provide a complete picture of IoT specific and application vulnerabilities. With the combination of critical infrastructure score, organization knows how to prioritize the never-ending patching programs.
Bring unmanaged devices under compliance: In almost all deployments Ordr found devices that the security teams never knew existed. These range from someone plugging in some device into the corporate network, contractor/vendor devices to third party managed networks. Ordr can easily identify these devices so that appropriate action can be taken to bring these devices in compliance.
Understand active threat posture: Active threats are different from vulnerabilities. Ordr has an inbuilt IDS engine that can detect East to West threat propagation. Understanding the criticality of the device along with the evidence of vulnerability exploitation is very critical. Typical Firewalls don’t catch East to West threat propagation. Ordr detects and reports the East to West threat propagation that reduces the threat response time.
Monitor active communications: No one wants their device to talk to the bad websites. Ordr detects these activities right away and triggers an alarm.
Backup and encryption: As a standard practice, perform regular backup and encryption.
Be proactive: These new attacks try to understand the network and the connectivity details to cause maximum damage. Microsegmentation is a sure way to protect the network from the ransomware attacks as the threat exposure is minimized. Ordr makes microsegmentation easier and a reality.Detect
Make sure standard security practices are up-to-date: Make sure that all the security measures you have in place like end-point protection software and threat feed information are up-to-date. Provide continuous security education to all the users including vendors and contractors.
Logging: Make sure that you have the logs of all transactions. Ordr records all network transactions over the network. This will help immensely for any forensic activities.
User to device mapping: Its critical to understand who is using what devices and what they are doing with those devices. Ordr helps map user to device mapping and device communication mapping.
Communication patterns: Understanding device to device communication patterns and blocking unnecessary or unexpected communication is another step towards protecting the infrastructure. One of the exploitation vectors for the recent ransomware attacks is the open RDP port 3389. Ordr provides an easy way to identify devices that are communicating over port-3389. User can then decide if this communication is expected or not and if the RDP port itself need to be changed.Respond
Incident response: Develop a plan to respond to an incident. Ordr helps identify the blast radius, understand the impacted applications and users to come up with an effective threat incident response plan.
Recover
Restore: With the backup and encryption mechanisms in place, restore the data.
Verify: Make sure that the suspect hardware software is not used in the future. Ordr continuous monitors the network for the devices and will let the user know about any vulnerable devices coming back into the network.
Report: Report the incident to appropriate authorities as designated by response and discloser policies.
In summary RaaS has no prescriptive solutions. This can be prevented by following the recommendations by Ordr and other authoritative sources. In the battle between good and evil always good triumphs – We just need to know the exploitation vectors, vulnerability posture of the organization and the active threat posture of the organization. We hope our recommendation will help organizations to continue their business and discourage bad actors from doing malicious activities.
For more information on how Ordr can help you identify and manage vulnerabilities for any connected device, please contact info@ordr.net.Prasanna Rajendiran
Prasanna Rajendiran has more than 20 years of experience in various engineering, solutions architect, product management and customer success roles with a focus in telecommunications and security. At Ordr, Prasanna serves as a Principal where he is responsible for working with customers in their complex environments and internally to develop cutting edge solutions.
Interested in Learning More?
Subscribe today to stay informed and get regular updates from Ordr Cloud
Ready to Get Started?
-
 BlogStrategic Risk Prioritization and Vulnerability Management
BlogStrategic Risk Prioritization and Vulnerability Management…mitigating alert fatigue and delivering a prioritized list of top risks. With features like the Vulnerability Dashboard for comprehensive insights, Query Builder for customized dashboards, and Ask OrdrAI for instant…
Blog
Strategic Risk Prioritization and Vulnerability Management
Across the Cyber Attack Surface
< 1Min Read
By Srinivas Loke
Studies show that close to 50% of ransomware attacks result from unpatched vulnerabilities, including weaknesses in an organization’s information systems, system processes, or internal controls. Prioritizing vulnerabilities presents a significant challenge for enterprises as security teams often must sift through thousands of vulnerabilities, each presenting different dangers to the organization based on the associated asset risk. Yet this must be done because unaddressed vulnerabilities increase the likelihood of a breach or cybersecurity incident.
To effectively manage vulnerability risks, enterprises must therefore develop a strategy that prioritizes vulnerabilities based on its specific risk and impact to their business. In general, assets can be categorized into three broad categories:
- Assets with known vulnerabilities that can be patched once a patch is available.
- Assets with known vulnerabilities that may have a recommended patch, but validation by the manufacturer is necessary before patching.
- Assets with an outdated operating system (OS) that typically cannot be patched. (In such cases, security teams must find alternate methods to prevent the exploitation of these vulnerabilities.)
To help organizations simplify and tackle the task of risk prioritization and vulnerability management, Ordr’s Cyber Asset Attack Surface Management (CAASM) product offers enterprises end-to-end vulnerability management, enabling their security teams to identify, investigate, and prioritize vulnerabilities efficiently. Below we will share how Ordr enables enterprise security teams to reduce alert fatigue and get a prioritized list of top risks.
Automatically Discover and Assign Vulnerabilities to All Assets
Ordr uses multiple methods to collect and de-duplicate vulnerability data from multiple sources, offering a streamlined approach to managing vulnerabilities on a single platform. Utilizing the following methods ensures security teams can discover and understand the full vulnerability landscape across all assets, including IT, IoT, IoMT, and OT.
1. For regularly scanned assets, integrations with vulnerability assessment systems, such as Rapid7, Tenable, and Qualys, collect vulnerability data. Ordr then deduplicates this data to ensure teams have an accurate list of vulnerabilities.
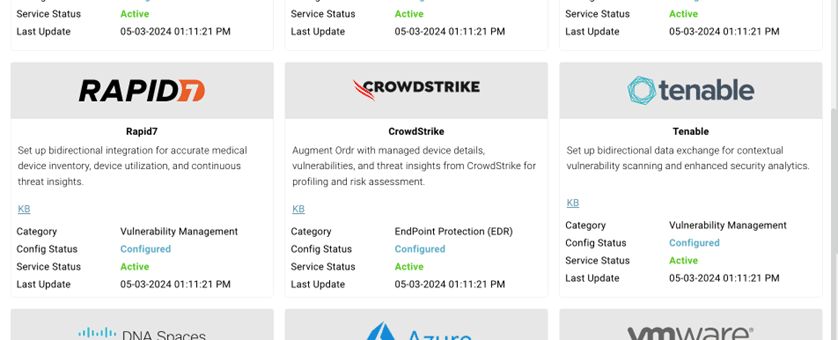
2. For assets that cannot be scanned or are not updated regularly, Ordr’s lightweight script, Software Inventory Collector, detects vulnerabilities based on KB/HF correlation instead of scanning the asset. This approach ensures comprehensive vulnerability coverage is collected for assets that cannot undergo traditional scanning.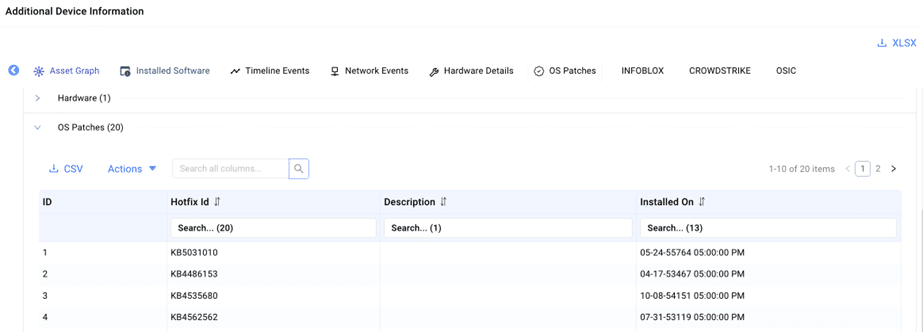
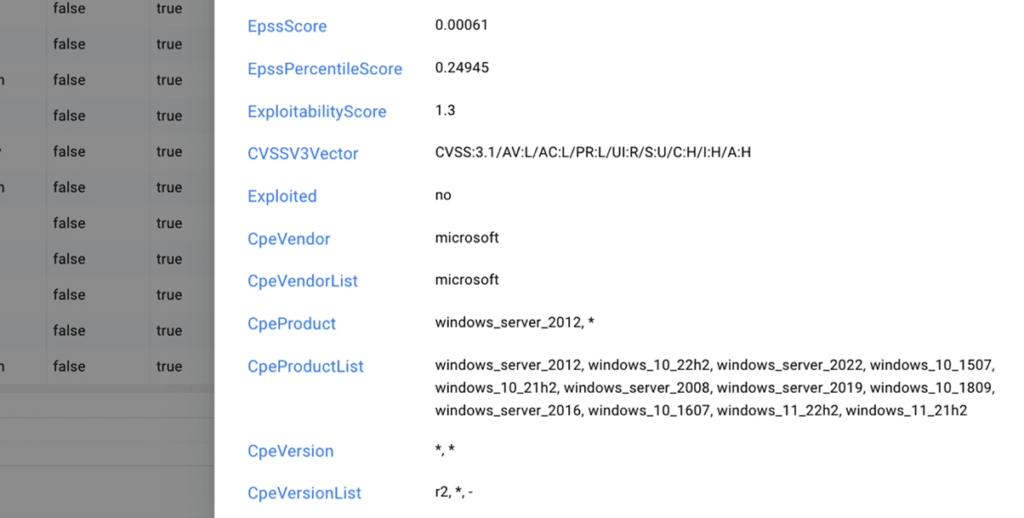
3. For assets with outdated operating systems, Ordr uses both passive and active scanning techniques to collect detailed asset context, including make, model, manufacturer, and OS. This data is then used to accurately assign vulnerabilities to these assets.Enhancing Vulnerability Data & Context for Risk-Based Prioritization
After identifying all assets with vulnerabilities, Ordr enriches the data by providing additional business context for each asset. This empowers security teams to prioritize vulnerabilities based on the criticality of assets to the business, enabling them to focus on addressing the most significant risks. Ordr’s Asset Risk Score considers multiple factors such as asset context, CVSS scores, vulnerability exploitability, type of data (encrypted), location, and more. To obtain detailed asset data and business context, Ordr utilizes:
- AI/ML technology to classify assets and assign business context. Customers can also add additional context to customize the risk score to further align with their specific business needs.
- Known Exploited Vulnerabilities (KEV) and Exploit Prediction Scoring System (EPSS) data to gain additional visibility into vulnerabilities posing the greatest risk.
After gathering asset context utilizing AI/ML technology, the data is standardized into a score, prioritizing assets based on numerical risk. Each asset is assigned a risk-based score ranging from Level 1 to Level 5, with mission-critical assets designated as Level 5.
Streamlining End-to-End Vulnerability Management
Ordr streamlines end-to-end risk and vulnerability management to cover everything from associating vulnerabilities with assets, to assigning remediation tasks to the appropriate asset owner and monitoring vulnerability status. Ordr’s comprehensive approach includes:
- Building integrations with vulnerability management tools, such as the ServiceNow VR module and others, to deliver real-time status updates based on reconciled data.
- Providing the capability to mute a vulnerability, allowing teams to temporarily hide the vulnerability from dashboards while still tracking the vulnerability until a patch is available.
- Enabling teams to assign vulnerability remediation tasks to individual users, complete with priority and due date specifications.
- Providing visualization of trending analysis based on newly discovered, open, and closed vulnerabilities.
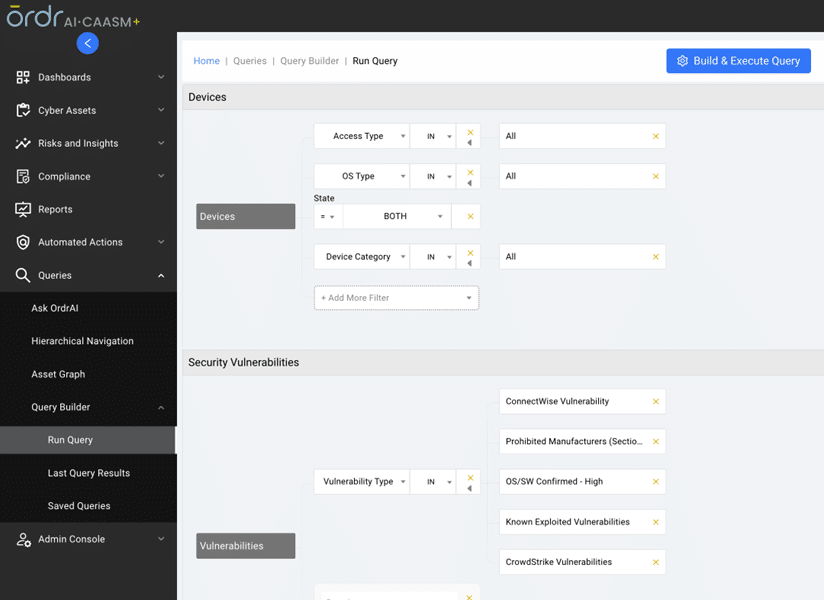
Intuitive Vulnerability Data Search
Ordr’s AI/ML mapping and correlation engine, along with the Software Inventory Collector, align technical and business priorities, mitigating alert fatigue and delivering a prioritized list of top risks. With features like the Vulnerability Dashboard for comprehensive insights, Query Builder for customized dashboards, and Ask OrdrAI for instant vulnerability information, CAASM+ simplifies risk and vulnerability management on a single platform.
Vulnerability Dashboard provides a complete “state of the union” on vulnerabilities.
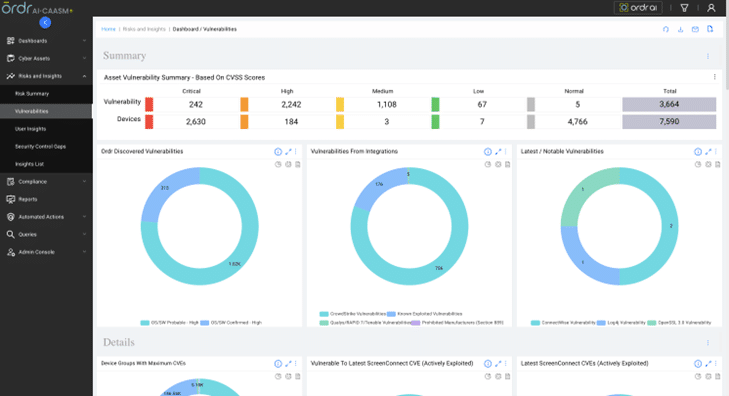
Query Builder for creating a custom dashboard based on the customer’s needs.
Ask OrdrAI gives security teams a natural language search option to get information on vulnerabilities, eliminating the need for technical expertise or coding.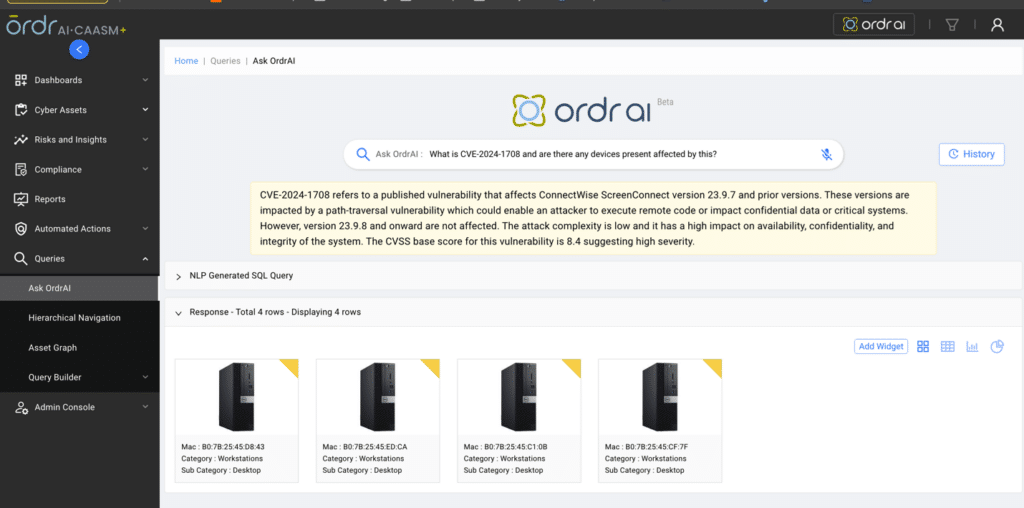
Ordr integrates with industry-leading security solutions to share data and insights when assets have vulnerabilities or remediation is needed. Recommended data sources for Ordr to integrate with for end-to-end vulnerability management include:
- EDR
- MDM
- CMDB
- Cloud Assets
- Vulnerability Assessment Systems
- Ordr Discovery Engine
Ordr provides a framework for remediation with multiple enforcement options. These enforcement actions include:
- Network based enforcement (changed VLAN, shutdown port, integrate with firewall)
- Integrations with ticketing systems
- Integrations with messaging/collaboration tools
- Integration with vulnerability management tools
Watch the video to see how CAASM+ empowers security teams to efficiently identify, investigate, and prioritize vulnerabilities.
https://www.youtube.com/watch?v=7fhFem5YqRcLearn more about Ordr’s risk-based vulnerability prioritization and management and connect with one of our experts for a personalized demo.
Thanks for joining us for another blog in our series on CAASM+ use cases. Stay tuned as we explore more of these critical use cases in the coming weeks and discuss how Ordr addresses them.
Srinivas Loke
Srinivas Loke is Vice President of Product Management at Ordr. Srinivas has a passion for cybersecurity with a deep understanding of network, end point, cloud and IoT security. Prior to Ordr, he led product teams at Aruba, Pulse Secure, FireEye and McAfee. He loves taking 1.0 products to the market and furthering cutting edge technologies that are solving customer problems.
Interested in Learning More?
Subscribe today to stay informed and get regular updates from Ordr Cloud
Ready to Get Started?
-
NewsOrdr Expands Platform, Increases Visibility and Attack Surface Insights
…to understand the risk posture of all managed and unmanaged devices, while maintaining a complete and accurate device inventory. Mobile Device Management (MDM) and Endpoint Detection and Response (EDR) –…
Ordr Expands Platform, Increases Visibility and Attack Surface Insights
4Min ReadSanta Clara, CA – May 2, 2023 – Ordr, the leader in connected device security, today announced the release of new innovations and ecosystem integrations in version 8.2 of its AI-powered platform. Ordr enables customers to SEE, KNOW, and SECURE every connected device across their whole organization – from laptops and traditional IT equipment, to especially vulnerable Internet of Things (IoT), Internet of Medical Things (IoMT), and Operational Technology (OT) devices. This release positions Ordr as the most comprehensive, granular, and accurate source of truth for every connected device.
Using Ordr version 8.2, customers will:
- SEE a greater amount of connected devices and better understand device context through integrations with leading Mobile Device Management (MDM) solutions Jamf and Microsoft Intune, Endpoint Detection and Response (EDR) platform SentinelOne, network management platform Cisco DNA Center; and through enhancements to the Ordr Software Inventory Collector.
- KNOW more about vulnerabilities and risks through integrations with leading EDR and threat intelligence platforms, including CrowdStrike and Qualys.
- SECURE devices more rapidly through enhanced automation capabilities across the Zero Trust ecosystem, including integration advancements with Aruba ClearPass.
“Today’s organizations must manage a tough balance between the demands of rapid digital transformation and the need to protect their businesses,” said Pandian Gnanaprakasam, Chief Product Officer and co-founder of Ordr. “While digital transformation is an opportunity to fundamentally improve enterprise operations, the tradeoff is an expansion of the cyber attack surface and the demands of an increasingly strict regulatory regime. At Ordr, we understand that balance. Our platform helps customers embrace digital transformation without compromising security.”
Ordr 8.2 gives customers a centralized view of the connected device attack surface, including vulnerabilities, risks, and active threats. As an open platform, Ordr takes pride in offering the largest number of security, networking, and IT solution integrations in the industry today, including bidirectional integrations. When combined with the Ordr Data Lake profiles, these integrations further Ordr with the most comprehensive and detailed context, flows, and insights on tens of millions of devices to mitigate risks and accelerate Zero Trust initiatives.
“The Ordr platform gives us invaluable insights that help accelerate our Zero Trust project with Aruba Clearpass,” said Randy Yates, VP, Chief Information Security Officer, Memorial Hermann. “With Ordr, we’re able to easily define granular policies based on device role and risk to ensure we can reduce our attack surface and improve security without fear of impacting operations.”
The new features and integrations announced as a part of Ordr version 8.2 include:
SEE: Gain Granular Visibility of Every Connected Device
Devices used every day by a remote and distributed workforce increase the attack surface and create visibility gaps for security teams, resulting in increased risk for organizations. Security teams need to understand the risk posture of all managed and unmanaged devices, while maintaining a complete and accurate device inventory.
Mobile Device Management (MDM) and Endpoint Detection and Response (EDR) – Ordr delivers device insights and enables a centralized view of every device for a comprehensive view of the attack surface. Ordr has integrated with top MDM and EDR platforms, including Jamf, Microsoft Intune, and SentinelOne, to enhance the view of vulnerabilities and risk with additional managed device details.
Ordr Software Inventory Collector – Ordr Software Inventory Collector gathers essential details from devices to provide deep insights into vulnerabilities and risks, such as unpatched software, unauthorized software, and outdated or disabled antivirus programs. Ordr Software Inventory Collector now fetches additional endpoint attributes for teams, including user login, admin, hardware details, certification, and IP address, while also complementing Software Bill-of-Materials (SBOM) efforts with real-time visibility into the state of software, the date it was installed, and any patches implemented.
Cisco DNA Center – By integrating with Cisco DNA Center, Ordr enhances the view of devices with location context, including building and floor details. This improves incident response when physical access is needed to remove a device from the network (e.g., unplug it) or if physical access is needed for patching.
ServiceNow Service Graph Connector – Ordr eliminates manual asset inventory efforts by automatically and continuously discovering and gathering granular details for every connected device. By integrating with ServiceNow Service Graph Connector, Ordr helps teams ensure that asset inventories are accurate and up-to-date.
KNOW: Strengthen Vulnerability Management and Risk Reduction Efforts
Ordr’s accurate device classification and insights enable teams to scan previously unscanned devices or environments, and optimize scanning to ensure that the operation of critical devices and services are not impacted.
Qualys Cloud Platform – Device scanning gives security teams an essential view into potential vulnerabilities and risks. That said, many devices have restrictions where scanning could affect operations and impact safety. By integrating with Qualys, previously unscanned devices and environments can now be scanned with Ordr insights to inform controls for scanning strength, depth, and timing. Gaps in the attack surface are closed without an impact on operations.
CrowdStrike Spotlight API – Ordr can now easily integrate device vulnerability information from CrowdStrike managed devices using the CrowdStrike Spotlight API. This provides teams with a centralized and enhanced view of device vulnerabilities and risks.
New Threat Detections – Ordr version 8.2 incorporates several features that help customers detect attempts to exploit the latest ransomware and zero-day threats, such as the OpenSSL vulnerability.
SECURE: Accelerate and Scale Proactive Security with Zero Trust
A critical part of implementing segmentation or other Zero Trust policies is that policy enforcement does not “break” critical applications, impacting operations, safety, or customer services. Capabilities in Ordr 8.2 help teams proactively improve security by automating the creation and customization of Zero Trust policies, and optimizing those policies for enforcement at scale on solutions such as Cisco ISE, Aruba ClearPass, and Fortinet FortiNAC.
Aruba ClearPass – Ordr 8.2 enhances integrations with Aruba ClearPass, auto-updating endpoints with current device classification information, security metrics (including an adjusted risk score), alarm categories triggered, and the reason for any block or quarantine action. With these enhancements, Ordr continues to offer HPE-Aruba customers the most comprehensive solution to support and accelerate Aruba ClearPass deployments.
“Ordr’s integrations are a game-changer for our customers, and we’re excited to see them continue to make investments in the ecosystem,” Said Tony Coleman, Executive VP of Sales and Service, Computer Solutions. “By connecting their tools to Ordr, we’ve been able to help customers see a much more complete view of their devices and risk. This not only contributes to their ability to protect their environments, but has also helped to improve efficiencies and drive down cost.”
Connect with us for more information about how Ordr can help security, network, and IT teams SEE, KNOW, and SECURE every connected device across the whole enterprise.
Interested in Learning More?
Subscribe today to stay informed and get regular updates from Ordr Cloud
Ready to Get Started?
-
 NewsOrdr Selected to Deliver Forensic Level Device Insight and Threat Protection
NewsOrdr Selected to Deliver Forensic Level Device Insight and Threat Protection…and compliance and accelerate IT initiatives. Ordr is backed by top investors including Battery Ventures, Wing, and TenEleven Ventures. For more information, visit www.ordr.net and follow Ordr on Twitter and LinkedIn. About University Hospital Southampton…
Ordr Selected to Deliver Forensic Level Device Insight and Threat Protection
For University Hospital Southampton NHS Foundation Trust
3Min ReadLONDON, Jan. 26, 2021 /PRNewswire/ — Ordr, the leader in security for enterprise IoT and connected devices, today announced that it has been named the solution of choice for the University Hospital Southampton NHS Foundation Trust (UHS) in the UK, providing further evidence of its rapid growth within the healthcare market. After analysing the market and reviewing various security solutions, UHS in partnership with reseller SmartGate Group deployed Ordr’s Systems Control Engine (SCE), which discovers and secures every connected device, including Internet of Medical Things (IoMT), Internet of Things (IoT) and Operational Technologies (OT).
Like many hyper-connected NHS organisations with a high number of devices attached to the network, UHS required a solution that protected against potential cyber threats and cyber criminals looking to ransom or steal valuable data, including patient information. Ordr SCE discovers every connected device, profiles device behaviors and risks, and automates response. Ordr not only identifies devices with vulnerabilities, weak ciphers, weak certificates, and active threats, but also those that exhibit malicious or suspicious behaviors.
The Informatics department at UHS faced an issue confronting many organisations – both within and outside of the healthcare community – whereby it is difficult to gain full visibility as to exactly what is connected to their network, the associated risk and how to mitigate the ‘east-to-west’ lateral movement threat from cyber exploitation. This is a common challenge for the NHS as many different departments connect a multitude of devices such as CCTV cameras, door access systems, HVAC systems and a wide range of medical equipment. These devices are business critical but are notoriously susceptible to cyber threats.
“We liked the simplicity of the Ordr solution coupled with its forensic level of insight. It’s very intuitive and quick to install, even on a network of this size, and instantly started to catalogue and risk profile every single device on our network,” said Darran Lebas, Network and IT Security Manager, University Hospital Southampton NHS Foundation Trust. “The way it automatically classifies and then baselines the communications of all our devices is very impressive.”
“By delivering real-time device inventory, monitoring east-to-west communications and providing invaluable utilisation data, Ordr is proving to be a valuable asset to the Trust and is a critical component of our cybersecurity strategy,” added Adrian Byrne, IT Director, University Hospital Southampton NHS Foundation Trust.
“The opportunity to partner with UHS has been fantastic, especially with such a forward-thinking IT team looking to take the Trust forward. It is another example of how our solution addresses the challenges faced by healthcare organisations,” commented Bob Vickers, Head of UK&I, Ordr. “UHS, like so many other hyperconnected organisations, sees our solution as being key in their quest to ensure the ongoing cyber security of their connected devices.”
Ordr continues to experience growth within the healthcare sector. The company was recently named a Leader in the Healthcare IoT Security market, according to a new report “Decision Insights: Healthcare IoT Security” from KLAS Research. Ordr was highlighted for its fast pace of growth, strong technology offering, high customer satisfaction, and the highest market share among selected vendors. Ordr was also named as a Representative Vendor in the Gartner Market Guide for Medical Device Security Solutions.
To view the UHS case study in full, please click this link here.
For more information on how Ordr helps industries such as Healthcare, please visit https://ordr.net/solutions/healthcare/.
For more information about University Hospital Southampton NHS Foundation Trust, please visit www.uhs.nhs.uk.
About Ordr
Ordr makes it easy to secure every connected device, from traditional IT devices to newer and more vulnerable IoT, IoMT, and OT. Ordr Systems Control Engine uses deep packet inspection and advanced machine learning to discover every device, profile its risk and behavior, map all communications and protect it with automated policies. Organizations worldwide trust Ordr to provide real-time asset inventory, address risk and compliance and accelerate IT initiatives. Ordr is backed by top investors including Battery Ventures, Wing, and TenEleven Ventures. For more information, visit www.ordr.net and follow Ordr on Twitter and LinkedIn.About University Hospital Southampton NHS Foundation Trust
University Hospital Southampton NHS Foundation Trust provides services to some 1.9 million people living in Southampton and south Hampshire, plus specialist services such as neurosciences, cardiac services and children’s intensive care to more than 3.7 million people in central southern England and the Channel Islands. They are recognised as one of twelve GDE (Global Digital Exemplar) NHS Trusts – NHS organisations are awarded this status for their IT thought leadership and adoption of effective technology.The Trust is also a major centre for teaching and research in association with the University of Southampton and partners including the Medical Research Council and Wellcome Trust. Follow UHS on Twitter @UHSDigital.
Interested in Learning More?
Subscribe today to stay informed and get regular updates from Ordr Cloud
Ready to Get Started?
-
 BlogCybersecurity Asset Management for Modern Organizations
BlogCybersecurity Asset Management for Modern Organizations…discovery to ensure total visibility and accountability into your entire managed and unmanaged device inventory; Real-time device monitoring and profiling to ensure you know the status of every connected asset,…
Use Case
Cybersecurity Asset Management for Modern Organizations
Ordr Use Case Series
3Min Read
By Danelle Au

IT asset management is the process of inventorying every piece of hardware, software, service, and application asset in the technology estate from acquisition and deployment to retirement. Doing it right can pay major dividends for improving enterprise security. In IT (information technology), asset management is the process of inventorying every asset that makes up the technology estate. Every piece of hardware and software, every service and application in use has to be tracked from the moment it is acquired until it is retired. Asset management is vital to keeping track of things like licenses, software updates, maintenance, depreciation, and other administrative aspects of enterprise technology ownership.
Asset management plays an essential, if unheralded role in cybersecurity. When you have an accurate and real-time accounting of all the assets that make up your IT environment, you can minimize the chances of an adversary finding a weak spot, or of an error that puts your systems and data at risk of a breach. That’s because cybersecurity asset management also involves things like patch management, access control, and assignment of user privileges.
The Challenges of Unmanaged and Hyperconnected Devices
One area that is difficult for traditional approaches to cybersecurity asset management is unmanaged and hyperconnected devices like IoT (internet of things). Many devices that are within the realm of IoT and that are connected to the enterprise are not traditional IT gear. This can range from devices that cannot be actively scanned to devices that slip through the cracks of NAC systems. (network access controller). Traditionally, whether the equipment is added with the knowledge of IT management, or whether it connects outside of the view of IT, it has to be monitored and tracked manually—and that is an impossible task given the number of devices in use today. And the problem is only going to get worse given predictions of increased deployment use. Juniper Research estimates IoT deployments will go from 36 billion devices today, to more than 83 billion by 2024.
When devices are undiscovered and unmanaged, they represent a potential point of entry for threat actors. And because the number of devices deployed in today’s sophisticated enterprises can reach five- and six-figures, organizations can’t afford to overlook them as a part of an IT security and management program. That is why a connected device security platform that foundationally performs cybersecurity asset inventory and management is an essential tool for the modern enterprise.
Three Keys to Success
To be effective at the task of cybersecurity asset management, organizations require a platform that is engineered for massive environments and is able to synthesize a significant amount of device data via machine learning and automation. That is because accurate device classification and behavioral baselining of device behavior inherently is made for machine learning.
The keys to successful cybersecurity asset management are:
- Complete device discovery to ensure total visibility and accountability into your entire managed and unmanaged device inventory;
- Real-time device monitoring and profiling to ensure you know the status of every connected asset, including configuration, communications patterns, and expected, unusual behavior, and more; and,
- Automated policy generation and enforcement to support the protection of devices that are at risk of compromise, or that cannot be managed and secured by legacy or manual processes.
These are baseline capabilities that can close the security gaps that exist in enterprises that are struggling to manage their expanding connected device inventories. Many devices were never meant to be accessible to the public internet, but are now connected to online supply chain networks; many devices were made by companies that no longer exist, and are now unsupported; many devices operate on obsolete software and operating systems and are vulnerable to well-know exploits; many medical devices are prohibited from needed updates because of FDA mandates.
Discover ALL Your Devices with Ordr
Ordr discovers all managed and unmanaged devices connected to your network, monitors and profiles device use and behavior, and assesses security risks in real time, and automatically generates and enforces security and management policies, ensuring complete coverage across your entire inventory.
If you’re struggling with cybersecurity asset management, Ordr can help. For quick visibility and assessment of your connected devices, request a demo with one of our experts.
Danelle Au
Danelle Au has more than 20 years of experience bringing new technologies to market. Prior to Ordr, she was CMO at Blue Hexagon, a deep learning for malware protection company, and CMO at SafeBreach where she helped build the marketing organization and and define the Breach and Attack Simulation category. Previously, she led strategy and marketing at Adallom, a cloud security company acquired by Microsoft. She was also Director, Security Solutions at Palo Alto Networks, driving growth in critical IT initiatives like virtualization, network segmentation and mobility. Danelle was co-founder of a high-speed networking chipset startup, co-author of an IP Communications Book and holds 2 U.S. Patents. She has an MSEE from UC Berkeley
Interested in Learning More?
Subscribe today to stay informed and get regular updates from Ordr Cloud
Ready to Get Started?
-
 BlogOrdr and FIPS Certification
BlogOrdr and FIPS Certification…of Standards and Technology) and their Canadian counterpart CSE (Communications Security Establishment). NIST and CSE both team up to staff the CMVP (Cryptographic Module Validation Program) and CAVP (Cryptographic Algorithm…

Federal Information Processing Standards (FIPS) are a set of standards for ensuring technology products are secure. We explain what FIPS 140-2 is, why FIPS certification is important to us, and the implications for not ensuring a product is secure. Last week, Ordr announced the expansion of our NIST FIPS 140-2 validated product offerings. As one of the only next-generation IoT vendors to support this, this announcement is both a reflection of our commitment to our Federal and public sector customers, as well as a testament to the continued speed of innovation by our engineering team.
There is sometimes confusion about what this certification means, so we thought we would address frequently asked questions about FIPS 140-2 in this blog
What is FIPS 140-2?
For those not familiar with the FIPS 140-2 certification, it is a cooperative effort between NIST (the U.S. National Institute of Standards and Technology) and their Canadian counterpart CSE (Communications Security Establishment). NIST and CSE both team up to staff the CMVP (Cryptographic Module Validation Program) and CAVP (Cryptographic Algorithm Validation Program), which work with independent third party testing labs to certify algorithms used in products.
Why is FIPS certification important?
Encryption is an important part of a security strategy to secure data. However, encryption algorithms can vary widely. Organizations in the private sector can use any encryption algorithm they prefer. The U.S. federal government however established FIPS as a standard for vendors and products. FIPS is a set of standards for encryption with the goal to ensure a minimum strength level for the cryptography is used in all Sensitive But Unclassified (SBU) federal operating environments.
FIPS 140-2 (the 2nd generation standard) is an accreditation program that certifies that any hardware or software cryptographic module used in a product must meet well-defined security standards, and specifically must implement algorithms from an approved list.
Is FIPS certification important only to Federal agencies?
FIPS is mandatory for use in federal agencies. The Federal Information Security Management Act (FISMA) dictates that all government agencies use the FIPS 140-2 validated cryptography models. This requirement extends to U.S. government contractors and third-parties working for the federal government.
In addition, FIPS 140-2 is now popular outside of the federal government. The FIPS 140-3 certification has also been adopted as a standard by state and local governments, and regulated industries such as finance, healthcare, legal and utilities.
How did Ordr achieve our FIPS certification?
The Ordr validation was granted after an independent third-party lab testing of the software used on the Ordr platform. FIPS Certificate numbers 2888 for the Kernel Crypto module and 2962 for the OpenSSL modules were achieved with Ordr’s integration partner Ubuntu/.
Which Ordr products are FIPS 140-2 certified?
Ordr has FIPS certified our hardware platforms with the following hardware & software:
- Ubuntu 16.04 LTS 64-bit running on Supermicro SMX11SPL-F with PAA
- Ubuntu 16.04 LTS 64-bit running on Supermicro SMX11SPL-F without PAA (single-user mode)
- Ubuntu 16.04 LTS 64-bit running on Supermicro Supermicro A1SAi with PAA
- Ubuntu 16.04 LTS 64-bit running on Supermicro Supermicro A1SAi without PAA
- Ubuntu 16.04 LTS 64-bit running on Supermicro SYS-5018R-WR with PAA
- Ubuntu 16.04 LTS 64-bit running on Supermicro SYS-5018R-WR without PAA
Does Ordr need re-certification when there is a new software release?
FIPS 140-2 certification is not tied to any specific release. It is validation of the operating system and the hardware layer. Since our software uses the underlying Kernel and OpenSSL modules, no revalidation is needed based on the software level. In short, all Ordr customers will be able to operate with the most recent version of our product without any certification validation delay.
Russell Rice
Russell Rice is VP Product Strategy at Ordr, and brings over 20 years of experience in the network security industry. Russell has held senior leadership roles in product management, technical marketing, and engineering in startups and established companies spanning Cisco, Skyport Systems, Global Internet, and Dow Jones. At Cisco, Russell was the executive business leader for network access control (NAC), policy, and remote access products. Russell is an accomplished speaker and his teams were responsible for the Cisco SAFE network security guidelines. He graduated from UC Berkeley with a bachelor’s degree in computer science.
Interested in Learning More?
Subscribe today to stay informed and get regular updates from Ordr Cloud
Ready to Get Started?