
Cisco
Ordr’s deep integrations across the Cisco portfolio adds visibility and insights needed to manage and secure the wide range of connected devices in today’s environments.
”Role of Huawei H19-431_V1.0 Exam Questions in Getting the Highest-Paid Job 💆 Search for { H19-431_V1.0 } and download exam materials for free through [ www.pdfvce.com ] 🏸Premium H19-431_V1.0 Files”

…the real composition of the packages and the dependent libraries that was pulled into each package when the software was built and shipped. Sometimes, the manufacturer may have customized and configured…
Security Strategy

By Benjamin Stock

Before medical device manufacturers are able to release a product to market, they are subject to Food and Drug Administration (FDA) reviews to evaluate the safety and effectiveness of these devices. Since 2014, those evaluations have included medical device security guidance, with a subsequent update in 2018. Now, with the explosive growth of connected devices used by hospitals and healthcare providers and a growing number of cyberattacks that have crippled healthcare services, the FDA recently released draft guidelines requiring that devices comprising the Internet of Medical Things (IoMT) meet more stringent cybersecurity standards.
“Cybersecurity in Medical Devices: Quality System Considerations and Content of Premarket Submissions,” is a 45-page document that deals with security design, vulnerability disclosures, Software Bill of Materials (SBOMs), and other documentation requirements that will have to be addressed by medical device manufacturers before their new devices can gain FDA premarket approval.
In general, this is a step in the right direction for the FDA. Security needs to be built into the design of medical devices. At the same time, because medical devices have longer lifecycles than typical IT devices, it also means that it may be a while years before new devices falling under this new guidance are deployed. Because of the risks inherent with existing medical devices, healthcare organizations need to take action to secure legacy devices now.
New medical device applicants are advised to submit “a plan to monitor, identify, and address, as appropriate, in a reasonable time, postmarket cybersecurity vulnerabilities, and exploits.”
They are also asked to “design, develop, and maintain processes and procedures to provide a reasonable assurance that the device and related systems are cybersecure.” This includes making patches available “on a reasonably justified regular cycle,” and for newfound critical vulnerabilities, “as soon as possible out of cycle.”
Finally, manufacturers must provide the FDA with “a Software Bill of Materials,” including any open-source or other software their devices use. This is one of the new changes in the FDA guidance— a complete SBOM requirement instead a Cybersecurity Bill of Materials (CBOM), as outlined in the 2018 guidance.
Note that even with a manufacturer-provided SBOM, when a zero vulnerability like Log4J or OpenSSL is discovered, it is almost impossible to find out the real composition of the packages and the dependent libraries that was pulled into each package when the software was built and shipped. Sometimes, the manufacturer may have customized and configured functionality and those additional details aren’t released.
Therefore, as the FDA determines the format for manufacturer SBOMs, it is important to ensure that these SBOM declarations are detailed enough to include each and every piece of library that is included in the build. With this FDA mandate, if manufacturers release an SBOM that is accurate and complete, along with configuration settings, Ordr (and our vulnerability matching engine) can immediately assess the risk of these vulnerabilities and understand the exposure and exploitability.
The new security requirements came into effect when the $1.7 trillion federal omnibus spending bill (the 2023 Consolidated Appropriations Act) was signed by President Joe Biden on December 29, 2022.
Section 3305 of the spending bill — “Ensuring cybersecurity of medical devices”— is an amendment to the Federal Food, Drug, and Cosmetic Act. It took effect 90 days after the Act became law, and with its new authority, the FDA has given manufacturers six months — until Oct. 1, 2023 — to comply with the new regulations. The new law also requires the FDA to update its medical device cybersecurity guidance at least every two years.
Security of medical devices is a shared responsibility. While the FDA mandate can ensure security for a device before it is released to the market, the day-to-day management and security of devices post FDA approvals is the responsibility of healthcare providers and requires a solution like Ordr. Ordr not only maintains an accurate device inventory and monitors devices for vulnerabilities and threats but also delivers device utilization details to optimize operations.
In addition, medical devices are expensive, and a complete upgrade to new devices that adhere to the new guidelines is not operationally feasible or cost effective. Ordr can ensure existing devices (pre-2022 devices) or devices with outdated operating systems in the network can be secured via Zero Trust segmentation policies to restrict access and communications to only enable access required for their role.
We recommend the following approach to secure every connected device. Download our Maturity Guide for connected device security for more details:
With regard to the new 2022 FDA mandate, Ordr can ingest SBOMs as manufacturers make them available, to enable easy visibility across the entire organization. Ordr Software Inventory Collector can complement manufacturer SBOMs by identifying applications for devices running Windows, iOS, and Linux operating systems.
The Ordr platform is trusted by the world’s leading healthcare delivery organizations. Schedule a demo with our product experts to see how we can secure your connected devices.
Benjamin Stock is the Director of Healthcare Product Management at Ordr. Previously, Ben worked as the Director of Clinical Equipment Systems and Project Support at SSM Health St. Louis, MO. With more than 15 years of experience in healthcare technology management, his wealth of knowledge in the Clinical Engineering space allows him to be a wonderful advocate for Ordr healthcare customers. Ben is also a Certified Biomedical Equipment Technician (CBET).
Subscribe today to stay informed and get regular updates from Ordr Cloud
…issued by the Federal Bureau of Investigation (FBI), Cybersecurity and Infrastructure Security Agency (CISA), Department of Health and Human Services (HHS), and Multi-State Information Sharing and Analysis Center (MS-ISAC) detailing…
Blog

By Pandian Gnanaprakasam
This security bulletin written with support from Ordr security research analyst Gowri Sunder Ravi
Ransomware attacks have become a critical threat to the healthcare industry, impacting patient care, data security, and disrupting operational continuity. The recent attack on UnitedHealth’s Change Healthcare subsidiary in February 2024 brought to light how attractive the healthcare industry and its data are to hackers. The ALPHV/BlackCat group was behind this attack and received a Bitcoin payment worth $22 million to restore affected data. Another notable threat group targeting the healthcare sector is the Black Basta ransomware gang.
Black Basta has targeted over 500 organizations in the past two years, and healthcare industries are no exception. A joint advisory was issued by the Federal Bureau of Investigation (FBI), Cybersecurity and Infrastructure Security Agency (CISA), Department of Health and Human Services (HHS), and Multi-State Information Sharing and Analysis Center (MS-ISAC) detailing the Black Basta threat.
The alert was issued after a ransomware attack hit major healthcare provider Ascension, affecting the critical services and systems of 140 hospitals in 19 states. Black Basta is regarded as a ransomware-as-a-service (RaaS) operator, and the group’s attacks have impacted more than 500 organizations and critical infrastructure operators in North America, Europe, and Australia between April 2022 and May 2024 according to the joint advisory. Black Basta has encrypted and stolen data from 12 of 16 critical infrastructure sectors, including the Healthcare and Public Health (HPH) sector.
Like many other members of the ransomware family, Black Basta exploits known vulnerabilities or uses phishing methods to gain initial access. Moreover, the advisory revealed that since February 2024 the group has exploited critical vulnerabilities in the ConnectWise ScreenConnect remote desktop software management application. Similarly, researchers from Trend Micro have linked Black Basta in exploiting CVE-2024-1709, a critical vulnerability with a CVSS score of 10.
All organizations and cybersecurity professionals should implement effective cybersecurity measures that align with the Cross-Sector Cybersecurity Performance Goals (CPGs) developed by CISA and NIST. The mitigation tips include the following:
CISA and NIST also recommend continuous testing of the security program to ensure its optimal performance against the MITRE ATT&CK techniques.
Black Basta is a notorious ransomware variant and Ransomware-as-a-Service (RaaS) operator that first appeared in early 2022. According to Malwarebytes, the group was linked with 28 of the 373 confirmed ransomware attacks carried out in April 2024. BlackBasta is believed to have a close affiliation with the Conti ransomware group because of the similarities in their approach to creating malware, leak sites, and communication for payment negotiation and data recovery.
Black Basta has targeted organizations across the globe, including a recent attack on the Toronto Public Library, Canada’s largest public library system, disrupting library services, including access to digital resources, patron information, and other essential functions.

(Image source: hhs.gov)
The group’s primary targets are the English-speaking “Five Eyes” countries of Australia, Canada, New Zealand, United Kingdom, and United States, suggesting a possible political agenda in addition to seeking financial gain. Black Basta use a variety of tools and remote access methods to execute their attacks and exfiltrate data, including Qakbot, SystemBC, Mimikatz, CobaltStrike, and Rclone.
The group employs the double extortion tactic, encrypting the victims’ data, and threatening to publish it online if their demands aren’t met. In early campaigns, Black Basta used email or spear phishing methods to get initial access to a target organization and deploy ransomware on their devices. The gang has also used other techniques to deploy ransomware, like disabling the compromised system DNS to complicate the recovery process and deploying ransomware that targets Linux-based VMware ESXi Virtual Machines (VMs). They have a public leak website where they publish data about their victims and samples of stolen data to create pressure to pay ransom.
Despite its success and widespread impact, Black Basta maintains a low profile, operating similarly to private threat groups like Conti, TA505, and Evil Corp. The group’s modus operandi is to conduct a careful assessment of an intended target before conducting a focused attack. This sets them apart from threat actors that conduct broader, less selective campaigns.
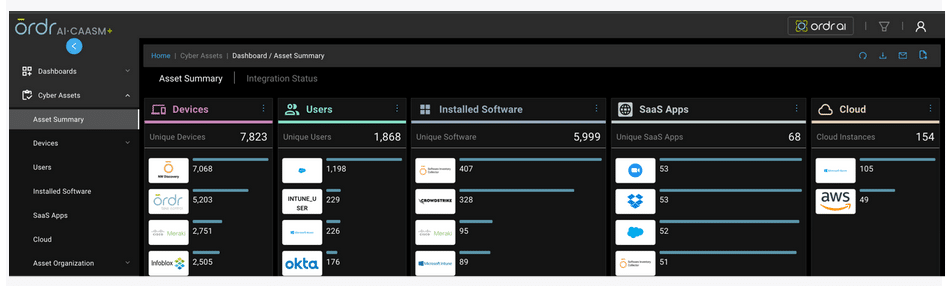
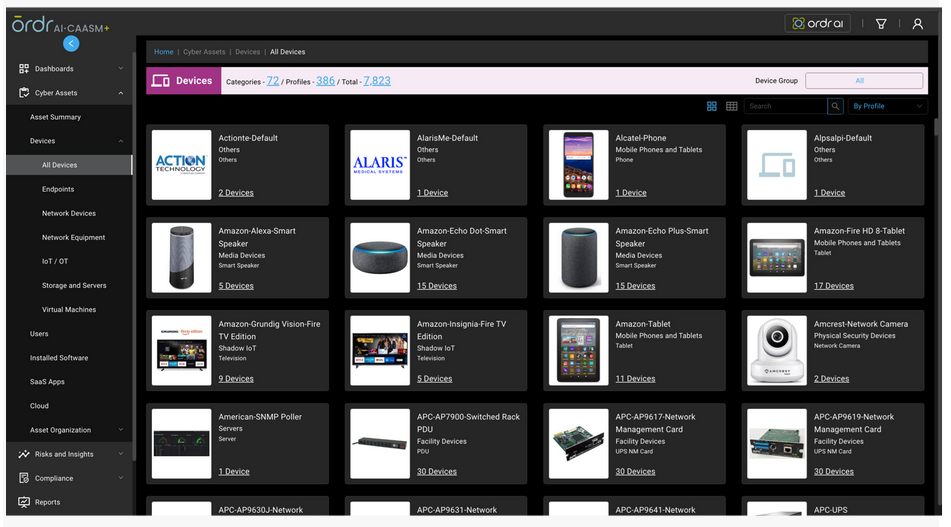
Organizations are increasingly exposed to cyber threats like ransomware attacks without even knowing about them, mainly because the enterprise attack surface continues to expand making it challenging for security teams to correlate asset data across multiple sources to identify security gaps, prioritize vulnerabilities, and remediate threats. Fortunately, OrdrAI Protect and the recently launched OrdrAI CAASM+ solutions provide comprehensive and accurate deduplicated asset visibility, thus preventing exposures.
OrdrAI automatically discovers, classifies, and profiles all devices based on the manufacturer, make, and model, while providing a granular view of data flows and asset attributes associated with all the devices in your environment.
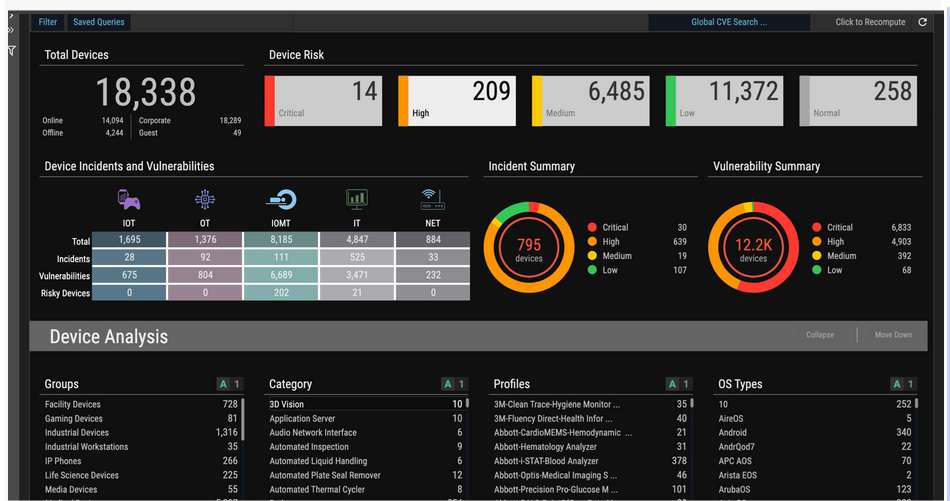

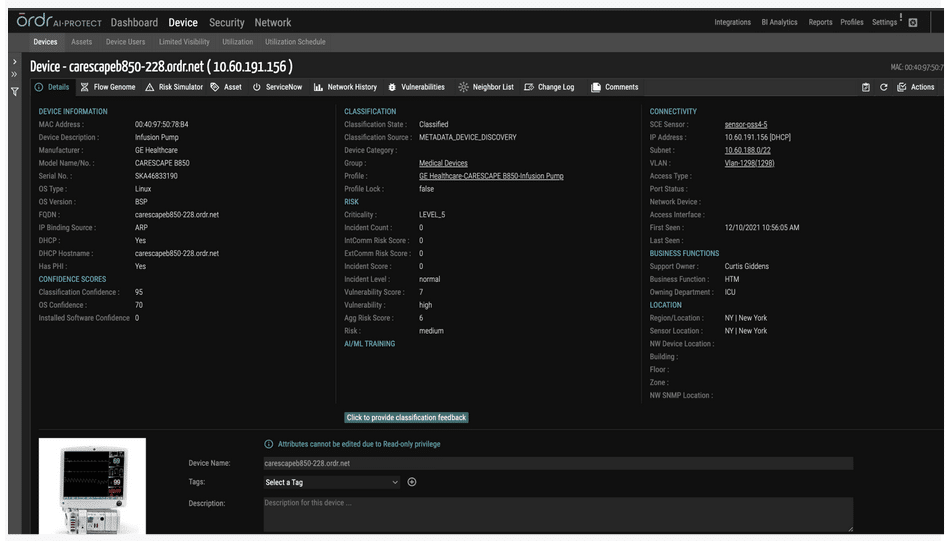
OrdrAI correlates and deduplicates all asset data (Including users, installed applications, IoT and IoMT, OT, cloud services, and more) across multiple sources, then classifies and profiles all devices based on the manufacturer, make, model, and other information pulled from integration sources.

OrdrAI ‘s external IP/IOC detects and tracks asset communication to prohibited IP/URLs in real-time:
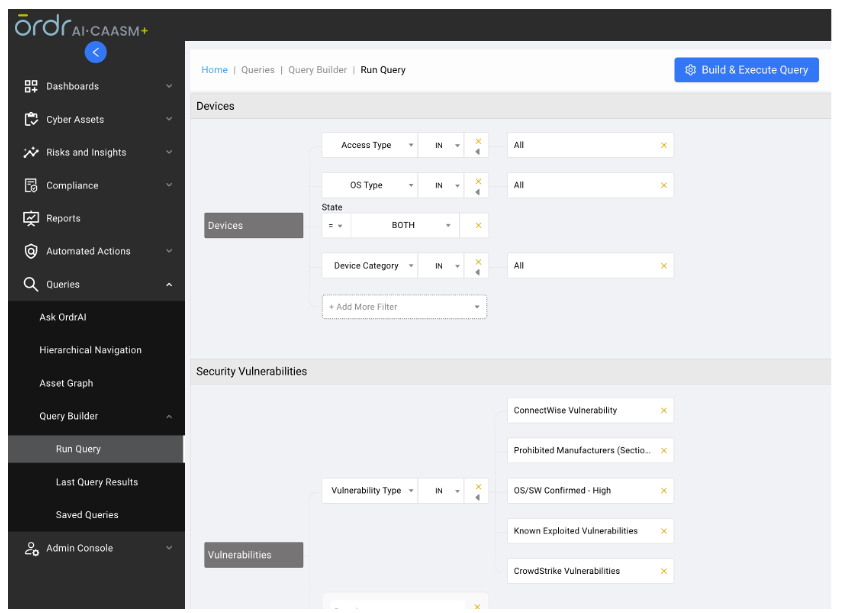
OrdrAI uses multiple methods to collect and deduplicate the vulnerability data from multiple sources and provide an easy way to manage the vulnerabilities.
Based on vulnerability info collected by these methods, OrdrAI customers can get an accurate assessment of risks in their environment, including:

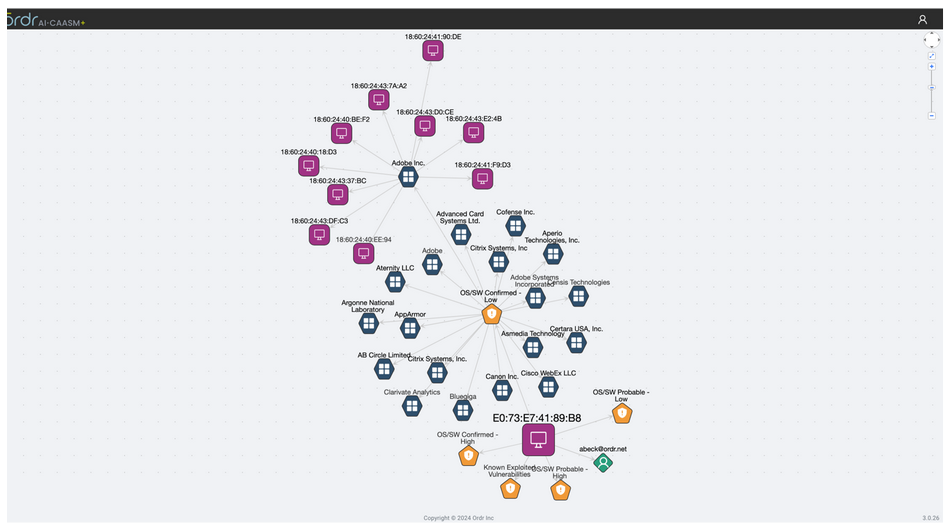
Customers can also get a detailed view of the blast radius via the “Asset Graph” feature, identifying devices, users, and applications associated with a vulnerable asset.
OrdrAI allows easy management of vulnerabilities, including assignments and status of the vulnerabilities, thanks to deep integration with vulnerability management tools like ServiceNow VR module, providing real-time status updates based on reconciled data. That delivers vital capabilities, including:
OrdrAI supports a variety of additional actions like
Are you ready to learn more about Ordr products and how they can reduce the likelihood of ransomware attacks? Schedule a demo now!
Helpful links:
Pandian has more than 20 years of product and engineering leadership experience and is also a serial entrepreneur. Before founding Ordr, he was the Chief Development Officer at Aruba, responsible for all of engineering and product management functions. Aruba, an enterprise mobile wireless company, was acquired by HPE for $3 Billion in March 2015. Before Aruba, Pandian served as the head of engineering for Cisco’s multi-billion-dollar Wi-Fi business unit and before that as VP of engineering for low-end switching product lines. He graduated with a master’s degree in Electrical Engineering from IIT, Chennai, India and holds several patents to his credit in various networking technologies.
Subscribe today to stay informed and get regular updates from Ordr Cloud
…horses, worms, and other forms of malware, and (ii) to monitor and record each and every instance of access to the Ordr’s assets and information systems and to Customer Data…
Last Updated: May 26th, 2022
Ordr shall implement data security measures that are consistent with industry best practices and
standards such that Ordr:
2.1 Environment:
Ordr shall provide assurance that it sets the foundation for the necessary tone, discipline, and structure to influence the control consciousness of its people necessary, and for the services provided to Customer, and/or
Customer’s customers.
2.2 Responsibility:
Ordr shall assign responsibility for information security management to appropriate skilled and senior personnel.
2.3 Qualification of Employees:
Ordr shall implement and maintain appropriate security measures and procedures, including background checks following industry best practices, to restrict access to information systems used in connection with this Agreement or to Customer information to only those personnel who are reliable, have sufficient technical expertise for the role assigned, and have personal integrity.
2.4 Obligations of Employees:
Ordr shall implement and maintain appropriate security measures and procedures in order to verify that any personnel accessing the Customer Information or information systems used in connection with this Agreement knows his or her obligations and the consequences of any security breach, and have read and agree to comply with all applicable Customer Information Security Policies and Standards.
2.5 Segregation of Duties:
Ordr shall provide reasonable assurance the organization of personnel provides adequate segregation of duties between incompatible functions.
3.1 Physical Security and Access Control
Ordr shall ensure that all systems hosting Customer Data and/or providing services on behalf of Customer are maintained consistent with industry best practices and standards in a physically secure environment that prevents unauthorized access, with access restrictions at physical locations containing Customer Data, such as buildings, computer facilities, and records storage facilities, designed and implemented to permit access only to authorized individuals and to detect any unauthorized access that may occur, including without limitation 24 x 7 security personnel at all relevant locations (“Customer Secure Area”).
3.2 Physical Security for Media
Ordr shall implement and maintain appropriate security measures and procedures consistent with industry best practices and standards to prevent the unauthorized viewing, copying, alteration or removal of any media containing Customer Data, wherever located.
3.3 Media Destruction
Ordr shall implement and maintain appropriate security measures and procedures consistent with industry best practices and standards to destroy removable media and any mobile device (such as discs, USB drives, DVDs, back-up tapes, laptops and PDAs) containing Customer Data where such media or mobile device is no longer used, or alternatively to render Customer Data on such removable media or mobile device unintelligible and not capable of reconstruction by any technical means before re-use of such removable media is allowed.
4.1 Access Controls
Ordr shall implement and maintain appropriate security measures and procedures consistent with industry best practices and standards to ensure the logical separation such that access to all systems hosting Customer Data and/or being used to provide services to Customer shall: be protected through the use of access control systems that uniquely identify each individual requiring access, grant access only to authorized individuals and based on the principle of least privileges, prevent unauthorized persons from gaining access to Customer Data, appropriately limit and control the scope of access granted to any authorized person, and log all relevant access events. These security measures and procedures shall include, but shall not be limited to:
4.2 Access Rights Policies
Ordr shall implement appropriate policies and procedures regarding the granting of access rights to Customer Data in Ordr’s possession or control, in order to ensure that only the personnel expressly authorized pursuant to the terms of the Agreement or by Customer in writing may create, modify or cancel the rights of access of the personnel. Ordr shall maintain an accurate and up to date list of all personnel who have access to the Customer Data and shall have the facility to promptly disable access by any individual personnel. For purposes of this Schedule, the term “personnel” as to Customer or Ordr shall mean such Party’s employees, consultants, subcontractor or other agents.
Ordr shall use appropriate security measures and procedures (i) to ensure that Customer Data in Ordr’s possession and control, and /or systems being used to provide Services, is protected against the risk of intrusion and the effects of viruses, Trojan horses, worms, and other forms of malware, and (ii) to monitor and record each and every instance of access to the Ordr’s assets and information systems and to Customer Data to detect the same, and to promptly respond to the same. If any malicious code is found to have been introduced by Ordr or any third party into any of Ordr’s information systems handling or holding Customer Data, Ordr shall take appropriate measures to prevent any unauthorized access or disclosure of any Customer Data and in any case (wherever such code originated), Ordr shall, at no additional charge to Customer, remove such malicious code and eliminate the effects of the malicious code. If such malicious code causes a loss of operational efficiency or loss of data, Ordr shall monitor such losses and restore such lost data in accordance with the terms of the Agreement. Unless, and to the extent, prohibited by law enforcement authorities, Ordr shall immediately notify Customer’s Chief Information Security Officer if it knows or reasonably suspects that there has been an actual instances of unauthorized access to the Customer Data and/or systems holding or handling Customer Data and shall cooperate fully in assisting Customer as necessary to enable Customer to comply with its statutory and other legal breach notice requirements, if any.
Ordr shall implement and maintain appropriate incident response measures and procedures for systems that handle or hold Customer Data, including, but not limited to:
6.1 Operational problems and security incidents are detected, reported, logged, and resolved in a timely manner.
6.2 Processing is appropriately authorized, scheduled, and that deviations from scheduled processing are detected, reported, logged, and resolved in a timely manner.
6.3 System availability, performance and capacity are routinely monitored to help ensure potential issues are detected, reported, logged, and resolved in a timely manner.
6.4 Networks are routinely monitored for availability and response times to help ensure potential issues are detected, reported, logged, and resolved in a timely manner.
7.1 Customer Data
Customer Data must only be used by Ordr for the purposes specified in this Agreement.
7.2 Customer Production Data
Where access is given to Customer Data on any Customer production system, unless otherwise agreed to in writing by Customer, Ordr must not and shall procure that its personnel and sub-contractors shall not copy, download or store such Customer Data on any desktop, server or other device at any Location, in Ordr’s or its personnel’s possession or otherwise.
7.3 Data Integrity Controls
Implementing and maintaining appropriate security measures and procedures to protect the integrity of the Customer Data in Ordr’s possession or control, to prevent the unauthorized recording, alteration or erasure of such Customer Data, and to ensure that it is subsequently possible to determine when, by whom and which Customer Data were recorded, altered or erased.
7.4 Data Destruction
Implementing and maintaining appropriate security measures and procedures to destroy Customer Data in Ordr’s possession or control when appropriate and in accordance with the Agreement. At the request of Customer at any time, Ordr will: (i) promptly return to Customer, in the format and on the media reasonably requested by Customer, all or any part of Customer Data; and (ii) erase or destroy all or any part of Customer Data in Ordr’s possession, in each case to the extent so requested by Customer.
7.5 Software Patching
Implementing and maintaining appropriate security measures and procedures in order to ensure the regular update and patching of all computer software on systems that handle or hold Customer Data to eliminate vulnerabilities and remove flaws that could otherwise facilitate security breaches. Patching schedule and regular verification access and/or reporting shall be mutually agreed upon by Customer and Ordr.
7.6 Virus Management
Ordr shall implement and maintain appropriate security measures and procedures designed to provide antivirus and spyware software protection to Ordr’s systems that handle or hold Customer Data, using the most recently distributed version of software.
…necessary credentials for the attackers to successfully move through the infected systems without hindrance. Execution Once the attackers have the credentials, they recon the network and systems to determine whether…
Ransomware is unlikely to go away any time soon, and the Ryuk ransomware family is a particularly nasty version of this tech. Ryuk ransomware has been around since 2018, and it continues to be a viable threat due to its evolving nature—particularly attacking large organizations in a variety of industries. If attackers think your organization could be vulnerable and/or an easy payday, you may find yourself under attack.
Understanding Ryuk ransomware is the best way to determine the necessary tools to protect yourself against it, and will help you formulate the policies and procedures vital to defend your organization. Furthermore, the more you know, the better educated you’ll be at choosing the best security solution for your organization.
Ryuk is a ransomware family that targets large companies, typically with Microsoft Windows operating system, and encrypts data to hold it hostage until a ransom is paid. In more technical terms, Ryuk ransomware is a human-operated ransomware family that uses AES-256–based file encryption to encrypt all files on the targeted systems, except for those with the .dll, .lnk, .hrmlog, .ini, and .exe extension, appending the .ryk extension to the newly encrypted files. Ryuk is considered to be a unique ransomware family because of continued human involvement throughout the attack, specifically, the group behind this ransomware uses manual hacking technique and open-source tools to move laterally through the network
Most ransomware attacks use a “spray and pray” approach, in which they hit multiple targets at once and hope for infiltration. Ryuk uses targeted attacks; it is an advanced persistent threat (APT) with human threat actors active in the network for an extended period of time. The network is infiltrated, with a prolonged period of data collection and network activity.
Ryuk continues to evolve. While still advanced with human involvement, that human interaction is no longer required for lateral movement. The newest strains of Ryuk are capable of auto-propagation through systems, once loaded into the network, using worm-like techniques. Because Ryuak doesn’t check to see if a system is already infected, it continues to re-infect systems, which makes the ransomware family that much more dangerous.
Ryuk has been used to target organizations in several different industries, including hospitals, governmental institutions, and news outlets. It’s used to “big game hunt”—an organization is specifically chosen before the attack. The victims are typically larger organizations with multiple or high-value critical assets because of the increased chances of the ransom being paid.
Part of what makes Ryuk so dangerous is it’s absolutely benign-looking delivery system: a common Microsoft Word document. The document is attached to a basic phishing email, often sent from a spoofed legitimate source. But, the document has a Emotet trojan downloader hidden in the macros, and it cleverly tricks a user into enabling macros in order to view the document. This then lets Ryuk launch the attack against the system.
Once the Emotet trojan is let loose, it downloads additional malware to install Trickbot onto the system. Trickbot is spyware that can collect the necessary credentials for the attackers to successfully move through the infected systems without hindrance.
Once the attackers have the credentials, they recon the network and systems to determine whether or not the organization is worth attacking. During this espionage, the threat actors do extensive mapping of the systems and identify which critical assets to target during the attack.
As part of this initial phase, Trickbot modules allow the malware to gain Remote Desktop Protocol (RDP) credentials via brute-force attack and create service user accounts on authentication servers on the network. This results in a faster and less detectable final deployment of the encryption. Once recon and set up is finished, the Ryuk encryption is deployed on the critical asset targets.
Many security solutions use registered signatures to scan for known threats. Ryuk ransomware is stealthy—it creates mutations of the original variant so it registers as a previously unseen threat. By mutating to a new variant, it doesn’t flag as a known threat. This constant evolution is a key reason for a more robust security solution—there are more factors than just looking for known security flags.
The attack targets are always what the organization would consider critical assets. However, what each organization considered critical assets isn’t the same across the board—depending on the industry, this could be protected customer data, patient charts, student transcripts, or an OT network. Ryuk’s goal is to target what would best cripple your organization because that increases the chances of you paying the ransom.
Ryuk encrypts the system in such a way that the organization can determine exactly what’s been encrypted, yet leave you still capable of digitally paying the ransom. Ryuk has been known to partially encrypt some files, which prevents decrypting the files with anything other than the designated key. This puts your decryption attempts at a high risk of causing file corruption.
Detecting ransomware like Ryuk requires a robust security solution like Ordr. Ordr integrates with Active Directory to tie devices with users, and ensure all access is valid, which can be used to detect any Ryuk-created service accounts as they appear on the network. Ordr also monitors for exploits, attacker tools and reconnaissance network scans with an integrated threat detection engine, and uses known behavioral baselines to detect unusual or suspicious traffic, which could flag Ryuk’s internal lateral movement before encryption deployment. The behavioral baseline capabilities can also track RDP activity, and if any suspicious activity is detected, Ordr can immediately obtain a list of infected assets and track down infection roots.
Furthermore, Ordr can proactively reduce the attack surface in ransomware attacks by using its discovery process to profile what devices connect to your organization’s network. High-risk devices can then be properly segmented. Ordr also offers retrospective security to look back at anomalous communications by devices in the network to newly discovered indicators of compromise.
Preventing a Ryuk ransomware attack can be accomplished by having a strong security solution that is foundational sound, tested often, and is continuously improved using an iterative approach. Your organization should also have a plan in place for handling an attack in progress once it has already infiltrated and been detected.
Fully define your organization’s attack profile. Understand what could make you a target by discovering and classifying every asset in your network, identifying the risks they bring, and determining which are critical assets to protect. Ensure the proper protections are in place for those assets. Keep patches updated and use enhanced security practices like multifactor authentication and microsegmenation.
Develop policies and procedures that embrace security methodologies and ensure that all teams are aware of how to best protect the network. People are a big factor in the cybersecurity picture, and everyone needs to understand and fulfill their part in order for the organization to have robust security. Defining risk management and accounting for any federal, state, or industry compliance standards is an absolute must.
As technology develops and new threats enter the threat landscape, it’s critical that security evolves over time to remain effective. Mitigate risk where possible, and document and patch vulnerabilities as they’re encountered. Ensure that you have a security solution that can detect known threats as well as behavioral anomalies that may provide early indicators of an attack in progress. Inspect external traffic communications to the Internet as well as East West traffic to detect lateral movement.
Keep improving over time. Operational readiness is key to handling any cyberattack, and it should include the input of not only security, but also key decision makers, as they provide a unique perspective in regards to risk.
Zero Trust is a very effective security methodology that’s best suited to the newly evolved threat landscape. It relies on the principle of least privilege and helps keep user access at safe levels, and it embraces microsegmentation, which can be a critical facet when trying to shut down an attack in progress. Additionally, Zero Trust prevents standard users from installing applications—that’s an important hurdle to place in front of a Ryuk ransomware attack.
The increase of complexity in the threat landscape will only grow, and it is up to your organization to put a solution in place that can expand to meet the needs that will come from threat expansion. The insidious malware family of Ryuk ransomware is an advanced, persistent threat that can seem overwhelming, especially since you deal with mutated, worn-like propagation capabilities and a human-operated attacker. The human element in the Ryuk ransomware makes it extremely formidable, as does its combining with Emotet and Trickbot to infiltrate and take over the network. But you can detect and halt a Ryuk ransomware attack with the right advanced solution.
Using an advanced security solution like Ordr gives your organization the necessary arsenal, such as microsegmentation, Zero Trust, internal lateral movement tracking, and much more.
Ordr gives you full visibility into all the devices connected to your network, helps you understand their purpose and operation, and automates management and security policies to ensure maximal protection. Should you fall under attack, Ordr can help you rapidly isolate and protect infected devices.
Subscribe today to stay informed and get regular updates from Ordr Cloud
…with Fortigate and FortiNAC solutions. Read More Fortinet Fortinet and Ordr have partnered to deliver an industry-leading IoT and unmanaged device security solution by integrating FortiManager, FortiGate and FortiNAC with…
See, know and secure every managed and unmanaged asset, from IT, IoT, IoMT, OT, to users, applications, SaaS and cloud, in any environment.
The OrdrAI Asset Intelligence Platform has been designed to be modular, and enable a building block approach to address your cybersecurity maturity – from asset visiblity all the way to Zero Trust.

Gain visibility for your entire asset attack surface. Prioritize vulnerabilities, identify gaps and reduce your exposure.
MINIMIZE YOUR ATTACK SURFACEAdvanced threat detection, behavioral intelligence and segmentation for mission-critical IT, IOT, OT, IOMT assets.
UNLOCK ASSET THREAT PROTECTIONAddress your entire asset management journey
EXPLORE WHY ORDR FOR TOTAL ASSET SECURITYAsset Visibility and Management
Security Issues and Coverage Gaps
Vulnerability Prioritization and Management
Threat And Anomaly Detection
Segmentation and NAC Acceleration
Regulatory Frameworks
Enrich CMDB and security operations with real-time, automated hardware and software inventory, granular asset details, connectivity, device flows and more.
AUTOMATE VISIBILITY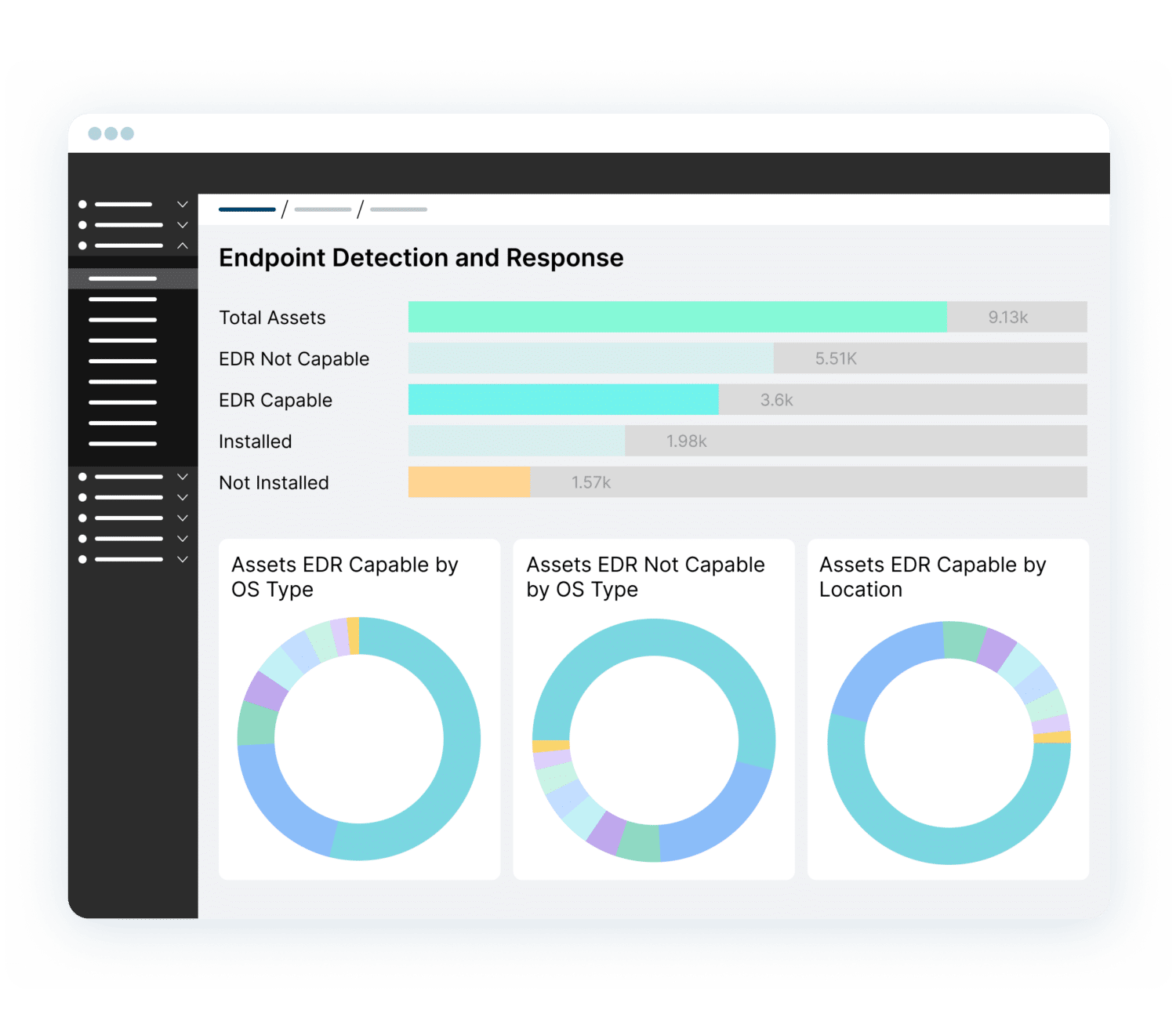
Improve your security hygiene by surfacing security gaps such as devices with outdated OS, or missing EDR/MDM agents.
PINPOINT SECURITY GAPSReduce risks by prioritizing vulnerabilities based on organizational impact. Automate remediation, assign to the right owner and track progress.
MINIMIZE SECURITY RISKS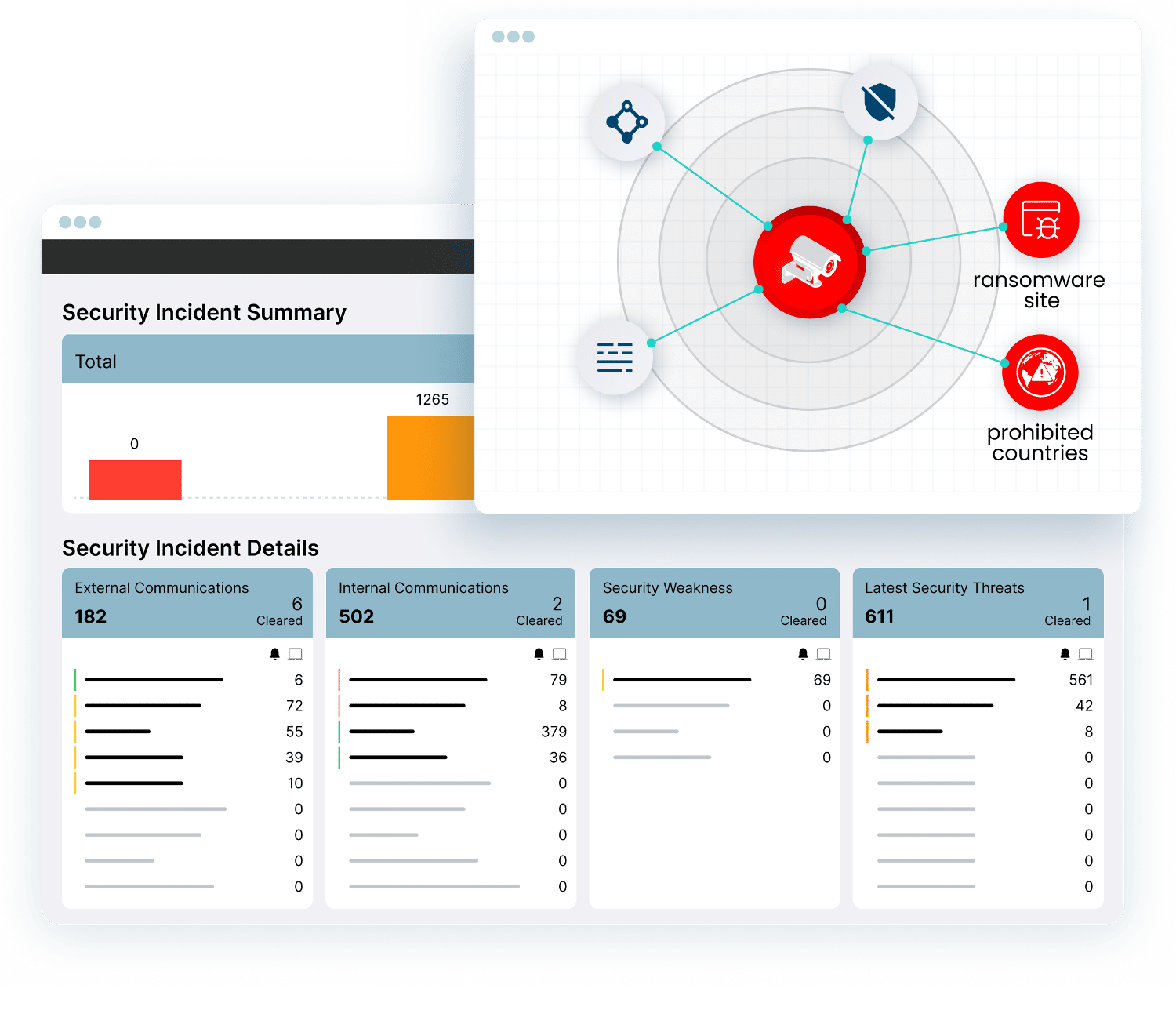
Reduce dwell time. Detect and quarantine devices with exploits, risky communications, anomalous behavior.
ACCELERATE RESPONSE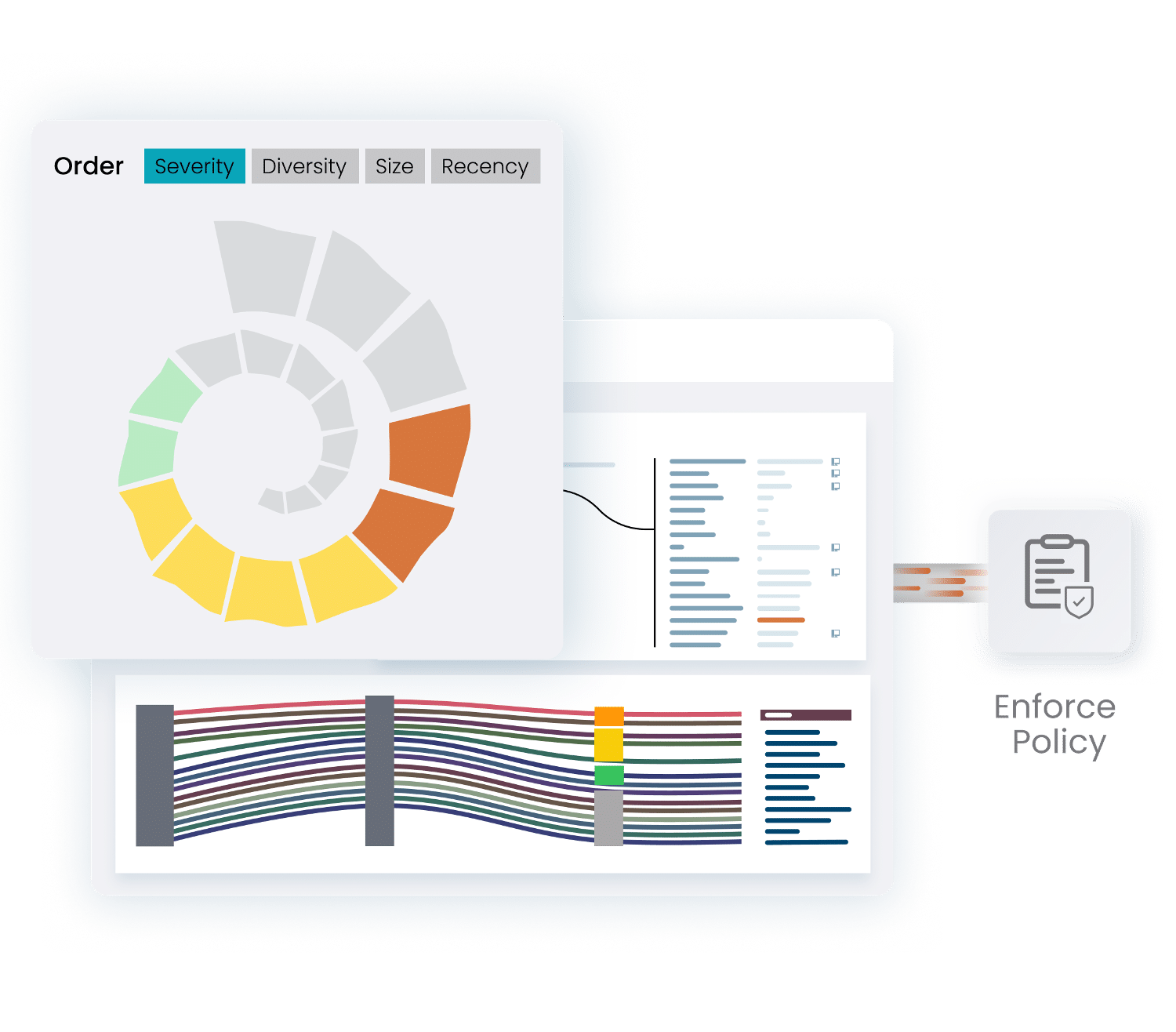
Accelerate NAC projects with asset context and automated policies. Implement Zero Trust segmentation for mission-critical devices.
ENHANCE SEGMENTATION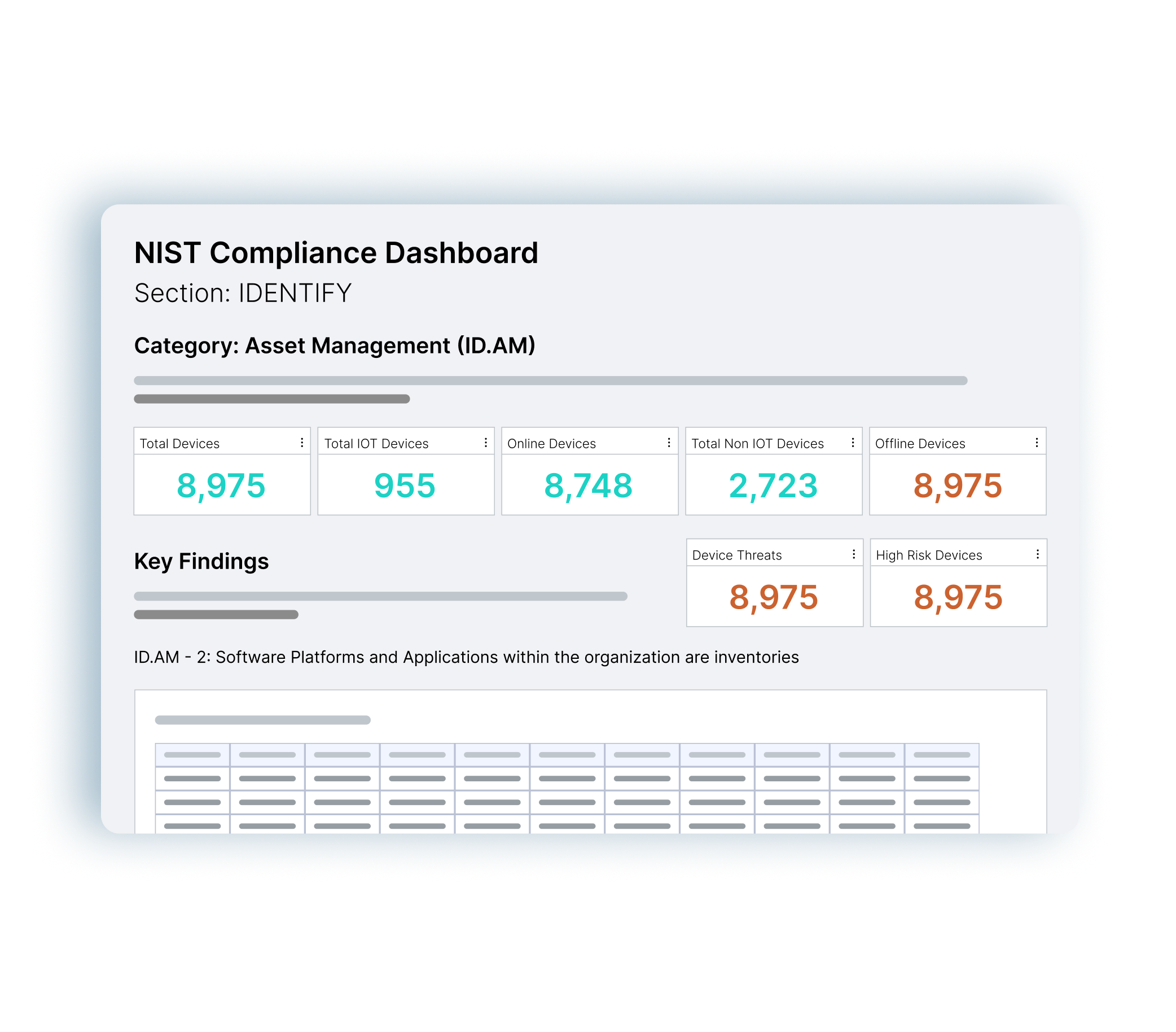
Simplify NIST, CIS Controls, CMMC, Cyber Essentials and NHS DSP Toolkit audits with asset data and reporting at your fingertips.
ENSURE COMPLIANCESeamlessly connect to hundreds of networking and security tools via API. Enrich your security tools with Ordr asset data, and automate response and segmentation policies on firewalls, switches, NAC.
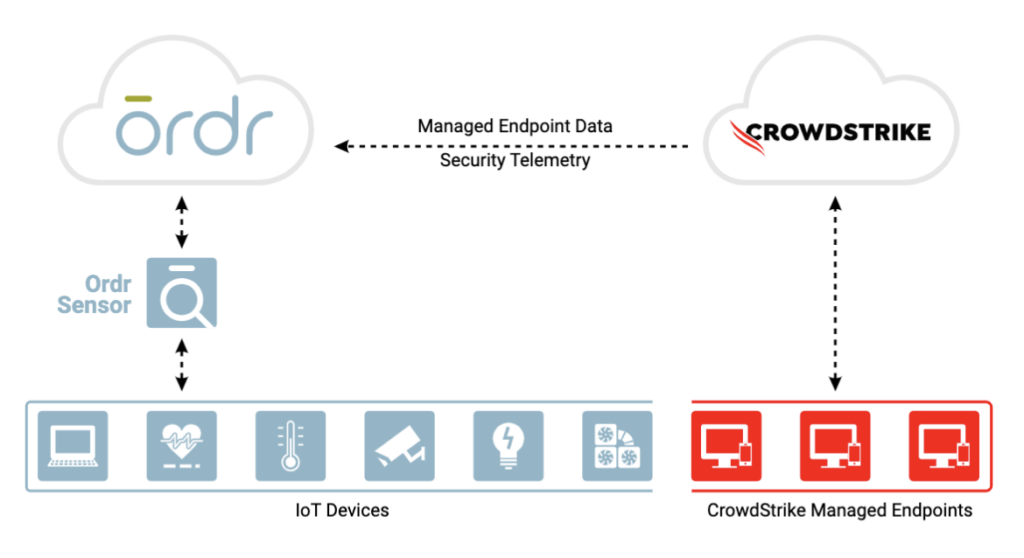
SEE ALL TECHNOLOGY PARTNERSIntegration between Ordr and CrowdStrike ensures the security of all managed and unmanaged devices with comprehensive device visibility, detailed vulnerability insights, an understanding of risk, and the ability to enforce policy to mitigate active threats and improve security across all connected devices
Ordr analyzes network flow data to automatically discover and classify every connected device, profile behavior, and identify active threats. Security telemetry from the CrowdStrike Falcon platform, is shared with Ordr to enhance device insights, and provide a centralized, deep understanding of each device and its associated risk. Ordr uses multiple factors to calculate risk for each device based on business context, asset criticality, vulnerabilities, and overall threat details. With additional device data from the Falcon platform, Ordr provides a highly accurate risk score for each device. By continuously synchronizing device risk scores with CrowdStrike’s enriched security data, Ordr enables teams with an up-to-date view of risk to help them focus on the most critical devices.
Gain complete device visibility
Minimize risk with better insights
Remediate faster
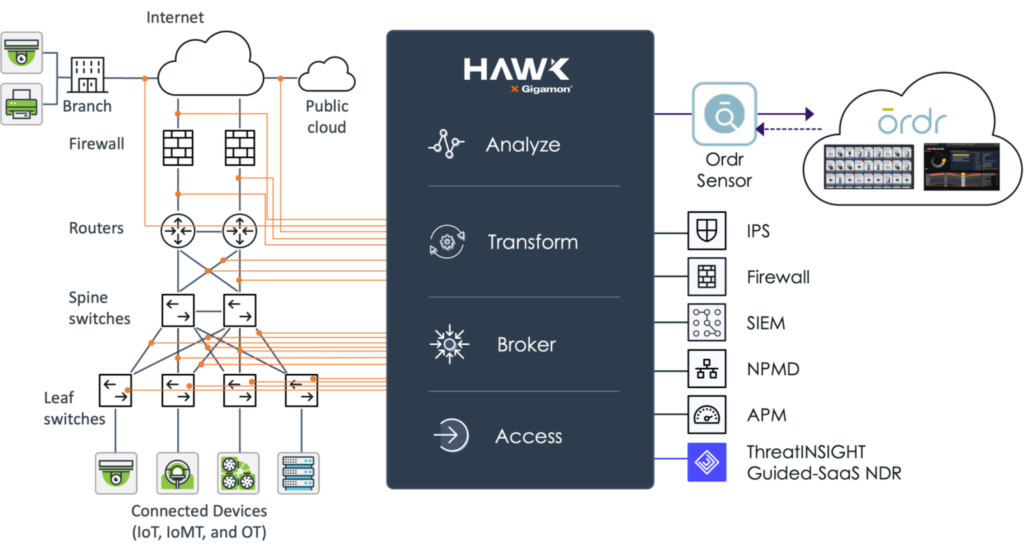
A basic tenet of network security and regulatory compliance is that “You cannot secure what you cannot see.” Gigamon and Ordr have teamed to deliver unsurpassed visibility and control into every thing connected to your network.
The Gigamon Visibility and Analytics Fabric (VAF) optimizes data collection of all north-south and east-west traffic across branch, campus, data center and cloud. Collected data is delivered to Ordr for analysis to ensure comprehensive device classification and visibility into all device communications. Integration with Gigamon VAF also eliminates concerns of SPAN security and potential impact to network infrastructure with “yet another SPAN port or session.”
By integrating with Gigamon VAF, customers can significantly reduce the number of Ordr sensors required to comprehensively discover and monitor every network-connected device, simplifying your network and security monitoring architecture.
Fortinet and Ordr have partnered to deliver an industry-leading IoT and unmanaged device security solution by integrating FortiManager, FortiGate and FortiNAC with Ordr Systems Control Engine (SCE)
Automated Visibility and Security of All Connected Devices
Ordr SCE automatically creates a complete asset inventory, identifies and prioritizes asset risk, and tracks and risk-rates asset communications patterns. Ordr transmits this critical security context to Fortinet FortiGate, FortiManager, and FortiNAC, allowing administrators to create and apply firewall and NAC policies using business-relevant groups, classifications, and device names, while understanding the full risk profile and impact of each change. Ordr further reduces administrative costs by automatically updating asset groupings as devices join and leave the network, as well as by creating and transmitting security policies directly to FortiGate and FortiManager for enforcement.
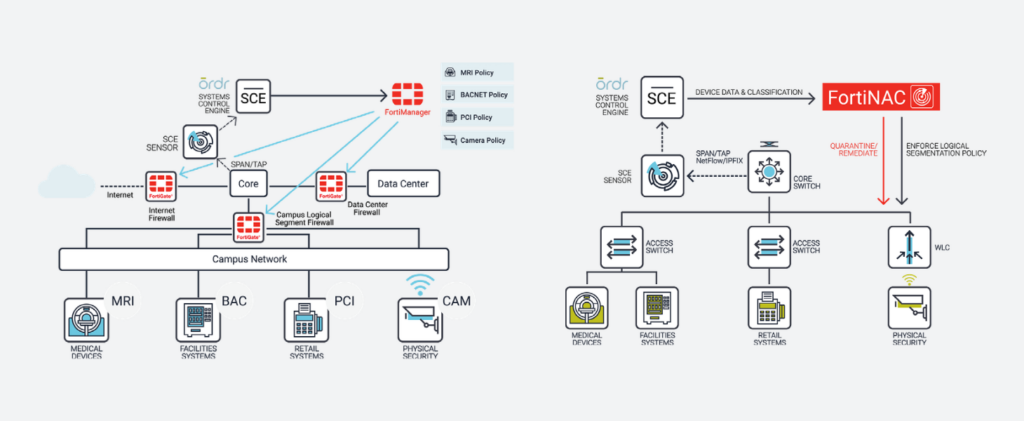
With the integration, joint customers can now:
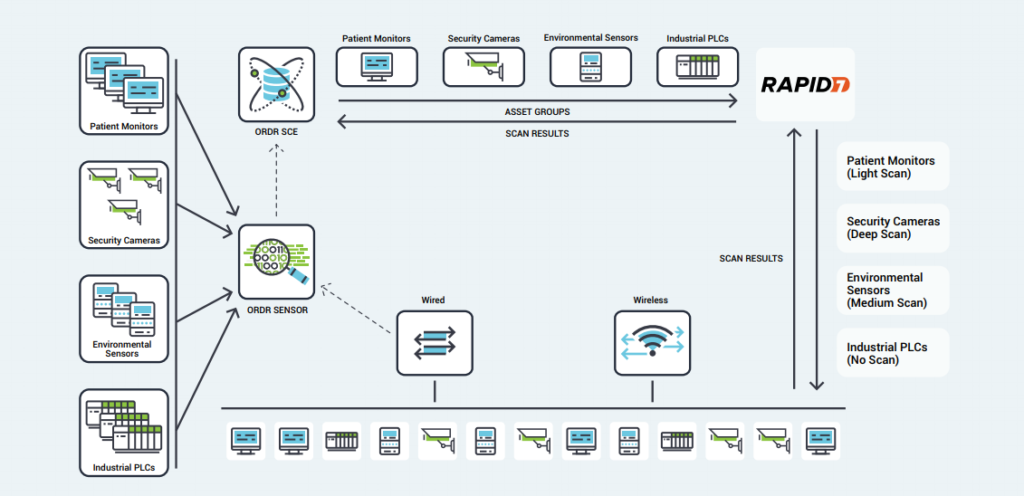
Ordr works with Rapid7 to seamlessly discover all connected assets including IoT, IoMT, and OT devices. The joint solution enables Rapid7 to perform the right scan at the right time regardless of the device type, location, criticality or role within the organization. Many vulnerable IoT/OT devices discovered by Rapid7 cannot be patched or updated. Ordr automates the application of compensating controls to safeguard these devices by sending protection policies directly to firewalls, switches, wireless, or NAC systems. Similarly, infected devices can be quickly isolated through existing network and security devices.
The integration with Ordr and Rapid7 InsightVM provide ongoing bi-directional synchronization for managing vulnerabilities with rich device context. Ordr discovers every connected device, profiles device behaviors and risks, and automates remediation responses. Rapid7 InsightVM provides visibility into the vulnerabilities and clarity on how those vulnerabilities translate into business risk. Combining Ordr’s unique device intelligence with Rapid7’s advanced vulnerability intelligence provides organizations with the ultimate solution to efficiently manage risks while reducing service disruption and time to remediate.
Explore how OrdrAI CAASM+ strengthens essential security measures by detecting gaps in security controls, evaluating security posture, and revealing asset exposures across all digital assets.
LEARN MORE ABOUT CAASM+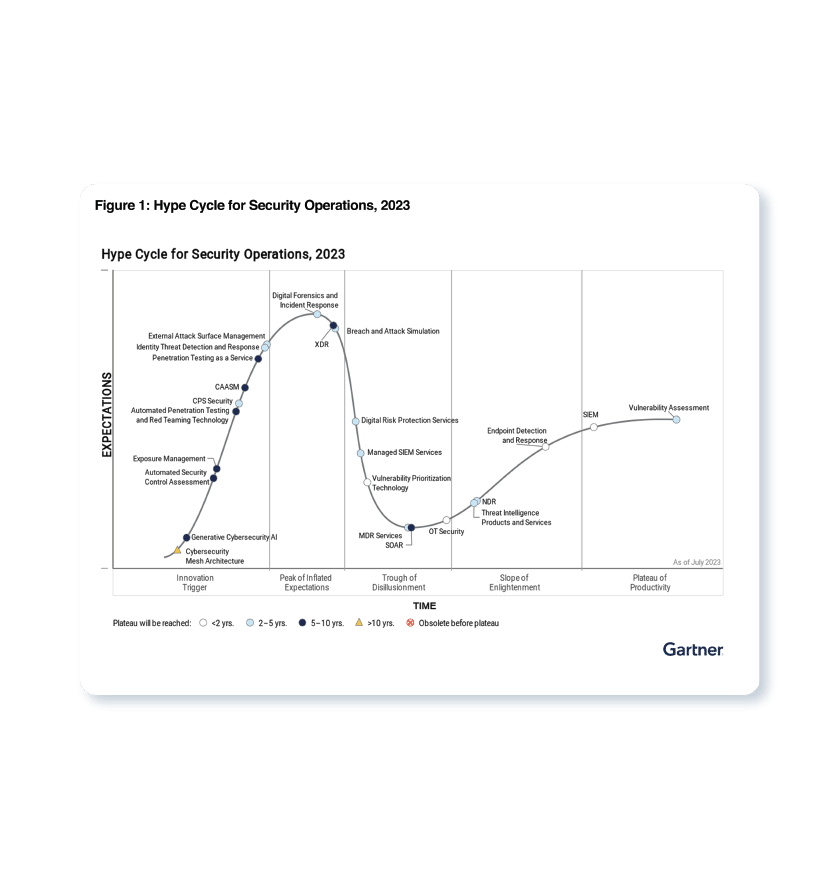

…the Ordr team together with our partners, customers, and advisors. For starters, despite economic friction remaining from the pandemic and the headwinds of inflation and recession, the Ordr team scored…
Uncategorized

By Pandian Gnanaprakasam

What a year it has been. Looking back there were plenty of surprises, but much to celebrate, be grateful for, proud of, and to leave us with ample optimism for the year to come. We’ll make our resolutions on January 1st, and have offered our opinions on what might transpire in 2023 elsewhere. But for now, let’s review the last twelve months and take in all that we accomplished as an organization–every member of the Ordr team together with our partners, customers, and advisors.
For starters, despite economic friction remaining from the pandemic and the headwinds of inflation and recession, the Ordr team scored many new customer wins, including many large enterprises representing every industrial sector. The message that organizations need to secure their growing inventory of connected devices is spreading, and Ordr stands head-and-shoulders above all other solutions in meeting that need. Among our many representative new customers earned during 2022 were:
Wins like these don’t happen without a lot of hard work. And as it has been since our founding, the Ordr team put in a lot of hard work during 2022 to build on past successes and execute against a goal of continuous improvement.
In March we launched Clinical Defender to enable Healthcare Technology Management (HTM) teams to manage their connected medical devices more efficiently and accurately in the face of an explosion of IoT and IoMT deployments in healthcare environments. As many as 20% of connected devices operating in healthcare organizations are unaccounted for. Clinical Defender closes that visibility gap while providing focused, actionable, and accurate HTM insights and workflows, so HTM and clinical engineering teams can:
Then in August we released Clinical Defender 8.1, adding the Ordr Software Inventory Collector and integration with Crowdstrike and Crowdstrike Humio to enhance the value of the platform by making it easy for Clinical Defender to gather contextual information from connected devices, and collaborate with security teams to defend the healthcare enterprise.
In May Ordr announced expanded technology integrations with our long-time partner Cisco, making Ordr available as a hosted application on Cisco Catalyst 9000 series switches. The integration enables Ordr’s seamless visibility, comprehensive insights, and enhanced security for connected devices in every environment using the Catalyst 9000 product family, and extends Ordr integrations with Cisco Meraki, Cisco Identity Services Engine (ISE), Cisco Software-Defined Access (SDA), and Cisco Trustsec.
“Ordr is a great purpose-built product that delivers exactly what they promise it will. It’s easy to work with and easy to maintain.” Network Engineer, healthcare and biotech industry.
Our partner relationships expanded further through new technology integrations with Arista, AWS, BigFix, Cisco Prime, CrowdStrike, Microsoft, Qualys, Rapid7, ServiceNow, and Tenable, as well as support for Osquery, contributing to the list of more than 80 integrations with the Ordr Data Lake. In total, these new integrations deliver stronger “ground to cloud” visibility, device management, and security capabilities for our customers by enabling them to operate with a richer, more contextual understanding of their connected device operations.
And then in November we added Sodexo Healthcare Technology Management to our partner network. The Ordr-Sodexo relationship delivers a people, process, and technology solution combining Sodexo Managed HTM Cybersecurity services with the Ordr platform. By combining the strengths of Ordr’s connected device security platform with Sodexo’s healthcare technology management services expertise, HTM teams can more easily identify threats and mitigate risks to their enterprises by securing all connected healthcare devices.
In November we also published our healthcare connected device maturity model entitled A Practical Guide: Implementing Connected Device Security for Healthcare Organizations. The guide outlines five stages of an effective connected device security program and strategies to achieve and maintain a Zero Trust security posture for healthcare organizations beleaguered by a relentless onslaught of cyberattacks. These stages include:
Ultimately our product improvements and partner relationships mean nothing if they don’t translate to greater connected device management and security capabilities for our customers. Our mission to help organizations See, Know, and Secure their entire connected device inventory and maintain a Zero Trust security posture was evinced throughout the year when we stepped up to help our customers identify and protect their devices from new threats like the Log4j and OpenSSL vulnerabilities, rogue device communications to risky foreign locations, malware variants like Maui Ransomware, and other threats to connected devices and the organizations that rely on them.
“Overall, we have a great experience with the Ordr system where our IoT and IoMT devices are well detected and inspected for inventory and vulnerability purposes.” Manager, IT Security and Risk Management, healthcare and biotech
Finally, it’s worth noting that every move we make is part of a strategy to grow Ordr into a strong, stand-alone technology leader that our customers know they can trust for years to come. That position as a market leader was reaffirmed during 2022 by respected organizations like KLAS Research, who named Ordr a healthcare IoT security leader for an unprecedented third year in a row, and IDC, who named Ordr a top innovator in healthcare security technology.
Our success and growth to date allowed us to attract another $40 million in new, C-round capital investments in June. Those funds are already at work building our organization through new hires and research and development, including the award of four new patents in October. Those patents are associated with processes for addressing unique challenges to securing connected devices, including the way we profile new devices, as well as innovations that make it easier for organizations to use our technology.
And as we continued to add human capital, among the many new faces Ordr welcomed to its roster was our new CEO, Jim Hyman, who took over the office formerly occupied by Greg Murphy during the last four years of incredible growth and success. Greg remains an integral part of the Ordr family operating as an advisor to the company. His hard work left Jim an organization well-positioned for future growth and success.
2022 was a big year for Ordr during which we achieved many important milestones. We look forward to helping even more organizations protect their networks from the increasing threats to their connected devices next year and beyond. After all, we are well-positioned to continue capitalizing on our unparalleled ability to secure the huge and growing number of healthcare and industrial IoT deployments.
“Deployment was easy; once running and we immediately got visibility. Support is great and helpful in tuning system, upgrades have been painless. Ordr has aided us in identifying unwanted devices and remediation activities, the behavior violation alerts position us to drive investigations based on known good traffic.” Director, IT Security and Risk Management, healthcare and biotech
As always, Ordr is here to make a major difference improving the way security controls are implemented, even as enterprises grow more complex. We are eager to meet whatever challenges 2023 has in store with confidence in our mission and clarity in our vision.
Pandian has more than 20 years of product and engineering leadership experience and is also a serial entrepreneur. Before founding Ordr, he was the Chief Development Officer at Aruba, responsible for all of engineering and product management functions. Aruba, an enterprise mobile wireless company, was acquired by HPE for $3 Billion in March 2015. Before Aruba, Pandian served as the head of engineering for Cisco’s multi-billion-dollar Wi-Fi business unit and before that as VP of engineering for low-end switching product lines. He graduated with a master’s degree in Electrical Engineering from IIT, Chennai, India and holds several patents to his credit in various networking technologies.
Subscribe today to stay informed and get regular updates from Ordr Cloud
…of bodily injury to workers, financial loss, and brand damage. Safety and availability go hand-in-hand in the OT space. And the security level of the IT network that communicates with…
In the legacy environment, operational technology (OT) security was heavily reliant on an ”air-gap” configuration, also known as the Purdue Model. OT systems weren’t exposed to the Internet or any internal networks. With the fourth revolution of industry ongoing, this configuration is no longer a viable option for manufacturing industries.
In today’s rapidly changing manufacturing environment and because of digital transformation, OT networks are now connected to IT networks and cloud. OT security now has to consider the wholistic needs of securing both the manufacturing floor and the ‘carpeted IT environment” from cyber attacks. In fact, analysis of recent cyber attacks against manufacturing environments show that the majority of threats are entering through the IT network and devices. As a result, OT and IT security must converge to work together in order to efficiently and comprehensively cover both networks.
OT is the use of hardware and software to monitor, maintain, and control the safe operation of manufacturing assets and processes. OT security is about protecting these devices, including Distributed Control Systems (DCS), Supervisory Control and Data Acquisition (SCADA) networks, Programmable Logic Controllers (PLC), and Remoted Processing Units (RPU) that are common in the industrial sectors and for maintaining cyber resiliency.
When OT wasn’t exposed to the IT networks, Internet or the cloud, securing the OT environment that was largely isolated was simpler. Now, OT is part of the same environment IT and facing a threat landscape similar to IT.
OT and IT are fundamentally different, so it’s no surprise that the previous security measures for OT didn’t include considerations for traditional IT security. The most relevant difference between the two is OT security focuses on securing assets that are part of the manufacturing facilities and process, rather than the digital assets and data of IT security. While OT security is centered around cyber resilience and keeping equipment and processes safe, IT security’s goal is to preserve confidentiality and data integrity.
Both types of security share the same goal of availability, but availability is a much higher priority for the OT sphere. If the components of the OT environment can’t run because they’ve been compromised by a cyberattack, this impacts the business. Consider the possible ramifications of a cyberattack immediately halting a manufacturing process without warning—physical damage to equipment, risk of bodily injury to workers, financial loss, and brand damage. Safety and availability go hand-in-hand in the OT space. And the security level of the IT network that communicates with the OT network directly affects the OT network’s safety and availability.
While the goals of IT security and OT security are different, and traditionally have followed different paths, converging IT and OT security into a cohesive whole has become the new normal. For example, the Colonial Pipeline attack forced 5,550 miles of pipeline to shut down for several days due to a ransomware attack. This ransomware attack on IT systems resulted in an OT impact even though the OT devices weren’t initially targeted. The shutdown was a precaution because the affected IT systems impacted billing.
In addition to the connection to traditional IT networks, the Industrial Internet of Things (IIoT) also factors into the convergence. Smart devices deployed in various industrial environments have helped create the need for IT/OT convergence. Even compliance is converging—any and all networks must be secure and meet a certain compliance threshold. The OT sphere is subject to its own regulations, creating a blending of needs to satisfy compliance frameworks.
IT security and OT security are bound together in the threat landscape because there’s no longer a distinct separation of OT and IT networks. This has led to development of viable OT security solutions that can provide asset visibility into the devices on the OT/IT converged network, monitor for threats and vulnerabilities, implement network segmentation, and maintain compliance while offering scalability.
OT security is an absolute must. It’s key to securing water treatment, waste management, utilities, manufacturing, and transportation facilities . A cyberattack that results in an OT security incident could have drastic and dire consequences for the company and the public at large. In order to operate safely and maintain optimal availability, a OT security solution should be implemented and maintained.
Asset discovery should be able to passively collect all necessary information on both IT and OT assets for the converged OT/IT network. Taking it a step further, continued visibility into what these discovered devices are communicating with provides a baseline of observed behaviors. This baseline on traffic visibility between OT, IT, and IIoT devices delivers actionable intelligence that can be used to identify anomalies, such as devices communicating outside of baseline to a malicious domain that may be indicative of a cyberattack in progress. Security starts with enterprise-wide visibility to all assets, including their vulnerabilities and behavior coalesced into a single source of truth.
A central OT security tool with monitoring allows a continuous analysis of OT network behavior. Using network behaviors as a guideline helps the system determine friend from foe, and reveals security insights that are critical to evolving measures on the network over time, such as vulnerabilities and weak passwords or certificates. Monitoring also provides logging, reporting, and event management. Because many OT networks are comprised of critical assets, continuous monitoring helps provide enhanced security for those assets.
IT/OT convergence has rendered the Purdue Model of layered segmentation inviable. Devices need to be able to communicate, which requires a more flexible version of network segmentation. OT security solutions today provide a modern version of segmentation and control zones. In addition, OT security solutions offer a more secure interface using a multifactor authentication method to implement appropriate user access, and methodical threat detection and remediation, including automated quarantine.
A strong OT security solution should provide detailed asset management, dynamic network segmentation, continuous threat assessment and vulnerability management, assist compliance and governance, and scale to meet business needs.
A key piece of asset management is continuous, real-time discovery that doesn’t impact operations. It should provide granular classification of OT, IT, IIoT, and unmanaged devices with comprehensive details. Using visibility across the various network topologies will help illustrate the cyberattack threat surface and designate non-compliant assets. Detailed asset management lowers the number of vulnerable entry points available to threat actors.
The CrashOverride attack in 2016 manipulated systems that relied upon the “air-gap” concept practiced in the Purdue model by infiltrating the gapped network. As attackers’ methods advance, so too must security practices to prevent incidents. A strong OT security solution delivers dynamic and automated network segmentation with layered zone controls. Using micro-segmentation policies on existing infrastructure limits devices’ ability to communicate, ensuring only authorized devices can do so.
Continuous monitoring of the behavior or communication flows of devices offers a window into what’s “normal” in the network. Combining behavioral anomalies with threat detection policy-based rules alerts system administrators of an attack before it begins or is in early stages. For example, an early indication of a ransomware attack might be application anomalies, such as SMB or RDP traffic from a targeted and vulnerable device. With continuous monitoring and behavioral analytics, this type of attack would be discovered before damage occurs.
OT compliance is always a pivotal concern and consists of a variety of frameworks and regulations. For compliance adherence, an OT security solution should provide in-depth inventory that pertains to ‘where and how’ sensitive regulatory information is stored. Identify devices running legacy systems, as well as devices that are potentially vulnerable, have expired certificates, or display anomalous behaviors. Vulnerable devices must be segmented and only interact with authorized devices and systems. With so many compliance caveats, a strong OT security solution helps facilitate and manage all these moving pieces.
OT must have high availability or cyber resilience to prevent financial ramifications or safety concerns. As business requirements change or capacity limits are reached, a solution must be able to expand to accommodate the change in needs. It should be easy to add new devices and sensors to a network without risking an interruption in productivity or system/device availability. Similarly, OT security solutions need to scale as the OT environment scales. Security policies that are in place to secure assets should be applied to new devices as they come onto the network.
The convergence of OT and IT has revolutionized OT security into more robust, complex requirements. While it’s beneficial that IT networks communicating with previously “air-gapped” OT networks have expanded the reach of the OT network significantly, it also increases the risk involved and introduces additional compliance concerns. Most cyber threats that affect OT systems enter through the IT space. The traditional Purdue Model can’t keep up with the advances in the cyber threat landscape, which have led to more dynamic and versatile OT security solutions that can protect valuable IT and OT assets, and can deliver segmentation inline with business needs.
In order to provide an adequate level of protection, an OT security solution must be able to work within the IT space and truly bring the IT and OT networks together into one cohesive “single source of truth” system.
Ordr provides a scalable solution to cover the entirety of the newly converged OT-IT network model that includes all the key components:
Subscribe today to stay informed and get regular updates from Ordr Cloud
…fear of hefty compliance fines for compromising patient data, but safe harbor laws protect hospitals in the event of an attack. Consider a cybersecurity vendor: The department of Health and Human…
In 2019, Verizon reported that ransomware already accounted for over 70% of successful cyber attacks on healthcare organizations. Since 2020, there’s been a 45% increase in attacks against healthcare providers. Beyond the financial impact to hospitals, the resulting device and system outages have had devastating consequences for patients — diverting ambulances to faraway hospitals, relocating at-risk patients, and rescheduling essential surgeries.
This guide explains how hospitals can protect themselves and their patients from the impact of cyber attacks, with staff education, thoughtful planning, threat detection, and incident response capabilities. Read on to learn more about the ransomware threats hospitals face and what can be done to prevent and overcome them.
The frequency and sophistication of ransomware attacks have dramatically increased over the past several years. Originally, attackers used what’s known as a “spray and pray” method: they would send mass email campaigns and hope that at least a few recipients would mistakenly open and download malware.
But in recent years, the strategy behind launching ransomware has evolved into a more targeted and stealthy operation. Today, cyberattackers prey on users’ psychology, posing as legitimate contacts at reputable organizations asking urgently for financial information, passwords, or other confidential data.
Hospitals are a prime target for ransomware attacks. Attackers know that hospitals collect and store sensitive information such as protected health information (PHI) and will do anything to minimize disruption in service and impact on patient safety. The COVID-19 pandemic exacerbated this problem. COVID pushed hospitals over capacity with record-setting admissions. With more to care for, employees were more likely to fall for ransomware traps.
On top of that, budget cuts have limited the amount of cybersecurity professionals on staff. This not only impacted the effectiveness of any cybersecurity programs in place, it also resulted in many organizations that were slower to identify and respond to developing threats.
Because of the imminent threat to patient safety, many organizations felt obligated to pay ransoms immediately. But this led to dangerous consequences. When hospitals paid a ransom, attackers would just ask for even more money, putting even more stress on healthcare systems. While insurance limited the impacts of high ransoms on hospitals, payouts often weren’t as high as organizations expected.
Allocating hospitals’ limited budget toward cybersecurity best practices and taking as many precautions as possible can help hospitals keep their patients, data, and organizations protected.
Thankfully, there are several proactive steps hospitals can take to prevent ransomware attacks and reduce impact to patients and the organization when attacks do happen. These steps include:
Platforms like Ordr are specifically designed to protect organizations such as hospitals from the impact of ransomware attacks, by identifying IoT, IoMT, OT, and IT devices that may be vulnerable to an attack, detecting anomalous behavior that may be an indicator of an attack, and automating the creation of policy to respond to an incident or proactively improve security with segmentation.
Ransomware attacks are evolving at an alarming rate, and the unfortunate reality is that hospitals continue to be a primary target. Dedicating time and effort to preparation is key to a swift and effective response. Some ways to prepare include:
Hospitals should be able to instantly detect and address any suspicious behavior on any device connected to their network. They should also take measures to identify devices that may need updates to configurations, patches to address vulnerabilities, or upgrades for outdated operating systems and software to plug up existing security gaps before they are exploited. The platform they use should also be able to aid in the response to an attack by automating policy and integrating with security and network products for enforcement.
Of course, not all vendors are created equal. Some are optimized for healthcare environments , monitoring all IoT, IoMT, and OT devices across the whole environment, laying the foundation for a comprehensive, real-time threat response strategy. Unlike other cybersecurity platforms, Ordr takes a “whole hospital” approach with capabilities that span across IoT, IoMT, OT, and IT devices.
The frequency of cyberattacks on hospitals and health systems more than doubled in the last five years, exposing the health information of nearly 42 million patients. And unfortunately, ransomware attacks will likely continue to target healthcare organizations into the future.
The good news is that hospitals can avoid detrimental consequences with the right plan, tools, and prevention measures. Proper staff education, vendor collaboration, segmentation, and sound cybersecurity plans contribute to a healthy security posture. But these methods can only offer so much protection. Hospitals need to gain visibility into their security gaps, clinical risks, and anomalous behavior — cybersecurity practices that can’t be achieved manually.
Ordr is an AI-powered platform built to keep hospitals and their patients safe by providing visibility and security of every connected device across the whole hospital. Ordr also integrates with a hospital’s existing security, network, and IT infrastructure enabling hospitals to maintain a comprehensive view of risk and focus efforts to respond and reduce threats. And because connected devices in hospitals are critical to the safety of patients, Ordr’s agentless, passive solution will provide insights and protection without impacting services.
Subscribe today to stay informed and get regular updates from Ordr Cloud
…and risks across IT, OT, and IoT assets as connectivity between industrial and administrative networks continues to expand. The blending of these environments will increase complexity and risk, while making…
General

By Danelle Au
It’s a new year, and with so much uncertainty, seven of Ordr’s executives and subject matter experts offer ironclad predictions for what to expect in connected device security in 2023.
Bryan Gillson, Head of Vertical Market Strategy
As a result of the convergence of information technology (IT) and operational technology (OT) and expanding connectivity of once isolated industrial infrastructure, there will be a notable increase in attacks targeting OT. Ransomware, cyberterrorism, and other attacks will be the unfortunate result and critical infrastructure environments will be a primary target.
OT like industrial control systems (ICS), supervisory control and data acquisition (SCADA), and similar equipment was once protected by air-gapping their networks from traditional IT and the internet (the Purdue Enterprise Reference Architecture, or Purdue Method). However, as trends like remote supervision, automation, and digital supply chain management have taken hold, greater levels of connectivity have opened those once isolated environments—including legacy systems running obsolete, unsupported, and unsecure equipment—putting them in reach of threat actors who have proven themselves all-too willing to take advantage of any vulnerability, and any type of organization.
Jim Hyman, CEO
CISOs and cybersecurity champions inside more organizations will see a sharp increase in support as corporate boards bring in cybersecurity expertise. When the U.S. Federal Trade Commission (FTC) issued guidance last year putting corporate boards on notice that “data security begins with the Board of Directors,” it added fuel to a process that had been slowly gaining momentum in recent years by elevating the issue of cybersecurity within corporate governance. In 2023 that process will translate to meaningful support for security initiatives, including budgets and staffing.
Similarly, in 2023 more organizations will be held to account for their lax security programs and we can expect to see greater attention given to the issue of cybersecurity by federal legislators. Lawmakers are growing impatient with corporate inaction even as threats begin to affect individuals amid attacks on critical infrastructure, including hospitals. As Senator Ron Wyden told MIT Technology Review, “There’s a tendency to hype the capabilities of the hackers responsible for major cybersecurity incidents, practically to the level of a natural disaster or other so-called acts of God. That conveniently absolves the hacked organizations, their leaders, and government agencies of any responsibility.”
In 2023 more organizations will be held to account for their lax security programs and we can expect to see greater attention given to the issue of cybersecurity by federal legislators.
Kahil Thomas, Regional Sales Manager, Healthcare
Inventory tools like configuration management databases (CMDBs) and computerized maintenance management systems (CMMSs) will play an increasingly critical role in cybersecurity as the number of connected devices continues to soar and organizations turn to automated solutions to scale security efforts. The importance of these tools , in turn, will prioritize the need to automate the collection of asset details, aggregate data from multiple sources, and ensure accurate, real-time information.
Gartner has identified the expansion of cyber-physical systems, including IoT and other connected devices, as a major risk for organizations that fail to account for all assets across their environment. Human effort alone is not capable of keeping up with the growth of connected devices and that is why automation is essential to all cybersecurity related tools.
Gnanaprakasam Pandian, Co-founder and Chief Product Officer
In 2023, organizations will finally have a single, unified asset knowledgebase for cyber security. This is essential to achieving and maintaining a Zero Trust security posture that spans IT, OT, and IoT. That is because maximizing protection demands there be no blind spots; and gaining a unified view of all connected assets, along with their essential business context, is foundational for cyber security today. That capability represents the keys to the cybersecurity kingdom, and it will be available to most organizations in 2023. Many organizations (but not all) will embrace it.
Also, the era of proactive protection using behavioral models will finally displace the era of reactive remediation. This will relieve a tremendous burden from security teams that currently spend an enormous amount of energy on reactive remediation and allow them to apply their skills to other areas of security, like optimization, automation, and forensics. Effective security means knowing what a device does much more than what the device is. Hence, behavioral modeling of devices will form the foundation of threat detection and automated response.
The era of proactive protection using behavioral models will finally displace the era of reactive remediation.
Darrel Kesti, VP of Sales
Healthcare will see an increase in mergers and acquisition activity in 2023 as a result of the financial toll on the industry since early 2020, including effects related to both the pandemic and a sharp increase in costly cyberattacks. Smaller and independent hospitals, clinics, and related service providers that are no longer able to deliver a high quality of care will see some operations shut down while others will be absorbed by larger providers, extending their reach and expanding their market footprint. But because many smaller healthcare organizations have been targeted relentlessly by threat actors, acquiring organizations must be careful to conduct thorough due diligence to determine if any threats exist before merging IT estates.
We will also continue to see an increase in cyber insurance premiums and coverage limitations in 2023 across healthcare and all other industries. As a result of the growing number of claims and increasing scrutiny, cyber insurance providers will demand greater documentation of essential security controls and will refine their audits and reviews to verify adequate security measures are in place, paying close attention to the complete 3PT (People, Process, Policy, and Technology) elements of security programs to reduce their risks.
Bryan Wallace – Head of Partner Sales
Network administration teams will be squeezed between being short-staffed due to a tight labor market and tightening budgets even as security requirements and expectations increase in the coming year. Trends toward network segmentation, Zero Trust implementation, and complete cyber asset attack surface management (CAASM), among other network-centric security priorities, will push organizations toward adopting new tools to simplify the definition and implementation of rigorous security policies (e.g., firewall, NAC, switch ACLs) and that allow teams to do more with less.
Similarly, both security and network teams will require a unified view of inventory and risks across IT, OT, and IoT assets as connectivity between industrial and administrative networks continues to expand. The blending of these environments will increase complexity and risk, while making security and IT operations management impossible without the right (automated) tools.
Trends toward network segmentation, Zero Trust implementation, and complete cyber asset attack surface management (CAASM)… will push organizations toward adopting new tools to simplify the definition and implementation of rigorous security policies
Paul Davis, VP of Customer Success
Cyberattacks targeting the healthcare industry will continue to increase, driving legislation at the state and federal level in the U.S., and abroad, while also prompting the industry to adopt stricter security standards on its own. In response, healthcare organizations will look for ways to generate efficiencies for security in what are often complex organizations.
With the overlap between traditional IT security teams and biomed/clinical engineering becoming more apparent, there will be pressure to adopt monitoring and security management tools that address requirements across the teams in 2023. The goal of these efforts is to improve visibility of the attack surface and response to threats while providing a more consistent and effective way of communicating security risk across the whole organization.
Danelle Au has more than 20 years of experience bringing new technologies to market. Prior to Ordr, she was CMO at Blue Hexagon, a deep learning for malware protection company, and CMO at SafeBreach where she helped build the marketing organization and and define the Breach and Attack Simulation category. Previously, she led strategy and marketing at Adallom, a cloud security company acquired by Microsoft. She was also Director, Security Solutions at Palo Alto Networks, driving growth in critical IT initiatives like virtualization, network segmentation and mobility. Danelle was co-founder of a high-speed networking chipset startup, co-author of an IP Communications Book and holds 2 U.S. Patents. She has an MSEE from UC Berkeley
Subscribe today to stay informed and get regular updates from Ordr Cloud
…interested in accessing Protected Health Information (PHI) , and it’s becoming challenging to safeguard patient data contained in Internet of Medical Things (IoMT) and other connected devices. Between 2009 and…
As healthcare technology advances, so do the many pervasive and complex threats for Healthcare Delivery Organizations (HDOs) and their patients.
Bad actors are increasingly interested in accessing Protected Health Information (PHI) , and it’s becoming challenging to safeguard patient data contained in Internet of Medical Things (IoMT) and other connected devices. Between 2009 and 2021, over 4,400 healthcare data breaches of 500 or more records were reported to the Department of Health and Human Services (HHS) and included the loss, theft, exposure, or impermissible disclosure of 314,063,186 healthcare records. So how can HDOs keep up with an ever-changing threat and risk landscape?
One of the key best practices is by addressing vulnerabilities associated with connected devices in the network. These vulnerabilities can be exploited by threat actors and used to gain unauthorized access, run malicious code, install malware, steal data, or even move laterally within a network.
Proactively identifying vulnerabilities and assessing their severity level helps security teams prioritize and respond to issues before data loss occurs. A solid vulnerability management program enhances the overall security posture of the organization, protects patient data, prevents unauthorized access, and reduces risk.
But implementing vulnerability management best practices is easier said than done. In this post, we’ll explain what vulnerability management is, how it works, and what you should look for in a solution.
Vulnerability management is the continuous process of identifying, analyzing, classifying, addressing, and reporting on vulnerabilities found across organizations, within operating systems, applications such as electronic medical records software and medical devices such as network connected infusion pumps, and MRI machines.
Security teams constantly track vulnerabilities and the severity of these vulnerabilities (typically via common vulnerability scoring systems (CVVS)) to identify potential risks in real-time as part of the vulnerability management process. The best organizations identify and prioritize the highest priority vulnerabilities and close existing security gaps before they are exploited. Operating at that level requires robust tools and well defined techniques.
Agent-based solutions and vulnerability scanning software are some of the most frequently used tools for vulnerability management with the ability to identify known vulnerabilities across various systems in the environment. However, these tools have limitations when it comes to the connected devices such as IoMT, IoT and OT devices that nurses, doctors, caregivers, and patients depend on daily. Many of these devices cannot accept agents and cannot be scanned for fear of impacting operations. HDOs need special connected device security solutions to monitor those devices for vulnerabilities and protect them from threats and exploits.
Any vulnerable device connected to the network can put patient safety at risk or impact care with delays to services.
An exploit is an attack that takes advantage of a vulnerability within a system. Bad actors look for software vulnerabilities, exploit them to gain entry into a network, and then employ methods to steal, destroy, or encrypt data or disrupt services . For instance, a cyberattacker might exploit a vulnerability in a medical device to gain access, and then install a ransomware. A threat is something that will exploit a vulnerability. And risk is the likelihood that a threat can exploit a vulnerability.
Security professionals aspire to minimize risks, threats, and exploits at all costs. Vulnerability management is one way to mitigate the risks to an organization. But security teams can take several other measures, such as:
Translating these high-level best practices into actionable steps is an easy way to mitigate vulnerability risks.
There are five stages in the vulnerability management process. Below, we cover each one in detail.
Every network connected device should be accounted for — from infusion pumps and imaging devices to tablets and smart speakers. The number of devices like these in a healthcare setting ranges in the thousands, and it can be difficult to see an organization’s entire connected footprint. Visibility of the number of devices, device type, operating system, where they’re located, and how they’re used are critical details needed for vulnerability management. Accurate classification of these devices, down to the make and model, exact operating system version, and other software details can help Healthcare Technology Management (HTM) professionals maintain a list of potential vulnerabilities.
Knowing where these devices are and how they are typically used can make locating and patching vulnerabilities easier. Knowing what devices are in your network also allows you to identify the scope of your vulnerability management program – for example, there may be specific types of devices that will not be scanned for fear of disrupting services, such as an MRI or imaging device .
Undetected vulnerabilities put organizations at risk of security breaches. There are a few techniques to identify vulnerabilities on a network, including active and passive scanning.
Active scanning can help you proactively identify and close any gaps with network connected, managed assets such as laptops. This type of scanning involves a software agent that is deployed on devices to test them and collect data on potential vulnerabilities. Agents cannot be deployed on many IoT, IoMT, and OT devices so you need specialized connected device security solutions to identify vulnerabilities on those devices.
Passive scanning reaches out from the server to network assets, and does not require the agents that active scanning does. This eliminates the need for additional software on devices. However, agentless scanning could impact device operations so it is not an option for many connected medical devices.
In order to prevent the impact to critical devices that could impact patient care, passive techniques are needed to gather device, operating system, and software details. This way, IoT, IoMT, and OT are not impacted while the make, model, OS, and patch level details of each is identified.
The goal of an efficient vulnerability management process is to identify the most relevant, high-risk vulnerabilities in order to prioritize security efforts and address them. As part of the vulnerability identification step, each new vulnerability should be prioritized based on its potential risk to your organization and your patients.
Thankfully, you won’t have to do this manually — there are many solutions that provide vulnerability risk rating capabilities. While this information is helpful, it’s much more valuable when combined with specifics about your organization and environment to understand the true priority.
The highest-risk vulnerabilities should be prioritized and tackled first.
Ownership across different device types can be complicated for HDOs: different teams may be responsible for medical, IT and facilities devices, including devices as varied as infusion pumps, nurse call stations, laptops, printers and HVAC systems. Organizations need clear ownership definitions and a process to identify owners which may be based on details such as region, location, cost center, department, and business criticality.
Make sure your vulnerability management system notifies device owners including IT personnel and security engineers whenever a new vulnerability is assigned, and consider creating reports to show what vulnerabilities each person is responsible for. Many vulnerability management platforms allow you to assign custom tags to each staff member, making it easy to assign and group vulnerabilities. Once vulnerabilities have been assigned to appropriate staff, they’re patched accordingly.
The final stage of the process is verifying that vulnerabilities have been addressed through remediation or by applying the proper mitigations. Engineers should follow proper testing protocols to ensure remediation is completed successfully and track each vulnerability’s status over time to document their progress. You should also pull reports of vulnerabilities on devices that cannot be patched. For example, manufacturers may provide patches on a regular release schedule, and you may need to segment or quarantine these affected devices until that update is available.
By adhering to these steps and adopting modern vulnerability management software, organizations can ensure that critical vulnerabilities don’t fall through the cracks during continuous monitoring. Make sure that your vulnerability management system can run organization-wide reports for governance, too. It’s critical that you adhere to reporting for regulatory bodies, and comply with frameworks such as ISO 27001 and HIPAA. Otherwise, your organization could face consequences like federal fines.
While modern technologies can revolutionize the way we work, they can also put our organizations and patients at tremendous risk. Comprehensive vulnerability management can maximize security and minimize the threat of exploitation. Establishing a thorough vulnerability management process and deploying extensive employee training are a good start. But what organizations really need is software like Ordr.
Ordr is an AI-powered platform to discover all connected devices, identify their vulnerabilities, assess risk, and provide capabilities to improve your security and ultimately the protection of your organization and patients. Unlike traditional vulnerability scanners or agent based tools, Ordr works passively to protect the IoT, IoMT, and OT devices connected to your network. This limits the potential impact and disruption to those devices while improving your security.
Ordr works with your traditional vulnerability management solution to ensure that there is a seamless strategy to manage vulnerabilities in managed and unmanaged devices across the whole hospital. For example, healthcare organizations today may have parts of the network with medical devices that are not scanned at all. Ordr enables tools such as Tenable and Rapid7 to have visibility into parts of the network that were previously not included in scans, along with detailed inclusion and exclusion details. This enables comprehensive vulnerability coverage without risk of disruption.
Subscribe today to stay informed and get regular updates from Ordr Cloud