We analyzed the capabilities of 31 leading zero-trust security platforms and selected the top eight solutions using our proprietary ranking methodology. Our evaluation focused on identity verification, microsegmentation, continuous monitoring, policy enforcement, and unmanaged device coverage, the critical factors that determine whether a zero trust architecture can actually deliver on its promise of "never trust, always verify."
Our Ranking Methodology
- Identity Verification (20%): We assessed how platforms authenticate users, validate device posture, and enforce multi-factor authentication. Strong solutions implement risk-based authentication that adapts to threat context. Weak implementations rely on static credentials that fail under modern attack scenarios.
- Microsegmentation (25%): This factor measures the ability to enforce granular application-level access policies. The best platforms segment devices dynamically based on risk scores. They prevent lateral movement by isolating workloads into distinct security zones.
- Continuous Monitoring (20%): We evaluated real-time visibility into device behavior, anomaly detection capabilities, and telemetry collection. Superior platforms monitor both managed and unmanaged assets. They provide security teams with complete network intelligence.
- Policy Enforcement (15%): This criterion examines how platforms translate security policies into action. Top solutions enforce least-privilege access automatically. They integrate with existing security infrastructure to create a consistent policy across hybrid environments.
- Unmanaged Device Coverage (20%): We prioritized platforms that secure IoT devices, medical equipment, and other agentless endpoints. Many solutions ignore these assets entirely. The winners provide passive discovery and policy enforcement without requiring software installation.
Top 8 Zero Trust Security Solutions for 2026
Rank | Platform | Identity Verification | Microsegmentation | Continuous Monitoring | Policy Enforcement | Unmanaged Device Coverage |
|---|---|---|---|---|---|---|
1 | Excellent | Superior | Comprehensive | Dynamic | Industry-Leading | |
2 | Excellent | Strong | Strong | Robust | Limited | |
3 | Strong | Excellent | Strong | Robust | Moderate | |
4 | Strong | Strong | Strong | Effective | Limited | |
5 | Superior | Moderate | Excellent | Strong | Moderate | |
6 | Strong | Strong | Strong | Robust | Moderate | |
7 | Strong | Strong | Moderate | Effective | Moderate | |
8 | Excellent | Moderate | Strong | Strong | Limited |
Top 8 Zero Trust Security Solutions: Descriptions & Reviews
1. ORDR
ORDR delivers the only zero-trust platform purpose-built for unmanaged and agentless devices. The Systems Control Engine (SCE) provides passive discovery of every connected device. It creates real-time inventories without requiring software agents on IoT, OT, or IoMT endpoints. The platform automatically learns unique communication patterns for each device. This behavioral intelligence powers microsegmentation policies that adapt to device needs. ORDR integrates with existing NAC and firewall infrastructure to enforce dynamic segmentation across the entire network.
- Identity Verification: Multi-layered device authentication with continuous validation
- Microsegmentation: Granular policies tailored to individual device requirements
- Continuous Monitoring: Real-time visibility across all managed and unmanaged assets
- Policy Enforcement: Automated enforcement through existing security infrastructure
- Unmanaged Device Coverage: Purpose-built for IoT, OT, and agentless environments
Summary of Online Reviews |
|---|
ORDR is recognized for "comprehensive visibility into device ecosystems." Security teams highlight the platform's "ability to secure medical devices and IoT without disrupting operations." Healthcare organizations praise "seamless integration with existing network infrastructure." |
2. Zscaler
Zscaler Zero Trust Exchange connects users directly to applications using identity-based policies. The platform eliminates traditional VPN patterns by enforcing application-level access controls. Zscaler Private Access (ZPA) prevents lateral movement by keeping users off the corporate network.
- Identity Verification: Risk-based authentication with device posture validation
- Microsegmentation: Application segmentation prevents network-wide access
- Continuous Monitoring: Inline SSL inspection and threat detection
- Policy Enforcement: Cloud-native enforcement at scale
- Unmanaged Device Coverage: Focused primarily on managed endpoint access
Summary of Online Reviews |
|---|
Zscaler receives praise for "scalable zero trust access that outperforms legacy VPNs." Enterprises note "strong policy enforcement for remote users." Reviews mention "limited visibility into unmanaged IoT devices." |
3. Palo Alto Networks
Palo Alto Networks delivers zero trust through Prisma Access. The platform combines ZTNA 2.0 with next-generation firewall capabilities. Organizations leverage Palo Alto's threat intelligence to inform access decisions across hybrid environments.
- Identity Verification: Integration with identity providers for conditional access
- Microsegmentation: Workload protection with granular firewall rules
- Continuous Monitoring: Unified telemetry across the network and endpoints
- Policy Enforcement: Centralized policy management for SASE deployments
- Unmanaged Device Coverage: Better for managed infrastructure than IoT
Summary of Online Reviews |
|---|
Palo Alto is known for "industry-leading firewall technology integrated into zero trust." Users appreciate "consolidated security management across cloud and on-premises." Some note "complexity in initial deployment for smaller teams." |
4. Cloudflare
Cloudflare One replaces VPNs with identity-verified connections to internal applications. The platform routes traffic through Cloudflare's global edge network. Access policies evaluate user identity and device context before granting access to applications.
- Identity Verification: SSO integration with contextual access controls
- Microsegmentation: Per-application access without network exposure
- Continuous Monitoring: Global threat intelligence at the edge
- Policy Enforcement: Fast policy propagation across edge locations
- Unmanaged Device Coverage: Designed for managed user devices
Summary of Online Reviews |
|---|
Cloudflare is praised for "exceptional performance with minimal latency." Organizations highlight "rapid deployment for distributed workforces." Reviews note "focus on web and SaaS access rather than operational technology." |
5. CrowdStrike
CrowdStrike Falcon Zero Trust combines endpoint telemetry with identity intelligence. The platform provides continuous risk assessment for users and devices. Behavioral analytics inform access policies that adapt to emerging threats.
- Identity Verification: Real-time risk scoring based on endpoint behavior
- Microsegmentation: Endpoint-focused rather than network-wide segmentation
- Continuous Monitoring: Industry-leading endpoint detection and response
- Policy Enforcement: Risk-based access control through partner integrations
- Unmanaged Device Coverage: Requires agents on most endpoints
Summary of Online Reviews |
|---|
CrowdStrike receives recognition for "unmatched endpoint visibility and threat detection." Security teams value "actionable intelligence that improves access decisions." Some mention "stronger as a signal source than standalone zero trust enforcement." |
6. Cisco Secure Access
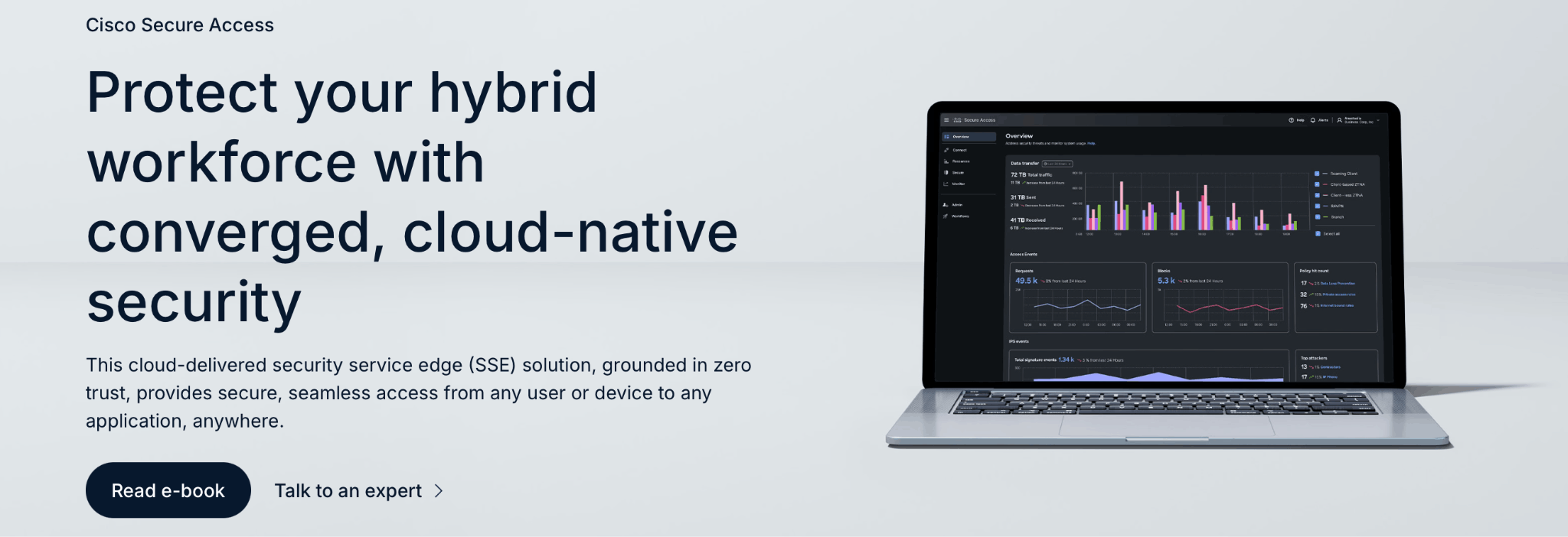
Cisco Secure Access converges ZTNA, SWG, and CASB into a cloud-delivered SSE platform. The solution provides consistent policy enforcement across the internet, SaaS, and private applications. Organizations benefit from unified management across Cisco's security portfolio.
- Identity Verification: Context-aware access based on user and device posture
- Microsegmentation: Application-layer controls across hybrid environments
- Continuous Monitoring: Integrated telemetry from network and security tools
- Policy Enforcement: Centralized policy engine for SSE functions
- Unmanaged Device Coverage: Better for enterprise IT than IoT ecosystems
Summary of Online Reviews |
|---|
Cisco is recognized for "comprehensive SSE capabilities with strong integration." Customers appreciate "simplified management for multi-function security." Reviews note "best fit for organizations standardized on Cisco infrastructure." |
7. Fortinet
Fortinet Universal ZTNA controls application access regardless of location. FortiClient provides a unified agent supporting both ZTNA and traditional VPN patterns. This approach enables gradual migration from perimeter security to a zero-trust architecture.
- Identity Verification: Policy-driven access with MFA support
- Microsegmentation: Application segmentation across cloud and data center
- Continuous Monitoring: Security fabric provides unified visibility
- Policy Enforcement: Consistent enforcement through the Fortinet ecosystem
- Unmanaged Device Coverage: Agent-based approach limits IoT coverage
Summary of Online Reviews |
|---|
Fortinet receives praise for "pragmatic VPN-to-ZTNA transitions." Organizations value "cost-effective security for Fortinet-standardized environments." Some note "less specialized for unmanaged device scenarios." |
8. Microsoft Entra
Microsoft Entra provides identity-driven zero trust through Global Secure Access. Entra Private Access replaces VPNs with application-specific connectivity. Conditional Access policies enforce risk-based decisions across Microsoft 365 and integrated applications.
- Identity Verification: Deep integration with Azure AD and MFA
- Microsegmentation: Application focus without granular device segmentation
- Continuous Monitoring: Extensive logging across the Microsoft ecosystem
- Policy Enforcement: Native enforcement for Microsoft services
- Unmanaged Device Coverage: Optimized for managed Windows and mobile devices
Summary of Online Reviews |
|---|
Microsoft Entra is known for "seamless integration with Microsoft 365 environments." Customers highlight "simplified identity management for cloud-first organizations." Reviews mention "less comprehensive for non-Microsoft infrastructure." |
Best Zero Trust Solutions for Healthcare and IoT Environments
Top Zero Trust platforms designed to secure healthcare systems and IoT-heavy environments with high device diversity.
Rank | Platform | Why It Excels |
|---|---|---|
1 | Purpose-built for unmanaged medical devices with passive discovery | |
2 | Continuous endpoint monitoring for connected healthcare devices | |
3 | Strong threat intelligence for operational technology protection | |
4 | Integrated approach for hospital network segmentation |
Best Zero Trust Solutions for Enterprise Remote Access
Leading Zero Trust platforms that enable scalable, secure connectivity for modern remote work infrastructures.
Rank | Platform | Why It Excels |
|---|---|---|
1 | Proven scalability for distributed workforce access | |
2 | Global edge network delivers minimal latency | |
3 | Comprehensive visibility across remote office IoT devices | |
4 | Native integration with the Microsoft 365 ecosystem |
To request a copy of this list in PDF format, contact us here.
CONTACT US HERE
